Setting up SSO to PingDirectory from PingOne
To set up single sign-on (SSO) access from the administrative console home page to PingDirectory, configure PingOne and test the sign-on experience.
Before you begin
Ensure that you have:
-
A PingDirectory server that accepts LDAPS connections. This server will host the admin console that is being configured for SSO.
-
A PingOne account. For more information, see Getting Started with PingOne.
|
You can use groups to organize user identities, as explained in Groups. You can also set access to applications, as explained in Application access control. |
About this task
During this setup:
-
Step 2 sets up a matching user between PingOne and the PingDirectory environments that allows the server’s
All Admin Usersidentity mapper to map the PingOne ID token to a PingDirectory LDAP user. -
Steps 3-8 set up the OpenID Connect (OIDC) client as described in Single sign-on with the administrative console.
-
Steps 9-11 configure both the administrative console’s configuration requirements (except for the
ldap.serverproperty) and the PingDirectory server’s configuration requirements.These configuration properties are outlined in more detail in Single sign-on with the administrative console.
Set up SSO to the PingDirectory administrative console from PingOne using the following steps.
Steps
-
From the admin console home page, add PingOne and PingDirectory:
Choose from:
-
To add a new environment for PingOne SSO and PingDirectory:
-
On the PingOne console home page, click Add Environment.
-
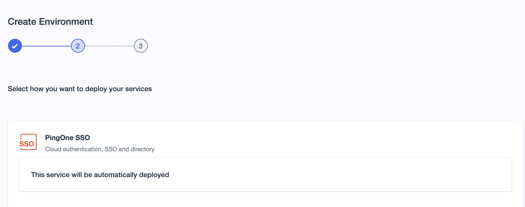
Select Customer solution, and then click Next.
-
Click Next.
-
Enter an Environment Name and Description, then in the labeled lists, select an Environment Type, Region, and License.
-
Click Finish.
PingOne SSO, PingOne Risk, PingOne Verify, and PingOne MFA are automatically deployed.
-
On the PingOne console home page, in the Your Environments list, select your new environment, and then click the icon.
-
Click Add next to PingDirectory.
Services that have been already added have a green check mark icon next to the service name instead of Add.
-
Click Finish.
-
-
To add PingOne SSO and PingDirectory to an existing environment:
-
On the PingOne console home page, in the Your Environments list, select the environment, and then click the icon.
-
Click Add next to PingOne SSO and PingDirectory.
Services that have been already added have a green check mark icon next to the service name instead of Add.
-
Click Finish.
-
-
Click Add Admin UI Link, and in the Enter Admin URL field, enter
https://<hostname>:<port>/console/login, replacing the bracketed variables with the PingDirectory server’s hostname and HTTP port.You can specify the LDAP server to bind to using the query parameters
ldap-hostnameandldaps-portwhen the administrative console is configured for SSO. By binding to the LDAP server, you can use a single console instance to administer multiple PingDirectory servers. An LDAPS scheme is always assumed because an encrypted connection is always required for SSO. Using these parameters, you can specify the URL as follows.https://<hostname>:<port>/console?ldap-hostname=<my-ldap-host>&ldaps-port=<my-ldaps-port>
-
Click Save.
-
-
To configure the matching administrator accounts for PingOne and the PingDirectory server, go to the PingOne dashboard for the environment that will be used with the PingDirectory server and repeat the following steps for each PingOne user for whom you want to enable SSO:
-
On the admin console home page, select the appropriate environment and click the PingOne icon.
-
In PingOne, go to Identities.
-
Select the administrative user you want to configure and click the Expand icon.
-
Run the following
dsconfigcommand and replace the bracketed fields with the values of the administrative user.~/<pd_install>/dsconfig create-root-dn-user --user-name <Username> \ --set first-name:<Given Name> \ --set last-name:<Family Name>
-
-
Register the admin console with PingOne.
-
Go to Adding an application and follow the instructions to add an OIDC app.
-
Enter the application properties, as shown in this table.
Property Value Application Name
PingDirectory Administrative Console
Description
Application for the PingDirectory Administrative Console
Redirect URLs
https://<hostname>:<port>/console/oidc/cbReplace the bracketed values in Redirect URLs with your PingDirectory server’s hostname and HTTP port. To find the port, run the
statuscommand from thebindirectory.Step 0.0.0.0:11443 : HTTPS : Enabled : HTTPS Connection Handler
Attribute Mapping
'Username' = 'sub'No OIDC scopes are required for PingOne to grant access to the PingDirectory console.
-
-
Select the newly-created PingDirectory Administrative Console application in the Applications list, and go to the Configuration tab.
-
To edit the listed configuration properties, click the Pencil icon.
Edit the configuration properties using the values in this table.
Property Value Response Type
Select the Code check box.
Grant Type
Select the Authorization Code check box.
Token Endpoint Authentication Method
Click Client Secret Basic.
For more information about updating the properties of your new application, see Editing an application - OIDC.
-
Click Save.
-
Click the toggle to enable user access to the application.
-
On the Configuration tab, record the values for these application properties to use in step 10:
-
Issuer
-
Client ID
-
Client Secret
-
-
Create a copy of the
PingDirectory/config/sample-dsconfig-batch-files/enable-pingone-admin-console-sso.dsconfigfile, leaving the source file as-is. -
Open the copy of the file and replace the bracketed values with the values from step 8.
# Create an ID token validator suitable for verifying ID tokens generated # by the PingOne service. The "All Admin Users" identity mapper will be used # to match users that authenticate with PingOne to either root DN users or # topology admin users defined in the server configuration. dsconfig create-id-token-validator \ --validator-name "PingOne ID Token Validator" \ --type ping-one \ --set enabled:true \ --set "identity-mapper:All Admin Users" \ --set evaluation-order-index:1 \ --set issuer-url:[PING_ONE_APPLICATION_ISSUER_URL] [...] # Configure the Administrative Console with your application's client # credentials and issuer URI. dsconfig set-web-application-extension-prop \ --extension-name Console \ --set sso-enabled:true \ --set oidc-client-id:[PING_ONE_APPLICATION_CLIENT_ID] \ --set oidc-client-secret:[PING_ONE_APPLICATION_CLIENT_SECRET] \ --set oidc-issuer-url:[PING_ONE_APPLICATION_ISSUER_URL]
-
Run the file using the following command.
dsconfig --batch-file \ enable-pingone-admin-console-sso-copy.dsconfig \ --no-prompt -
Select the link to the PingDirectory server from the PingOne solutions home page.
Result:
A PingOne sign-on page opens.
-
Sign on using the administrative user credentials.
Result:
The PingDirectory server administrative console home page opens.