PingFederate 11.0 - December 2021
PingFederate 11.0 provides the following enhancements and resolved issues.
Enhancements
- PingOne integration
-
- PingOne LDAP Gateway datastore
PingFederate in the cloud can now connect to on-premise directory servers through the PingOne LDAP Gateway.
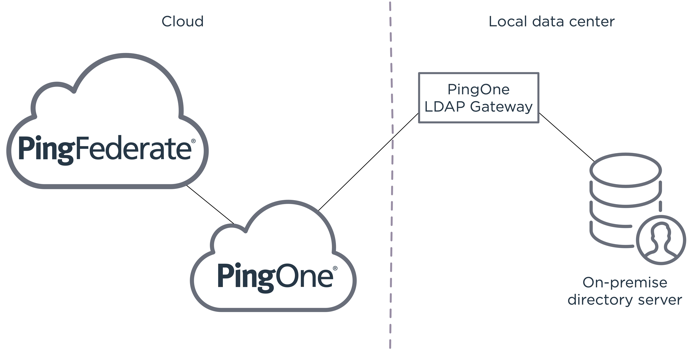
This new capability reduces the complexity of moving to the cloud, while maintaining connectivity to on-premise end-user data.
- PingOne unified admin integration
-
Administrators can now open the PingOne unified admin from any configuration window in the PingFederate administrative console. To activate the new Home icon, enter the PingOne region and the environment ID in the
run.propertiesfile.- Management of configuration encryption keys
-
PingFederate maintains a set of configuration encryption keys to encrypt sensitive configuration information provided by the administrators and decrypt them later as needed. While we continue recommending customers to protect their configuration encryption keys by AWS KMS or custom solutions based on the PingFederate SDK (the
MasterKeyEncryptorinterface), we are introducing two enhancements in this area.
- Key rotation
-
Administrators or key-management processes can now insert a new configuration encryption key into the system with one click in the administrative console or a single administrative API request. Once rotated, PingFederate starts using this new encryption key when it needs to encrypt sensitive configuration data.
- Re-encryption of configuration data
-
Version 11 also comes with a new
configkeymgrcommand-line utility. Administrators can optionally scan, review, re-encrypt, and delete older configuration encryption keys in their systems. Furthermore, administrators can now choose to re-encrypt sensitive information when importing an archive from a different environment; this is most useful when administrators do not want to share configuration encryption keys between the two environments.- Secret Managers
-
The new Secret Managers support allows customers to store certain credentials, such as data store credentials, in external secret management systems and have PingFederate retrieve them as needed. It helps customers comply with internal IT policies or meet and exceed their industry standards. Version 11 integrates out-of-the-box with CyberArk Credential Provider. Customers can also develop custom solutions based on the PingFederate SDK (the
SecretManagerinterface), to connect to other secret management systems. - Financial Grade API enhancements
- FAPI 1 Advanced Final certifications
-
Ping Identity remains a solid contributor to the financial-grade API initiatives from the OpenID Foundation. We’re proud that PingFederate is a certified implementation of various FAPI 1 Advanced Final profiles, including all profiles under Australia CDR and UK Open Banking and four profiles under Brazil Open Banking. Deploy Open Banking solutions with confidence and rest assured that we will continue to invest in OAuth, OpenID Connect, and FAPI specifications. For more information about OpenID certifications, visit .net/certification///[https://openid.net/certification/#FAPI_OPs].
- Flexibility in ID token issuance
-
When processing an OpenID Connect hybrid flow, in addition to issuing an ID token from the token endpoint, PingFederate may also return an ID token from the authorization endpoint, depending on the requested response type. Administrators now have the flexibility to separate these two ID token issuances and configure their fulfillment differently. These enhancements allow our customers to comply with the regulatory requirements and open standards set by the Australian CDR and FAPI specifications.
- Encrypted request objects
-
PingFederate now supports encrypted request objects that OAuth clients send to its Authorization endpoint and the Pushed Authorization Requests (PAR) endpoint. As needed, administrators can make encrypted request objects mandatory. This new capability further secures the confidentiality of authentication request parameters.
- Authorization server issuer identification
-
The OAuth 2.0 Authorization Server Issuer Identification draft specification intends to mitigate the scenario where mix-up attacks are a potential threat to all OAuth clients interacting with multiple authorization servers. As needed, administrators can enable this optional capability.
- Better private key JWT validation
-
In the context of OAuth client authentication, when processing private key JWTs from applications, PingFederate now ensures that the issuer (
iss) claim value matches the client ID. This enhancement removes the need to use issuance criteria to enforce this validation requirement.- Other OAuth and OpenID Connect improvements
- Message customization in OIDC IdP connection
-
PingFederate 11 can now take the request parameters from the SAML 2.0 SP or the OpenID Connect relying party (OIDC RP) into account when building its OIDC authentication request to the third-party OpenID Provider (OP). This capability allows administrators to selectively configure the values in the outbound OIDC authentication requests if their use cases or the third-party OPs have the need to gather more information from the originating SP or RP.
- Multi-valued attribute format
-
Administrators can optionally indicate that PingFederate should always return an array for an attribute value regardless of whether the attribute contains one or multiple values. This flexibility simplifies the logic required to consume attribute values from access tokens or ID tokens.
- Administrative experience enhancements
- Streamlined initial setup experience
-
We’re pleased to introduce a brand new initial setup experience, where administrators can finish their initial setup in as little as four steps, rapidly making our rock-solid capabilities available after starting PingFederate for the first time.
- Individual policy management by API
-
Administrators can now focus solely on one policy without including other policies as part of the API request when managing an individual authentication policy through the administrative API. This simplification improves the API experience and eliminates the risk of making unexpected changes in other authentication policies.
- Console heartbeat
-
Monitoring the status of the console node is now more straightforward with the addition of the
/pf/heartbeat.pingheartbeat endpoint to the administrative port. Like its runtime counterpart, the administrative heartbeat endpoint is also capable of returning additional information. If administrators want detailed information in the responses, set thepf.heartbeat.system.monitoringproperty totruein therun.propertiesfile. - Datastore enhancements
-
-
We expanded the REST API datastore with HTTP POST support. Administrators can connect to data repositories that prefer or require the HTTP POST method.
-
Administrators can add attribute options in their LDAP directory searches. This enhancement expands what PingFederate can retrieve from the directory servers that support attribute options, PingDirectory being one of them.
-
When configuring an LDAP search filter that uses one or more variables, an administrator can optionally specify default values for them, most useful in the scenarios where these variables may not contain any values at runtime.
- Improvements in upgrade experience
-
- Migration of templates
-
Our upgrade tools now copy customized default templates from the previous installation to the new one. This improvement preserves the end-user experience and branding, making it easier to verify and move forward with version 11 and beyond.
- New configuration for dynamic discovery settings
-
Previously, administrators could only define dynamic discovery settings to discover cluster membership in the
server/default/conf/tcp.xmlfile. Version 11 provides a new configuration file for these settings,jgroups.propertiesin thebindirectory. This new approach streamlines future upgrade experiences. For new installations, we recommend defining dynamic discovery settings in thejgroups.propertiesfile. While upgraded environments will continue to look for dynamic discovery settings from thetcp.xmlfile, we recommend performing a one-time migration to ease the upgrade experiences in the future.- Enriching end-user experience
- Email ownership verification by OTP
-
For customer identities, in addition to email ownership verification by one-time link, administrators can now enable email ownership verification by one-time passcode (OTP). This new option offers a modern verification experience. It also helps customers who prefer not to send hyperlinks via email to their consumers.
- Request context to authentication API applications
-
Administrators can optionally configure PingFederate to pass contextual information, such as the OAuth client ID or tracked HTTP parameters, from the sign-on requests to the authentication API applications. This allows developers to build applications that offer tailored experiences and satisfy branding requirements from their organizations based on contextual information from the sign-on requests.
- Kerberos authentication improvement
-
Administrators can now ensure Kerberos authentication remains functional for service tickets associated with older Kerberos service account passwords after updating the Domain/Realm Password field with a new password in PingFederate. This optional capability increases productivity because workforce identities are no longer required to restart their Windows sessions in order to authenticate via Kerberos.
- Contextual information in Session Management API responses
-
The Session Management API now includes IP address and User-Agent information in its responses. Clients with access to this API can learn more about their users and provide suitable offerings based on this new insight.
- Security enhancements
-
-
PingFederate now supports Amazon EC2 Instance Metadata Service version 2 (IMDSv2) when AWS_PING is the chosen dynamic discovery method. No PingFederate configuration changes are required, and IMDSv1 remains supported.
-
PingFederate now records administrative timed-out events in the administrator audit log (
admin.log). -
The Change Password and Password Reset end user-facing pages now time out after 30 minutes. This is the new default behavior for new and upgraded installations. As needed, administrators can configure a different Password Update Timeout value per HTML Form Adapter instance to suit the needs of their organizations.
-
- Other improvements
-
-
PingFederate now includes HTTP/2 support for inbound requests for better performance.
-
Administrators can optionally configure PingFederate to mask values obtained from tracked parameters in the server log. Look for the
MaskTrackedParamssetting in theorg.sourceid.saml20.domain.mgmt.impl.TrackedHttpParamManagerImpl.xmlfile. -
Administrators are free to enable the refresh token grant type independently on a per-client basis regardless of whether session validation is enabled in any Access Token Managers.
-
Administrators can optionally configure PingFederate to redirect end-users back to the Sign On page after successfully updating their soon-to-expire password as part of their SSO requests.
-
The Reuse Existing Persistent Access Grants for Grant Types authorization server setting is now overridable per client.
-
PingFederate now supports RSAES OAEP using SHA-256 and MGF1 with SHA-256 (RSA-OAEP-256) when minting outbound ID tokens or processing inbound encrypted request objects
-
Administrators can optionally restrict access to the redirectless mode per authentication API application. Additionally, administrators can further limit each application to an OAuth client to improve security around the redirectless mode of the authentication API.
-
We upgraded the framework of our administrative API documentation to Swagger 2.0.
-
PingFederate now preserves line breaks and indentations of OGNL expressions.
-
The following templates now share these Velocity template variables, which makes branding end-user experiences easier.
Templates Variables -
identifier.first.template.html -
html.form.login.challenge.template.html -
html.form.login.template.html -
html.form.message.template.html -
html.form.password.expiring.notification.template.html
-
$client_id- The ID of the OAuth client used by the request -
$entityId- The entity ID of the SP connection used by the request -
$connectionName- The name of the SP connection used by the request -
$baseUrl- The base URL of PingFederate instance -
$adapterId- The IdP adapter ID used by the request -
$spAdapterId- The SP adapter ID used by the request
-
-
Updated the following bundled components and third-party dependencies:
-
Jetty 9.4.44
-
JGroups 4.2.16
-
jose4j 0.7.9
-
Log4j 2.16.0
-
PingFederate Agentless Integration Kit 2.0.4
-
PingID Integration Kit 2.15.0
-
PingOne Integration Kit 2.4.1
-
Spring Framework 5.3.5
-
-
Resolved issues
| Issue ID | Description |
|---|---|
PF-20709 |
Resolved an issue that sometimes caused a cluster’s dynamic OAuth/OpenID Connect keys to fail to synchronize when a node restarts. |
PF-27519 |
Resolved an issue that prevented a PingFederate provisioner from using a group of GUIDs as the source to detect new and removed records. |
PF-28074 |
Now PingFederate correctly applies customizations of |
PF-28842 |
Reduced the time it takes for PingFederate to retrieve OAuth clients from Oracle databases. |
PF-29189 |
Unnecessary dependency error banners no longer appear in the administrative console when you use the administrative API to modify selectors or service provider adapters. |
PF-29202 |
Now you can localize end user messages from the authentication API for registration failure scenarios. |
PF-29294 |
Resolved an issue that stopped PingFederate from completing a device authorization flow when using IdP connection OAuth attribute mapping. |
PF-29318 |
When a proxy is in front of PingFederate, the Multiple Sign-On Delay template now redirects to the correct port. |
PF-29352 |
As a service provider (SP), when PingFederate can’t decrypt an assertion using the primary encryption certificate, it now logs the following message at the WARN level instead of the ERROR level: " |
PF-29381 |
Resolved a security vulnerability caused by web server URI mishandling. |
PF-29392 |
Introduced the ability to add response headers to the |
PF-29470 |
Fixed to the upgrade utility so that, in non-interactive mode, it retains cipher related settings that are different from the default settings in the source version. PingFederate changes to new default settings on upgrade only if the settings have not been changed from the defaults in the source install. |
PF-29509 |
Resolved an issue that caused PingFederate to render the default |
PF-29668 |
Resolved an issue that prevented the use of partial matches for resource URIs with OAuth 2.0 Token Exchange and produced the error message: " |
PF-29795 |
Now, when administrators add an attribute to a data source lookup but do not use the attribute anywhere, such as for contract mapping or issuance criteria, the attribute persists in the administrative console and API. |
PF-29847 |
The Microsoft Active Directory LDIF script for persistent grant storage now creates an index for the |
PF-29870 |
Resolved the following notification publisher issues:
|
PF-30002 |
Now target resources that don’t start with |
PF-30039 |
Now various endpoints return |
PF-30232 |
The administrative console no longer shows an error message when you try to create an instance of a custom IDP adapter that uses the class for filterable dropdown controls, |
PF-30272 |
Reduced memory usage during certificate revocation list (CRL) parsing, which speeds up CRL retrieval and avoids memory exhaustion in the case of very large CRLs. |