Configuring OpenID Provider information
You must configure OpenID Provider (OP) settings and information when configuring service provider (SP) browser single sign-on (SSO).
Steps
-
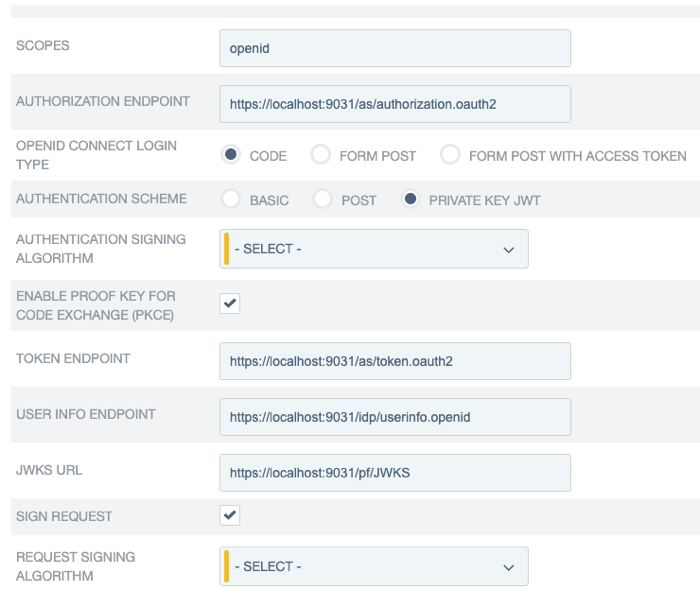
On the OpenID Provider Info tab, provide the scopes, the endpoints, and the authentication scheme.
If you clicked Load Metadata from the OpenID Provider (OP) on the General Info tab, the Scopes field and all endpoints are pre-populated, provided that the metadata contains the information.
Field Description Scopes
The scopes to be included in the OpenID Connect authentication and OAuth token requests to the OP. Multiple space-separated values are allowed.
The default value, without loading metadata from the OP, is
openid.For a list of OpenID Connect defined scopes, see the section about requesting claims using scope values in the OpenID Connection specification at Requesting Claims using Scope Values.
Authorization Endpoint
The authorization endpoint at the OP.
You can enter a relative path, starting with a forward slash, if you provide base URL on the General Info tab.
There is no default value without loading metadata from the OP.
OpenID Connect Login Type
The OpenID Connect client profile of the client. This client represents PingFederate and is created and managed at the OP.
-
If the client is configured to support the Basic Client profile, select Code.
The resulting value of the
response_typeparameter iscode. -
If the client is configured to support the Implicit Client profile, select Form POST.
The resulting value of the
response_typeparameter isid_token. -
If the client is configured to support the Implicit Client profile and the target application requires the associated access token, select Form POST with access token.
The resulting values of the
response_typeparameter areid_token token.
The default selection, without loading metadata from the OP, is Code.
Authentication Scheme
The client authentication method that PingFederate uses. Applicable and visible only to clients supporting the Basic Client profile.
-
Select Basic to submit credentials with HTTP Basic authentication.
-
Select POST to submit credentials with POST.
-
Select Private Key JWT to authenticate with the private_key_jwt Client Authentication method. For more information, see Client Authentication in the OpenID Connect specification.
The default selection, without loading metadata from the OP, is Basic.
Authentication Signing Algorithm
Select the algorithm that PingFederate uses to sign the JSON Web Token (JWT).
Private Key JWT is the chosen authentication scheme.
If PingFederate is deployed to run in a Java 8 or Java 11 runtime environment, or is integrated with a hardware security module (HSM) and configured to use static keys for OAuth and OpenID Connect (OIDC), additional RSASSA-PSS signing algorithms become available for selection. For more information on HSM integration and static keys, see Supported hardware security modules and Keys for OAuth and OpenID Connect.
If static keys for OAuth and OpenID Connect are enabled, Elliptic-curve cryptography (EC) algorithms that have not been configured with an active static keys are hidden.
Changes made in the static-key configuration might affect runtime transactions and require additional changes here. For more information, see Keys for OAuth and OpenID Connect.
Based on the chosen signing algorithm, PingFederate selects the signing JSON Web Key (JWK) from its JWK Set (JWKS) at runtime.
For the OP to validate the signed JWT, ensure that the OP can access the PingFederate JWKS endpoint, which returns the current JWKS. The PingFederate JWKS endpoint is located at
<Base URL>/pf/JWKS, where Base URL is defined on System → Server → Protocol Settings → Federation Info.For example, if the Base URL field value is https://www.example.com, the PingFederate JWKS endpoint is https://www.example.com/pf/JWKS. You can pass the PingFederate JWKS endpoint directly to the OP or have the OP contact the PingFederate OP configuration endpoint to obtain the information.
For more information, see OpenID Provider configuration endpoint.
Enable Proof Key for Code Exchange (PKCE)
Select this check box to enable PingFederate to send a SHA256 code challenge and corresponding code verifier as a Proof Key for Code Exchange (PKCE) to the OP during the Code authentication flow.
This check box is applicable and visible only when the OpenID Connect Login Type is Code.
When Load Metadata on the General Info tab is clicked, PingFederate displays the Enable PKCE check box if S256 is listed as a supported method in the
code_challenge_methods_supportedby the OP.Token Endpoint, UserInfo Endpoint, and JWKS URL
OAuth 2.0 and OpenID Connect 1.0 endpoints at the OP. For more information, see openid.net/connect.
- Token Endpoint
-
The Token Endpoint field is only visible and required for clients supporting the Basic Client profile. In other words, the OpenID Connect Login Type field is set to Code.
- UserInfo Endpoint
-
The UserInfo Endpoint field is optional. If omitted, PingFederate only has access to the end-user claims from the ID tokens.
- JWKS URL
-
The JWKS URL is required for PingFederate to validate the inbound ID tokens from the OP. If the OP signs its JWTs using an RSASSA-PSS signing algorithm, PingFederate must be deployed to run in a Java 8 or Java 11 runtime environment, or integrated with a hardware security module (HSM) and a static-key configuration for OAuth and OpenID Connect.
For more information on HSM integration and static keys, see Supported hardware security modules and Keys for OAuth and OpenID Connect, respectively.
There are no default values without loading metadata from the OP.
Sign Request
Select this check box to send request parameters as claims in a request object, a self-contained, signed JWT as one
requestquery parameter to the OP.When this optional configuration is enabled, the OP can validate the integrity of the request parameters based on the digital signature found in the signed JWT. For more information, see the section explaining passing a request object by value in the OpenID Connect specification at Passing a Request Object by Value.
This check box is not selected by default, in which case PingFederate sends request parameters with multiple query parameters, unsigned.
Request Signing Algorithm
Select the algorithm that PingFederate uses to sign the request object.
Applicable and visible only when the Sign Request check box is selected.
If PingFederate is deployed to run in a Java 8 or Java 11 runtime environment, or is integrated with a hardware security module (HSM) and configured to use static keys for OAuth and OIDC, additional RSASSA-PSS signing algorithms become available for selection. For more information on HSM integration and static keys, see Supported hardware security modules and Keys for OAuth and OpenID Connect.
If static keys for OAuth and OpenID Connect are enabled, Elliptic-curve cryptography (EC) algorithms that have not been configured with an active static keys are hidden.
Changes made in the static-key configuration might affect runtime transactions and require additional changes here. For more information, see Keys for OAuth and OpenID Connect.
PingFederate automatically selects the signing JSON web key (JWK) based on the selected signing algorithm from its JWK Set (JWKS).
In order for the OP to validate the signed request object, ensure that the OP can access your PingFederate’s JWKS URL, which returns the current set of JSON web keys. The PingFederate JWKS URL is located at
<Base URL>/pf/JWKS, where Base URL is defined on System → Server → Protocol Settings → Federation Info.For example, if the Base URL field value is https://www.example.com, the PingFederate JWKS URL is https://www.example.com/pf/JWKS. You can pass the JWKS URL directly to the OP or have the OP contact the PingFederate OpenID Provider configuration endpoint for it. For more information, see OpenID Provider configuration endpoint.
-
-
Optional: Remain on the OpenID Provider Info tab and specify the request parameters that are allowed to be included in the authentication requests to the OP under Request Parameters. For more information, see Configuring request parameters and SSO URLs.