Prepare to install
Before you install, make sure your installation meets the requirements in the release notes.
Create an IG service account
To limit the impact of a security breach, install and run IG from a dedicated service account. This is optional when evaluating IG, but essential in production installations.
A hacker is constrained by the rights granted to the user account where IG runs; therefore, never run IG as root user.
-
In a terminal window, use a command similar to the following to create a service account:
-
Linux
-
Windows
$ sudo /usr/sbin/useradd \ --create-home \ --comment "Account for running IG" \ --shell /bin/bash IG
> net user username password /add /comment:"Account for running IG"
-
-
Apply the principle of least privilege to the account, for example:
-
Read/write permissions on the installation directory,
/path/to/identity-gateway-2023.11.2. -
Execute permissions on the scripts in the installation
bindirectory,/path/to/identity-gateway-2023.11.2/bin.
-
Prepare the network
Configure the network to include hosts for IG, AM, and the sample application. For more information about host files, refer to the Wikipedia entry, Hosts (file).
-
Add the following entry to your host file:
-
Linux
-
Windows
/etc/hosts%SystemRoot%\system32\drivers\etc\hosts127.0.0.1 localhost ig.example.com app.example.com am.example.com -
Set up Identity Cloud
This documentation contains procedures for setting up items in ForgeRock Identity Cloud that you can use with IG. For more information about setting up Identity Cloud, refer to the ForgeRock Identity Cloud docs.
Authenticate an IG agent to Identity Cloud
|
IG agents are automatically authenticated to Identity Cloud by a non-configurable authentication module. Authentication chains and modules are deprecated in Identity Cloud and replaced by journeys. You can now authenticate IG agents to Identity Cloud with a journey. The procedure is currently optional, but will be required when authentication chains and modules are removed in a future release of Identity Cloud. For more information, refer to Identity Cloud’s Journeys. |
This section describes how to create a journey to authenticate an IG agent to Identity Cloud. The journey has the following requirements:
-
It must be called
Agent -
Its nodes must pass the agent credentials to the Agent Data Store Decision node.
When you define a journey in Identity Cloud, that same journey is used for all instances of IG, Java agent, and Web agent. Consider this point if you change the journey configuration.
-
Log in to the Identity Cloud admin UI as an administrator.
-
Click Journeys > New Journey.
-
Add a journey with the following information and click Create journey:
-
Name:
Agent -
Identity Object: The user or device to authenticate.
-
(Optional) Description: Authenticate an IG agent to Identity Cloud
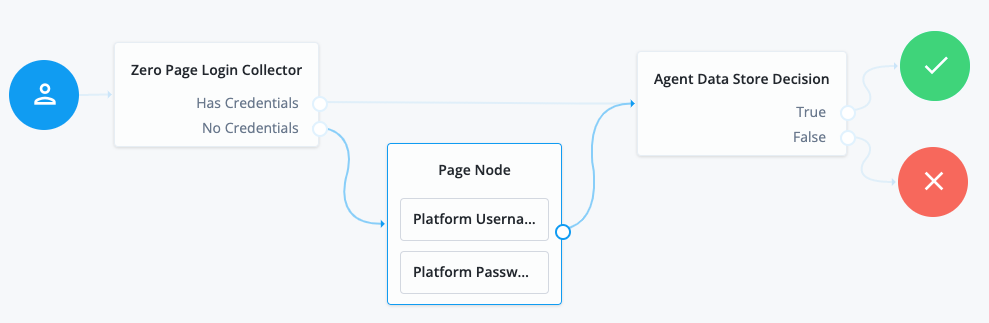
The journey designer is displayed, with the
Startentry point connected to theFailureexit point, and aSuccessnode. -
-
Using the Filter nodes bar, find and then drag the following nodes from the Components panel into the designer area:
-
Zero Page Login Collector node to check whether the agent credentials are provided in the incoming authentication request, and use their values in the following nodes.
This node is required for compatibility with Java agent and Web agent.
-
Page node to collect the agent credentials if they are not provided in the incoming authentication request, and use their values in the following nodes.
-
Agent Data Store Decision node to verify the agent credentials match the registered IG agent profile.
Many nodes can be configured in the panel on the right side of the page. Unless otherwise stated, do not configure the nodes, and use only the default values. -
-
Drag the following nodes from the Components panel into the Page node:
-
Platform Username node to prompt the user to enter their username.
-
Platform Password node to prompt the user to enter their password.
-
-
Connect the nodes as follows and save the journey:
Register an IG agent in Identity Cloud
This procedure registers an agent that acts on behalf of IG.
-
Log in to the Identity Cloud admin UI as an administrator.
-
Click Gateways & Agents > New Gateway/Agent > Identity Gateway > Next, and add an agent profile:
-
ID: agent-name
-
Password: agent-password
Use secure passwords in a production environment. Consider using a password manager to generate secure passwords.
-
-
Click Save Profile > Done. The agent profile page is displayed.
-
To add a redirect URL for CDSSO, go to the agent profile page and add the URL.
-
To change the introspection scope, click Native Consoles > Access Management, and update the agent in the AM admin UI. By default, the agent can introspect OAuth 2.0 tokens issued to any client, in the realm and subrealm where it is created.
-
To direct login to a custom URL instead of the default AM login page, click Native Consoles > Access Management. Select the agent in the AM admin UI and configure Login URL Template for CDSSO.
Set up a demo user in Identity Cloud
This procedure sets up a demo user in the alpha realm.
-
Log in to the Identity Cloud admin UI as an administrator.
-
Go to Identities > Manage > Alpha realm - Users, and add a user with the following values:
-
Username:
demo -
First name:
demo -
Last name:
user -
Email Address:
demo@example.com -
Password:
Ch4ng3!t
-
Set up AM
This documentation contains procedures for setting up items in AM that you can use with IG. For more information about setting up AM, refer to the Access Management docs.
Authenticate an IG agent to AM
|
This section describes how to create an authentication tree to authenticate an IG agent to AM. The tree has the following requirements:
-
It must be called
Agent -
Its nodes must pass the agent credentials to the Agent Data Store Decision node.
When you define a tree in AM, that same tree is used for all instances of IG, Java agent, and Web agent. Consider this point if you change the tree configuration.
-
On the Realms page of the AM admin UI, choose the realm in which to create the authentication tree.
-
On the Realm Overview page, click Authentication > Trees > Create tree.
-
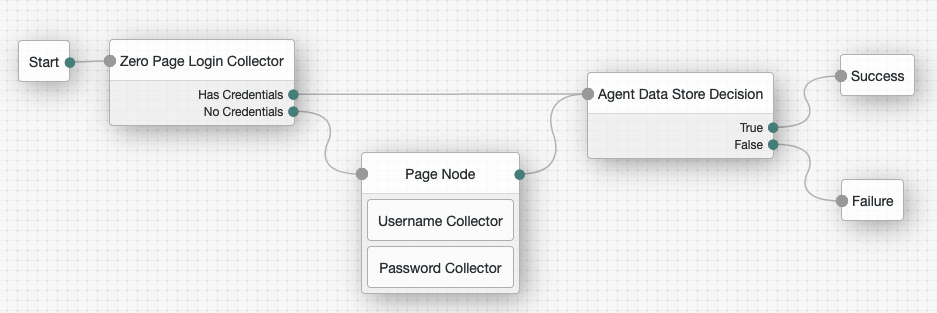
Create a tree named
Agent.The authentication tree designer is displayed, with the
Startentry point connected to theFailureexit point, and aSuccessnode.The authentication tree designer provides the following features on the toolbar:
Button Usage 
Lay out and align nodes according to the order they are connected.

Toggle the designer window between normal and full-screen layout.

Remove the selected node. Note that the
Startentry point cannot be deleted. -
Using the Filter bar, find and then drag the following nodes from the Components panel into the designer area:
-
Zero Page Login Collector node to check whether the agent credentials are provided in the incoming authentication request, and use their values in the following nodes.
This node is required for compatibility with Java agent and Web agent.
-
Page node to collect the agent credentials if they are not provided in the incoming authentication request, and use their values in the following nodes.
-
Agent Data Store Decision node to verify the agent credentials match the registered IG agent profile.
Many nodes can be configured in the panel on the right side of the page. Unless otherwise stated, do not configure the nodes and use only the default values. -
-
Drag the following nodes from the Components panel into the Page node:
-
Username Collector node to prompt the user to enter their username.
-
Password Collector node to prompt the user to enter their password.
-
-
Connect the nodes as follows and save the tree:
Register an IG agent in AM 7 and later
In AM 7 and later versions, follow these steps to register an agent that acts on behalf of IG.
-
In the AM admin UI, select the top-level realm, and then select Applications > Agents > Identity Gateway.
-
Add an agent with the following configuration, leaving other options blank or with the default value:
-
For SSO
-
For CDSSO
-
Agent ID :
ig_agent -
Password :
password
-
Agent ID :
ig_agent -
Password :
password -
Redirect URL for CDSSO :
https://ig.ext.com:8443/home/cdsso/redirect -
Login URL Template for CDSSO: Configure this property to direct login to a custom URL instead of the default AM login page.
-
Register an IG agent in AM 6.5 and earlier
In AM 6.5 and earlier versions, follow these steps to register an agent that acts on behalf of IG.
-
In the AM admin UI, select the top-level realm, and then select Applications > Agents > Java (or J2EE ).
-
Add an agent with the following configuration, leaving other options blank or with the default value:
-
For SSO
-
For CDSSO
-
Agent ID :
ig_agent -
Agent URL :
http://ig.example.com:8080/agentapp -
Server URL :
http://am.example.com:8088/openam -
Password :
password
-
Agent ID :
ig_agent_cdsso -
Agent URL :
http://ig.ext.com:8080/agentapp -
Server URL :
http://am.example.com:8088/openam -
Password :
password -
Login URL Template for CDSSO: Configure this property to direct login to a custom URL instead of the default AM login page.
-
-
On the Global tab, deselect Agent Configuration Change Notification.
This option stops IG from being notified about agent configuration changes in AM. IG doesn’t need these notifications.
-
(For CDSSO) On the SSO tab, select the following values:
-
Cross Domain SSO : Deselect this option
-
CDSSO Redirect URI :
/home/cdsso/redirect
-
-
(For CDSSO and policy enforcement) On the SSO tab, select the following values:
-
Cross Domain SSO : Deselect this option
-
CDSSO Redirect URI :
/home/pep-cdsso/redirect
-
Set up a demo user in AM
AM is provided with a demo user in the top-level realm, with the following credentials:
-
ID/username:
demo -
Last name:
user -
Password:
Ch4ng31t -
Email address:
demo@example.com -
Employee number:
123
For information about how to manage identities in AM, refer to AM’s Identity stores.
Find the AM session cookie name
In routes that use AmService, IG retrieves AM’s SSO
cookie name from the ssoTokenHeader property or from AM’s
/serverinfo/* endpoint.
In other circumstances where you need to find the SSO cookie name, access
http://am-base-url/serverinfo/*. For example, access the
AM endpoint with curl:
$ curl http://am.example.com:8088/openam/json/serverinfo/*