Snowflake connector
| This is a SaaS common connector. |
The Snowflake connector allows you to manage users, grant and revoke roles and database roles, and synchronize data between IDM or Advanced Identity Cloud and Snowflake.
Snowflake requirements
To configure the connector, you need a Snowflake account with the SYSADMIN role. Complete the following steps to gather the required values, then use them to configure the connector.
-
Generate an unencrypted RSA key pair using OpenSSL:
-
Generate a private key:
openssl genrsa -out rsa_key.pem 2048 -
Extract the public key:
openssl rsa -in rsa_key.pem -pubout -out rsa_key.pub
-
-
In your Snowflake platform:
-
Set
SYSADMINas default role:ALTER USER YOUR_USERNAME SET DEFAULT_ROLE = 'SYSADMIN'; -
Set the public key for the user:
ALTER USER YOUR_USERNAME SET RSA_PUBLIC_KEY='-----BEGIN PUBLIC KEY-----YOUR_PUBLIC_KEY-----END PUBLIC_KEY----'; -
Save the snowflake context URL subdomain:
-
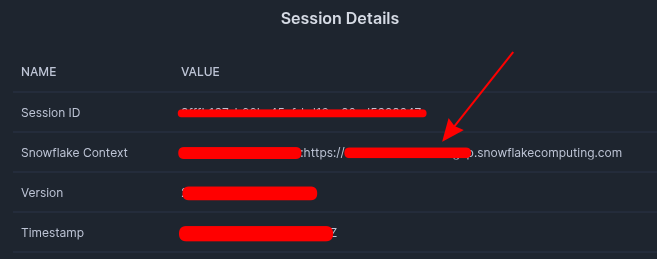
Go to Nav > Session details.
-
In the Session Details modal, save the subdomain value of the Snowflake Context field.
Show Me
-
-
Define the claims:
-
Query and save the account locator:
SELECT CURRENT_ORGANIZATION_NAME() || '-' || CURRENT_ACCOUNT_NAME(); -
Query and save the
RSA_PUBLIC_KEY_FP:DESCRIBE USER YOUR_USERNAME; -
Construct the claims using the account locator and
RSA_PUBLIC_KEY_FP:-
Issuer:
account_locator.username.RSA_PUBLIC_KEY_FP -
Subject:
account_locator.username
-
-
-
Install the Snowflake connector
|
To check for an Advanced Identity Cloud application for this connector, refer to: |
You can download any connector from Backstage, but some are included in the default deployment for Advanced Identity Cloud, IDM, or RCS. When using an included connector, you can skip installing it and move directly to configuration.
| Connector | IDM | RCS |
|---|---|---|
No |
No |
Download the connector .jar file from Backstage.
-
If you’re running the connector locally, place it in the
/path/to/openidm/connectorsdirectory, for example:mv ~/Downloads/snowflake-connector-1.5.20.34.jar /path/to/openidm/connectors/
-
If you’re using a remote connector server (RCS), place it in the
/path/to/openicf/connectorsdirectory on the RCS.
Configure the Snowflake connector
Create a connector configuration using the IDM admin UI:
-
From the navigation bar, click Configure > Connectors.
-
On the Connectors page, click New Connector.
-
On the New Connector page, type a Connector Name.
-
From the Connector Type list, select Snowflake Connector - 1.5.20.34.
-
Complete the Base Connector Details and any applicable Additional Options.
For a list of all configuration properties, refer to Snowflake Connector Configuration. -
Click Save.
When your connector is configured correctly, the connector displays as Active in the admin UI.
Refer to this procedure to create a connector configuration over REST.
Connection Details
| Property | Description |
|---|---|
|
The service endpoint URI. |
|
The role for performing queries. |
|
The authentication method. Must be |
|
The private key generated during the Snowflake requirements. |
|
The access token expiration time in seconds. |
|
The algorithm type. Must be |
|
The key type. Must be |
|
The claims to include in the payload to sign and get the access token. This object must contain the following keys:
Example
jwtClaimsLearn more about obtaining these values in Snowflake requirements. |
|
A list of databases to exclude from operations. |
|
The warehouse name that provides computing resources. |
|
The timeout for the underlying HTTPS connection in seconds. Defaults to |
Example Snowflake configuration
This excerpt shows a sample Snowflake connector configuration:
{
"configurationProperties" : {
"tokenExpiration" : null,
"accessToken" : null,
"serviceUri" : "https://your.tenant.snowflakecomputing.com/api/v2",
"login" : null,
"password" : null,
"authenticationMethod" : "JWT_TOKEN",
"tokenEndpoint" : null,
"clientId" : null,
"clientSecret" : null,
"refreshToken" : null,
"authToken" : null,
"acceptSelfSignedCertificates" : false,
"disableHostNameVerifier" : false,
"disableHttpCompression" : false,
"clientCertAlias" : null,
"clientCertPassword" : null,
"httpProxyHost" : null,
"httpProxyPort" : null,
"httpProxyUsername" : null,
"httpProxyPassword" : null,
"connectionTimeout" : "30",
"grantType" : null,
"scope" : null,
"authorizationTokenPrefix" : "Bearer",
"useBasicAuthForOauthTokenNeg" : true,
"jwtKey" : null,
"customGrantType" : null,
"defaultHeader" : null,
"keyAlgorithm" : "RSA",
"jwtPem" : "MIIEvAIBADANB...",
"jwtExpiration": 60,
"jwtAlgorithm": "RS256",
"jwtClaims": {
"iss": "XXXXX-XXXXX.USERNAME.SHA256:RSA_PUBLIC_KEY_FP",
"sub": "XXXXX-XXXXX.USERNAME"
},
"excludeDatabases": [
"DATABASE NAME TO EXCLUDE"
],
"role": "USERADMIN",
"warehouse": null
}
}Mapping
From Snowflake users to IDM or Advanced Identity Cloud users
Attributes Grid: Where the columns represent the attribute name mapped from source to target and the necessary data transformation to synchronize successfully.
| SOURCE | TARGET | TRANSFORMATION SCRIPT |
|---|---|---|
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
From IDM or Advanced Identity Cloud users to Snowflake users
Attributes Grid: Where the columns represent the attribute name mapped from source to target and the necessary data transformation to synchronize successfully.
| SOURCE | TARGET | TRANSFORMATION SCRIPT |
|---|---|---|
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
From Snowflake roles to IDM or Advanced Identity Cloud roles
Attributes Grid: Where the columns represent the attribute name mapped from source to target and the necessary data transformation to synchronize successfully.
| SOURCE | TARGET | TRANSFORMATION SCRIPT |
|---|---|---|
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
From Snowflake database roles to IDM or Advanced Identity Cloud database roles
Attributes Grid: Where the columns represent the attribute name mapped from source to target and the necessary data transformation to synchronize successfully.
| SOURCE | TARGET | TRANSFORMATION SCRIPT |
|---|---|---|
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
|
|
N/A |
Test the Snowflake connector
Test that the configuration is correct by running the following command:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Accept-API-Version: resource=1.0" \
--request POST \
"http://localhost:8080/openidm/system/snowflake?_action=test"
{
"name": "snowflake",
"enabled": true,
"config": "config/provisioner.openicf/snowflake",
"connectorRef": {
"bundleVersion": "1.5.20.34",
"bundleName": "org.forgerock.openicf.connectors.snowflake-connector",
"connectorName": "org.forgerock.openicf.connectors.snowflake.SnowflakeConnector"
},
"displayName": "org.forgerock.openicf.connectors.snowflake.SnowflakeConnector",
"objectTypes": [
"__DATABASE_ROLE__",
"__ACCOUNT__",
"__ALL__",
"__ROLES__"
],
"ok": true
}
Snowflake remote connector
If you want to run this connector outside of PingOne Advanced Identity Cloud or IDM, you can configure the Snowflake connector as a remote connector. Java Connectors installed remotely on a Java Connector Server function identically to those bundled locally within PingOne Advanced Identity Cloud or installed locally on IDM.
You can download the Snowflake connector from here.
Refer to Remote connectors for configuring the Snowflake remote connector.
Configure connection pooling
The Snowflake connector supports HTTP pooling, which can substantially improve the performance of the connector. Learn more about the basic connection pooling configuration and different pooling mechanisms described in Connection pooling configuration.
If the command returns "ok": true, your connector is configured correctly and can authenticate to the Snowflake
environment.
Use the Snowflake connector
You can use the Snowflake connector to perform various actions on the following Snowflake resources:
| Connector resource | Snowflake resource type |
|---|---|
|
|
|
|
|
Users
Create a Snowflake user
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request POST \
--data '{
"__NAME__": "JOHNDOE",
"display_name": "john doe",
"first_name": "john",
"last_name": "doe",
"login_name": "john.doe",
"email": "john.doe@example.com",
"disabled" : true,
"mins_to_unlock" : 60,
"days_to_expiry": 99,
"default_warehouse" : "COMPUTE_WH",
"default_namespace" : "TEST",
"default_role" : "USERADMIN",
"comment": "This is a new user",
"roles" : [
"ACCOUNTADMIN"
],
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"default_secondary_roles": [
"ALL"
]
}'\
'http://localhost:8080/openidm/system/snowflake/__ACCOUNT__?_action=create'
{
"_id": "JOHNDOE",
"__NAME__": "JOHNDOE",
"owner": "USERADMIN",
"last_name": "doe",
"first_name": "john",
"email": "john.doe@example.com",
"default_warehouse": "COMPUTE_WH",
"default_namespace": "TEST",
"default_role": "USERADMIN",
"default_secondary_roles": [
"ALL"
],
"roles": [
"ACCOUNTADMIN"
],
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"snowflake_lock": false,
"last_success_login": null,
"must_change_password": false,
"disabled": true,
"display_name": "",
"mins_to_unlock": 60,
"days_to_expiry": 99,
"locked_until_time": "2026-01-20 14:22:10.196 UTC",
"created_on": "2026-01-20 14:17:10.184 UTC",
"expires_at_time": "2026-01-30 14:17:10.196 UTC",
"comment": "This is a new user"
}
|
When you create a new user, you must specify at least the |
Update a Snowflake user
The PUT operation replaces the entire user object. The request body must contain all modifiable attributes for the user. Any omitted attributes are removed or reset to their default values.
The following user attributes can’t be modified:
-
created_on -
__NAME__ -
snowflake_lock -
owner -
locked_until_time -
last_success_login -
expires_at_time
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--header "If-Match:*" \
--request PUT \
--data '{
"display_name": "john doe",
"first_name": "john",
"last_name": "doe",
"login_name": "john.doe",
"email": "john.doe@example.com",
"disabled" : true,
"mins_to_unlock" : 120,
"days_to_expiry": 99,
"default_warehouse" : "COMPUTE_WH",
"default_namespace" : "TEST",
"default_role" : "USERADMIN",
"comment": "User updated",
"roles" : [
"ACCOUNTADMIN",
"SYSADMIN"
],
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"default_secondary_roles": [
"ALL"
]
}' \
"http://localhost:8080/openidm/system/snowflake/__ACCOUNT__/JOHNDOE"
{
"_id": "JOHNDOE",
"__NAME__": "JOHNDOE",
"owner": "USERADMIN",
"last_name": "doe",
"first_name": "john",
"email": "john.doe@example.com",
"default_warehouse": "COMPUTE_WH",
"default_namespace": "TEST",
"default_role": "USERADMIN",
"default_secondary_roles": [
"ALL"
],
"roles": [
"ACCOUNTADMIN",
"SYSADMIN"
],
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"snowflake_lock": false,
"last_success_login": null,
"must_change_password": false,
"disabled": true,
"display_name": "",
"mins_to_unlock": 120,
"days_to_expiry": 99,
"locked_until_time": "2026-01-20 14:22:10.196 UTC",
"created_on": "2026-01-20 14:17:10.184 UTC",
"expires_at_time": "2026-01-30 14:17:10.196 UTC",
"comment": "User updated"
}
Query all Snowflake user IDs
The following example queries all Snowflake users:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__ACCOUNT__?_queryId=query-all-ids"
{
"result": [
{
"_id": "JOHNDOE"
},
{
"_id": "JANEDOE"
},
...
],
"resultCount": 999,
"pagedResultsCookie": "",
"totalPagedResultsPolicy": "NONE",
"totalPagedResults": -1,
"remainingPagedResults": -1
}
Read Snowflake users
The following example reads all Snowflake users, by default 10.000:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__ACCOUNT__?_queryFilter=true"
{
"result": [
{
"_id": "JOHNDOE",
"__NAME__": "JOHNDOE",
"owner": "USERADMIN",
"comment": "John Doe user",
"email": "john.doe@example.com",
"last_name": "DOE",
"first_name": "JOHN",
"login_name": "JOHNDOE",
"display_name": "JOHN DOE",
"must_change_password": false,
"snowflake_lock": false,
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"roles": [
"ACCOUNTADMIN"
],
"default_secondary_roles": [
"ALL"
],
"default_role": "USERADMIN",
"default_namespace": "default_namespace",
"default_warehouse": "COMPUTE_WH",
"mins_to_unlock": null,
"last_success_login": null,
"disabled": true,
"locked_until_time": "2026-01-20 14:22:10.196 UTC",
"created_on": "2026-01-20 14:17:10.184 UTC",
"expires_at_time": "2026-01-30 14:17:10.196 UTC",
"days_to_expiry": 99
},
...
{
"_id": "JANEDOE",
"__NAME__": "JANEDOE",
"owner": "USERADMIN",
"comment": "Jane Doe user",
"email": "jane.doe@example.com",
"last_name": "DOE",
"first_name": "JANE",
"login_name": "JANEDOE",
"display_name": "JANE DOE",
"must_change_password": false,
"snowflake_lock": false,
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"roles": [
"SYSADMIN"
],
"default_secondary_roles": [
"ALL"
],
"default_role": "SYSADMIN",
"default_namespace": "default_namespace",
"default_warehouse": "COMPUTE_WH",
"mins_to_unlock": null,
"last_success_login": null,
"disabled": true,
"locked_until_time": "2026-01-20 14:22:10.196 UTC",
"created_on": "2026-01-20 14:17:10.184 UTC",
"expires_at_time": "2026-01-30 14:17:10.196 UTC",
"days_to_expiry": 99
}
],
"resultCount": 999,
"pagedResultsCookie": "",
"totalPagedResultsPolicy": "NONE",
"totalPagedResults": -1,
"remainingPagedResults": -1
}
Read a single Snowflake user
The following example reads Snowflake user JOHNDOE:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__ACCOUNT__/JOHNDOE"
{
"_id": "JOHNDOE",
"__NAME__": "JOHNDOE",
"owner": "USERADMIN",
"last_name": "doe",
"first_name": "john",
"email": "john.doe@example.com",
"default_warehouse": "COMPUTE_WH",
"default_namespace": "TEST",
"default_role": "USERADMIN",
"default_secondary_roles": [
"ALL"
],
"roles": [
"ACCOUNTADMIN"
],
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"snowflake_lock": false,
"last_success_login": null,
"must_change_password": false,
"disabled": true,
"display_name": "",
"mins_to_unlock": 60,
"days_to_expiry": 99,
"locked_until_time": "2026-01-20 14:22:10.196 UTC",
"created_on": "2026-01-20 14:17:10.184 UTC",
"expires_at_time": "2026-01-30 14:17:10.196 UTC",
"comment": "This is a new user"
}
Delete a Snowflake user
The following example delete a Snowflake user JOHNDOE:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--header "If-Match: *" \
--request DELETE \
"http://localhost:8080/openidm/system/snowflake/__ACCOUNT__/JOHNDOE"
{
"_id": "JOHNDOE",
"__NAME__": "JOHNDOE",
"owner": "USERADMIN",
"last_name": "doe",
"first_name": "john",
"email": "john.doe@example.com",
"default_warehouse": "COMPUTE_WH",
"default_namespace": "TEST",
"default_role": "USERADMIN",
"default_secondary_roles": [
"ALL"
],
"roles": [
"ACCOUNTADMIN"
],
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER"
],
"snowflake_lock": false,
"last_success_login": null,
"must_change_password": false,
"disabled": true,
"display_name": "john doe",
"mins_to_unlock": 60,
"days_to_expiry": 99,
"locked_until_time": "2026-01-20 14:22:10.196 UTC",
"created_on": "2026-01-20 14:17:10.184 UTC",
"expires_at_time": "2026-01-30 14:17:10.196 UTC",
"comment": "This is a new user"
}
Roles
Query all roles IDs
The following example queries all Snowflake roles IDs:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__ROLES__?_queryId=query-all-ids"
{
"result": [
{
"_id": "ACCOUNTADMIN"
},
...
{
"_id": "USERADMIN"
}
],
"resultCount": 7,
"pagedResultsCookie": null,
"totalPagedResultsPolicy": "NONE",
"totalPagedResults": -1,
"remainingPagedResults": -1
}
Query a specific role
The following example reads Snowflake role ACCOUNTADMIN:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__ROLES__/ACCOUNTADMIN"
{
"_id": "ACCOUNTADMIN",
"owner": "",
"privileges": [
{
"granted_on": "ACCOUNT",
"name": "AA92044",
"privilege": "APPLY AGGREGATION POLICY"
},
{
"granted_on": "ACCOUNT",
"name": "AA92044",
"privilege": "APPLY BACKUP RETENTION LOCK"
}
],
"is_inherited": "N",
"database_roles": [
"SNOWFLAKE.ALERT_VIEWER",
"SNOWFLAKE.BUDGET_CREATOR"
],
"created_on": "2026-01-16 12:53:41.879 UTC",
"roles": [
"SECURITYADMIN",
"SNOWFLAKE_LEARNING_ROLE",
"SYSADMIN"
],
"__NAME__": "ACCOUNTADMIN",
"comment": "Account administrator can manage all aspects of the account.",
"is_default": "N",
"is_current": "N"
}
Database Roles
Read all Snowflake database roles Ids
The following example queries all Snowflake database roles IDs:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__DATABASE_ROLE__?_queryId=query-all-ids"
{
"result": [
{
"_id": "SNOWFLAKE.ALERT_VIEWER"
},
...
{
"_id": "SNOWFLAKE.CLASSIFICATION_ADMIN"
}
],
"resultCount": 99,
"pagedResultsCookie": null,
"totalPagedResultsPolicy": "NONE",
"totalPagedResults": -1,
"remainingPagedResults": -1
}
Read a single Snowflake database role
The following example reads Snowflake database role SNOWFLAKE.ALERT_VIEWER:
curl \
--header "X-OpenIDM-Username: openidm-admin" \
--header "X-OpenIDM-Password: openidm-admin" \
--header "Content-Type: application/json" \
--request GET \
"http://localhost:8080/openidm/system/snowflake/__DATABASE_ROLE__/ID"
{
"_id": "SNOWFLAKE.ALERT_VIEWER",
"owner": "",
"privileges": [
{
"granted_on": "DATABASE",
"name": "SNOWFLAKE",
"privilege": "USAGE"
},
...
{
"granted_on": "FUNCTION",
"name": "SNOWFLAKE.ALERT.\"GET_CONDITION_QUERY_UUID():VARCHAR(16777216)\"",
"privilege": "USAGE"
}
],
"is_inherited": "Y",
"created_on": "2023-04-10 21:28:01.698 UTC",
"__NAME__": "SNOWFLAKE.ALERT_VIEWER",
"comment": "",
"is_default": "N",
"is_current": "N"
}
Supported search filters
The Snowflake connector for users and roles via the __NAME__ field supports equals, contains, startswith, and endswith filters.
OpenICF Interfaces Implemented by the Snowflake Connector
The Snowflake Connector implements the following OpenICF interfaces. For additional details, see ICF interfaces:
- Create
-
Creates an object and its
uid. - Delete
-
Deletes an object, referenced by its
uid. - Schema
-
Describes the object types, operations, and options that the connector supports.
- Script on Connector
-
Enables an application to run a script in the context of the connector.
Any script that runs on the connector has the following characteristics:
-
The script runs in the same execution environment as the connector and has access to all the classes to which the connector has access.
-
The script has access to a
connectorvariable that is equivalent to an initialized instance of the connector. At a minimum, the script can access the connector configuration. -
The script has access to any script arguments passed in by the application.
-
- Search
-
Searches the target resource for all objects that match the specified object class and filter.
- Test
-
Tests the connector configuration.
Testing a configuration checks all elements of the environment that are referred to by the configuration are available. For example, the connector might make a physical connection to a host that is specified in the configuration to verify that it exists and that the credentials that are specified in the configuration are valid.
This operation might need to connect to a resource, and, as such, might take some time. Do not invoke this operation too often, such as before every provisioning operation. The test operation is not intended to check that the connector is alive (that is, that its physical connection to the resource has not timed out).
You can invoke the test operation before a connector configuration has been validated.
- Update
-
Updates (modifies or replaces) objects on a target resource.
Snowflake Connector Configuration
The Snowflake Connector has the following configurable properties:
Configuration properties
| Property | Type | Default | Encrypted(1) | Required(2) |
|---|---|---|---|---|
|
|
|
|
No |
Description is not available |
||||
|
|
|
|
No |
Description is not available |
||||
(1) Whether the property value is considered confidential, and is therefore encrypted in IDM.
(2) A list of operations in this column indicates that the property is required for those operations.
Basic Configuration Properties
| Property | Type | Default | Encrypted(1) | Required(2) |
|---|---|---|---|---|
|
|
|
|
No |
Databases to exclude. |
||||
|
|
|
|
Yes |
The service endpoint URI. |
||||
|
|
|
|
Yes |
Specifies the security role that defines the access privileges and context for the request. |
||||
|
|
|
|
Yes |
The service login name. |
||||
|
|
|
Yes |
No |
The service user password. |
||||
|
|
|
|
Yes |
Define the computer engine. |
||||
|
|
|
|
Yes |
Defines which method is to be used to authenticate on the remote server. Options are |
||||
|
|
|
|
No |
When using OAUTH as authentication method, this property defines the endpoint where a new access token should be queried for (https://myserver.com/oauth2/token). |
||||
|
|
|
|
Yes |
The client identifier for OAuth2. |
||||
|
|
|
Yes |
No |
Secure client secret for OAuth2. |
||||
|
|
|
Yes |
No |
Static authentication token. |
||||
|
|
|
|
Yes |
To be used for debug/test purposes. To be avoided in production. |
||||
|
|
|
|
Yes |
To be used for debug/test purposes. To be avoided in production. |
||||
|
|
|
|
Yes |
Set this property to |
||||
|
|
|
|
Yes |
If TLS Mutual Auth is needed, set this to the certificate alias from the keystore. |
||||
|
|
|
Yes |
Yes |
If TLS Mutual Auth is needed and the client certificate (private key) password is different from the keystore password, set this to the client private key password. |
||||
|
|
|
|
Yes |
Defines the max size of the HTTP connection pool used. |
||||
|
|
|
|
Yes |
Defines the Hostname if an HTTP proxy is used between the connector and the service. |
||||
|
|
|
|
Yes |
Defines the Port if an HTTP proxy is used between the connector and the service. |
||||
|
|
|
|
Yes |
Defines Proxy Username if an HTTP proxy is used between the connector and the service. |
||||
|
|
|
Yes |
Yes |
Defines Proxy Password if an HTTP proxy is used between the connector and the service. |
||||
|
|
|
|
No |
Defines a timeout for the underlying HTTP connection in seconds. |
||||
|
|
|
|
No |
Used by the refresh_token grant type. |
||||
|
|
|
|
No |
The OAuth2 grant type to use ( |
||||
|
|
|
|
No |
The OAuth2 scope to use. |
||||
|
|
|
|
No |
The prefix to be used in the Authorization HTTP header for Token authentication. |
||||
|
|
|
|
Yes |
The Authentication method for refresh token (Basic Authentication or Sending the ClientId and Client Secret in the Header). |
||||
|
|
|
|
No |
The JWT data structure that represents a cryptographic key. |
||||
|
|
|
|
No |
Defines the JWT expiration time in seconds. |
||||
|
|
|
|
No |
The Algorithm type to sign payload. |
||||
|
|
|
|
No |
JWT Claims to be included in the payload |
||||
|
|
|
|
No |
The contents of the private key of the PEM file |
||||
|
|
|
|
No |
The contents of the certificate of the PEM file |
||||
|
|
|
|
No |
Indicates the type of key (such as RSA, DSA or EC) used to sign from the PEM. |
||||
(1) Whether the property value is considered confidential, and is therefore encrypted in IDM.
(2) A list of operations in this column indicates that the property is required for those operations.