Key concepts
This section introduces the foundational ideas behind PingOne Privilege. These topics explain the challenges of securing cloud infrastructure and how PingOne Privilege addresses these with modern, identity-based solutions. Use this section to understand the principles and practices that guide secure access for both human and non-human identities.
Core concepts
Privileged access management (PAM)
PAM is a set of principles and practices to control, monitor, and secure access to critical resources by both human and machine identities. In short, PAM ensures that users have the right-sized permissions essential to access critical resources, such as infrastructures, applications, or data essential to an organization’s operations.
In simpler terms, PAM ensures that privileged users have access with the right-sized permissions to access critical resources. Critical resources are infrastructures, applications, or data essential to an organization’s operations, and could cause significant harm if compromised or unavailable.
Trusted Platform Module (TPM) and Secure Enclave
Modern Windows and Mac laptops include hardware-based security features like the TPM chip or Apple’s Secure Enclave. These provide a secure, tamper-resistant location for storing private keys, offering stronger security than file-based credentials because the keys can’t be directly read or extracted.
How PingOne Privilege works
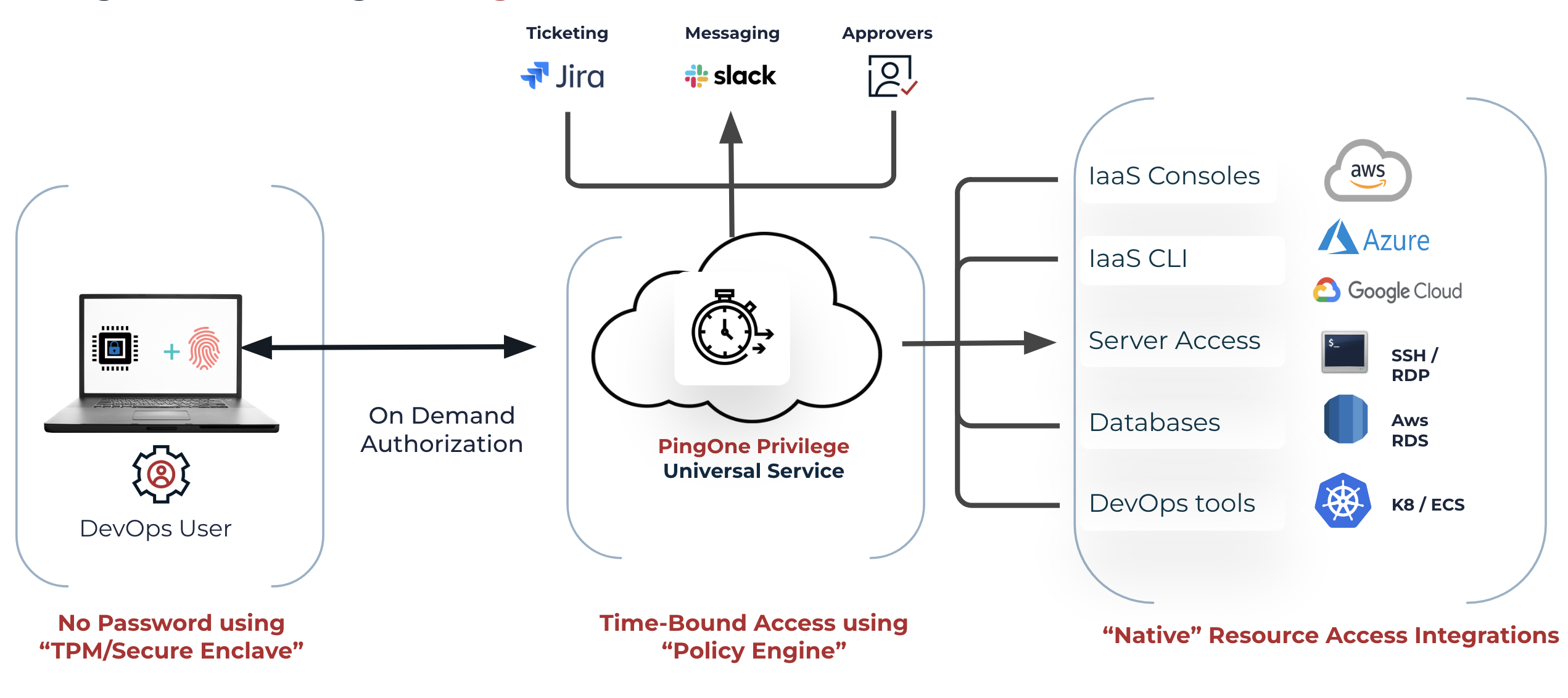
PingOne Privilege acts as an infrastructure access platform. Administrators use the self-service portal to provision access for users by setting policies or approving requests. When a user requests access, the workflow engine generates an on-demand, short-term token, granting secure access to the cloud infrastructure for a limited duration.
PingOne Privilege agent
The PingOne Privilege agent, installed during setup, creates and stores a non-exportable private key in the device’s TPM or Secure Enclave. The agent uses this key to establish a secure mutual TLS (mTLS) connection with PingOne Privilege, which verifies the identity of both the user and the device.
Agentless CLI
For situations where the agent can’t be installed, the agentless CLI provides secure access to resources like SSH, cloud CLIs, and Kubernetes. When a user authenticates with the agentless CLI, they’re redirected to PingOne SSO for authentication. After successful authentication, the user can access resources based on their permissions.