Choosing a deployment model
PingOne Privilege offers agent-based and agentless deployment models. Choosing the right model depends on your organization’s priorities for security, ease of deployment, and user experience.
Agent-based deployment
The agent-based model is recommended for organizations requiring the highest level of device and user identity assurance. In this model, users install the PingOne Privilege agent on their device. The agent leverages the device’s Trusted Platform Module (TPM) to create a strong, hardware-backed identity.
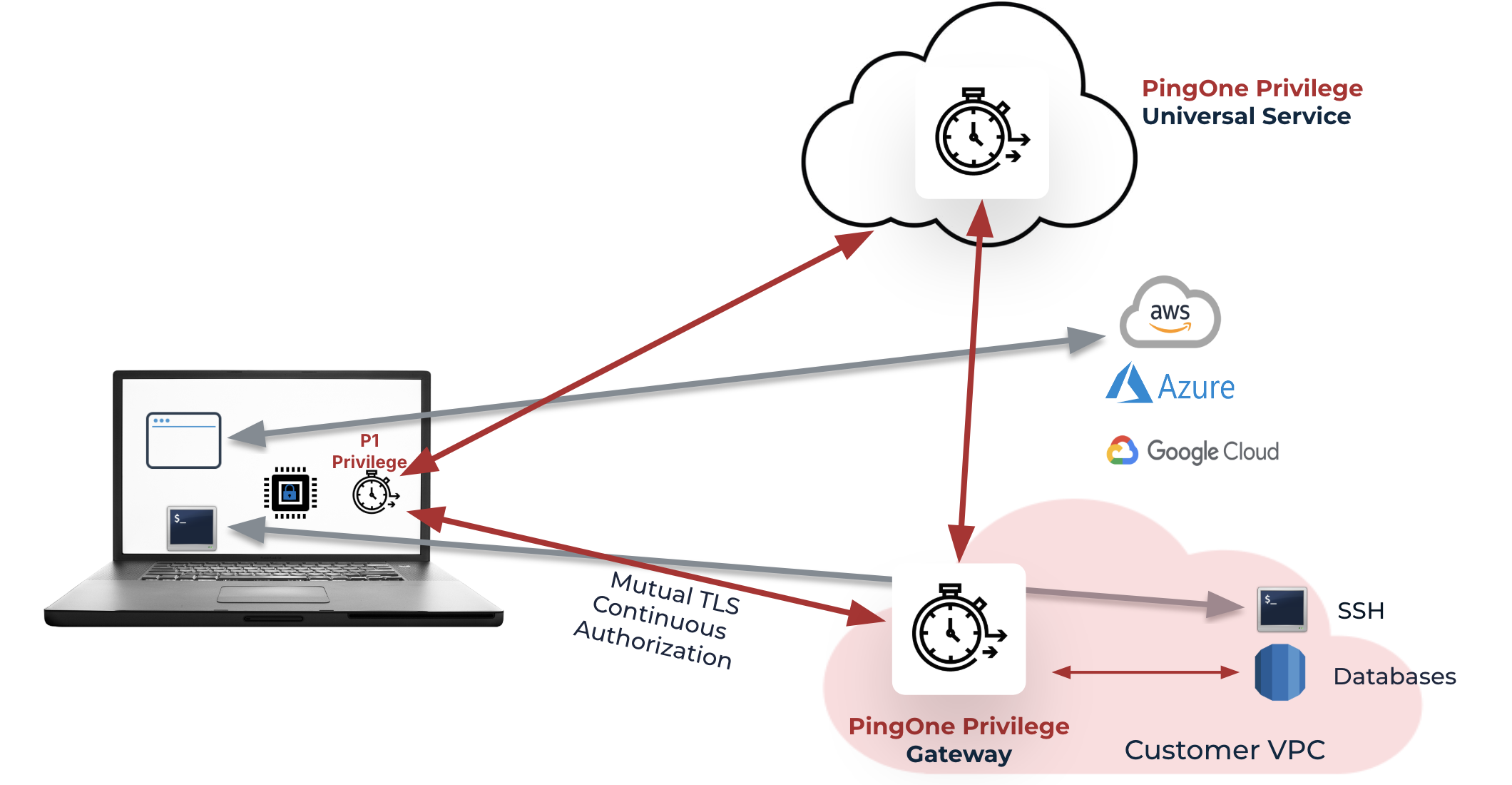
Key features of this model include:
-
Strong device and user identity verification.
-
Continuous authorization and session monitoring.
-
Enhanced security for sensitive environments.
Agentless deployment
The agentless model is ideal for organizations seeking a fast, low-friction rollout, or for environments where agents can’t be installed. Users access resources like SSH, cloud CLIs, and Kubernetes using the PingOne Privilege CLI (PCLI) shell utility.
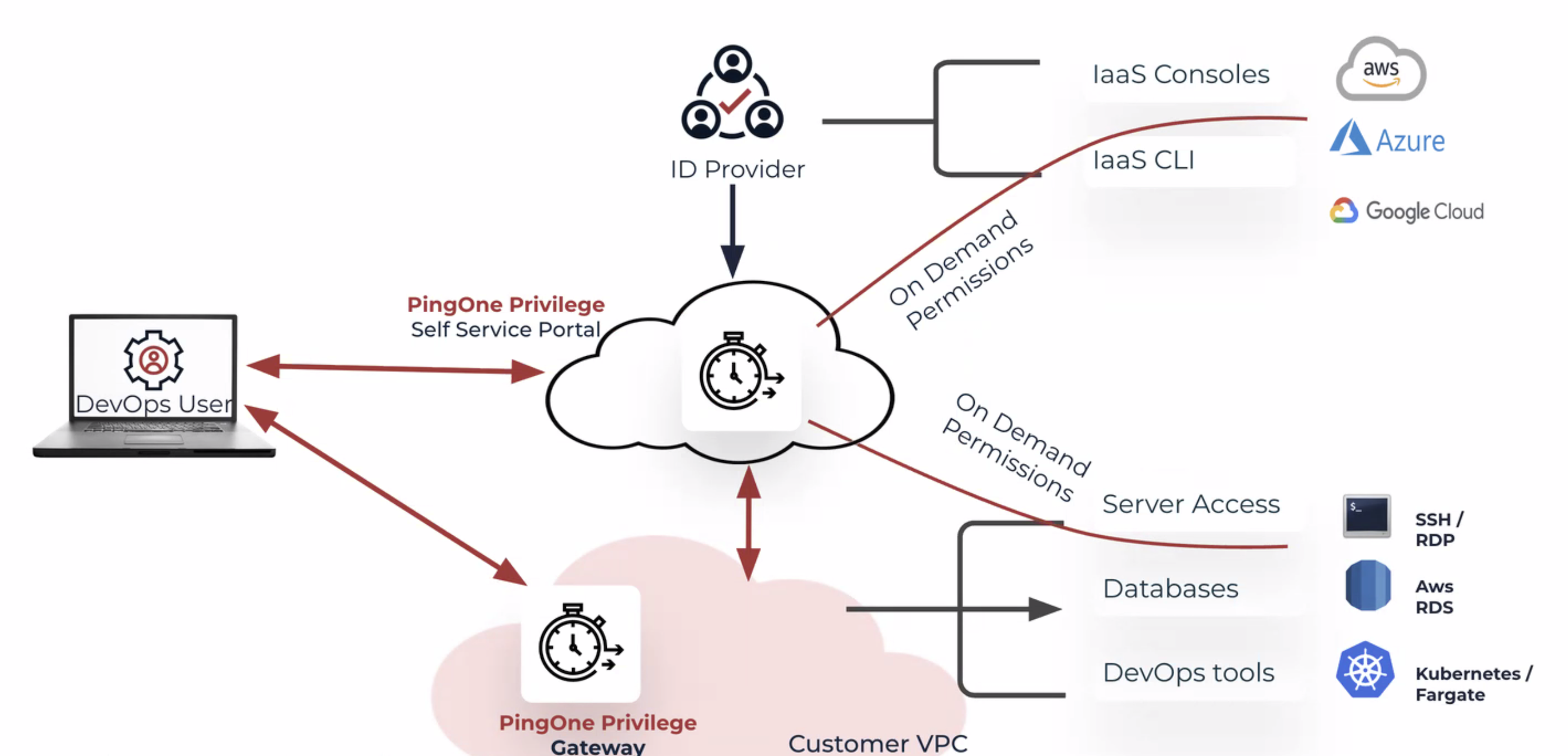
Key features of this model include:
-
Rapid deployment with no client-side software installation.
-
Flexibility for organizations with diverse device management policies.
-
A phased approach to privileged access management (PAM).
-
Some trade-offs in device identity assurance compared to the agent-based model.
Gateways and resource access
Both deployment models require gateways to access on-premises resources like servers, databases, and Kubernetes clusters. Direct access to cloud accounts (such as AWS, GCP, and Azure) is supported without a gateway. For resources behind a firewall, session logs are captured at the gateway for both models.