Introduction to verified trust

Verified trust represents a fundamental paradigm shift from implicit to explicit trust. Traditionally, identity management acted as a gatekeeper, and if a user had the right credentials, they were granted access. However, the threat landscape has dramatically changed, and traditional credentials are dangerously vulnerable.
Attackers are using agentic AI to automate and scale identity attacks, launching brute force attempts, credential testing, and multi-factor authentication (MFA) prompt-bombing campaigns at machine speed. They’ve shifted focus from hardened "front doors" to softer "side doors," leveraging social engineering to manipulate privileged users and admins. For example, some attackers have employed real-time deepfakes and synthetic identities to bypass standard checks.
Traditional access controls are insufficient, and the mantra "trust, but verify" is outdated. The new necessity is to verify every interaction because you can no longer assume trust.
What is verified trust?
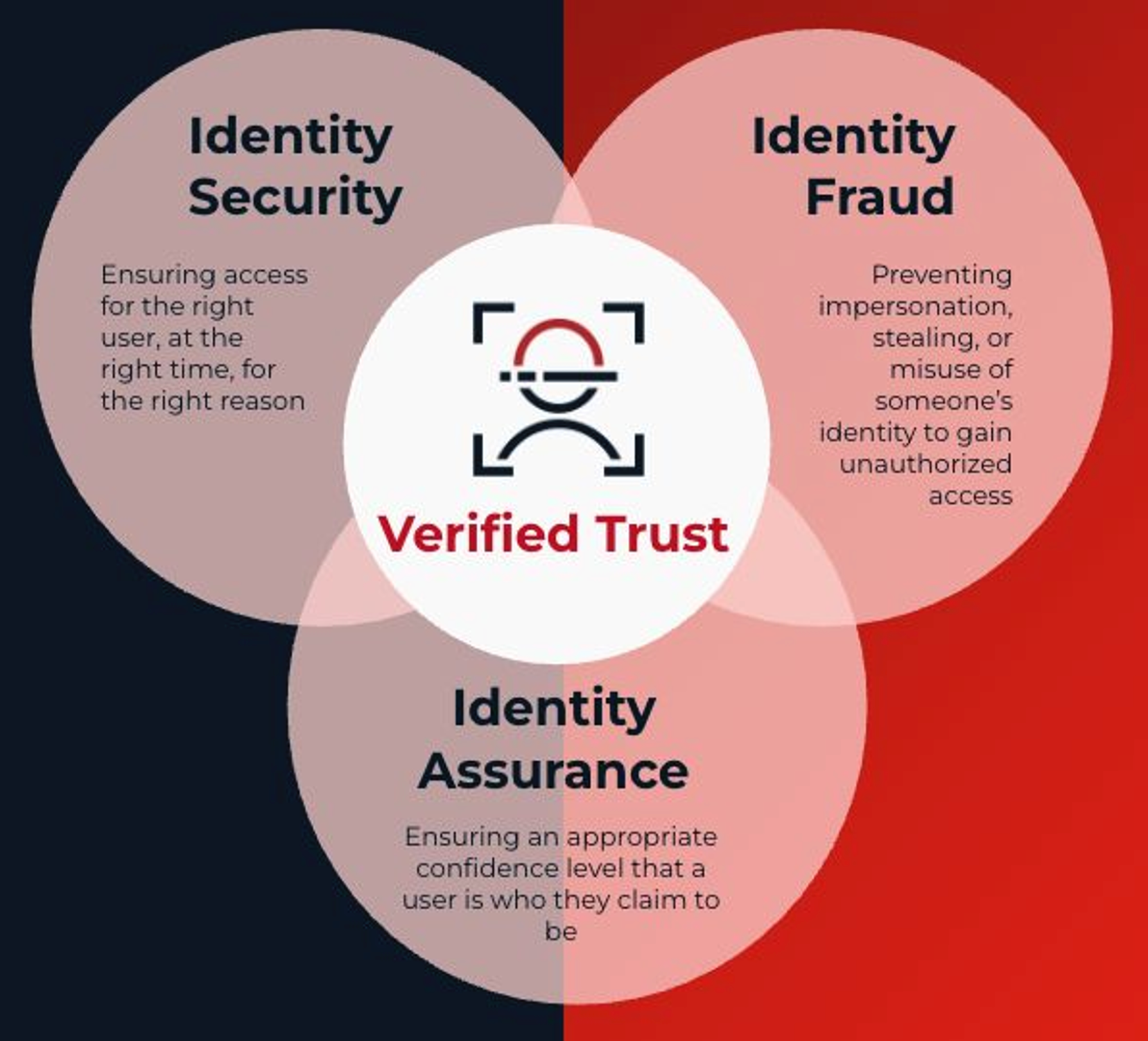
Verified trust changes the role of the identity provider by combining verification, authentication, and authorization into a single, real-time control plane for the enterprise. It answers the critical question "Are you really you?" before granting access to sensitive assets. It’s a strategic identity framework that fundamentally shifts the focus from managing access to confirming the reality of the user behind the screen. This framework depends on the convergence of three distinct disciplines:
-
Identity security: Traditional access management, ensuring the right user has access at the right time (authentication and authorization).
-
Identity fraud: Preventing impersonation and the use of synthetic identities or deepfakes to gain unauthorized access.
-
Identity assurance: Establishing high confidence that the user is genuinely who they claim to be through the verification of biometrics and government documents.
By layering core identity functions like authentication and access with advanced capabilities, including real-time threat detection and identity verification, verified trust empowers organizations to verify users continuously, contextually, and seamlessly.
Why implement verified trust?
Businesses face daily challenges that can be mitigated by using a verified trust architecture. Now that you understand the concepts, you might be wondering how exactly verified trust can help your organization:
-
Organizations are facing "bait-and-switch" schemes, where candidates use deepfakes to pass interviews. Verified onboarding stops this by verifying candidate identities before they can access company systems.
-
Attackers target help desk agents to get account credentials reset. A verified help desk experience closes this vulnerability by enforcing biometric and credential verification before an agent can assist.
-
Many organizations have experienced internal account takeover (ATO), often driven by MFA fatigue (bombarding users with prompts until they accept). Verified access uses real-time risk signals to stop these attacks without frustrating legitimate users.
Verified trust applies rigorous verification standards to help ensure that the digital identity presented matches the human behind it—for every user, device, and system interaction. Consider how this verification secures the following high-risk workflows:
-
Hiring and onboarding: Rather than verifying identity days after a candidate has accessed systems, verified trust shifts this process to day zero. By integrating government ID checks, liveness detection, and biometric binding during the application phase, organizations can prevent "bait-and-switch" hiring and issue a reusable digital credential immediately upon offer acceptance.
-
Account recovery and help desk: The help desk has become a primary "side door" for attackers using social engineering. Verified trust requires that a user verifies their identity (through a mobile biometric check) before an agent resets a password or recovers an account. This heavily reduces reliance on knowledge-based authentication (KBA) or agent discretion.