Set up PingOne workers and configure them as Advanced Identity Cloud services
Integrate your Advanced Identity Cloud tenant environments with PingOne workers so that you can configure PingOne products (such as PingOne Protect and PingOne Verify) in your Advanced Identity Cloud authentication journeys.
PingOne workers are userless service applications that can perform administrative functions in PingOne. You connect to them from Advanced Identity Cloud using an access management service configured with the worker’s OpenID Connect (OIDC) credentials or a PingOne credential JWT, if provided. A PingOne credential JWT contains the worker’s OpenID Connect (OIDC) credentials.
| You only need to set up workers once for each of your Advanced Identity Cloud tenant environments and their mapped PingOne environments. You can then use the same worker service configuration in each of your Advanced Identity Cloud tenant environments. |
Task 1: Create a worker application in each mapped PingOne environment
| If you’ve been provided with a PingOne credential JWT, you can skip this task and proceed to task 2. |
Create a worker application in each of your mapped PingOne environments. These provide access to the PingOne admin APIs using OpenID Connect (OIDC) credentials. In later tasks, you’ll configure each of your Advanced Identity Cloud tenant environments with these OIDC credentials.
In the PingOne admin console, perform the following steps for each of your mapped PingOne environments:
-
In the sidebar, click the Ping Identity logo to open the Environments page.
-
Click an environment in the list, then click Manage Environment.
-
Go to Applications > Applications, then click the add icon ().
-
In the Add Application panel:
-
In Application name, enter a unique name for the worker application.
For example,
PingOne Worker AIC. -
(Optional) Enter a Description for the application, select an Icon, or both. These don’t affect the operation of the worker application but do help you identify it in the list.
-
In Application Type, select Worker.
-
Click Save.
-
-
In the application properties panel for the worker application you created:
-
On the Roles tab, click Grant Roles.
-
On the Available responsibilities tab, select the Identity Data Admin row, and ensure the environment is correct.
-
Click Save.
-
On the Overview tab, enable the worker application using the toggle switch in the top-right corner.
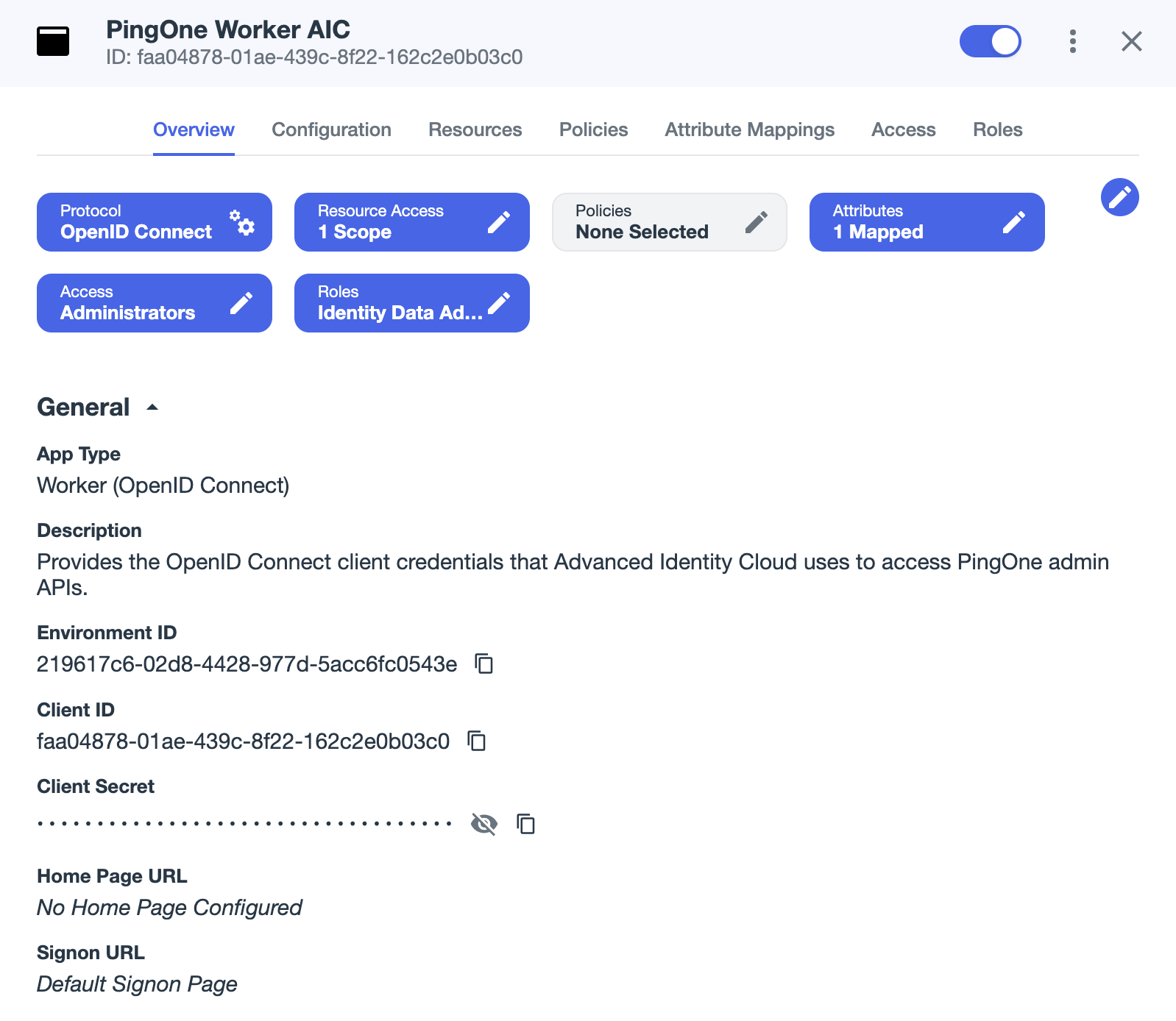
Your worker application should now resemble the following image:
-
Make a note of the following attributes in the Overview tab:
Use the Secret Mask () or Copy to Clipboard () buttons to obtain the value of the client secret. Attribute name Description Example value Environment ID
Identifier of the PingOne environment that contains the worker application.
219...43eClient ID
OIDC client ID of the worker application.
faa...3c0Client Secret
OIDC client secret of the worker application.
zcy...MEM
-
Task 2: Create ESVs for the worker application credentials in each tenant environment
Create ESVs (Environment Secrets and Variables) in each of your Advanced Identity Cloud tenant environments to hold either the client credentials and environment IDs of the PingOne worker applications you created in task 1 or the PingOne credential JWT. Creating ESVs lets you configure Advanced Identity Cloud in a way that’s compatible with the promotion process.
In each of your Advanced Identity Cloud tenant environments, perform the following steps:
-
Create the ESVs. The ESVs required depend on whether you intend to use the OIDC credentials of the worker application or the PingOne credential JWT to configure the worker service in task 3.
-
OIDC credentials
-
Credential JWT
Create the following ESVs using the attribute values from the tenant environment’s mapped PingOne environment.
ESV name ESV type Expression type PingOne attribute value esv-pingone-environment-idVariable
String
Environment ID
esv-pingone-worker-client-idVariable
String
Client ID
esv-pingone-worker-client-secretSecret
String
Client Secret
Create the following ESV using the provided PingOne credential JWT.
ESV name ESV type Expression type esv-pingone-worker-credential-secretSecret
String
You can create variables and secrets using the Advanced Identity Cloud admin console or the API.
-
Create a variable or create a secret using the Advanced Identity Cloud admin console.
-
Create a variable or create a secret using the API.
-
Task 3: Create a service in your development environment
Create a PingOne Worker Service in your Advanced Identity Cloud development environment and configure it with the OIDC credentials of the worker application in its mapped PingOne environment or the PingOne credential JWT. The service is used in Advanced Identity Cloud authentication journey nodes to connect to the PingOne APIs.
Configure the service
Create a PingOne Worker Service in your development environment:
-
In the Advanced Identity Cloud admin console, go to Native Consoles > Access Management.
-
Click Services.
-
Choose one of the following options:
-
If the PingOne Worker Service is in the list of services, select it.
-
If not:
-
Click Add a Service.
-
In Choose a service type, select
PingOne Worker Service, then click Create.
-
-
-
On the Secondary Configurations tab, click Add a Secondary Configuration.
-
On the New workers configuration page:
-
Enter a Name for the configuration. For example,
PingOne Worker AIC.Make a note of this name. You’ll use this value when configuring PingOne authentication journey nodes. -
Click Create
-
-
On the Workers Configuration page, configure the service using either the OIDC credentials of the worker application or the PingOne credential JWT:
-
OIDC credentials
-
Credential JWT
-
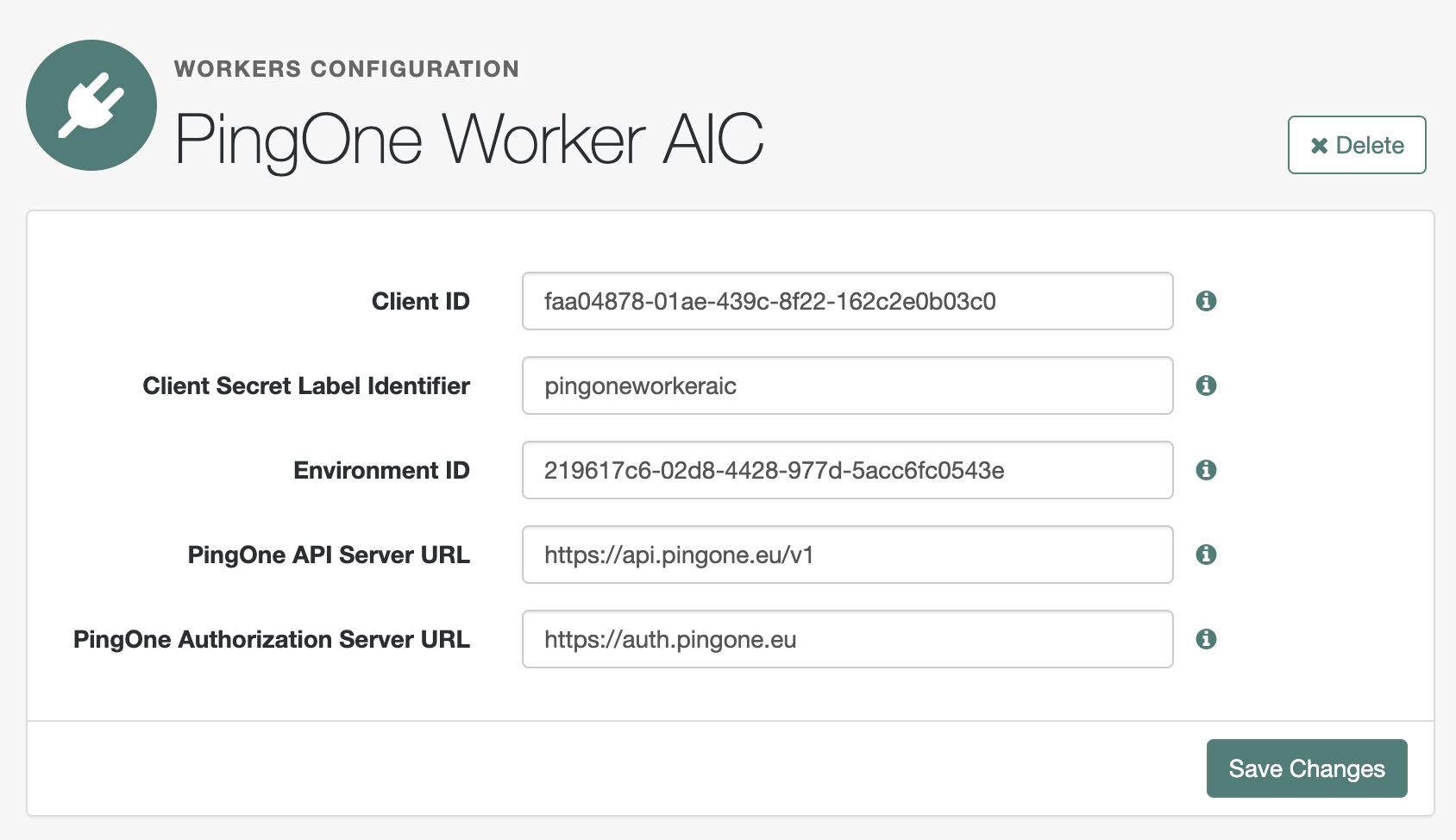
In the Client ID and Environment ID fields, enter the OIDC client ID and environment ID respectively of the worker application in the development environment’s mapped PingOne environment.
Enter the literal values for these fields at this stage, not ESV placeholders. In later steps, you’ll replace the literal values with placeholders for their respective ESVs ( esv-pingone-environment-idandesv-pingone-worker-client-id). -
In the Client Secret Label Identifier field, enter an identifier to create a specific secret label to represent the OIDC client secret of the worker application. For example,
pingoneworkeraic. This field can only contain charactersa-z,A-Z,0-9, and.and can’t start or end with a period.In later steps, you’ll use this identifier to create a mapping to the esv-pingone-worker-client-secretESV. -
Ensure that the PingOne API Server URL and PingOne Authorization Server URL are correct for the region of your PingOne servers:
Region Authorization URL API URL North America
(Excluding Canada)
https://auth.pingone.comhttps://api.pingone.com/v1Canada
https://auth.pingone.cahttps://api.pingone.ca/v1Europe
https://auth.pingone.euhttps://api.pingone.eu/v1Asia-Pacific
https://auth.pingone.asiahttps://api.pingone.asia/v1 -
Confirm your configuration resembles the image below.
-
Select Enable Connection via Credential.
-
In the Credential Secret Label Identifier field, enter an identifier to create a specific secret label to represent the PingOne credential JWT. For example,
pingoneworkeraicjwt. This field can only contain charactersa-z,A-Z,0-9, and.and can’t start or end with a period.In later steps, you’ll use this identifier to create a mapping to the esv-pingone-worker-credential-secretESV. -
Confirm your configuration resembles the image below.

-
-
Click Save and Test Connection.
Advanced Identity Cloud attempts to get an access token from PingOne using your worker service configuration to verify the details.
If the connection fails, check the worker service configuration:
-
Ensure that the ESVs contain the correct values from the worker in the mapped PingOne environment.
-
Ensure that the ESVs are correctly mapped in the Advanced Identity Cloud service.
-
Map the Secret Label Identifier of the service to an ESV secret
Make the esv-pingone-worker-client-secret ESV or the esv-pingone-worker-credential-secret ESV available to the PingOne Worker Service. To do this, map it using the respective secret label identifier you specified in the service.
In your development environment:
-
In the Advanced Identity Cloud admin console, click Native Consoles > Access Management.
-
Go to Realm > Secret Stores.
-
Click the ESV secret store, then click Mappings.
-
Click + Add Mapping.
-
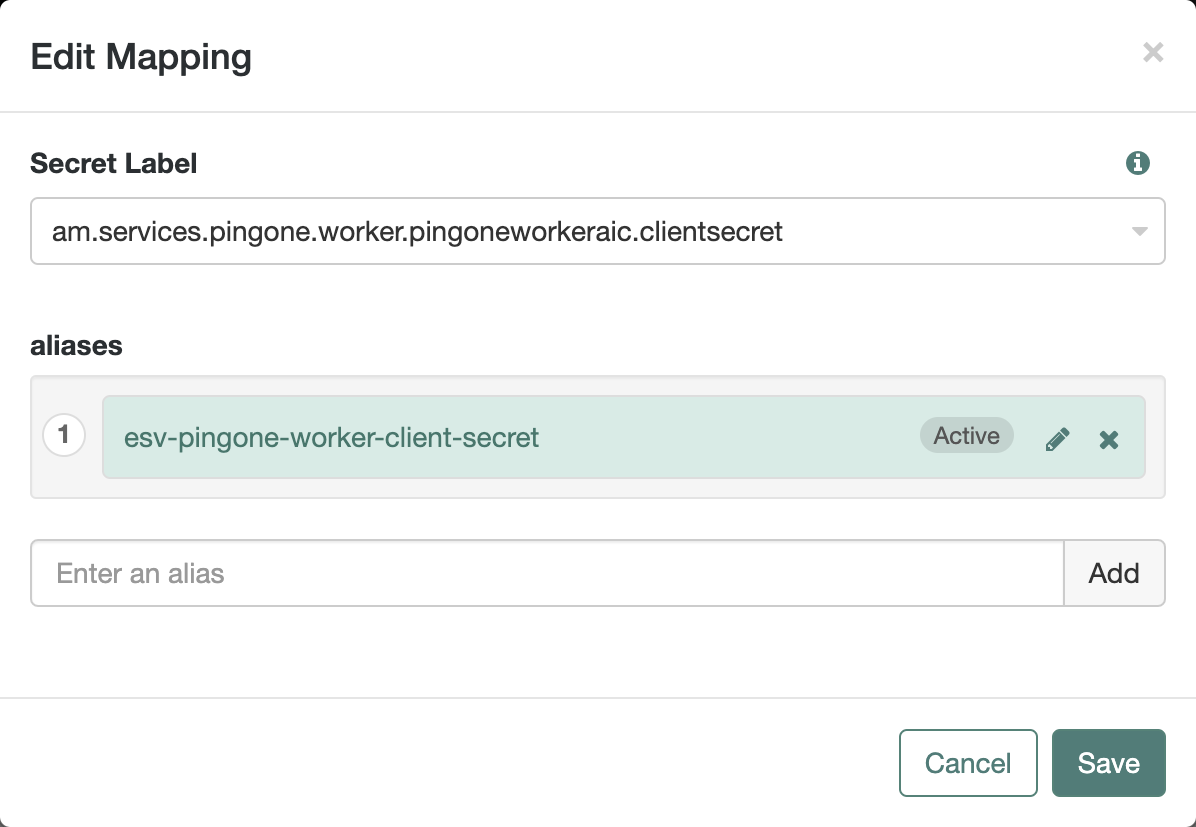
In Secret Label, select the label generated when you entered the Client Secret Label Identifier or the Credential Secret Label Identifier value in the worker service configuration. For example:
-
Entering
pingoneworkeraicas the Client Secret Label Identifier generates the secret labelam.services.pingone.worker.pingoneworkeraic.clientsecret. -
Entering
pingoneworkeraicjwtas the Credential Secret Label Identifier generates the secret labelam.services.pingone.worker.pingoneworkeraicjwt.credential.
-
-
In aliases, enter the name of the corresponding ESV secret you created earlier (
esv-pingone-worker-client-secretoresv-pingone-worker-credential-secret), then click Add.
The result resembles the following:
-
-
Click Create.
Learn more about mapping secrets and label identifiers for Advanced Identity Cloud in Secret labels.
Insert ESV placeholders into the service configuration
-
OIDC credentials
-
Credential JWT
To make the esv-pingone-environment and esv-pingone-worker-client-id ESVs available to the PingOne Worker Service, you must replace the literal values in the worker service configuration with ESV placeholders.
In your development environment, follow the instructions in Insert ESV placeholders into the secondary configuration of a PingOne worker service.
Skip this step if you’ve been provided with a PingOne credential JWT.
Task 4: Promote the integration to your other environments
Once you have successfully tested the integration in your development environment, you can promote the worker service configuration to your other environments (UAT[1], staging, production) using the standard promotion process.
-
Determine the promotion order of your tenant environments. This will depend on whether you have a standard promotion group of environments or whether you also have additional UAT environments.
-
In promotion order, for each of the tenant environments in your promotion group, perform the following steps:
-
Ensure that the required ESVs are present and correctly set:
-
OIDC credentials
-
Credential JWT
-
esv-pingone-environment-id -
esv-pingone-worker-client-id -
esv-pingone-worker-client-secret
-
esv-pingone-worker-credential-secret
-
-
Run a promotion to move the configuration changes to the tenant environment from its respective lower tenant environment. Learn more in:
-
-
(Optional) If you have sandbox[2] environments, repeat task 3 for each of your sandbox environments to create a service.