Adding the PingAuthorize Shared Flow to Apigee
About this task
To install the PingAuth Shared Flow bundle in Apigee and configure it to integrate with PingAuthorize:
Steps
-
Create a new bundle:
Choose from:
-
For Apigee X, go to Develop → Shared Flows and click Upload Bundle.
-
For Apigee Edge and Apigee Private Cloud, click +Shared Flow and then click Upload Bundle.
-
-
Upload the PingAuth Shared Flow bundle
.zipfile and name the shared flowPingAuth. -
Configure the connection to PingAuthorize:
Choose from:
-
Apigee X
Apigee X doesn’t support managing the configuration values stored in key value maps through the Apigee UI. You must add these configuration values to the key value map policy. The key value map is created and the configuration values are added the first time the PingAuth Shared Flow executes at runtime.
-
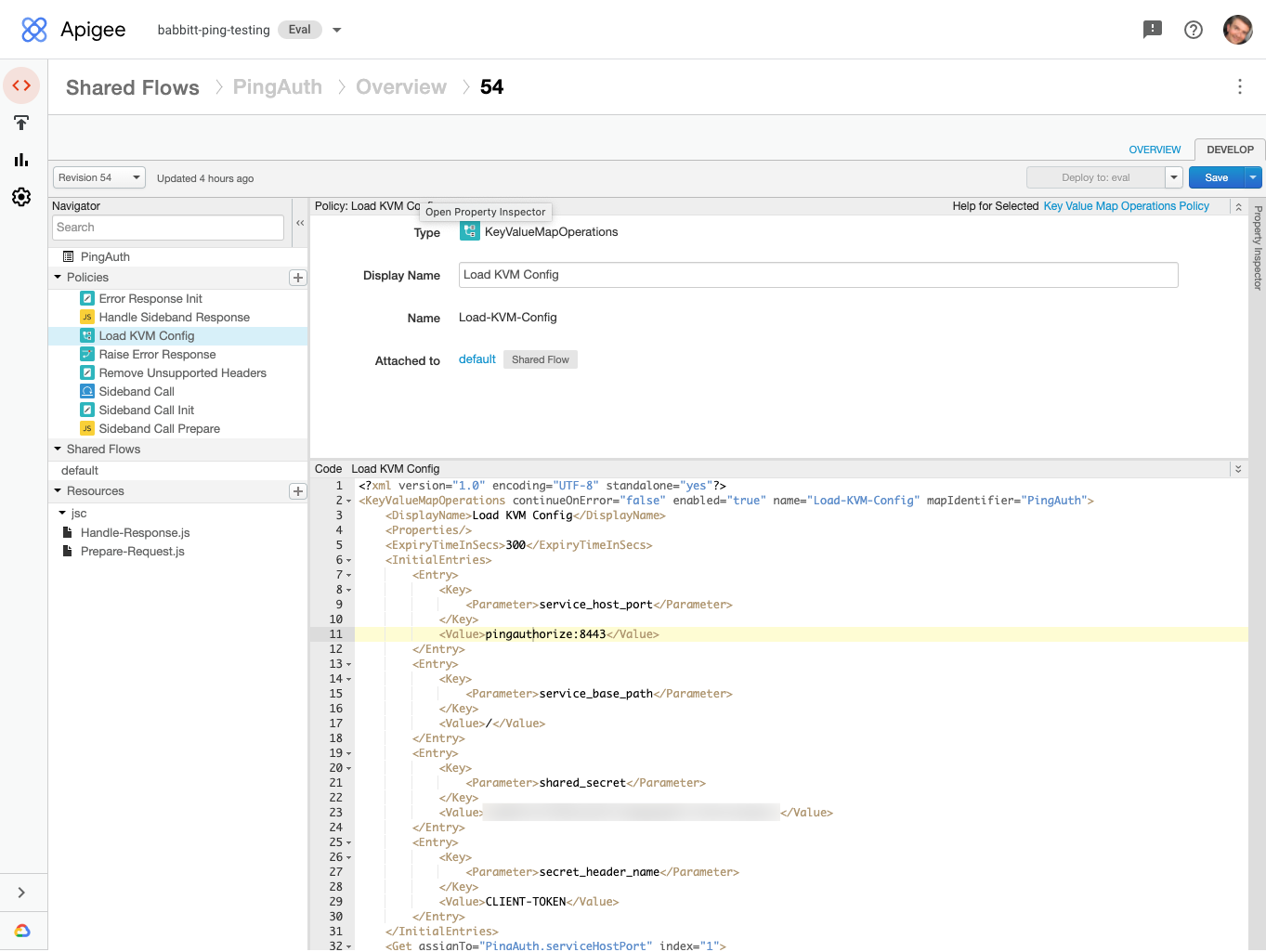
Go to Develop → Shared Flows → PingAuth.
-
On the Develop tab, select the latest revision in the Revisions list.
-
In the Policies list, select the Load KVM Config policy.
-
Remove the comment characters above and below the
InitialEntrieselement in the policy editor panel. -
Edit the value for
service_host_portto match the host name of your PingAuthorize server and the port of the HTTPS connection handler.For example,
pingauthorize:8443.You can find the HTTPS connection handler port from the Configuration page of the PingAuthorize administrative console by going to System → Connection Handlers.
-
Edit the value of
shared_secretto match the value of the shared secret that you created in PingAuthorize. -
Click Save.
Your finished configuration should look like this:
-
-
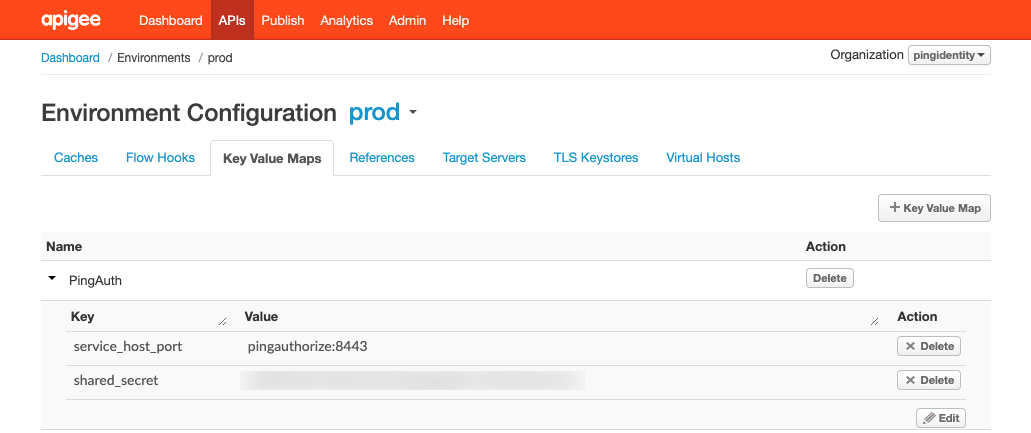
Apigee Edge and Apigee Private Cloud
Apigee Edge stores environment-specific configuration values in key value maps so that the same policies can be used across multiple deployment environments without any changes to the policies.
-
Go to Environment → Key Value Maps and click +Key Value Map.
-
Edit the key value map and click Add Entry.
-
Use the key name
service_host_portand set the value to match the host name of your PingAuthorize server and the port of the HTTPS connection handler. For example,pingauthorize:8443. -
Add a key called
shared_secretand set the value to the shared secret that you created in PingAuthorize. -
Click Save.
-
Your finished configuration should look like this:
-
-
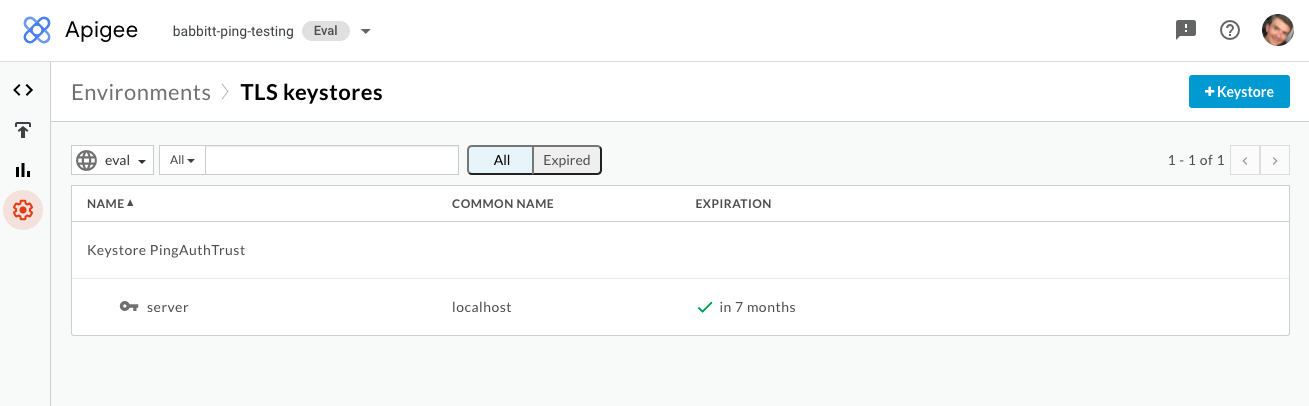
Optional: Configure HTTPS trust for PingAuthorize.
By default, the PingAuth Shared Flow is configured to only trust the PingAuthorize HTTPS connection handler certificate if it is issued from a well-known certificate authority. To enable Apigee to trust specific HTTPS certificates from PingAuthorize servers:
-
Go to Environment → TLS Keystores and click +Keystore.
-
Give the keystore a name that helps you identify your PingAuthorize environment. For example,
PingAuthorize-dev-truststore. -
Click the button to add a certificate. Enter a certificate alias and upload the certificate that is configured for the HTTPS connection handler in PingAuthorize. Click Save.
-
Go to Environment → References and click +Reference.
-
Name the new reference
PingAuthTrust. Select the keystore that you created previously, and then click Save.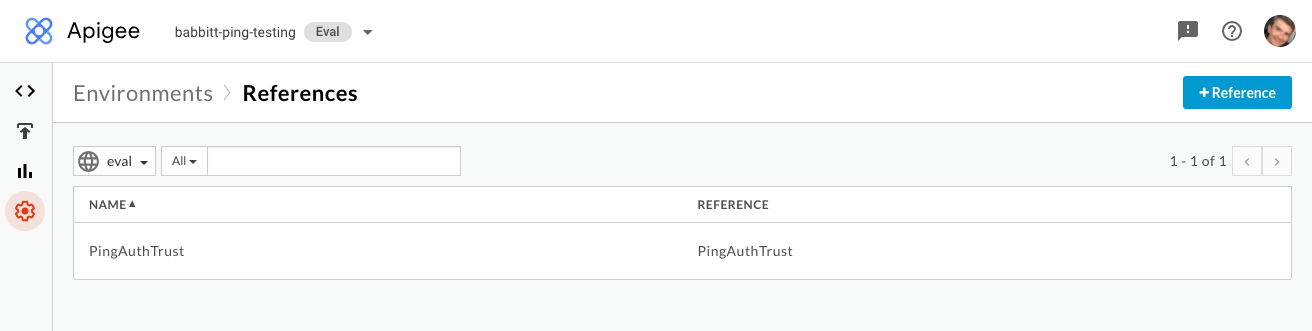
-
Go to Develop → Shared Flows → PingAuth.
-
On the Develop tab, select the latest revision in the Revisions list.
-
In the Policies list, select the Sideband Call policy .
-
Remove the comment characters surrounding the
TrustStoreelement in the policy editor panel, and then click Save.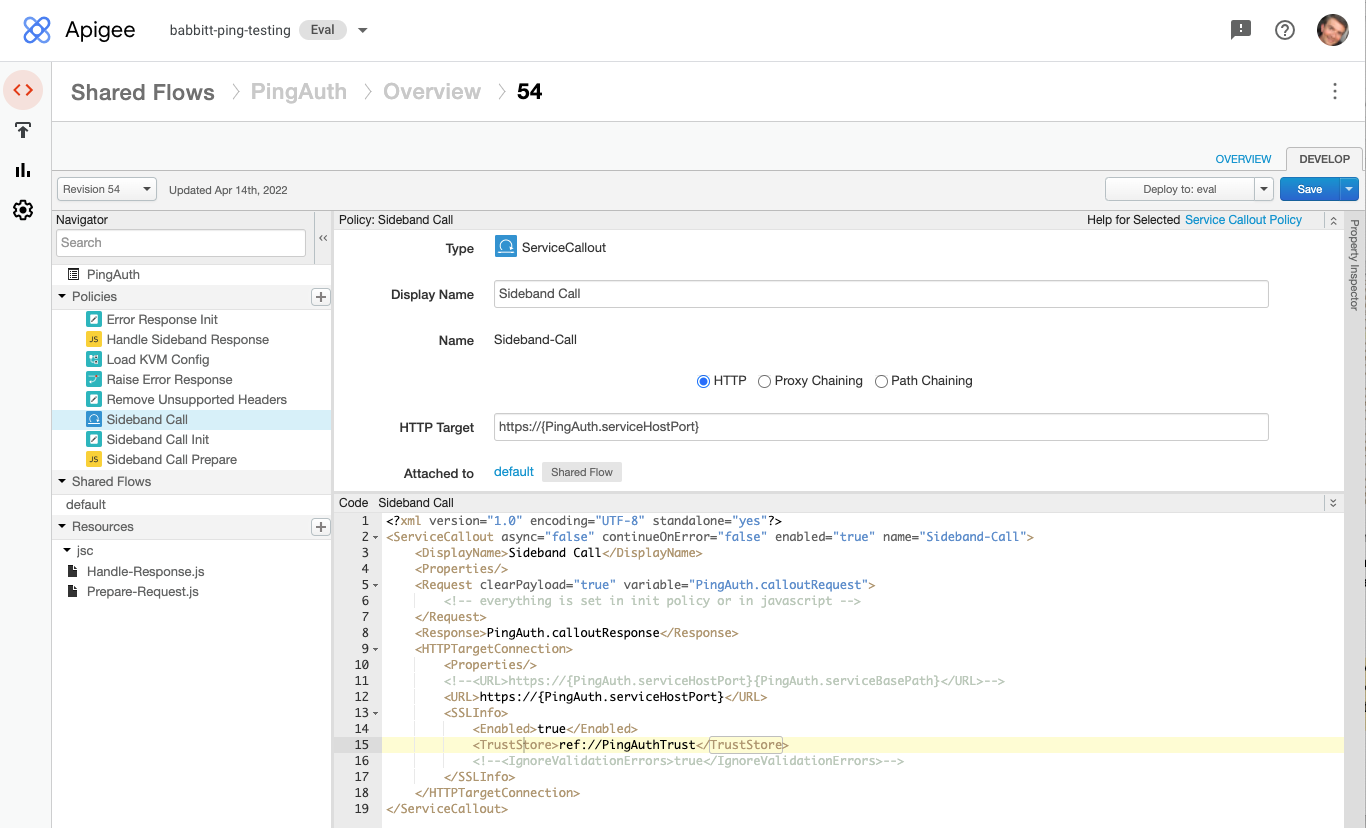
-
-
Go to Develop → Shared Flows → PingAuth and deploy the most recent revision to your environment.