Release process
Ping Identity continuously provides general availability (GA) releases to PingOne Advanced Identity Cloud to introduce new features, fix known issues, and address security issues.
GA releases are delivered through two channels:
-
Rapid channel releases contain the newest GA release features and fixes and are deployed to sandbox[1] environments.
-
Regular channel releases contain established GA release features and fixes and are deployed to development, UAT[2], staging, and production environments.
Optionally, you can defer releases from the regular channel to your production environment to let you test and validate regular channel releases.
Release versions
Ping Identity gives each release in each channel a unique release version. The release version is numeric (for example, 15158.7) and increases with each successive release. A greater release version includes the changes from lesser release versions.
The release version is displayed in your tenant environments and in each published changelog entry to let you track which features are in your tenant environments.
Rapid channel
If you have a sandbox[1] environment, a continuous stream of the newest features and fixes are deployed there as soon as they are ready for GA release. This lets you test and evaluate GA releases to make sure they are compatible with your Advanced Identity Cloud implementation. It also lets Ping Identity qualify and establish GA releases through cumulative usage and soak testing, typically over a two-week period. When a GA release has been established, it is allocated to the regular channel and deployed into your development, UAT[2], staging, and production environments.
For early access to documentation about features in the rapid channel, learn more in Rapid channel features.
Regular channel
Only established GA releases are deployed to your development, UAT[2], staging, and production environments. Typically, two weeks' worth of GA releases in the rapid channel are rolled up into one release to the regular channel 2–4 weeks later[3].
Track regular channel releases
You can track regular channel releases in these ways:
-
-
Subscribe to email notifications:
-
Scroll down to Documentation Digests.
-
Check the Advanced Identity Cloud Regular Channel Changelog checkbox.
Release deferral
|
Advanced Identity Cloud limited availability feature
Release deferral is a limited availability feature. It is also an opt-in feature. Contact your Ping Identity representative if you are interested. |
Ping Identity lets you defer regular channel releases to your production tenant environments for up to seven days. This allows you to test and validate new regular channel releases in your lower environments (development, UAT[2], and staging) using your most up-to-date configuration.
You can trigger the deployment of the regular channel release to your production environment at any time during the seven-day deferral period by running a promotion from your staging environment to your production environment. Otherwise, at the end of the seven-day deferral period, the regular channel release is automatically deployed to your production environment.
In the rare event that Ping Identity applies a hotfix to the regular channel release while you are testing it in the lower environments, the seven-day deferral period in your production environment is not extended. This ensures that Ping Identity can apply security updates quickly and effectively without impacting the cadence of scheduled regular channel releases.
You can use the release information from your production environment to track the seven-day deferral period.
Release notes
Advanced Identity Cloud provides the following changelogs as part of its release process:
| Sandbox and UAT environments are add-on capabilities. |
Scheduled release freezes
Rapid channel release freezes (all dates inclusive):
-
Tuesday, November 25, 2025 - Friday, November 28, 2025
-
Monday, December 22, 2025 - Friday, January 2, 2026
Regular channel release freezes (all dates inclusive):
-
Friday, November 21, 2025 - Tuesday, December 2, 2025
-
Monday, December 15, 2025 - Monday, January 5, 2026
During a release freeze, Ping Identity only makes critical updates.
Regular channel changelog
Subscribe to get automatic updates: Regular channel changelog RSS feed
For release notes published before December 2024, refer to the Regular channel changelog archive.
April 2025
15 Apr 2025
Version 17106.8
Enhancements
-
ANALYTICS-846: You can now select the attribute type and value for report entity attributes.
-
ANALYTICS-983[4]: You can now use regular expression operators in Advanced Reporting.
-
OPENAM-23718: Added additional Java classes to the SAML 2.0 SP adapter scripting allowlist.
Fixes
-
FRAAS-24631: Fixed a promotions issue where ESVs mapped to secret labels aren’t identified as available in the upper environment.
-
FRAAS-24648: Fixed an issue with loading ESVs with values containing leading blank spaces.
-
IAM-7202: In the custom application modal, the native apps link now correctly points to the SDKs documentation.
09 Apr 2025
Version 16955.13
Fixes
-
FRAAS-24646[6]: Fixed an issue where ESVs mapped to AM secret labels could block configuration promotions.
03 April 2025
Version 16955.12
Key Features
- OIDC application journeys (AME-28650)
-
You can now configure OAuth 2.0 / OIDC client applications to redirect authentication requests to a specified journey. Learn more in Client application journeys.
- Flow Control node (AME-30017)
-
You can now randomly direct users down different journey paths. Learn more in Flow Control node.
- Advanced sync (IAM-8090)
-
Many of the mapping synchronization features available in the IDM admin console are now exposed in the Advanced Sync tab when viewing an application. You can create additional mappings between applications or between applications and identity profiles. Learn more in Advanced sync.
Enhancements
-
AME-27705: Extend the
utilsbinding for all next-generation scripts to support low-level cryptographic operations. These operations include encryption, decryption, hashing, signing, verification, and key generation.Find more information in Access utility functions.
-
AME-28780: Added an IDM policy condition that can assert conditions against an IDM resource type such as user identities.
-
AME-28954: Modified the import metadata endpoint to support updating signing and encryption certificates for existing SAML service providers (SPs) without requiring the deletion or recreation of SP configurations.
-
AME-28954: Modified the import metadata endpoint to support updating signing and encryption certificates for existing SAML service providers (SPs) without requiring the deletion or recreation of SP configurations.
-
AME-29307: You can now use DER-encoded certificates for OAuth 2.0 client authentication.
-
AME-29810: The realm default authentication service can no longer be a journey with
mustRunenabled. Also,mustRuncan no longer be enabled on journeys that are set as the realm default authentication service. -
AME-29835: Configuration Provider Node scripts can now use the next-generation scripting engine, which gives them access to common bindings such as
openidmandhttpClient. -
AME-30076: New
getApplicationId()method provides a consistent way to retrieve the application ID from both SAML and OAuth 2.0 applications. -
IAM-7967[7]: Added an image description for the approvals Low Priority icon.
-
OPENIDM-20139: Applications can now use
postActionscripts for theONBOARDaction. -
FRAAS-24020[8]: Consolidated
End User UI,Login UI,Administrator Registration UI, andAdministrator UIstatus page components into a singleAdministrator UIcomponent as they were all reporting the same service. -
IAM-7229[8]: Added
noneas a client authentication method when configuring an OIDC federation IdP. -
IAM-8419[8]: Added icons to all nodes in the journey editor. The icons are applied based on the node category, improving consistency and visual clarity in the editor.
-
SDKS-3774[8]: Added script input configuration for the PingOne Verify Completion Decision node. This can be used to specify the node state required by a script within the node.
-
FRAAS-24371[8]: New ESVs now load into AM and IDM only when the restart is initiated using the ESV restart API endpoint or the ESV update banner in the admin console. Other restarts (for example, after a promotion) won’t load the ESVs. This makes it easier to identify issues caused by ESV changes.
-
IAM-6996: Added the ability to create a specific OAuth 2.0 client when creating a connector server, rather than relying on the default RCSClient.
-
IAM-7109: You can now use an ESV to set the From Address in the email provider configuration.
-
IAM-7827/ANALYTICS-835[4]: In the analytics report editor in Advanced Reporting, you can now reorder columns by dragging and dropping them.
-
IAM-7841/ANALYTICS-840[4]: The reports page in Advanced Reporting is now a list view with pagination and search.
-
IAM-8321: In the journey editor, the node titles now wrap within the left nodes panel.
Fixes
-
AME-29504: The
scriptNameandloggerbindings in library scripts referenced the same default script name and ID. Their previous behavior has now been restored by inheriting values from the referencing script. -
AME-29965: The Configuration Provider node now works with the Inner Tree Evaluator for nested inner journeys.
-
AME-30377: The following two warning level log messages have been reduced to debug level because they’re rarely useful and appear frequently, drowning out more useful log entries:
-
No users have been identified. -
Ignoring the new universal id as that is empty and the current universal id is already set.
-
-
IAM-7719[7]: Users are now redirected back to the compliance Policy Rules tab after creating or editing a policy rule.
-
IAM-7977: Improved the font color contrast ratio of the email address displayed in Advanced Identity Cloud admin console user profiles.
-
IAM-8053: The Advanced Identity Cloud end-user UI can now use
defaultTextvalue as a fallback value when the actual value of a field returns empty. -
OPENAM-22120: Back-channel logout tokens now include the
expclaim. -
OPENAM-23077: The
access_tokenendpoint now responds with the correct error code when thecode_verifierisn’t supplied (for example,invalid_grant). -
FRAAS-24042[8]: Fixed an issue where Proxy Connect could be unintentionally deactivated.
-
FRAAS-24058[8]: Increased max HTTP header size accepted by access management endpoints.
-
IAM-1504: User no longer needs to click the cancel button twice in some journey dialogs.
-
IAM-8111: Schedules can no longer be disabled when running.
March 2025
25 Mar 2025
Version 16747.9
| This version was partially deployed but has now been reverted. All associated changes have been withdrawn. |
21 Mar 2025
Enhancements
-
ANALYTICS-789[9]: Change the 'Status' parameter input type to combo box along with drop down list in out-of-the-box reports.
Fixes
-
ANALYTICS-904[9]: Fixed report tab keep loading in end user UI.
20 Mar 2025
18 Mar 2025
Version 16747.7
| This version has been reverted and all associated changes withdrawn. |
Key Features
- OIDC application journeys (AME-28650)
-
You can now configure OAuth 2.0 / OIDC client applications to redirect authentication requests to a specified journey. Learn more in Client application journeys.
- Flow Control node (AME-30017)
-
You can now randomly direct users down different journey paths. Learn more in Flow Control node.
- Advanced sync (IAM-8090)
-
Many of the mapping synchronization features available in the IDM admin console are now exposed in the Advanced Sync tab when viewing an application. You can create additional mappings between applications or between applications and identity profiles. Learn more in Advanced sync.
Enhancements
-
AME-27705: Extend the
utilsbinding for all next-generation scripts to support low-level cryptographic operations. These operations include encryption, decryption, hashing, signing, verification, and key generation.Find more information in Access utility functions.
-
AME-28780: Added an IDM policy condition that can assert conditions against an IDM resource type such as user identities.
-
AME-28954: Modified the import metadata endpoint to support updating signing and encryption certificates for existing SAML service providers (SPs) without requiring the deletion or recreation of SP configurations.
-
AME-28954: Modified the import metadata endpoint to support updating signing and encryption certificates for existing SAML service providers (SPs) without requiring the deletion or recreation of SP configurations.
-
AME-29307: You can now use DER-encoded certificates for OAuth 2.0 client authentication.
-
AME-29810: The realm default authentication service can no longer be a journey with
mustRunenabled. Also,mustRuncan no longer be enabled on journeys that are set as the realm default authentication service. -
AME-29835: Configuration Provider Node scripts can now use the next-generation scripting engine, which gives them access to common bindings such as
openidmandhttpClient. -
AME-30076: New
getApplicationId()method provides a consistent way to retrieve the application ID from both SAML and OAuth 2.0 applications. -
IAM-7967[7]: Added an image description for the approvals Low Priority icon.
-
OPENIDM-20139: Applications can now use
postActionscripts for theONBOARDaction. -
FRAAS-24020[8]: Consolidated
End User UI,Login UI,Administrator Registration UI, andAdministrator UIstatus page components into a singleAdministrator UIcomponent as they were all reporting the same service. -
IAM-7229[8]: Added
noneas a client authentication method when configuring an OIDC federation IdP. -
IAM-8419[8]: Added icons to all nodes in the journey editor. The icons are applied based on the node category, improving consistency and visual clarity in the editor.
-
SDKS-3774[8]: Added script input configuration for the PingOne Verify Completion Decision node. This can be used to specify the node state required by a script within the node.
Fixes
-
AME-29504: The
scriptNameandloggerbindings in library scripts referenced the same default script name and ID. Their previous behavior has now been restored by inheriting values from the referencing script. -
AME-29965: The Configuration Provider node now works with the Inner Tree Evaluator for nested inner journeys.
-
AME-30377: The following two warning level log messages have been reduced to debug level because they’re rarely useful and appear frequently, drowning out more useful log entries:
-
No users have been identified. -
Ignoring the new universal id as that is empty and the current universal id is already set.
-
-
IAM-7719[7]: Users are now redirected back to the compliance Policy Rules tab after creating or editing a policy rule.
-
IAM-7977: Improved the font color contrast ratio of the email address displayed in Advanced Identity Cloud admin console user profiles.
-
IAM-8053: The Advanced Identity Cloud end-user UI can now use
defaultTextvalue as a fallback value when the actual value of a field returns empty. -
OPENAM-22120: Back-channel logout tokens now include the
expclaim. -
OPENAM-23077: The
access_tokenendpoint now responds with the correct error code when thecode_verifierisn’t supplied (for example,invalid_grant). -
FRAAS-24042[8]: Fixed an issue where Proxy Connect could be unintentionally deactivated.
-
FRAAS-24058[8]: Increased max HTTP header size accepted by access management endpoints.
05 Mar 2025
Version 16583.6
Enhancements
-
FRAAS-23002: Improvements to OATH support for MFA authenticators
-
Update the default OATH shared secret length from 32 to 40 for existing and new tenants so that tenant administrators can use Google Authenticator with MFA when signing on using their Advanced Identity Cloud native accounts.
-
Make the OATH shared secret length configurable (using a support request) to support other MFA authenticators.
-
-
IAM-4692: Managed identity boolean fields now use a checkbox instead of a toggle.
-
IAM-6581: SAML 2.0 application journeys can now be configured in the Advanced Identity Cloud admin console.
-
IAM-7248[7]: In IGA sources, the
displayNameandlogocan now be obtained from the CDN. -
IAM-7874[7]: The Governance > Requests > Settings tab now lets you activate or deactivate Governance LCM.
Fixes
-
IAM-1262: Clicking the Toggle Sidebar button now collapses the sidebar.
-
IAM-5801: For applications that mandate a minimum page size, the page size selector on the Data tab and the Reconciliation Results tab has been removed.
Corrections
-
IAM-5813: UI support for managing certificates was released on January 9, 2025 (Version 16100.4) but inadvertently excluded from the changelog.
February 2025
26 Feb 2025
Version 16368.14
Fixes
-
FRAAS-24058 [8]: Increased the maximum HTTP header size accepted by access management endpoints.
24 Feb 2025
18 Feb 2025
Version 16508.8
| This version has been reverted and all associated changes withdrawn. |
Enhancements
-
FRAAS-23002: Improvements to OATH support for MFA authenticators
-
Update the default OATH shared secret length from 32 to 40 for existing and new tenants so that tenant administrators can use Google Authenticator with MFA when signing on using their Advanced Identity Cloud native accounts.
-
Make the OATH shared secret length configurable (using a support request) to support other MFA authenticators.
-
-
IAM-4692: Managed identity boolean fields now use a checkbox instead of a toggle.
-
IAM-6581: SAML 2.0 application journeys can now be configured in the Advanced Identity Cloud admin console.
-
IAM-7248[7]: In IGA sources, the
displayNameandlogocan now be obtained from the CDN. -
IAM-7874[7]: The Governance > Requests > Settings tab now lets you activate or deactivate Governance LCM.
04 Feb 2025
Version 16368.7
Enhancements
-
FRAAS-23375: You can now obtain the HTTP client location from the
X-Client-City&X-Client-City-Lat-LongHTTP headers in Advanced Identity Cloud scripts and journeys. -
IAM-6833 : Made existing synchronization tokens editable for incremental reconciliations.
-
IAM-7223[7]: Added the ability to set user, role, organization, application, or entitlement objects to provide predefined values for select and multiselect fields in request forms.
-
IAM-7454: The inbound mapping for all application templates and scripted application templates has now been configured to make fewer connector requests.
Fixes
-
FRAAS-23780[6]: Optimized network utilization to distribute workloads more effectively.
-
IAM-5242: The Previous link in the New Script modal now always shows the previous step.
-
IAM-5482: Password policy no longer allows Password length to be set as an empty string.
-
IAM-7799: Identity attributes with
TimeandDateTimeformat now trigger change events only when a change occurs.
January 2025
09 Jan 2025
Version 16100.4
Key features
- UI support for managing certificates [10] (IAM-5813)
-
You can now use the Advanced Identity Cloud admin console to generate CSRs and upload SSL certificates in your tenant environments.
Learn more in Manage SSL certificates using the admin console.
- PingOne Authorize node (TNTP-183)
-
Use this node to send a decision request to a specified decision endpoint in your PingOne Authorize environment.
- PingOne node improvements (SDKS-3468)
-
- PingOne Create, Identify, and Delete Nodes
-
The following PingOne nodes are now available:
- PingOne Identity Match node
-
Use the PingOne Identity Match node to identify if a user exists both in the user repository and in PingOne, using defined attributes.
- PingOne Create User node
-
Create new users in the PingOne platform using the PingOne Create User node. Create users based on an existing user’s properties or choose to create the user anonymously. For example, when used in conjunction with PingOne Verify.
- PingOne Delete User node
-
Delete users from the PingOne platform with the PingOne Delete User node.
- PingOne Verify nodes
-
Use the following PingOne Verify nodes in conjunction with the PingOne Identity Match node, PingOne Create User node, and PingOne Delete User node to create a seamless verification process in your journey:
- PingOne Verify Evaluation node
-
Use PingOne Verify to initiate or continue a verification transaction with the PingOne Verify Evaluation Node.
- PingOne Verify Completion Decision node
-
Determine the completion status of the most recent identity verification transaction for an end user.
Use before the PingOne Verify Evaluation node to determine the status of the verification process or after the PingOne Verify Evaluation node using a script to evaluate the transaction.
For example, you can evaluate if the transaction was completed using a passport and route your journey accordingly.
Use these nodes in place of the PingOne Verify Marketplace nodes. - reCAPTCHA Enterprise node (SDKS-3322)
-
The reCAPTCHA Enterprise node node adds Google reCAPTCHA Enterprise support to your journeys.
- Set Failure Details node (AME-27871)
-
Use the Set Failure Details node to configure a localized error message on journey failure. You can also configure extra details in the response body of the failure request.
- Set Success Details node (OPENAM-12335)
-
Use the Set Success Details node to add additional details to the success response of a journey.
- Reports for IGA data sources (ANALYTICS-571)
-
Advanced Reporting[11] now supports various IGA[12] data sources and relationships. This lets IGA administrators create customer-friendly report templates.
Enhancements
-
ANALYTICS-459: Report query data is now retained for 30 days for customers using OOTB reports and 90 days for customers with Advanced Reporting[11].
-
ANALYTICS-495: Replace
emailwithusernamein User Last Login report. -
ANALYTICS-817[4]: Report authors can now query on "Password Last Changed Time" for user entity.
-
ANALYTICS-818[4]: Report authors can now query on "Password Expiration Time" for user entity.
-
AME-26050: You can now create Next-generation Policy Condition scripts that have access to all common bindings, such as
openidmandhttpClient. Additionally, some existing bindings have been wrapped to improve usability in scripts. -
AME-28228: OAuth 2.0 audit logs now include the OAuth 2.0 client ID and any journey associated with the client.
-
AME-29009: When using the new FIDO Metadata Service, if you link to the FIDO metadata using a URL, Advanced Identity Cloud periodically downloads and updates the latest FIDO metadata based on the
nextUpdatedate specified in the downloaded data. -
AME-29093: Added configuration for integration with WebAuthn Metadata Services (such as the FIDO Metadata Service). This includes a realm-level WebAuthn Metadata service and a new FIDO Certification Level configuration attribute in the WebAuthn Registration Node.
-
FRAAS-22321: You can now obtain the HTTP client location from the
X-Client-RegionHTTP header within your scripts and journeys. TheX-Client-Regionheader contains the country (or region) associated with the client’s IP address in the form of a Unicode CLDR region code, such asUSorFR. For most countries, these codes correspond directly to ISO-3166-2 codes. -
FRAAS-23073: The SAML scripting adapter now lets scripts access
org.forgerock.http.protocol.*. -
IAM-3323: You can now use XPath transformation functions with additional Workday application template attributes.
-
IAM-4540: You can now change the border color of a selected input field in journey and end-user pages.
-
IAM-6397: The Advanced Identity Cloud admin console now lets you page through the list of OAuth 2.0 client profiles.
-
OPENAM-20314: Added the ability to indicate whether an OIDC provider doesn’t return a unique value for the
subclaim. -
OPENAM-22966: Social IDPs now support NONE as a client authentication method. This option should be used if the provider doesn’t require client authentication at the token endpoint.
-
OPENAM-23109: During a WebAuthn registration flow, if Store data in transient state is enabled, the Authenticator Attestation Global Unique Identifier (AAGUID) is now added to the node state under the
webauthnDatakey. -
OPENIDM-20542: Added a feature service named
am/2fa/profilesto expose certain multi-factor attributes onalphaandbravousers.
Fixes
-
ANALYTICS-474: The User Journey Stats report now provides aggregates by outcome in the report result when more than one outcome is selected.
-
ANALYTICS-837: The User Count by Status report now provides aggregates by status in the report result when more than one outcome is selected
-
ANALYTICS-585[4]: Remove Report Admin and Report Owner group selection when creating a new report.
-
AME-28016: When an invalid redirect URI is provided to the
/parendpoint, the URI mismatch error is nowredirect_uri_mismatchinstead ofinvalid_request. -
AME-28017: Advanced Identity Cloud now accepts the requested OAuth 2.0 endpoint as a valid JWT audience claim, as per RFC 7519 and RFC 9126.
-
AME-28906: The stack trace of an authentication exception generated on login failure is now logged only when
debuglevel logging is enabled. -
AME-29170: On LDAP Decision node login failure, stack traces are now logged at
debuglevel. -
AME-29504: Fixed issue with script names not displaying in next-generation script logs.
-
AME-29965: The Configuration Provider node now works with the Inner Tree Evaluator node for nested inner journeys.
-
IAM-1782: Long gateway and agent IDs no longer overflow in the Advanced Identity Cloud admin console.
-
IAM-7523[7]: A user receiving a forwarded fulfillment task now has permission to approve or reject the task.
-
IAM-7537[7]: Governance functionality is now only shown for the
alpharealm. -
IAM-7689[7]: The Advanced Identity Cloud admin console now displays the Assigned To value in the task list for a user assigned to a role who receives a forwarded fulfillment task.
-
OPENAM-18252: Journeys acting on multiple identities now successfully update
universalIdin the journey context during the authentication flow.
07 Jan 2025
Version 15726.9
Enhancements
-
OPENDJ-9287: The password validation mechanism has been enhanced to include checks for portions of attribute values within passwords. This improvement ensures that even partial matches between portions of passwords and portions of attribute values are identified and restricted, thereby enhancing security.
For example, if the password is
abcdefand the attribute value isabcdef123, the password is rejected. Similarly, if the password isabcdefAZERTYand the attribute value isabcdef123, the password is rejected.
December 2024
04 Dec 2024
Version 15726.4
Key features
- Configure journey to always run (AME-27848)
-
Added a new setting for journeys to always run regardless of existing user sessions.
Learn more in Configure an authentication journey to always run.
- SAML application journeys (AME-27850)
-
Added support for SAML application journeys with a new setting on the remote SP. Configure a specific authentication journey that always runs for users authenticating with your SAML 2.0 app, regardless of existing sessions or configured authentication context.
Learn more in Configure a SAML 2.0 application journey.
- SAML application script binding (AME-28012)
-
Added a new
samlApplicationbinding for querying the SAML 2.0 authentication request properties and IdP and SP configuration attributes.Learn more in Query SAML application and authentication request.
- Suspend and resume journeys (OPENAM-21806)
-
Next-generation decision node scripts can now use the new
action.suspend()method to suspend the current authentication session and send a message to the user. Implement custom logic with the resume URI, for example, to send an email or SMS using the HTTP client service.Learn more in Suspend and resume journeys.
Enhancements
-
AME-27074: Added a new
configProviderScriptaction to each authentication node endpoint to generate a configuration provider template script For example,authentication/authenticationtrees/nodes/MessageNode?_action=configProviderScript. -
AME-28258: Added a new "webAuthnExtensions" input to the WebAuthn Registration and Authentication nodes. This can be set via a Scripted Decision node. It is expected to contain a map of extension name to input. Output is currently not available.
-
AME-28384: The outcome of a Scripted Decision node can now also be a
CharSequencetype. -
AME-28777: The refresh token grace period now applies to both client-side refresh tokens and server-side refresh tokens.
-
AME-29157: Authentication nodes with limited possible outcomes are now available to the Configuration Provider node, including:
The Identity Assertion node, Push Wait node, and Enable Device Management node nodes with fixed outcomes are also now available to the Configuration Provider node.
-
OPENAM-22601: You can now use the next-generation script binding,
utils, to generate secure random numbers. -
OPENAM-22811: NodeState has two new methods:
mergeShared(Map<String, Object>)andmergeTransient(Map<String, Object>). Use them to merge keys into the shared/transient state, includingobjectAttributeskeys. -
OPENDJ-11012: Added support for Microsoft Identity Cloud PBKDF2-SHA512 password scheme in Advanced Identity Cloud.
Fixes
-
AME-25491: The Configuration Provider node script now correctly reads node state after an inner tree callback.
-
AME-28786: Removed several unused UI properties from default social identity provider profiles.
-
AME-29027: WebAuthN attestations containing a self-signed root CA are now rejected instead of silently removed.
-
OPENAM-22465: Fixed error to return
invalid_resource_uriwhenrequest_uriclient doesn’t match request parameter client in PAR authorize request. -
OPENAM-22675: In next-generation scripting, you can now set a default name correctly when creating a
NameCallback. -
OPENAM-22688: Page node localization now defaults to correct locale when the incoming
accepted-languageheader doesn’t match the node’s language configuration.
Regular channel changelog archive
2024
18 Nov 2024
Version N/A
Notices
- End of life announcement for Autonomous Access and Autonomous Access documentation[13]
-
Ping Identity announces the planned end of life for the Advanced Identity Cloud Autonomous Access product. The product will reach end of life on October 31, 2025. During the deprecation period, Ping Identity will not provide new patches, updates, or new features for Autonomous Access.
To support our Autonomous Access customers, we’re providing migration assistance to PingOne Protect, an advanced threat detection solution that leverages machine learning to analyze authentication signals and detect abnormal online behavior. PingOne Protect is a well-established product, trusted by hundreds of customers worldwide.
The Autonomous Access documentation has now moved to the documentation archive at https://docs.pingidentity.com/archive/.
For any questions, please contact Ping Identity support.
12 Nov 2024
Version 15472.8
Key features
- PingOne Authorize node[8] (TNTP-183)
-
The new PingOne Authorize node sends a decision request to a specified decision endpoint in your PingOne Authorize environment.
Learn more in PingOne Authorize node.
Enhancements
-
IAM-6388: Added the ability to specify that inner journeys can’t be accessed directly. Learn more in Custom journeys.
-
IAM-7185: The mapping tab for application provisioning now shows the inbound or outbound application type without needing to inspect a drop-down.
-
OPENIDM-19810[8]: The
_refPropertiesof the last relationship field leading to a vertex, whose state is harvested to constitute the RDVP state, can now be included in this RDVP state. -
OPENIDM-19847[8]: The
accountTypefor application grants is now configured in the object mapping under "accountTypes". -
OPENIDM-20371[8]: IDM now allows up to 20 indexed string attributes per user in both Alpha and Bravo realms.
-
OPENIDM-20372[8]: IDM now supports up to ten custom relationships per managed object, except for one-to-many relationships.
04 Nov 2024
Version 15312.5
Enhancements
-
IAM-7187: Integration of SAP app template with IDM scripts.
-
IAM-7243[7]: Added text field to utilities category in IGA access request forms.
29 Oct 2024
Version N/A
- Configure PingOne as a federation IdP for Advanced Identity Cloud (FRAAS-17705)
-
You can now configure PingOne as a federation IdP for Advanced Identity Cloud. After configuration in PingOne, a tenant environment in Advanced Identity Cloud automatically displays PingOne in its list of federation IdPs.
Learn more in Configure federated access using PingOne.
24 Oct 2024
Version N/A
Key features
- Proxy Connect (FRAAS-14278)
-
Ping Identity introduces Proxy Connect, a new add-on capability for Advanced Identity Cloud.
You can use Proxy Connect to configure a proxy service, such as a web application firewall (WAF) or a content delivery network (CDN), in front of your Advanced Identity Cloud tenant environments. This lets you secure traffic to your tenant environments in seamless compliance with the security controls you apply to your company’s other network resources.
Learn more in Configure a proxy service with Proxy Connect.
15 Oct 2024
Version 15158.7
Key features
- Scripted SAML v2.0 NameID values (AME-25921)
-
The NameID mapper script lets you customize SAML v2.0 NameID values per application.
- Set State node (AME-26443)
-
The Set State node lets you add attributes to the journey state.
- Http Client service (AME-27936)
-
The new Http Client service lets you create named instances that you can reference from a next-generation script to make mTLS connections to external services.
Learn more in Access HTTP services.
- Support for LINE as a social identity provider (AME-28672)
-
You can now configure a social provider authentication with LINE Login when signing in from a browser. There is a separate configuration for authenticating from a mobile app.
Learn more in Social authentication.
- Advanced Reporting (ANALYTICS-763)
-
Ping Identity introduces Advanced Reporting, a new add-on capability for Advanced Identity Cloud.
Advanced Reporting lets you create custom reports on activity in your tenant environments. You can query a number of metrics to create useful reports for your company.
Learn more in Advanced Reporting.
- Identity Governance request and approval forms[7] (IAM-6358)
-
Identity Governance now lets you create request and approval forms to make it easier for end users to request access to applications.
Learn more in Identity Governance forms.
- Additional cloud connectors
-
The following connectors are now bundled with Advanced Identity Cloud:
-
AWS IAM Identity Center Connector v1.5.20.23 (OPENIDM-20038)
-
Box Connector v1.5.20.23 (OPENIDM-20367)
Learn more in the ICF documentation.
-
- Enable Device Management node (SDKS-2919)
-
The new Enable Device Management node lets end users manage devices from their account.
Enhancements
-
FRAAS-21728: Updated the cookie domain API to add default values for GET requests where cookie domain values haven’t been overridden by a PUT request. The default values are derived from the existing tenant cookie domain configuration, so are backward compatible.
-
AME-26594: Added secrets API binding to all next-generation script contexts.
-
AME-27129: Added option to exclude client certificate from SAML hosted SP metadata.
-
AME-27792: Added
AM-TREE-LOGIN-COMPLETEDaudit log event that outputs aresultofFAILED. -
AME-27839: Added the ability to specify connection and response timeouts for Http Client service instances.
-
AME-28008: You can now disable certificate revocation checks, or all certificate checks entirely, on your Http Client service instances.
-
IAM-4753: Added a toggle to the application catalog to hide deprecated templates.
-
OPENIDM-19698: Added ability to use wildcards in the
watchedFieldsproperty. -
OPENAM-22666: The well-known endpoint is no longer required when configuring a social identity provider service. If it is not provided, AM uses the client secret for signature verification.
-
SDKS-1752[8]: Enhance WebAuthn Authentication node, OATH Token Verifier node, and Push Result Verifier node to store creation date and last sign-on date.
Fixes
-
FRAAS-16228: Promotions are now halted if the AM CORS service is disabled; the service is essential to the correct functioning of promotions.
-
FRAAS-21715: Environments can now be unlocked if configuration rollback fails because there are no promotions to roll back.
-
OPENAM-15410: Fixed an issue that prevented customization of claims if
profileandopenidscopes are requested. -
OPENAM-20609: Fixed inconsistent error message when generating access token using refresh token after changing username.
-
OPENAM-21974: Adds an OAuth 2.0 client configuration for the new version of the LinkedIn provider.
-
OPENAM-22298: Log unretrieved SP and IdP descriptors in SAML2 Authentication node.
-
OPENIDM-19336: Fixed an issue where delegated administrators couldn’t add new users to their organization.
-
OPENIDM-20238: Fixed an issue where clustered reconciliation can fail with "Expecting a Map or List" under specific circumstances.
18 Sep 2024
Version 14800.7
Key features
- DocuSign application template (IAM-6194)
-
The DocuSign application lets you manage DocuSign service accounts and synchronize DocuSign accounts and Advanced Identity Cloud identities.
Enhancements
-
IAM-6493: The PingOne application template now supports specifying an LDAP gateway.
-
IAM-6868: Added screen reader label to end-user access approval button.
-
IAM-6870: Added screen reader label to end-user access request button.
-
IAM-6880: Added a toggle in the hosted pages journey settings to disable the error heading fallback that displays if there is no heading in the page content. (FORGEROCK-1582)
03 Sep 2024
Version 14620.4
Key features
- BeyondTrust application template (IAM-6492)
-
The BeyondTrust application lets you manage and synchronize data from Advanced Identity Cloud to BeyondTrust.
20 Aug 2024
Version 14442.2
06 Aug 2024
Version 14260.4
Key features
- Adobe Admin Console application template (IAM-6195)
-
The Advanced Identity Cloud Adobe Admin Console application lets you manage users, groups, and user group memberships between Adobe Admin Console and Advanced Identity Cloud.
- Paris added to data residency regions (FRAAS-20850)
-
The Paris region (europe-west9) is now available. For more information, refer to:
Enhancements
-
AME-26135[8]: The Advanced Identity Cloud admin console now lets you configure a secret from a secret store for these features:
-
Identity Gateway agents
-
Web and Java agents
-
OAuth 2.0 agents
You can now optionally set a secret label identifier for these features instead of a manually entered client secret.
-
-
IAM-4279: Display available ESV placeholders in Decision Node script editor.
-
IAM-4654: Enable creation of all script types in Advanced Identity Cloud admin console.
Fixes
-
FRAAS-20397: The promotion process now retries tagging the lower environment after a network interruption, preventing blocking promotion failures.
-
IAM-5356: Session logout warning not displaying when maximum idle time set to a higher value than maximum session time.
-
IAM-6628: New draft option shouldn’t exist for out-of-the-box workflows.
-
IAM-6779: Pagination for list of apps not working when there are over 4000 apps.
23 Jul 2024
Version 14077.0
Fixes
-
FRAAS-20970: The
/monitoring/logsendpoint now returns anX-Ratelimit-Limitheader with a fixed value of 60. Previously, the value was misleading due to the way it was calculated when scaling an environment’s resources. TheX-Ratelimit-Remainingheader continues to report the number of requests that may be sent before receiving a rate limited response. -
FRAAS-20983: Promotion reports now list changes to the default OAuth 2.0 provider.
11 Jul 2024
Version 13945.9
Key features
- Additional cloud connectors
-
The following connectors are now bundled with Advanced Identity Cloud:
-
Adobe Admin Console connector (OPENIDM-19843)
-
DocuSign connector (OPENIDM-20190)
For more information, refer to the ICF documentation.
-
Fixes
-
OPENIDM-20142: Resolved a communication failure between Advanced Identity Cloud and RCS instances that could result in a prolonged failure to activate remote connectors.
Changed functionality
-
OPENIDM-20178: You can’t use scope private fields in query filters. For more information, refer to Security Advisory #202402.
10 Jul 2024
Version 13945.8
Key features
- Product name change for Identity Cloud (FRAAS-20178)
-
To align ForgeRock products with Ping family names, ForgeRock Identity Cloud has been renamed to PingOne Advanced Identity Cloud. Name and logo changes have been updated throughout the user interfaces, and documentation updates will occur when the UI changes are released to the regular channel.
For more information, refer to the New names for ForgeRock products FAQ
- Organization-based certification[7] (IAM-5237)
-
Advanced Identity Cloud introduces organization-based certification—a new Identity Governance feature that lets you configure B2B customers and partners as organizations and allow designated organization administrators to certify access for the users in their organization.
For more information, refer to Certify access by organization.
- Segregation of duties (SoD) (IAM-5624)
-
Advanced Identity Cloud introduces a new Identity Governance compliance feature designed to help you create and manage segregation of duties (SoD) policies and rules. SoD is a crucial practice that ensures no single individual has privileges that could lead to a conflict of interest.
For more information, refer to Configure compliance policies.
- Scoping rules[7] (IAM-5629)
-
Advanced Identity Cloud introduces a new Identity Governance feature that lets you create scoping rules to determine what actions an end user can perform and on what resource.
For more information, refer to Configure scoping rules to resources.
Enhancements
-
IAM-4785: Synchronize only the modified properties on a target source during reconciliation of applications.
-
IAM-5487: Correlation rules moved to the top of the reconciliation settings page.
-
IAM-6231: Scripted Decision Node now updates the list of scripts when a script is added or edited.
-
IAM-6544: Add reviewer column to administrator list view of compliance violations.
Fixes
-
FRAAS-20604: Removed superfluous AM metrics related to token store internals:
-
am_cts_connection_count -
am_cts_connection_seconds -
am_cts_connection_seconds_total -
am_cts_connection_state -
am_cts_reaper_cache_size -
am_cts_reaper_deletion -
am_cts_reaper_deletion_count -
am_cts_reaper_deletion_total
-
-
IAM-6135: ESV values containing accents get corrupted by encoding process.
-
IAM-6562: Label duplicated for OAuth 2.0 access token and ID token endpoints.
-
IAM-6669[7]: Badge count of violations in end-user navigation doesn’t update when an action is performed.
01 Jul 2024
Version 13848.13
Fixes
-
OPENIDM-18495[6]: Disable sorting in the connector data tab in the IDM native admin console. (FORGEROCK-1582)
26 Jun 2024
Version 13848.8
Key features
- Certificate API[14] (FRAAS-7319)
-
You can now use the certificate API to upload SSL certificates to your tenant environments. You can create the certificates in two ways:
-
Use a tenant-generated private key that is only accessible by the tenant itself. The tenant generates the CSR, and you install the resulting certificate on the same tenant. Refer to Create a certificate using a tenant-generated private key.
-
Use a locally generated private key that you retain access to. You generate the CSR locally and install the resulting certificate on as many tenants as you need. Refer to Create a certificate using a locally generated private key.
-
- Promotion rollback API (FRAAS-20048)
-
You can now roll back configuration promotions using the API. You can roll back an environment successively to revert as many previous promotion changes as needed.
For more information, refer to Run a rollback.
- New utility binding available for scripting (AME-25519)
-
You can now use a new utility binding in your scripts to access several common utility classes. For example, the utility binding includes classes for generating random UUIDs and for base64 encoding and decoding.
- PingOne Protect nodes (TNTP-180)
-
The following PingOne Protect nodes are now available in the regular channel:
-
These nodes replace the deprecated PingOne Protect Marketplace nodes.
Before using the PingOne Protect nodes, you must:
Enhancements
-
AME-26199: Added the ability to set additional claims, including non-registered claims, during JWT assertion and generation, as per the specification.
-
AME-26820: Provided library scripts with access to all common script bindings.
-
AME-26993: Enhanced secret mapping for agents. Updating a secret label identifier value now causes any corresponding secret mapping for the previous identifier to also be updated, provided no other agent shares that secret mapping. If another agent shares the secret mapping, Advanced Identity Cloud creates a new secret mapping for the updated identifier and copies its aliases from the previously shared secret mapping.
-
AME-27346: Renamed Secret ID Identifier to Secret Label Identifier in the SAML remote entity provider configuration.
-
AME-27478: Renamed Client ID Token Public Encryption Key property to ID Token Encryption Public Key in the OAuth 2.0 client configuration.
-
AME-27775: Added scripting thread pool metrics per script context.
-
OPENAM-16564: Enabled next-generation scripts to access the cookies in incoming requests.
-
OPENAM-21800: Added page node functionality to next-generation scripts.
-
OPENAM-21933: Enabled auto-encoding of the
httpClientform body in next-generation scripts.
Fixes
-
FRAAS-20786: Fixed the case where a promotion attempts to delete the same application more than once.
-
FRAAS-19461: Fixed an issue where large audit logs could be missing from IGA events and processing.
-
FRAAS-20154: ESVs with special characters are now correctly encoded. The workaround of double-encoding ESVs is no longer required.
-
OPENAM-21748: Restored the missing
getwrapper function forHiddenValueCallbackin next-generation scripting. -
OPENAM-21830[8]: Unable to get entitlement info hashmap values in SAML
IdPAdapterscript -
OPENAM-21864: Fixed an issue that prevented setting the tracking cookie to resume a journey after returning from a redirect flow.
-
OPENAM-21897: Corrected inconsistent results from the policy
evaluateTreeendpoint. -
OPENAM-21951: Enabled setting of the
selectedIndexproperty in aChoiceCallbackin next-generation scripts. -
OPENAM-22181: Corrected an issue with UMA
approveandapproveAllrequests failing. -
TNTP-166:
-
Add configuration options to P1 Verify Authentication nodes.
-
Verify code not visible when using QR option.
-
Set claim mapping only in shared state in P1 Proofing node.
-
11 Jun 2024
Version 13664.8
Key features
- Localize the Advanced Identity Cloud admin console[8] (IAM-6267)
-
You can now localize static content and server messages in the Advanced Identity Cloud admin console to support your company’s tenant administrators in different language locales. The localization is implemented in the same way as the existing localization functionality used by the login and end-user UIs. Refer to Configure tenant localization.
- Oracle E-Business Suite app template (IAM-6342)
-
The Advanced Identity Cloud Oracle E-Business Suite (EBS) application lets you manage and synchronize accounts between EBS and Advanced Identity Cloud.
Enhancements
-
FRAAS-15404: When updating ESV secrets, the API saves a new secret version only when it differs from the previous value.
-
FRAAS-19982: Configuration promotion now fails if Advanced Identity Cloud services do not restart successfully with the new configuration.
-
IAM-6376: In the applications rules tab, you can now configure custom logic to perform specific actions, such as sending an email, when an account is successfully created or updated.
-
IAM-6380: In the applications rules tab, you can now use the provisioning failure rule to configure custom logic to perform specific actions when provisioning fails.
Fixes
-
FRAAS-11180: Authentication session whitelisting is now enabled by default for new tenants
-
IAM-5593: Adding roles to certain objects no longer breaks readable titles
-
IAM-6537: Journey import now alerts users if they try to import a file containing missing references
-
IAM-6548[8]: Advanced Identity Cloud admin console now loads Identity Gateway profile properties
07 Jun 2024
| The following issues were released on May 30, 2024 but inadvertently excluded from the changelog. |
Version 13465.7
Key features
- Improved promotion of applications (FRAAS-19241)
-
It is now possible to promote applications via the API and not just the UI.
Additionally, the provisional report has been improved to only show applications that have changed, rather than show all applications in the report.
- Epic EMP application template (IAM-2407)
-
The Epic EMP application lets you manage and synchronize data between Epic EMP and Advanced Identity Cloud.
Enhancements
-
IAM-2653: Configure object properties with user-friendly display names.
-
IAM-3857: Application list view displays enabled/disabled status of enterprise apps.
-
IAM-5913[7]: Create custom access request workflows.
20 May 2024
| The following issues were released on February 6, 2024 but inadvertently excluded from the changelog. |
Key features
- Social Provider Handler node (OPENAM-20924)
-
The new Social Provider Handler node adds an outcome to better handle interruptions in a social authentication journey after requesting profile information.
14 May 2024
Version 13313.2
Key features
- Event-based certification[7] (IAM-5148)
-
Identity Governance now allows tenant administrators to configure certifications that are triggered by specific governance events, a process referred to as event-based certification. This method offers faster certification resolution compared to scheduled—and often lengthy—campaigns spanning weeks or months and involving numerous applications, intricate rules, and hundreds of reviewers.
The event-based certifications feature kicks off an identity certification for the following events:
-
User create. Advanced Identity Cloud detects when a user account has been created.
-
User modify. Advanced Identity Cloud detects when an existing user account has been modified or updated.
-
Attribute change. Advanced Identity Cloud detects changes in the attributes of an existing user account.
-
User delete/deactivate. Advanced Identity Cloud detects if a user account has been deleted or deactivated.
For more information, refer to Certify access by event.
-
- Grant entitlements to users and roles[7] (IAM-5146)
-
Identity Governance now allows tenant administrators to carry out more fine-grained entitlement grants for their user accounts. Tenant administrators can now:
-
Create a role and grant entitlements to the role.
-
Revoke entitlements in a role.
-
Grant entitlements to a user account.
-
Revoke entitlements from a user account.
For more information, refer to Manage entitlements.
-
- Authenticate gateway and agent profiles with a shared secret (IAM-5833)
-
The Advanced Identity Cloud admin console for gateways and agents now lets you authenticate with a shared secret instead of a password. Use this to set the label for the shared secret.
- Authenticate OAuth 2.0 applications with a shared secret (IAM-6028)
-
The Advanced Identity Cloud admin console for OAuth 2.0 applications now lets you authenticate with a shared secret instead of a password. Use this to set the label for the shared secret.
Enhancements
-
IAM-3199: HTML styling in the Message node journey editor allows you to left justify text.
Fixes
-
FRAAS-19334: Failure to look up service account names following changes applied through the ESV API.
-
IAM-5079[7]: End-user roles page sometimes shows role grants as conditional even when the grants are direct.
-
IAM-5363[7]: Show the total number of approvals and access reviews in the inbox.
-
IAM-5858[7]: Missing support for access request global configuration options.
-
IAM-6138[7]: The governance events filter builder incorrectly validates
beforeandafterproperties in the user created state. -
IAM-6176[7]: The end-user access request rejection is missing a justification message.
-
IAM-6203[7]: The governance events filter doesn’t use
aftertemporal values for user created flows. -
IAM-6209: The Advanced Identity Cloud admin console navigation panel text appears when the panel is collapsed.
-
OPENIDM-19879: Identity management reconciliation service processes additional source query pages whenever a query returns a
pagedResultsCookie. -
OPENIDM-19924: Unnecessary quotes not being removed from email addresses.
-
TNTP-166:
-
Add configuration options to P1 Verify Authentication nodes.
-
Verify code not visible when using QR option.
-
Set claim mapping only in shared state in P1 Proofing node.
-
01 May 2024
Version 13162.0
Key features
- Identity Assertion node (AME-26821)
-
The new Identity Assertion node provides a secure communication channel for authentication journeys to communicate directly with PingGateway.
- PingOne Verify service (TNTP-118)
-
The PingOne Verify service lets you configure and use PingOne Verify nodes (PingOne Verify Authentication node and PingOne Verify Proofing node) in your authentication journeys.
For more information, refer to PingOne Verify service.
- PingOne nodes (TNTP-119)
-
- PingOne node
-
The PingOne node node establishes trust between PingOne and Advanced Identity Cloud by leveraging a federated connection. For more information, refer to PingOne node.
- PingOne DaVinci API node
-
The PingOne DaVinci API node node lets an Advanced Identity Cloud journey trigger a PingOne DaVinci flow through the API integration method. For more information, refer to PingOne DaVinci API node.
Enhancements
-
AME-26085: SAML v2.0
NameIDmapping can be configured per SP -
AME-27126: A SAML SP can now authenticate to IDPs using mutual TLS (mTLS) when making an artifact resolution request.
-
AME-27133: "Secret ID" has been renamed to "Secret Label" for secret mappings
-
The following services now support configuration using the Secrets API:
-
AME-16536: The OAuth 2.0 provider hash salt secret
-
AME-25885: The persistent cookie core authentication attribute
-
AME-26110: The client-side session signing key
-
AME-26134: The social provider service
-
AME-26441: The new CAPTCHA node (replaces the legacy CAPTCHA node)
-
AME-26442: The OIDC Token Validator node now lets you store the client secret in any type of secret store
-
AME-26633: The OAuth 2.0 client
clientJwtPublicKey -
AME-26637: The OAuth 2.0 client
idTokenPublicEncryptionKey -
AME-26639: OAuth 2.0 client mTLS self-signed certificates
-
AME-26668: The post authentication process (PAP) replay password
-
AME-26670: The web agents replay password key
-
AME-26998: The OAuth 2.0 client secret
-
-
The following services now support rotation of secrets using secret versions:
-
AME-25988: The persistent cookie encryption secret
-
AME-26999: OAuth 2.0 client secrets
-
AME-27000: OAuth 2.0 client
clientJwtPublicKey -
AME-27001: OAuth 2.0 client mTLS self-signed certificates
-
-
OPENAM-21031: The performance of Google KMS has been improved by the introduction of caching.
Fixes
-
FRAAS-19596: Promotion report should include changes to realm authentication settings.
-
OPENAM-21473: If you set the collection method of a Certificate Collector node to
REQUEST,HEADER, orEITHER, and the certificate is not provided in the request or in the header, the node now returns a status ofNot collected.
22 Apr 2024
Version 13019.10
Key features
- Additional cloud connectors
-
The following connectors are now bundled with Advanced Identity Cloud:
-
Dropbox connector (OPENIDM-19838)
-
PingOne connector (OPENIDM-19736)
-
Webex connector (OPENIDM-19920)
For more information, refer to the ICF documentation.
-
Enhancements
-
OPENIDM-19921: The following connectors included with Advanced Identity Cloud were upgraded to 1.5.20.21:
-
Google Apps connector
-
Microsoft Graph API connector
-
AWS connector
For details, refer to 1.5.20.21 Connector changes.
-
16 Apr 2024
Version 13019.8
Enhancements
-
FRAAS-19414: You can now configure custom domains directly in all environments without needing to create ESVs or promote configurations. Existing custom domains will be migrated automatically.
-
FRAAS-19566: Add
_sortKeysquery parameter to ESV API -
IAM-4585[7]: Request and approvals page now shows the current and past approvers, their decisions, and the dates
-
IAM-4968: Expose additional top-level parameters in the advanced section of mapping pages
-
IAM-5674: Target application can use ONBOARD action for FOUND situation
-
IAM-5769: Add grouping logic to journey node items
Fixes
-
IAM-3927[7]: Identity Governance now enforces mandatory comments (if configured) for revoke and allow exceptions
-
IAM-4309[7]: Access reviews no longer display the internal
lastSyncuser attribute -
IAM-4762: Authoritative apps are now requestable
-
IAM-4986: Platform UI can now determine whether to use a pagedResultsCookie or offset for paging results
-
IAM-5076[7]: "Abstain from action" option no longer displays when a campaign has expired
-
IAM-5362: Marking a property as an authoritative app entitlement no longer causes target app config to be generated
-
IAM-5413: Account deprovisioning now works in AD/LDAP after deleting a user identity
-
IAM-5794: Border color of sign-in input fields in hosted pages can now be overridden in themes
-
IAM-5810: Add option for email configuration to specify UTF-8 address support
-
IAM-5814: Allow fixed application usernames to be chosen for custom SAML apps
-
IAM-5875: Journey editor no longer orphans deleted nodes
04 Apr 2024
Version 12820.5
Key features
- HTTP Client node (TNTP-136)
-
The HTTP Client node lets you make HTTP(S) requests to APIs and services external to Advanced Identity Cloud from within a journey.
Use the HTTP Client node to simplify the integration with a broad range of external services by making direct HTTP(S) requests.
For more information, refer to HTTP Client node.
- PingOne Service (TNTP-148)
-
The PingOne Service lets you set up the PingOne service in your Advanced Identity Cloud tenant so you can add Ping Identity nodes to your authentication journeys.
For more information, refer to PingOne Service.
03 Apr 2024
Version 12820.5
Enhancements
-
FRAAS-19341: ESV support for AES keys through the
base64aesencoding typeFor more information, refer to Encoding format.
-
IAM-5602: Add functionality for viewing and deleting user’s trusted devices in Advanced Identity Cloud admin console
For more information, refer to Manage trusted devices (tenant administrators) and Configure visible information and end user actions (end users).
26 Mar 2024
Version 12589.7
Key features
- Implemented "remember me" functionality
-
You can now display a checkbox on the end user sign-in card that makes it remember and pre-populate the username.
Refer to Customize sign-on and end-user pages
Enhancements
-
FRAAS-15371: Added ability to prevent search engines from indexing end user login pages
-
IAM-4257: Updated Azure AD app template to accommodate the latest changes
-
IAM-4342: Updated MSGraphAPI Connector with a new configuration property
-
IAM-4892: Updated Salesforce app template to accommodate the latest changes
-
IAM-4900: Added build number and next release cycle date range to user interface
-
IAM-5334: Exposed guarded string as an object type property in scripted template
-
IAM-5459: KBA answer field should contain question context
-
IAM-5461: Custom login error not read with priority
-
IAM-5503: Rename "Orchestrations" to "Workflows"
-
IAM-5563: Updated Google Apps app template to accommodate the latest changes
-
IAM-5603: Added ability to view device details for managed user identities
-
IAM-5606: Added "POWERED BY" metadata to journey nodes
-
IAM-5748: Made 'PingOne' a special case on the federation providers page
Fixes
-
IAM-4918: Check that user has correct permissions when requesting access for other users
-
IAM-5287: Make username, password, and KBA fields H3 elements
-
IAM-5598: Prevent styled terms and conditions included in a journey from making authenticate call fail
-
IAM-5611: Correct ability to revoke custom apps from roles, or edit them from the role view
-
IAM-5641: Custom Endpoints search returned endpoints created by other areas of the UI
-
IAM-5692: Remove console errors when opening the "Add Bravo user" modal
-
IAM-5767: SAML SSO was not remembered when app is saved from another tab after SSO setup
-
IAM-5873: Fix
.getTranslationcall in Vue -
OPENIDM-19405: Special non-ascii characters in emails sent from Advanced Identity Cloud would fail
25 Mar 2024
Notices
ForgeRock deprecated the option to let Advanced Identity Cloud tenant administrators skip 2-step verification on Friday, February 3, 2023.
This is a reminder that the end-of-life date for this deprecation is Tuesday, April 2, 2024, when the skip option functionality will be removed from Advanced Identity Cloud.
You have until this date to update your tenants to make 2-step verification mandatory for all tenant administrators. For more information, refer to Tenant administrator mandatory 2-step verification FAQ.
13 Mar 2024
Enhancements
-
FRAAS-19288: Autonomous Access and Identity Governance are now available in the Jakarta (asia-southeast2) region
05 Mar 2024
Deprecations
- Duo authentication node (FRAAS-19062)
-
ForgeRock has deprecated the Duo authentication node because Duo has deprecated Traditional Duo Prompt that is used by the Duo node.
ForgeRock created Duo Universal Prompt node in anticipation of this depreciation. You should use Duo Universal Prompt node instead of Duo node (Deprecated).
Refer to Duo Universal Prompt node.
28 Feb 2024
Notices
ForgeRock deprecated the option to let Advanced Identity Cloud tenant administrators skip 2-step verification on Friday, February 3, 2023.
The end-of-life date for this deprecation has been moved to Tuesday, April 2, 2024, when the skip option functionality will be removed from Advanced Identity Cloud.
You have until this date to update your tenants to make 2-step verification mandatory for all tenant administrators. For more information, refer to Tenant administrator mandatory 2-step verification FAQ.
16 Feb 2024
Notices
ForgeRock deprecated the option to let Advanced Identity Cloud tenant administrators skip 2-step verification on Friday, February 3, 2023.
The end-of-life date for this deprecation is Friday, March 1, 2024, when the skip option functionality will be removed from Advanced Identity Cloud. You have until this date to update your tenants to make 2-step verification mandatory for all tenant administrators. For more information, refer to Tenant administrator mandatory 2-step verification FAQ.
08 Feb 2024
Key features
- Advanced Identity Cloud security guide update
-
ForgeRock has updated the Advanced Identity Cloud security guide to advise caution with using the
X-Forwarded-ForHTTP header to identify the originating IP address of a client due to security and privacy concerns.Instead, you should consider using the
X-Real-IPorX-Trusted-Forwarded-ForHTTP headers as trusted replacements. Refer to Identify originating client IP addresses.
06 Feb 2024
Key features
- Create and manage custom relationship properties (OPENIDM-19106, OPENIDM-19109)
-
You can now create and manage custom relationship properties using the Advanced Identity Cloud admin console.
- Schema API improvements (OPENIDM-19107)
-
You can now directly modify managed object schemas over REST using the schema API. This capability includes configuring custom relationship properties.
- Password timestamps (OPENIDM-19262)
-
Enabling this new feature lets you view or query when a user password was last changed and when it is set to expire.
- Fingerprint Profiler and Fingerprint Response nodes (TNTP-130)
-
The Fingerprint nodes nodes let you integrate your Advanced Identity Cloud environment with the Fingerprint platform to help reduce fraud and improve customer experience.
- iProov Authentication node (TNTP-131)
-
The iProov authentication node integrates Advanced Identity Cloud authentication journeys with the Genuine Presence Assurance and Liveness Assurance products from iProov.
- RSA SecurID node (FRAAS-18037)
-
The RSA SecurID node lets you use the RSA Cloud Authentication Service (RSA ID Plus) or RSA Authentication Manager from within an authentication journey on your Advanced Identity Cloud environment.
Enhancements
-
OPENIDM-17878: Allow access to operational attributes in the Advanced Identity Cloud data store
-
OPENIDM-19674: The relationship-defined virtual property (RDVP) schema editor allows you to edit the
flattenPropertiesproperty. The anaged object schema editor allows you to edit thenotifyRelationshipsproperty.
Fixes
-
FRAAS-18398: Allow the HTTP OPTIONS method on calls to /openidm/config/* endpoints for CORS preflight checks
-
FRAAS-18526: Script library functionality can’t be used in the UI in certain environments
-
IAM-5656: Fix alignment of text, buttons, and links in Message nodes
-
IAM-5660: Hosted pages not displaying list of themes
-
OPENIDM-18743: Attempts to use connectors fail with null pointer exceptions when
operationOptionsis defined in the provisioner configuration -
OPENIDM-18957: The scheduler now attempts to release any triggers it attempted to acquire during a timeout due to an unresponsive repository
-
OPENIDM-19141: Workflow engine queries now properly honor
tablePrefixandtablePrefixIsSchemaconfiguration options -
OPENIDM-19279: Resource collection is required to create a relationship
22 Jan 2024
Key features
- Advanced Identity Cloud use case catalog
-
Introducing the release of the Advanced Identity Cloud use case catalog, a collection of guides that focus on tenant administrator use cases and third-party integrations.
19 Jan 2024
Key features
- New Identity Governance capabilities[7][15] (IAM-4617, IGA-1664)
-
The Workflow UI lets you define custom workflow definitions for all access request types.
Role membership certification, a new certification type for access reviews, lets you review and certify roles and the users who have access to roles. Primary reviewers are role owners, a single user, or users assigned to a role.
09 Jan 2024
Key features
- Schedule jobs directly in the Advanced Identity Cloud admin console (IAM-3489)
-
You can now schedule the following jobs directly in the Advanced Identity Cloud admin console without using the IDM native admin console:
-
Scripts: Execute a script at a regular interval.
-
Task scanner: Execute a scan of identities using a complex query filter at a regular interval. The scan can then execute a script on the identities returned by the query filter.
-
Enhancements
-
FRAAS-7382: Add ability to include JavaScript snippets in login and end-user UIs
-
IAM-4514[7]: Allow reviewers to add user, entitlement, and role columns to an access review
-
IAM-4739: Add read schema option to SCIM application template to discover custom schemas/attributes
-
IAM-5138[8]: Add ability to view reports to end-user UI
-
IAM-5201: Focus on first input field or button automatically upon page load
-
IAM-5268: Add source-missing situation rule to authoritative applications
Fixes
-
IAM-4810: Custom endpoint UI missing context option
-
IAM-5072: Inbound mapping tab shows in target applications
-
IAM-5171: Azure Active Directory application template doesn’t return a user’s role membership
-
IAM-5187: LDAP v2.1 application template doesn’t clear
dc=example,dc=combase DN -
IAM-5238: LDAP application template is missing the group object classes property
-
IAM-5422[7]: Entitlement owner doesn’t show in the entitlement list
-
OPENAM-21856: Introspecting stateless token with IG/Web agents will cause
OAuth2ChfException
2023
12 Dec 2023
Key features
- Duo Universal Prompt node (FRAAS-15675)
-
The Duo Universal Prompt node lets you provide two-factor authentication using Duo’s Universal Prompt authentication interface. You can integrate Universal Prompt with your web applications using the Duo Web v4 SDK.
For details, refer to Duo Universal Prompt node.
Enhancements
-
AME-22326: The
httpClientavailable in scripts now automatically adds the currenttransactionIdas an HTTP header. This lets you correlate caller and receiver logs to make requests to other ForgeRock products and services. -
AME-25392: Add
org.forgerock.openam.scripting.api.PrefixedScriptPropertyResolver, used for accessing ESVs from scripts, to the allowlist forSAML2_SP_ADAPTERandSAML2_IDP_ADAPTERscript types -
AME-25433: Add
com.sun.crypto.provider.PBKDF2KeyImpl,javax.crypto.SecretKeyFactory, andjavax.crypto.spec.PBEKeySpecto the allowlists for Scripted Decision nodes and Configuration Provider nodes -
AME-25608: Add auditing for opening and closing connections for the LDAP decision node, ID Repo service, and Policy Configuration service
-
AME-25630: Add
java.security.spec.InvalidKeySpecExceptionto the allowlist for the Scripted Decision and Configuration Provider nodes -
FRAAS-17939: Some connectors included with Advanced Identity Cloud were upgraded to the following versions:
1.5.20.19For details, refer to 1.5.20.19 Connector changes.
-
Microsoft Graph API connector
-
SCIM connector
1.5.20.18For details, refer to 1.5.20.18 Connector changes.
-
Google Apps connector
-
Microsoft Graph API connector
-
Salesforce connector
-
SCIM connector
-
Workday connector
-
-
IAM-4511: Hide fields in the Users & Roles tab when editing and creating unreadable properties
-
IAM-4615: Add a "Skip to main content" link to page headers
-
OPENAM-16897: The OAuth 2.0 Device grant flow can now return either JSON or HTML
-
OPENIDM-19037: Update property value substitution to reflect boolean value in the UI
Fixes
-
COMMONS-1397: Audit event log entries not logged due to thread contention
-
FRAAS-17686: Add
org.forgerock.json.jose.jwe.JweHeaderto the allowlists for theAUTHENTICATION_TREE_DECISION_NODEandCONFIG_PROVIDER_NODEscript types -
IAM-4401: Disabling
Clear-Site-Dataheader breaks realm login -
IAM-4991: When a
suspendedIdis in use, redirect tofailureUrlfails -
IAM-5075: Login messages are read twice by screen readers
-
IAM-5186: User identity related values aren’t saved after removal
-
OPENAM-17331: Disabled SNS endpoints can now be re-enabled
-
OPENAM-17816: OAuth 2.0 requests without a
Content-Typeheader fail with a 500 error -
OPENAM-19282: Recovery Code Display node only works immediately after a registration node
-
OPENAM-19889: Policy evaluation fails when subject is agent access token JWT
-
OPENAM-20026: Social IDP with trailing whitespace in the name can’t be deleted using the UI
-
OPENAM-20329: Issuer missing from OAuth 2.0 JARM response
-
OPENAM-21053: Missing
userIdfrom access audit log whenorg.forgerock.security.oauth2.enforce.sub.claim.uniqueness=falsein JWT client authentication flow -
OPENAM-21421: Scripting logger name isn’t based on logging hierarchy convention
-
OPENAM-21476: Persistent cookie is not created when using Configuration Provider node
-
OPENAM-21484: Introspection of a stateful refresh token for claims field for known OAuth2 fields is now a string and not nested in a list
-
OPENIDM-19328: Fix queued sync to recover following node restart
30 Nov 2023
Fixes
-
IAM-5275: Advanced Identity Cloud admin console doesn’t add query parameters to the logout URL
-
IAM-5289: Fix warning message when
maxidletimeis greater than 24.8 days
Notices
ForgeRock deprecated the option to let Advanced Identity Cloud tenant administrators skip 2-step verification on Friday, February 3, 2023.
The end-of-life date for this deprecation is Friday, March 1, 2024, when the skip option functionality will be removed from Advanced Identity Cloud. You have until this date to update your tenants to make 2-step verification mandatory for all tenant administrators. For more information, refer to Tenant administrator mandatory 2-step verification FAQ.
14 Nov 2023
Key features
- Next generation scripting enhancements (AME-25928)
-
The next generation scripting engine for journey decision node scripts lets you:
-
Reduce the need to allowlist Java classes with a stable set of enhanced bindings.
-
Simplify scripts with fewer imports and more intuitive return types that require less code.
-
Debug efficiently with clear log messages and a simple logging interface based on SLF4J.
-
Make requests to other APIs from within scripts with a more intuitive HTTP client.
-
Modularize your scripts by reusing common code snippets, including external libraries such as CommonJS, with library scripts.
-
Access identity management information seamlessly through the
openidmbinding.
The next generation engine can’t use legacy scripts.
If your Scripted Decision node uses legacy scripts, you must convert them to use updated bindings to take advantage of the benefits of the next generation scripting engine.
Where possible, you should migrate legacy scripts to take advantage of next generation stability.
For more information, refer to Next-generation scripts.
-
- Gateway Communication node (FRAAS-17380)
-
Lets Advanced Identity Cloud authentication journeys communicate directly with the PingGateway (PingGateway).
This secure communication channel extends the Advanced Identity Cloud capabilities with PingGateway features, such as validating a Kerberos ticket and performing other certificate handshakes.
For details, refer to Gateway Communication overview.
Enhancements
-
FRAAS-3841: Activate and deactivate journeys in the Advanced Identity Cloud admin console. Refer to Deactivate journeys.
-
IAM-4191: Allow tenant session cookie name to be configured. Refer to Session cookie name.
-
IAM-4735: Add support for schema discovery in application templates
-
IAM-4806: Show outbound tenant IP addresses in Advanced Identity Cloud admin console. Refer to Access global settings.
-
IAM-4853: Add AS400 application template. Refer to the AS400 section in Provision an application.
Fixes
-
FRAAS-16785: Incorrect positioning of reCAPTCHA v2 elements
-
FRAAS-17883: Tenant administrators cannot save edits to their personal information
-
IAM-2936: Journeys hang indefinitely when using a State Metadata node within a Page node
-
IAM-4521: Screen readers announce field labels twice
-
IAM-4956: Advanced Identity Cloud admin console doesn’t use the current realm when logging out
-
IAM-5113: Unable to remove an NAO assignment from a user in Advanced Identity Cloud admin console
-
IAM-5226: Tenant administrator security questions should not be shown when editing personal information
-
IAM-5240: No error message displays when a tenant administrator fails to save edits to their personal information
31 Oct 2023
Key features
- New Autonomous Access capabilities[16] (DATASCI-1269)
-
Autonomous Access User access behavior and tenant access behavior UI pages let administrators understand the typical authentication behavior for a selected user or for all users in the tenant for the past six months by displaying key metrics. Administrators can filter the UI to show certain login metrics, like time of day, city, country, day of week, device used for login, operating system, and browser type. Administrators can also compare a selected user’s authentication behavior to that of the authentication attempts for all other users in the tenant.
Enhancements
-
FRAAS-17373[17]: The following connectors included with Advanced Identity Cloud were upgraded from 1.5.20.15 to 1.5.20.17:
-
Adobe Marketing Cloud connector
-
Google Apps connector
-
Microsoft Graph API connector
-
Salesforce connector
-
SCIM connector
Some highlights include:
-
OPENICF-900: SCIM connector: Add support for dynamically generated SCIM schemas
-
OPENICF-2453: SCIM connector: Persist optional refresh token upon successful access token renewal
For a complete list of enhancements and fixes, refer to Connector changes.
-
-
IAM-4211: Display disaster recovery region in the Advanced Identity Cloud admin console
-
IAM-4369: Remove AM applications from application list view
-
IAM-5045: Display pop-up warning when an end user is about to be logged out of an Advanced Identity Cloud hosted page
Fixes
-
ANALYTICS-311: The
USER-LAST-LOGINreport doesn’t show results if the last journey failed -
FRAAS-17413: Improve IDM service reliability during upgrades and routine maintenance
-
IAM-4698: Fix accessibility issues with messages in page nodes
-
IAM-4812: Correctly save array ESVs containing newline characters
-
IAM-4863: Display ESV buttons properly when the user gives them focus
-
IAM-4877: Display ESV selection button properly while user is modifying a script associated with a Scripted Decision node
17 Oct 2023
Key features
- OneSpan Identity Verification node (FRAAS-13738)
-
Sends request to OneSpan to analyze the image and determine whether the document is genuine or fraudulent.
For details, refer to OneSpan Identity Verification node.
- OneSpan Get User Authenticator (FRAAS-13160)
-
Retrieves the authenticators assigned to a user and helps enable user’s authentication and security levels.
For details, refer to OneSpan Get User Authenticator node.
- New Identity Governance capabilities[7] (IGA-1691)
-
Access requests let end users request access to resources and let managers request that access be removed from their delegates. The list of resources an end user can request access to is referred to as the access catalog.
Manage access request workflows is a new feature that lets you optionally define flows to include business logic, decisions, and approvals. For example, decide what happens when an approver rejects an access request for an application. Workflows currently only supports access request-related features.
New options in the Advanced Identity Cloud end-user UI let end users submit access requests, submit requests to remove access, and review assigned request items:
-
The My Requests option lets you view and create access requests to resources (applications, roles, entitlements) for yourself or on behalf of others.
-
The My Directory > Direct Reports option lets managers submit access removal requests.
-
The Inbox > Approvals option lists request items (requests an end user submits) for an approver (designated owner) to act on.
-
Enhancements
-
IAM-3648: ESV placeholders can now be entered from a drop-down list
-
IAM-3651: ESV placeholders can now be entered from key-value input fields
-
IAM-4236: Improve layout of the applications reconciliation tab
-
IAM-4367: Separate the connection status of OAuth 2.0 client applications into a dedicated list
-
IAM-4662: ESV placeholders can now be entered from tag input fields
-
IAM-4717: Added date, datetime, and time fields to the login UI
-
IAM-4789: Grant roles now show temporal constraints
-
OPENAM-20847: Sanitized HTML can now be added into messages for the Email Suspend node
Fixes
-
FRAAS-17235: Validate ESV values correctly when they are wrapped in white space
-
FRAAS-17283: Tenant status pages not automatically updated during downtime
-
IAM-4235: Passthrough authentication using AD connector fails if set up in UI and user DN includes a space
-
IAM-4418: Fix accessibility issues with multi-select input fields
-
IAM-4489: Align checkbox color with other form elements
-
IAM-4491: Correctly label sidebar buttons when expanded or collapsed
-
IAM-4492: Make navigation bars in end-user UI accessible for screen readers
-
IAM-4528: Outbound reconciliation mapping preview shows generated password value
-
IAM-4798: The
aria-labelis now correctly displayed for all component types on sidebar buttons -
OPENIDM-19192: Personal information is still editable by end users when User Editable is set to
false
03 Oct 2023
Key features
- Query Parameter node (AME-24069)
-
Allows you to insert query parameter values from a journey URL into configurable node state properties. This lets you customize journeys based on the query parameter values.
For details, refer to Query Parameter node.
Enhancements
-
IAM-3650: Add a drop-down menu to checkbox inputs for selecting ESV placeholders
-
IAM-3826: Add the ability to specify a source and transformation script when mapping application properties.
-
IAM-4515: Include autocomplete attribute with login form fields
-
IAM-4525: Update profile picture modal with accessibility improvements for screen readers
-
IAM-4567: Add a warning when running reconciliations and selecting the
persistAssociationsoption. For details, refer to View a report about the last reconciliation. -
IAM-4576: Increase time on screen for loading spinner so that screen readers can announce it
-
IAM-4616: Include contextual information with the show/hide buttons for improved accessibility
-
OPENAM-21073: Request headers are now accessible in OAuth 2.0/OIDC scripts for
OIDC_CLAIMS,OAUTH2_ACCESS_TOKEN_MODIFICATION, andOAUTH2_MAY_ACTscript contexts using therequestPropertiesbinding -
OPENAM-21346: Add classes
java.util.concurrent.TimeUnit,java.util.concurrent.ExecutionException, andjava.util.concurrent.TimeoutExceptionto the scripting allowlist -
OPENAM-21355: Jakarta AWS region (ap-southeast-3) enabled for the PingAM push notification service
-
OPENAM-21416: Canada Central AWS region (ca-central-1) enabled for the PingAM push notification service
Fixes
-
IAM-4366: Provide browser-specific logic to handle alternative CSS for accessibility
-
IAM-4409: Require at least three characters before running identity searches when there are more than 1000 identities of that type
-
IAM-4460: Screen readers read show/hide buttons for security questions as show/hide password
-
IAM-4478: Only allow certain combinations of properties in a mapping transformation script
-
IAM-4493: Fix the heading hierarchy in the UI
-
IAM-4523: Screen readers read avatar alt text when tabbing to action menu
-
IAM-4524: Two buttons with different labels open the same dialog
-
IAM-4568: Do not enable the option to change a user association in the UI
-
IAM-4584: Drop-down boxes fail ADA compliance
-
IAM-4639: String/password field button is highlighted in the UI
-
IAM-4703: Fix display of password fields in some themes
-
IAM-4710: Fix rounded border of password fields in hosted pages
-
IAM-4829: Eye icon displays over the password field highlight box in the UI
-
OPENAM-18599: Allow customization of the error message that displays to end users when their account is locked or inactive using
.withErrorMessage()in a Scripted Decision node -
OPENAM-18685: Use the OAuth2 Provider service in the AM admin console to specify if tokens issued should contain the
subnameclaim -
OPENAM-19261: Errors are incorrectly logged when triggered by introspection of tokens using OAuth 2.0 client credentials grant
-
OPENAM-20451: The WebAuthn Registration node now displays an end user’s
userNamewhen registering a device when the identity’s name isn’t human-readable -
OPENAM-21158: Add support for trusted platform module (TPM) attestation using elliptic curve cryptography (ECC) unique parameter validation starting with Windows 11 version 22H2
-
OPENAM-21304: The
request_urisfield does not populate when OAuth 2.0 clients register using dynamic client registration
26 Sep 2023
Fixes
-
FRAAS-17278: Health status reports for AM, IDM, and Admin services incorrectly reported as available in some situations
-
IAM-4843: The user column in the certification task list now shows a user’s full name instead of only the first name
-
IAM-4903[18]: Fix IGA calls that are not working in a custom domain
-
IAM-4915[18]: Fix Access Review UI that shows the JSON object of the manager relationship in the User Details modal
05 Sep 2023
Key features
- Salesforce Community User application template (IAM-4340)
-
Provision, reconcile, and synchronize Salesforce, Salesforce Portal, and Salesforce Community accounts.
For details, refer to Salesforce application template or Salesforce Community User application template.
- OneSpan Auth VDP User Register node (FRAAS-15426)
-
Registers end users to authenticate using the virtual one-time password (VOTP).
For details, refer to OneSpan Auth VDP User Register node.
- OneSpan Auth Assign Authenticator node (FRAAS-15426)
-
Assigns a VIR10 authenticator to an end user if the end user isn’t already assigned to one. Requires a VIR10 authenticator to be available in the tenant.
For details, refer to OneSpan Auth Assign Authenticator node.
- OneSpan Auth Generate VOTP node (FRAAS-15426)
-
Generates a virtual one-time password (VOTP) and delivers it to an end user through the node’s configured delivery method. Requires the end user to be assigned to a VIR10 authenticator.
For details, refer to OneSpan Auth Generate VOTP node.
28 Aug 2023
Key features
- Add preference-based provisioning to Privacy and Consent settings (IAM-4243)
-
End users in target applications can share their data with other applications. After the end user configures a preference to share data with other applications, data from the target application is synchronized with Advanced Identity Cloud.
For details, refer to End-user data sharing.
Enhancements
-
AME-25061: Provide additional context information in Marketplace authentication nodes to enable UI improvements
-
IAM-3502: Add the ability to set and reset a sync token for identity management account object type. For details, refer to Reset the last reconciliation job.
-
IAM-3678: Update error messages and labels in login and signup pages
-
IAM-3962: Improve design of push number challenge page for Push Wait node
-
IAM-4248: Add three additional non-account objects to ServiceNow page
-
IAM-4326: Improve onLink script to handle mapped properties of type array and object
-
IAM-4334: Update SuccessFactors application templates to support Advanced Identity Cloud built-in SuccessFactors connector
Fixes
-
IAM-3877: UI loader spins indefinitely when realm is deactivated
-
IAM-4093: Replace Google Fonts in the login UI to meet GDPR compliancy requirements
-
IAM-4176: Advanced setting query filter does not show all available properties
-
IAM-4240: Accessibility issues in Page node when NVDA readers are used
-
IAM-4261: Accessing end-user UI with query parameter "code" displays empty page
-
IAM-4371: Unable to create applications due to
userpasswordproperty set -
IAM-4384: Platform UI does not resume journeys with custom redirect logic
-
IAM-4427: Platform UI does not show assignments for tenants running deprecated application management
-
IAM-4475: Platform UI does not load after tenant administrator signs into an upper tenant during promotion
-
IAM-4533: Journeys do not resume correctly when returning from a social identity provider without a realm identifier
-
IAM-4534: Redirect callbacks for journeys not working correctly
-
OPENAM-18004: Audit logging does not specify transaction IDs correctly for internal requests to certain APIs
-
OPENAM-18709: Calls to the
nodeState.get()method in Scripted Decision nodes do not return values in shared state when a variable is stored in both shared state and secure state -
OPENAM-20230: Calls to classes in the allowlist fail occasionally with access prohibited messages
-
OPENAM-20682: Unable to encrypt
id_tokenerror when there are multiple JWKs with the same key ID but different encryption algorithms -
OPENAM-20691: Session quota reached when oldest session is not destroyed due to race condition
-
OPENAM-20783: Logging is incorrect when the authorization code grant flow is used successfully
-
OPENAM-20920: Null pointer exceptions when a SAML v2.0 binding is null and the SSO endpoint list contains non-SAML v2.0 entries
-
OPENAM-20953: Policy evaluation with a subject type
JwtClaimreturns HTTP response code 500 -
OPENAM-21001: Custom scripted SAML v2.0 IDP account mappers are determined incorrectly
-
OPENAM-21004: Invalid session ID error when session management is disabled in an OIDC provider
-
OPENAM-21046: The Create Object and Patch Object nodes do not log exception stack traces when they can’t retrieve the object schema
-
OPENAM-21164: XML string formatted incorrectly when using a custom adapter to get the assertion from a SAML v2.0 response
19 Jul 2023
Deprecations
- Introspect endpoint GET requests and URL query string parameters (FRAAS-10638)
-
ForgeRock has deprecated the following behaviors of the OAuth 2.0
introspectendpoint in Advanced Identity Cloud:-
Accept GET requests
-
Accept data in POST requests from URL query string parameters
You can continue to use these behaviors, but they will be removed on July 19, 2024. Instead, when using the OAuth 2.0
introspectendpoint, you should use POST requests and pass data in the POST request body.Refer to /oauth2/introspect.
-
17 Jul 2023
Fixes
-
OPENIDM-19245[8]: Fix IDM version qualifier to prevent ForgeRock REST proxy error
07 Jul 2023
Fixes
-
FRAAS-16041: Support Basic Authentication for Identity Cloud logging endpoints
-
OPENIDM-19240[8]: Fix the "internal server error" message when configuring reconciliation mappings
27 Jun 2023
Key features
- New Identity Governance capabilities[7] (IGA-1592)
-
Entitlements are specific permissions given to an account in an onboarded target application. Each entitlement correlates to a permission. Pull in entitlements from all onboarded target applications into Advanced Identity Cloud for use in certifications.
Entitlement assignment certification, a new certification type for access reviews, lets you review and certify entitlements and the users who have access to entitlements on some or all applications. Primary reviewers are entitlement owners, a single user, or users assigned to a role.
The governance glossary lets you attach business-friendly attributes to applications, entitlements, and roles to add more specificity to the data you review in access certifications.
New options in the Advanced Identity Cloud end-user UI let you view your access, your direct reports, and the access your direct reports have:
-
The My Access option lets you view your access in Advanced Identity Cloud and onboarded target applications. This includes accounts from onboarded target applications, roles you are assigned in Advanced Identity Cloud, and entitlements or privileges you have in onboarded target applications.
-
The Direct Reports option lets you get access information for individuals you manage. This includes their profile information, accounts from onboarded target applications, roles they are assigned in Advanced Identity Cloud, and entitlements or privileges they have in onboarded target applications.
-
- Lexis-Nexis ThreatMetrix Authentication nodes (FRAAS-15325)
-
Integrate Lexis-Nexis ThreatMetrix decision tools and enable device intelligence and risk assessment in Advanced Identity Cloud.
For details, refer to ThreatMetrix Authentication nodes.
- Filter log results (FRAAS-15378)
-
Use the
_queryFilterparameter to filter log results on any field or combination of fields in a payload. For details, refer to Filter log results. - Microsoft Graph API email client (OPENIDM-17899)
-
Configure the email client to use the MS Graph API Client for sending email.
For more information, refer to Microsoft Graph API email client.
- Included connectors and framework upgraded to OpenICF 1.5.20.15
-
The connectors included with Advanced Identity Cloud have been upgraded from version 1.5.20.12 to 1.5.20.15. Some highlights include:
-
MS Graph API Connector: Add the ability to read
applicationandservicePrincipalobject (OPENICF-2208) -
MS Graph API Connector: Implement application role assignments (OPENICF-2269)
-
SCIM Connector: Support for throttling (OPENICF-1916)
For a complete list of enhancements and fixes, refer to Connector changes.
-
Enhancements
-
IAM-2826: Filter the "Assignments" tab for identities so that it does not show overrides, entitlements, or resources
-
IAM-3408: Let provisioners use a range of connector versions
-
IAM-3677: Remove increment/decrement arrows from numeric input fields
-
IAM-3678[8]: Improved ADA accessibility for error messages associated with input fields
-
IAM-3982: Let users filter risk activity using distributed attack as a risk reason
-
IAM-3983: Show distributed attack as a risk reason in the risk dashboard
-
IAM-4051: Improved ADA accessibility for drop-down boxes
-
IAM-4053: Improved ADA accessibility when NVDA readers are used on pages that use the Page node
-
IAM-4074: Add a loading animation to the pie chart component
-
IAM-4136: Use the tab key to move focus and remove tags in multi-select components
Fixes
-
FRAAS-5756[8]: Journeys don’t resume after authentication in downstream identity provider
-
FRAAS-9230: Sanitize
aria-hiddenfields -
FRAAS-14214: Changing an existing ESV type is now denied by the API and new ESVs always require an explicit type
-
FRAAS-14262: Include changes to group privileges in the configuration promotions report
-
FRAAS-14706: Improve the detection of changes to complex configuration files and IDM script hooks in promotion reports
-
FRAAS-14897: Improve the rate limiting behavior of the
/monitoring/logsendpoint -
IAM-2026: Support versioning of the application and connector templates
-
IAM-2713: Prohibit editing of managed application objects
-
IAM-2972: Route users to the correct realm after granting Salesforce permissions
-
IAM-3089: Unable to exit a social provider and select a different social provider in a journey
-
IAM-3594: Correctly redirect control to the End User UI after authenticating with itsme
-
IAM-3719: Modals not showing display access review comments and activity
-
IAM-3939: Let end users switch to a different authentication journey
-
IAM-4013: When using a custom domain,
originalLoginRealmis set incorrectly -
IAM-4116: Don’t let access review users add reviewers with greater privileges than they themselves have
-
IAM-4134: User pop-up is visible in "Entitlement" tab
-
IAM-4200: Last certified date, decision, and actor displaying incorrectly in Governance account details
-
IAM-4242: Add "Conflicting changes" category to reconciliation summary
-
IAM-4289: Unable to assign non-account object properties to roles
-
IAM-4293: Access reviews and line items not shown for staged campaigns
-
IAM-4295: Reviewer not redirected back to pending reviews after access review sign off
-
OPENIDM-17481: Managed object schema can now describe a field as a nullable array and specify a default value for this field if not provided in a create request
-
OPENIDM-17771: Processing of a large number of scheduled jobs no longer causes all scheduled tasks to continuously misfire
-
OPENIDM-18192: Updating a relationship-defined virtual property (RDVP) on a managed object by signal receipt no longer causes other RDVP state within that object to be lost
-
OPENIDM-18292[8]: Add support for the
_fieldsrequest parameter to the syncgetTargetPreviewendpoint. -
OPENIDM-18360: Use the full object state when validating requests made by a delegated administrator to modify a relationship
-
OPENIDM-18613: Provide the ability to remove the
userPasswordattribute -
OPENIDM-18644: Correctly determine whether it’s possible to configure clustered reconciliation
-
OPENIDM-18807[8]: Update user provisioning workflow sample to check for empty manager strings
-
OPENIDM-18895: Fixes support for multi-version concurrency control on managed object patches and updates
-
OPENIDM-18898[8]: Add support for the
_countOnlyparameter in identity management scripts -
OPENIDM-18980[8]: Add a new metric to measure the duration of a LiveSync event
-
OPENIDM-19098[8]: Enable ES6 support for identity management scripts
13 Jun 2023
Key features
- Administrator federation enhancements (FRAAS-12097)
-
- Groups support
-
The new groups feature allows you to add and remove administrators depending on group membership in your identity provider. Using administration groups lets you automate the granting and removing of access for administrators that are being on-boarded, switching roles, or leaving your organization.
- OIDC Federation
-
OIDC is now supported as a federation identity provider, along with Microsoft ADFS and Microsoft Azure.
For more information, refer to Configure federated access for tenant administrators.
- OIDC ID Token Validator node (OPENAM-13293)
-
The new OIDC ID Token Validator node lets Advanced Identity Cloud rely on an OIDC provider’s ID token to authenticate an end user. The node evaluates whether the ID token is valid according to the OIDC specification.
For details, refer to OIDC ID Token Validator node.
- Scripted SAML 2.0 SP adapter (AME-21638)
-
Customize the SAML 2.0 SP adapter using a script.
For details, refer to SP adapter.
Enhancements
-
AME-24073: Expose the
prompt_values_supportedparameter of the provider configuration at the OIDC.well-knownendpoint -
AME-24175: Provide additional classes in the allowlist that scripts used in the Scripted Decision node
-
FRAAS-13293: Provide more accurate and granular information in promotion reports
-
FRAAS-14063: Remove orphaned unused scripts during promotion
-
FRAAS-15022: Improve promotion reports
-
IAM-2561: Allow adding applications to a user or role from the Identities > Manage page
-
IAM-3666: Add alternative text to QR code image
-
IAM-3676: Add keyboard controls to UI to select multiple values in multivalued lists
-
IAM-4030: Improve handling of identity provider and groups claims
-
IAM-4031: Generic OIDC configuration returns HTTP 400 Bad Request
-
OPENAM-18692: Set the minimum value for the Default Max Age property to
0 -
OPENAM-19745: Add support for EdDSA signing algorithm to WebAuthn Registration node
-
OPENAM-20541: Add additional inner classes to scripting allowlist to support RSA keypair generation
Fixes
-
AME-24026: Allow specifying inputs required by the provider scripts in the Configuration Provider node
-
IAM-3550: When attempting to validate Office 365 applications, a blank screen appears
-
IAM-3580: Improve service accounts UI including error handling
-
IAM-4032: Federation enforcement is missing from the UI
-
FRAAS-10816: Include thread ID and remove control characters from some Identity Cloud log files for easier log correlation
-
FRAAS-14956: Promotion preview and report not showing all configuration changes
-
FRAAS-15188: Ensure environments can be recreated after deletion
-
OPENAM-12030: Authentication node instances are deleted when journeys containing them are deleted
-
OPENAM-13329: Display journeys with spaces in their name in the Authentication Configuration drop-down menu
-
OPENAM-13766: Route user session based on whether policy evaluation is requested or not
-
OPENAM-17179: Correctly delete a script if its referring journey is deleted
-
OPENAM-17566: Display account name instead of UUID in the ForgeRock Authenticator when using MFA
-
OPENAM-18488: Support certificate-based attestation in certificate chains terminating at an intermediate CA
-
OPENAM-20082: Show correct error message to locked out users
-
OPENAM-20104: Fix the fragment response mode for the OAuth 2.0 authorize endpoint
-
OPENAM-20187: Fix the "waiting for response" page so that it fails authentication as configured in the authentication journey
-
OPENAM-20230: Prevent class allowlist from failing for classes already on the allowlist
-
OPENAM-20318: Allow a restricted set of HTML tags to be rendered in page node headers and descriptions
-
OPENAM-20360: Fix default URL encoding to ensure ampersand characters are not double encoded in a SAML assertion
-
OPENAM-20386: Fix authentication node state reconciliation in some complex journeys
-
OPENAM-20451: Fix WebAuthn registration node to return a human-readable username
-
OPENAM-20457: Device Location Match node routes to "Unknown Device" outcome instead of failing the authentication journey when the previously stored location of the device is not provided
-
OPENAM-20479: Enhance OIDC authentication to handle unsecured JWS requests
Deprecations
- Deprecate health check endpoints (FRAAS-15623)
-
ForgeRock has deprecated the following Advanced Identity Cloud health check endpoints:
-
/am/isAlive.jsp -
/am/json/health/live -
/am/json/health/ready -
/openidm/info/ping
You can continue to use the endpoints, but they will be removed on June 13, 2024.
You should update any external monitoring to use the Advanced Identity Cloud
/monitoring/healthendpoint instead.Refer to Monitor using health check endpoint.
-
07 Jun 2023
Key features
- UAT environment (FRAAS-13196)
-
You can now add one additional environment to your standard promotion group of development, staging, and production tenant environments. A UAT environment has the same capabilities as your staging environment, which allows your organization an additional production-like environment in which to test your development changes.
A UAT environment is an add-on capability.
For details, refer to UAT environments.
- Secure Connect (FRAAS-15187)
-
You can now use ForgeRock Secure Connect to create dedicated, direct, and secure communication between your Advanced Identity Cloud network and your private network, such as an on-premises data center or IaaS provider. Secure Connect bypasses the public internet, improving latency, throughput, and security.
Secure Connect is a limited availability feature.
For details, refer to Secure Connect.
16 May 2023
Key features
- PowerShell connector
-
Use the PowerShell Connector Toolkit to register a connector that can provision any Microsoft system.
For details, refer to PowerShell.
- SAP SuccessFactors Account or SAP SuccessFactors HR connector
-
Use the SAP SuccessFactors connectors to synchronize SAP SuccessFactors users with Advanced Identity Cloud users.
For details, refer to SAP SuccessFactors Account or SAP SuccessFactors HR.
- Bookmark application
-
You can now register a bookmark application - for example, OneNote, Evernote, Google Bookmarks, or raindrop.io - to direct users to specific URLs. A bookmark application displays shortcut links on dashboards. When you click one of the links, the browser opens a new tab.
For details, refer to Bookmark.
- Microsoft Intune node
-
Integrates Microsoft Intune to control features and settings on Android, Android Enterprise, iOS/iPadOS, macOS, and Windows 10/11 devices in your organization.
For details, refer to Microsoft Intune node.
- Secret Double Octopus (SDO) nodes
-
PingOne Advanced Identity Cloud integrates with Secret Double Octopus (SDO) to provide high-assurance, passwordless authentication systems that address the diverse authentication needs of a real-world, working enterprise.
For details, refer to Secret Double Octopus (SDO) nodes.
Fixes
| Issue ID | Summary |
|---|---|
IAM-2911 |
Add support for bookmark apps in application management |
IAM-3472 |
Update promotions UI to set tenant color dynamically based on the tenant name |
IAM-3518 |
Make Auto Access dashboard data realm specific |
IAM-3560 |
Add new default SCIM object types and mappings |
IAM-3563 |
Access review progress tooltip not working in end-user UI |
IAM-3630 |
Add SuccessFactors template and connector configuration |
IAM-3656 |
Display sign-off button in access review page in admin UI |
IAM-3666 |
Add alt text to QR code |
IAM-3667 |
Add visual indication of keyboard focus on input fields |
IAM-3681 |
Improve accessibility of the |
IAM-3682 |
Line items not showing for completed access reviews |
IAM-3688 |
Validate campaign deadline dates in admin UI |
IAM-3703 |
Campaign owner is duplicated in user drop-down after reconciliation run |
IAM-3734 |
Ensure relationship resource collection grids filter based on managed object settings |
IAM-3778 |
Allow login UI to work when browser session storage is unavailable |
IAM-3792 |
Prevent login UI rendering extra whitespace character in front of text on suspended nodes |
IAM-3806 |
Remove beta indicator from the trends chart in admin UI dashboard |
IAM-3840 |
Change color of radio button changed in Choice Collector node |
IAM-3879 |
Ensure global variable |
IAM-3887 |
Enhance |
IAM-3910 |
New PowerShell configuration properties |
IAM-3922 |
Risk score definition on autonomous decision node is not working |
IAM-3937 |
Risky events are not shown in the risk dashboard |
IAM-3964 |
Risk reasons do not display in the risk dashboard |
OPENAM-18895 |
Fix API request timeout errors for slow connections |
OPENAM-20815 |
Add missing footer to Page node when session expired |
OPENIDM-18917 |
Display last name instead of user ID on user profile when no first name is provided |
TNTP-42 |
Microsoft Intune marketplace node |
TNTP-45 |
Secret Double Octopus marketplace node |
02 May 2023
Key features
- Support for all Google Fonts for hosted pages
-
Meet your organization’s brand guidelines by using any Google Font in your hosted pages.
Fixes
| Issue ID | Summary |
|---|---|
FRAAS-13247 |
Set the log API key creation date correctly |
IAM-1686 |
Allow any Google Font to be used on hosted pages |
IAM-3164 |
Prevent table columns from stacking vertically on smaller viewports |
IAM-3313[7] |
Additional Options section missing from Identity Certification campaign template |
IAM-3950 |
End-user UI fails to load when accessing Advanced Identity Cloud in a new tab |
OPENIDM-18988 |
Prevent repository reads when anonymous users make requests to info and ping endpoints |
21 Apr 2023
Resolved issues
| Issue ID | Summary |
|---|---|
OPENIDM-18967[20] |
RelationshipArray grid queries use unnecessary |
18 Apr 2023
Key features
- IP allowlisting
-
Enterprises often need to ensure that requests entering their network come from trusted sources. PingOne Advanced Identity Cloud now offers outbound static IP addresses for all environments.
Outbound static IP addresses let you implement network security policies by setting up allowlists of IPs originating from Advanced Identity Cloud. This adds an extra layer of security to outbound calls to your APIs or SMTP servers.
For more information, refer to Outbound static IP addresses.
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-5995 |
Outbound request static IP allows IP allowlisting for new customers |
FRAAS-9376 |
Provide the ability to display a login journey in an iframe for specific custom domains. To implement this feature, you need to open a support ticket. |
FRAAS-13522 |
Promotion report does not include changes to custom email provider |
FRAAS-14097 |
Promotion report should identify journeys by their name |
FRAAS-14187 |
Updated user registration cloud logging to capture events from identity providers |
FRAAS-14260 |
UI displays "Resource 'managed/alpha_application' not found" message |
FRAAS-14265 |
Cannot access ESVs in sandbox tenants |
FRAAS-14353 |
Configuration placeholder replacement assumes a string value |
FRAAS-14475 |
Certain searches cause |
OPENIDM-18957 |
Update the scheduler to attempt to release any triggers it previously attempted to acquire from a timeout due to an unresponsive repository |
11 Apr 2023
Key features
- PingOne® Identity Governance (add-on capability)
-
PingOne Identity Governance is a new add-on capability that allows you to centrally administer and manage user access to applications and data across your organization to support regulatory compliance.
With Identity Governance you can:
-
Work with onboarded target applications when reviewing user data. This allows you to review user data for onboarded applications.
-
Define and launch reviews of data using certification campaigns.
-
Review and manage user access to applications. This includes managers reviewing the access their direct reports have.
For more information, refer to About Identity Governance.
To purchase an Identity Governance subscription, contact your ForgeRock representative.
-
- Administrator federation
-
Administrator federation allows administrators to use single sign-on (SSO) to log in to an Advanced Identity Cloud tenant.
By using federation to authenticate your administrators to Advanced Identity Cloud, you can quickly and easily deprovision an administrator by removing their access from your centralized identity provider.
For details, refer to Configure federated access for tenant administrators.
Resolved issues
| Issue ID | Summary |
|---|---|
IGA-1433 |
Initial release of Identity Governance with identity certifications |
FRAAS-5416 |
Administrators can access Advanced Identity Cloud using single sign-on from another identity provider |
OPENDJ-9295[8] |
Search with |
29 Mar 2023
Key features
- OneSpan authentication journey nodes
-
The new OneSpan authentication journey nodes integrate OneSpan Intelligent Adaptive Authentication (IAA) scoring for identity proofing, continuous authentication, and fraud protection.
For details about OneSpan authentication integration set up, refer to OneSpan.
- Jumio identity verification
-
The new Jumio identity verification integrates with Jumio’s NetVerify service to easily and securely verify identity by using facial recognition to authenticate against government issued IDs.
For details about Jumio identity verification, refer to Jumio identity verification.
- Logout for all server-side sessions for a user or set of users
-
Administrators can now invalidate (log out) all server-side sessions for a user by sending a POST request to the
json/sessionsendpoint with thelogoutByUseraction, specifying the username in the request payload.
- Composite advice with an AuthLevelCondition in journeys
-
Composite advice gives AM hints about which authentication services to use when logging in a user. Journeys now take into account the AuthLevelCondition composite advice.
For example, you can now use AuthLevelCondition composite advice so that AM uses a journey that provides an authentication level of 10 or higher.
- Promotions API documentation
-
The promotions API documentation is now publicly available at https://apidocs.id.forgerock.io/#tag/Promotion.
- SCIM built-in connector
-
You can now use the SCIM built-in connector to manage user and group accounts on any SCIM-compliant resource provider.
- Support for REST connector applications
-
Application management now lets you create, provision, and manage REST connector applications.
For details, refer to Scripted REST connector.
Resolved issues
| Issue ID | Summary |
|---|---|
AME-21638 |
Scripted plugin for SAML 2.0 SP Adapter |
AME-22942 |
Log out all server-side sessions for a user or set of users so that they have to reauthenticate |
FRAAS-5416 |
Let administrators access Identity Cloud using single sign-on from another identity provider |
FRAAS-8225 |
The promotions API documentation is now publicly available at https://apidocs.id.forgerock.io/#tag/Promotion |
FRAAS-8709 |
Include the log sources in the logged events |
FRAAS-12402 |
Add /platform/oauthReturn route to support authentication for Salesforce and Google Apps |
FRAAS-12413 |
OIDC login from a custom domain results in blank page |
FRAAS-13454 |
Integrate Jumio identity verification journey nodes |
FRAAS-13555 |
Integrate OneSpan authentication nodes |
FRAAS-13478 |
Promotions report shows changes that it shouldn’t |
FRAAS-13597 |
Remove unexpected changes from promotion reports |
FRAAS-13866 |
Let Identity Cloud administrators access policy configuration |
FRAAS-13933 |
Make managed groups visible in the AM admin UI |
FRAAS-13974 |
Add class |
FRAAS-13983 |
Remove OneSpan nodes from the Basic Authentication journey node list |
FRAAS-14030 |
Add inner classes from |
FRAAS-14069 |
Add |
FRAAS-14260 |
UI displays "Resource 'managed/alpha_application' not found" message |
FRAAS-14265 |
Cannot access ESVs in sandbox tenants |
IAM-662 |
Fixed agent logout in platform UI |
IAM-2879 |
Allow properties in forms to be reordered |
IAM-2921 |
In the Dashboard, the total number of applications that display in the Applications box now includes those applications registered using the new app catalog in tenants created on or after January 12, 2023. |
IAM-3089 |
Unable to exit a social provider and select a different social provider in a journey |
IAM-3094 |
Add support for enumerated values in array attributes |
IAM-3156 |
Update the descriptive text in the "Add Property" modal to be more accurate |
IAM-3160 |
Added ability to configure the scripted Groovy connector |
IAM-3180 |
Hide the SSO tab when an application is authoritative |
IAM-3193 |
Updated SCIM app template to only show the refresh token property for OAuth authentication |
IAM-3261 |
Adjust Autonomous Access risk filter to better handle scoring edge cases |
IAM-3262 |
Adjust menu width on the Autonomous Access Risk Administration page |
IAM-3303 |
Enable clicking a row to edit entries on the service accounts page |
IAM-3304 |
Added breadcrumbs to the service accounts page |
IAM-3305 |
Added a search field to the service accounts page |
IAM-3461 |
Fix display of OAuth 2.0 applications with a UUID for a name |
IAM-3462 |
Corrected AD template property from |
IAM-3478 |
Addressed accessibility concerns when displaying password policy validation |
IAM-3492 |
Fix objects ending in |
IAM-3642 |
Fixed an issue with unselected applications being imported when promoting, and improved the user experience for selecting and deselecting applications in the promotions UI |
IAM-3694 |
Added ability to customize the success color in hosted pages |
IAM-3760 |
Apple social authentication works with other authentication methods |
OPENAM-16374 |
Add support in journeys for composite advices that use an AuthLevelCondition |
OPENAM-18270 |
Don’t raise errors when calls to the access_token endpoint specify the scope parameter in OAuth2 authorization_code exchange |
OPENAM-18488 |
Handle the CA certificate correctly for Windows Hello attestations |
OPENICF-400 |
The LDAP connector now correctly reads the AD Account tokenGroups attribute |
OPENICF-1762 |
IBM RACF API connector |
OPENICF-1858 |
Add group owners management support to the Microsoft Graph API connector |
OPENICF-2033 |
PeopleSoft connector v2.0 |
OPENICF-2039 |
Add archived, languages, isEnrolledIn2Sv, and isEnforcedIn2Sv fields to the Google Apps connector |
OPENICF-2067 |
Adjust license assignments as part of the user creation and update operations in the Google Apps connector |
OPENICF-2068 |
The Microsoft Graph API connector now lets you assign and revoke directory roles to an Azure AD user account and query the target instance for roles |
OPENICF-2088 |
The Microsoft Graph API connector now lets you assign and revoke custom roles to an Azure AD user account and query the target instance for roles |
OPENICF-2102 |
Assign and revoke PermissionSets and Groups to Salesforce user accounts in the Salesforce connector |
OPENICF-2110 |
Expose groups and roles through user object in the ServiceNow connector |
OPENICF-2111 |
View, update, and remove a group’s roles through the role object in the ServiceNow connector |
OPENICF-2129 |
The LDAP connector now includes a parameter to use isMemberOf by ldapGroups |
OPENICF-2192 |
In the Google Apps connector, don’t throw an NPE when updating a user with a change to license assignments if _NAME_ is not specified |
OPENICF-2194 |
In the GoogleApps connector, the PATCH remove operation doesn’t update the object when both the field and value are provided |
OPENIDM-17876 |
Query filter editor no longer removes double quotes from all properties that aren’t of type string |
OPENIDM-17936 |
Saving changes to the authzRoles field on users no longer overrides the field type |
OPENIDM-18001 |
Country codes in locales are no longer ignored when sending emails |
OPENIDM-18077 |
Added new default policy, cannot-contain-others-case-insensitive |
OPENIDM-18153 |
Custom script exception messages are no longer incorrectly truncated in REST responses |
OPENIDM-18216 |
IDM admin UI should query recon association data instead of audit data |
OPENIDM-18238 |
Improved resiliency of clustered reconciliations |
OPENIDM-18243 |
Validate that connector names are alphanumeric |
OPENIDM-18260 |
New sync mapping fields, defaultSourceFields and defaultTargetFields, let you specify which fields to use for read and query requests |
OPENIDM-18261 |
Endpoints within /system now support specifying additional fields when using wildcards |
OPENIDM-18275 |
The groups' name field is now searchable |
OPENIDM-18319 |
An up-to-date target object state is now provided in sync script bindings and sync audit mechanisms |
OPENIDM-18336 |
The default assignment object schema now contains a "condition" field |
OPENIDM-18476 |
The IDM admin UI now defaults identity object number fields to |
OPENIDM-18498 |
Queued sync not triggered if target is a CREST proxy endpoint |
OPENIDM-18501 |
Tenant administrator password policy no longer restricts passwords to a maximum length |
OPENIDM-18629 |
Reconciliation job identifiers now use a more precise timestamp |
OPENIDM-18650 |
Add new SCIM connector; applications now support creating connections to SCIM services |
OPENIDM-18865 |
Script changes cannot be saved unless you click outside the Inline Script box |
OPENIDM-18868 |
Inability to save a schedule when you add or remove a passed variable |
OPENIDM-18870 |
Inability to delete an inline reconciliation or schedule script |
15 Mar 2023
Key features
- Improved access to reconciliation logs in Advanced Identity Cloud
-
You can now view IDM reconciliation logs in your tenant by updating your audit configurations and specifying the log source
idm-reconin a call to the logging API endpoint.For more information, refer to Update audit configuration.
14 Feb 2023
Key features
- Application promotions
-
You can now use the UI to promote applications between tenant environments. Promoted applications are recreated in the upper environment with any associated static configuration (connectors, mappings, or SAML configuration) and any associated dynamic configuration (OAuth 2.0 clients).
For more information, refer to Manage self-service promotion of applications using the UI.
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-7542 |
Control access to hosted account and journey pages |
FRAAS-11599 |
Don’t allow changes to scripts in staging and production environments |
FRAAS-13464 |
Adjust sandbox environment migration to not use development environment migration steps |
FRAAS-13809 |
Autonomous log filters fail in connected environments |
IAM-2725 |
Adjust input field placeholders to clear properly when a user starts typing |
IAM-3084 |
Only allow unique values when adding application owners |
IAM-3141 |
Add the ability to promote dynamic configuration attached to application |
IAM-3151 |
Remove redirect to global settings during administrator login |
IAM-3183 |
Let users filter the trends dashboard by date without resetting the journeys dashboard |
IAM-3339 |
After refreshing the realm settings page, set the current tab using the identifier specified in the URL fragment |
IAM-3512 |
Access Management native console incorrect redirect URL |
OPENIDM-16640 |
Changes to identity objects by onUpdate scripts not triggering relationship property onRetrieve hooks |
03 Feb 2023
Key features
- Deprecate skip option for tenant administrator MFA
-
ForgeRock has deprecated the option to let Advanced Identity Cloud tenant administrators skip 2-step verification. Customers can continue to use the skip option in their tenants, but this functionality will be removed from Advanced Identity Cloud on February 3, 2024.
31 Jan 2023
Key features
- Service accounts
-
You can now use service accounts to request access tokens for most Advanced Identity Cloud REST API endpoints without relying on a particular identity in your system:
-
Call Identity Cloud APIs programmatically without needing a human identity.
-
Access AM or IDM APIs in the same way using a signed JWT.
-
Set scopes on each service account to assign only necessary permissions to access tokens.
-
Use for automation and CI/CD tooling.
For details, refer to Service accounts.
-
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-13478 |
Remove unrelated AM root realm changes from promotion reports |
FRAAS-13519 |
Remove unexpected file changes from self-service promotion reports |
FRAAS-13620 |
Improve performance of promotion report generation by removing unrelated data |
FRAAS-8477 |
Service accounts |
IAM-1939 |
Fix hCaptcha support in Platform UI |
IAM-2025[8] |
Add Uncategorized to the journey category filter |
IAM-2224 |
Replace bullets with checkmarks when validating password policy |
IAM-2305[8] |
Add support for localized logos in end-user UI |
IAM-2847 |
Increase the size of the terms and conditions modal window |
IAM-2912 |
Enable promotions UI to ignore encrypted secrets |
IAM-3011 |
Update risk configuration UI to show only user-modifiable configuration |
IAM-3012 |
Add new |
IAM-3015 |
Update risk configuration evaluation UI so that updates use the new APIs |
IAM-3016 |
Fix the |
IAM-3041 |
Prevent proceeding from the Active Directory modal window without entering base DNs |
IAM-3076 |
Fix Salesforce provisioning connection |
IAM-3079 |
Fix single sign-on (SSO) setup when app name has a space |
IAM-3088 |
Enable suppression of the login failure message from the failure node |
IAM-3091[8] |
Fix localized headers rendering as [object Object] |
IAM-3107[8] |
Remove bitwise filter on Active Directory page |
IAM-3108[8] |
Update Maintain LDAP Group Membership option to not be selected by default |
IAM-3109[8] |
Update cn property to be optional in Active Directory target mode |
IAM-3110[8] |
Update ldapGroups property to be available by default in Active Directory target mode |
IAM-3111[8] |
Fix password hash algorithm |
IAM-3122 |
Fix font weight of the title text on provisioning tab |
IAM-3139[8] |
Fix Revoke button in Users & Roles to revoke users, and not be clickable when there are no users to revoke |
IAM-3142[8] |
Fix Active Directory user filter anomaly when deleting a row |
IAM-3145 |
Fix Active Directory assignment on array attributes to be a merge and not replace |
IAM-3146[8] |
Update user-specific attributes to be editable by administrators |
IAM-3177 |
Add paging back to application list view if workforce feature is not enabled |
IAM-3257[8] |
Fix escaping of ESV placeholders in the advanced email editor |
IAM-3335 |
Fixed display of localized favicon |
19 Jan 2023
Key features
- BioCatch authentication nodes
-
The new BioCatch authentication nodes integrate BioCatch scoring for identity proofing, continuous authentication, and fraud protection.
For details, refer to Marketplace.
Resolved issues
| Issue ID | Summary |
|---|---|
AME-22948[8] |
Create endpoint to log out sessions based on user identifier |
FRAAS-11964 |
Avoid potential performance degradation when removing expired token state |
FRAAS-12140 |
Integrate BioCatch authentication journey nodes |
FRAAS-13242 |
Improve invalid page size error message |
OPENAM-13766[8] |
No configuration found for log in with session condition advice deny |
OPENIDM-17392 |
Prevent script typos that cause services to fail from being introduced into the system |
OPENIDM-17664 |
LDAP connector has invalid configuration when whitespace added to Base DN |
OPENIDM-17953 |
Support email addresses that contain non-ASCII UTF-8 characters |
12 Jan 2023
Key features
- Workforce application and connector management
-
In new tenants created on or after January 12, 2023, you can use the improved applications page to integrate Advanced Identity Cloud with external data stores or identity providers. The applications page acts as a one-stop location where you can:
-
Register and provision popular federation-capable applications quickly and easily by choosing from a library of templates, such as Salesforce and Workday.
-
Register and provision your organization’s custom applications.
-
Manage data, properties, rules, SSO, provisioning, users, and groups for an application.
-
View the connection status of each application.
-
Activate and deactivate an application.
For details, refer to Application management.
-
- Event hooks
-
Event hooks let you trigger scripts during various stages of the lifecycle of users, roles, assignments, and organizations.
You can trigger scripts when one of these identity objects is created, updated, retrieved, deleted, validated, or stored in the repository. You can also trigger a script when a change to an identity object triggers an implicit synchronization operation.
Post-action scripts let you manipulate identity objects after they are created, updated, or deleted.
For details, refer to Event hooks.
- Daon IdentityX authentication nodes
-
The new Daon authentication nodes let you integrate with the Daon IdentityX platform for MFA with mobile authentication or out-of-band authentication using a separate, secure channel.
For details, refer to Marketplace.
- Onfido authentication nodes
-
The new Onfido authentication nodes let you use Onfido’s solution for collecting and sending document identification and, optionally, biometrics to the Onfido backend for verification.
For details, refer to Marketplace.
Resolved issues
| Issue ID | Summary |
|---|---|
DATASCI-1548 |
Update the filter text on the Autonomous Access dashboard from "All Risk Scores" to "Risk Score" |
DATASCI-1550 |
Update text on the Autonomous Access dashboard’s Copy on User Detail page |
FRAAS-11158[8] |
AM cache outdated during restart of Identity Cloud services |
FRAAS-11574 |
Integrate Daon authentication journey nodes |
FRAAS-11575 |
Integrate Onfido authentication journey nodes |
FRAAS-11964 |
Avoid potential performance degradation when removing expired token state |
FRAAS-12477 |
Add list of encrypted secrets to promotion reports |
FRAAS-12492[8] |
Add classes to the scripting allow list |
FRAAS-12494 |
Unlock the environment and stop checking progress after successfully promoting an environment |
FRAAS-12545 |
Remove the option to keep orphaned configuration nodes from the promotions API |
FRAAS-12552 |
Add redirect for custom domain login screen |
FRAAS-12713 |
Promotions API failed to generate a report |
FRAAS-12917[8] |
Email invites to sandbox tenant administrators sometimes do not work |
FRAAS-12939 |
Add proxy state to output of lock state endpoint for promotions API |
FRAAS-12988 |
Prevent placeholder support being enabled unless a specific migration flag value is set |
FRAAS-13057 |
Add only standard placeholders (not user-defined placeholders) prior to enabling placeholder management |
FRAAS-13082[8] |
Provisional report endpoint can return 500 if requested repeatedly before cache is built |
FRAAS-13121 |
Provisional reports can cause promotion service to run out of memory and restart |
FRAAS-13244 |
Unable to log into tenant to perform self-service promotion |
IAM-2658 |
Application management improvements |
OPENAM-19485 |
Access multi-tenant social providers without requiring multiple secondary configurations |
OPENIDM-17556 |
Ensure RDVPs are not erased for all types of managed objects for all types of PUT operations |
OPENIDM-17616[8] |
Add support for direct assignments |
OPENIDM-18024[8] |
Implement weighted assignments |
OPENIDM-18037[8] |
Create endpoint for aggregating effective assignments and user identity object type outbound mapping values |
OPENIDM-18063[8] |
Include Google Apps connector in bundled connectors |
OPENIDM-18388[8] |
Do not schedule clustered-recon-resilience jobs for reconById invocations |
2022
14 Dec 2022
Resolved issues
| Issue ID[21] | Summary |
|---|---|
FRAAS-8589 |
Promotion hangs when waiting for Identity Cloud services |
FRAAS-9155 |
Promotion reports not showing changes for all connectors |
FRAAS-11830 |
Promotion reports rendering new line characters inside JSON strings |
FRAAS-11158 |
Restart of AM can lead to outdated cache |
FRAAS-12049 |
Promotion reports not showing changes to custom endpoint scripts |
IAM-2465 |
Password policy to force password expiry not working |
IAM-2706 |
Embedding images in the theme editor only displays alternative text |
IAM-2739 |
Email suspend message displayed without line breaks |
IAM-2939 |
Add translation configuration key for "Passwords do not match" message |
IAM-2973 |
Self-service promotions migration UI flow should enable promotions UI features |
OPENIDM-16830 |
Speed up search for organizations |
OPENIDM-18388 |
Do not flag reconById invocations as clustered |
OPENIDM-18483 |
Add name field to resourceCollection query fields for group identity objects |
29 Nov 2022
Key features
- Group management
-
You can now create and manage groups that are shared across AM and IDM within your Advanced Identity Cloud instance. New tenants have group management enabled by default, and existing tenants can follow an upgrade path to enable it.
For more information, refer to Group management.
- ID Cloud Analytics Dashboard enhancements
-
You can now take advantage of the following enhancements to the analytics dashboard:
-
The journey chart now lets users drill down at specific points on a trend line to view individual journey outcomes for that date/hour. Journeys are sorted by a ranking of percentage failures, but can also be sorted based on number ranking.
-
Two new widgets — Top Five Journeys by Outcome and Top Five Journeys by Usage — that rank trending journeys based on outcomes and usages are now available.
For more information, refer to Advanced Identity Cloud analytics dashboard.
-
09 Nov 2022
Key features
- Self-service promotions
-
Self-service promotions let you promote configuration between environments without raising a support ticket. You can perform self-service promotions from development to staging tenant environments, and from staging to production tenant environments. You cannot promote sandbox environments.
For more information, refer to Introduction to self-service promotions.
- Configuration placeholders visible in all APIs
-
Configuration placeholders let you set ESVs in your configuration.
For more information, refer to Configure placeholders to use with ESVs.
- Duo authentication node
-
The new Duo authentication node lets you use Duo’s solution for adaptive authentication, bring your own device security, cloud security, endpoint security, mobile security, and two-factor authentication.
- Twilio authentication node
-
The new Twilio authentication node allows you to use Twilio for two-factor authentication during account setup, sign-on, and other scenarios. The node lets you integrate Twilio’s APIs to build solutions for SMS and WhatsApp messaging, voice, video, and email. The node uses Twilio’s latest Lookup API, which uses real-time risk signals to detect fraud and trigger step-up authentication when needed.
For details, refer to Marketplace.
Resolved issues
| Issue ID | Summary |
|---|---|
ANALYTICS-52 |
Correct the value in the All Journeys field |
DATASCI-1437 |
Correct prefilled username fields in Filters window |
DATASCI-1474 |
Don’t show explainability if not specified in response after applying Unusual Day of Week filter |
DATASCI-1497 |
Let users see previously selected risk reasons after closing the Filter window |
DATASCI-1504 |
Prevent the truncation of text on the right side of pages |
FRAAS-10979 |
Configuration placeholders visible in all APIs in new customer environments |
FRAAS-11570 |
Add Duo authentication node |
FRAAS-11571 |
Add Twilio authentication node |
FRAAS-11825 |
Add translation configuration key for no search results message |
FRAAS-12219 |
Self-service promotions available in new customer environments |
FRAAS-12301 |
Add Marketplace nodes to journey editor menu |
FRAAS-12413 |
Remove blank page shown when user returns to login page following successful login to custom domain |
FRAAS-12625 |
Handle ESVs as string type if no type is set |
IAM-1935 |
Expose ESV variable type in the UI |
IAM-2038 |
Prevent theme styles rendering in the hosted pages editor |
IAM-2066 |
Show the entire answer to a long security question after clicking the visibility icon |
IAM-2259 |
Do not let users save email templates that contain JavaScript |
IAM-2312 |
Render SVG images correctly |
IAM-2411 |
ForgeRock favicon displays briefly before the customer’s favicon |
IAM-2502 |
Remove flashing red text from security questions window |
IAM-2633 |
Support localization for radio display fields in Choice Collector node |
IAM-2696 |
Remove legend from Risk Score window |
IAM-2869 |
Update UI regex validation for ESV list type |
05 Oct 2022
Resolved issues
| Issue ID | Summary |
|---|---|
AME-22684 |
Include grace period configuration in the OAuth2 provider settings |
DATASCI-1165 |
Remove Automated User Agent from the list of risk reasons filters |
DATASCI-1358 |
Let users filter dashboards by date, risk scores and features |
DATASCI-1365 |
Update the Risk Activity page when applying a filter without requiring users to refresh the page |
DATASCI-1394 |
Show the times that events occurred correctly without requiring users to refresh the display |
DATASCI-1395 |
Let users see their last five risky authentication attempts |
DATASCI-1397 |
Remove risk administration options from end users' navigation menus |
DATASCI-1406 |
When filtering activities using a date range, include the activities that occur on the end date |
IAM-1678 |
Allow login journey attributes that are not required to have empty values |
IAM-1682 |
When editing email templates, cut text correctly |
IAM-1932 |
When placeholders are used, display read-only strings in the Platform UI |
IAM-1933 |
Alter AM XUI to display readonly strings wherever placeholders are in use |
IAM-2028 |
Remove excess space from journey editor fields that do not require floating labels |
IAM-2064 |
Replace fields for specifying numeric thresholds with a risk score definition slider in Autonomous Access Decision nodes |
IAM-2080 |
Let users create customized footers on Page nodes |
IAM-2141 |
Add option to customize Page node background color |
IAM-2142 |
Add option to customize Page node button width |
IAM-2143 |
Add option to customize label text for Page node fields |
IAM-2227 |
Remove spurious "No configuration exists for id external.email" pop-up warning |
IAM-2249 |
Add option to display Message node as a link |
IAM-2250 |
After importing journeys, let user delete all imported journeys with a single delete action |
IAM-2251 |
Provide a value when the object.password variable is specified in an email template |
IAM-2258 |
Remove tenant information from the Realm menu |
IAM-2285 |
Make H2, H3, and H4 HTML headings bigger when there’s no higher-level predecessor heading |
IAM-2290 |
Show the correct number of events per country on the Activity Risk dashboard |
IAM-2294 |
Show previous authentication attempts when doing anomaly lookups |
IAM-2320 |
Change the default navigation background color of Account pages without changing the dashboard color |
IAM-2329 |
Change the color of the Autonomous Access event log indicator to red |
IAM-2351 |
Correct pagination on the Autonomous Access Risk page |
IAM-2373 |
Make dashboard analytics pipeline logs in Autonomous Access work as expected |
IAM-2468 |
Wrap long security questions |
IAM-2521 |
Don’t reuse authId during password validation |
OPENAM-18112 |
Provide better error message when an LDAP authentication node encounters a TLS connection issue |
OPENAM-18933 |
Do not override the Success URL node’s value |
OPENAM-19196 |
Do not wait for cache timeout before OAuth2 clients reflect changes to Javascript origins |
OPENAM-19868 |
Correctly handle multi-line text in Email Suspend nodes |
OPENIDM-16420 |
Update the default email validation policy to conform with RFC 5322 |
OPENIDM-17533 |
Allow configuration changes to the repo.ds.json file to take effect without restarting IDM |
OPENIDM-17720 |
Fix null pointer exception when the repo.ds.json file is misconfigured |
OPENIDM-17836 |
Fix for startup error message caused by ObjectMapping constructor exception |
OPENIDM-17911 |
Fix email validation errors in the IDM admin UI (native console) |
OPENIDM-18272 |
Save managed object properties correctly in Identity Management native console |
SDKS-1720 |
Point developers to the ForgeRock SDKs when they create an OAuth2.0 client in the Platform UI |
SDKS-1721 |
Point developers to the ForgeRock SDKs when they configure CORS in the Platform UI |
24 Aug 2022
Resolved issues
| Issue ID | Summary |
|---|---|
OPENAM-19427 |
Display security questions in the correct default language |
OPENIDM-17644 |
Release scheduled tasks after all failures so they are rerun |
OPENIDM-17858 |
Process job completion instructions when a trigger is not found |
OPENIDM-18123 |
Correctly load scripts that use ISO 8859-1 encoding |
18 Aug 2022
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2282 |
Do not ignore the noSession=true parameter in journeys that do not have Email Suspend nodes |
IAM-2412 |
Left-align long security questions |
IAM-2473 |
Control redirection precedence with AlignGoToPrecedence environment variable |
OPENAM-19631 |
Prevent end users from defining their own security questions in the KBA Definition node (UI fix) |
28 Jul 2022
UI release (hotfix)
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2051 |
Turn off autocomplete for select and multi-select field components |
IAM-2091 |
Fix unstyled content flashing |
IAM-2232 |
Fix Platform Password node validation when allowlisting is enabled for trees |
IAM-2348 |
Localize label text used for confirming passwords |
IAM-2452 |
Fix issue with login callback components mounting twice |
21 Jun 2022
Platform release: 2022.6
Key features
- Workday built-in connector
-
You can now use the Workday built-in connector to synchronize Advanced Identity Cloud easily with a datastore in the Workday cloud service.
Resolved issues
| Issue ID | Summary |
|---|---|
AME-22011 |
Allow OAuth 2.0 clients to override plugin configuration |
OPENAM-13557 |
Add support for JWT Secured Authorization Response Mode for OAuth 2.0 (JARM) |
OPENAM-18223 |
Return 400 Bad Request error code if the id_token_hint is invalid |
OPENAM-18252 |
Allow nodes to update the universal ID for use cases like impersonation and peer authentication |
OPENAM-19028 |
Support social identity providers that provide IDs that are not returned as strings |
OPENAM-19119 |
Provide localization for the URL links on the GetAuthenticatorApp node |
OPENIDM-17659 |
Add the Workday connector as a built-in Identity Cloud connector |
15 Jun 2022
Key features
- Remove log sources for internal services
-
The following log sources are no longer available in the
/monitoring/logsREST API endpoint:-
ctsstore
-
ctsstore-access
-
userstore
-
userstore-access
These sources are for internal services that are managed by ForgeRock, so have been removed to simplify the API.
-
09 Jun 2022
Key features
- Import and export journeys
-
You can now import and export journeys from the Advanced Identity Cloud admin console, making it easier to back up and restore journeys in your environment. You can also import and export associated assets, such as themes and scripts, along with journeys.
- Email template editor enhancements
-
The email template editor now takes better advantage of available space on the the screen. A new preview panel shows you what your template looks like without the need to scroll. A new option in the editor lets you use HTML with CSS, giving you more control over the look and feel of your email templates.
- Journey configuration enhancements
-
You can now take advantage of the following enhancements when you configure journeys:
-
Configure a Choice Collector node to let end users select from a set of radio buttons or a drop-down field.
-
Add a password confirmation field to a Platform Password node by simply selecting a checkbox.
-
Configure a Message node to have a single button instead of two buttons, so that end users can simply acknowledge messages.
-
Customize text in the Next button text on a Page node.
-
Resolved issues
| Issue ID | Summary |
|---|---|
ANALYTICS-8 |
Clarify the tool tip shown with the user engagement graph |
IAM-1649 |
Enhance email template editor |
IAM-1167 |
Add UI for importing and exporting journeys, nodes, and scripts |
IAM-1981 |
Increase use of landmarks across all journeys to improve accessibility |
IAM-1997 |
Make full recovery question visible on password reset page |
IAM-2144 |
Allow confirmation callbacks to have a single outcome and message nodes to show a single button |
IAM-2145 |
Let choice collector nodes show choices as radio buttons |
IAM-2146 |
Add option to require password confirmation |
IAM-2147 |
Make text displayed in the Next button configurable |
IAM-2151 |
Remove text that inadvertently appears in the theme editor |
20 May 2022
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2059 |
Add UI support for Autonomous Access |
IAM-1343 |
Add duplicate option to email templates list |
IAM-1899 |
Convert page node from string to object to support additional feature specifications |
IAM-1962 |
Double password reveal icon in Edge browser in non-login pages |
IAM-1972 |
Changing tenant administrator status resets list sort |
IAM-1980 |
Add font weight slider to themes |
IAM-2004 |
Realms not deleting |
IAM-2010 |
Platform Admin UI rendering with horizontal scroll |
IAM-2050 |
Ensure date inputs include Zulu timezone |
IAM-2065 |
Wrong months order in calendar history of analytics UI date picker |
IAM-2075 |
Make spinner component color inherit from theme primary color |
IAM-2085 |
Allow users to be created without a password in Platform Admin UI |
11 May 2022
Key features
- ForgeRock® Autonomous Access (add-on capability)
-
Autonomous Access is a new add-on capability that provides your Advanced Identity Cloud tenant with significant threat protection capabilities. Autonomous Access helps to prevent account takeover and fraud at the identity perimeter. It leverages artificial intelligence and machine learning techniques to analyze threat signals and anomalous behavior patterns. It speeds and simplifies access decisions, enabling your organization to block threats and deliver personalized journeys that enhance the digital experience of legitimate users.
ForgeRock Autonomous Access includes:
-
ForgeRock Autonomous Access journey nodes:
-
The Autonomous Access Prediction node produces a risk score based on anomalous user behavior, credential stuffing, suspicious IP’s, automated user agents (bots), impossible travelers, and brute force attacks.
-
The Autonomous Access Decision node lets you control users' journeys based on their risk scores.
-
The Autonomous Access Results node, when added to your journeys, provides data that lets Autonomous Access populate the activity dashboard, learn, and make its AI models more accurate.
-
-
The activity dashboard, which shows you risky access activity. It lets you drill down to investigate risky activity across time, risk reason, and risk score.
For more information, see About Autonomous Access.
Interested in adding Autonomous Access to your Advanced Identity Cloud subscription? Contact your ForgeRock account executive.
-
10 May 2022
Resolved issues
| Issue ID | Summary |
|---|---|
AME-21573 |
Add set custom cookie node |
AME-22248 |
Provide option to mandate that clients must use pushed authorization requests |
OPENAM-17698 |
Let users request specific claims from a social identity provider as part of an OIDC request |
OPENAM-18533 |
Distinguish between standard OIDC and JAR OIDC request parameters |
OPENAM-19089 |
Return to user’s UI after completion of a login journey with SAML federation |
OPENDJ-8503 |
Populate the total paged results counter for query responses with an estimate when possible |
02 May 2022
Key features
- New identity store decision node
-
The new Identity Store Decision node lets you make authentication decisions based on user information in Advanced Identity Cloud. You can configure identity store decision nodes to control authentication flow based on any of the following conditions:
-
A username and password exists in Advanced Identity Cloud.
-
The profile associated with a user is locked.
-
A user’s password has expired.
-
A user needed to change their password on first login, but canceled the password change form.
-
19 Apr 2022
Resolved issues
Hotfix release:
| Issue ID | Summary |
|---|---|
DATASCI-1020 |
Correct the times at the bottom of the analytics dashboard charts after clicking Today |
DATASCI-1040 |
Filter journeys correctly in the analytics dashboard |
DATASCI-1041 |
Display months before January 2022 correctly in the analytics dashboard filter |
FRAAS-10342 |
Remove inadvertent popups after administrator signouts |
IAM-2031 |
Fix Platform UI errors during navigation within the UI and resizing the UI window |
11 Apr 2022
Key features
- Dynamic configuration in journey nodes
-
Many nodes have static configuration, which forces you to have a new node for each use case. With dynamic configuration, you can now pass dynamic information to any static node during a journey’s execution.
- Better control over device codes used in the OAuth 2.0 device flow
-
You can now specify the length of generated user codes, and the set of characters that’s used to generate the user codes.
Resolved issues
| Issue ID | Summary |
|---|---|
AME-22015 |
Dynamically resolve configuration in node tree execution |
AME-22247 |
Make request URI single time use for pushed authorization requests |
OPENAM-17756 |
Provide better control over the list of characters used in device codes |
OPENIDM-16774 |
Provide full details of schedules in the IDM admin UI |
OPENIDM-17029 |
Allow IDM string properties to have formats, such as date and time |
OPENIDM-17065 |
Return idm_sync_queue_failed error in Prometheus when an implicit sync fails |
OPENIDM-17116 |
Don’t force persistAssociations=true in a URL that starts a reconciliation operation |
OPENIDM-17204 |
Improve IDM REST API query performance |
OPENIDM-17410 |
Allow time and datetime policies to specify +-00:00 locale |
OPENIDM-17420 |
Allow any number of digits of precision for fractions of seconds when specifying time policy |
SDKS-1329 |
Make push notification compatible with iOS 15 focus mode |
31 Mar 2022
Key features
- Advanced Identity Cloud analytics dashboard
-
The Advanced Identity Cloud analytics dashboard will be the new landing page for tenant administrators. The dashboard gives tenant administrators a snapshot of Ping Identity service usage, including views of the latest metrics and trends for:
-
User engagements
-
New users
-
Total users
-
Applications
-
Organizations
-
Successful and failed journey outcomes
-
25 Mar 2022
Hotfix release:
| Issue ID | Summary |
|---|---|
IAM-1902 |
Extend the Login UI to set transaction IDs for authentication sessions |
IAM-2005 |
Display debug pop-up windows correctly after trees with debug mode enabled fail and are auto-restarted |
24 Mar 2022
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-9031 |
Allow valid characters in "From Name" during Platform UI validation |
IAM-1482 |
Display Internal Role permission dialog correctly |
IAM-1594 |
Eliminate doubled password reveal icon in Microsoft Edge |
IAM-1834 |
Support new Config Provider script type, Config Provider Node, in journey editor |
IAM-1942 |
Don’t throw console error reading filter |
IAM-1945 |
Support undo in email template markdown and style editor |
IAM-1955 |
Enable saving changes to existing email templates |
IAM-1958 |
Improve page load time when there are multiple journeys in one category |
IAM-1964 |
Correct Highlander theme enduser footer |
IAM-1973 |
Clear journey tags when user closes modal window |
IAM-1977 |
Don’t overlay User Name and Password fields in the Login UI when highlighting saved login details |
15 Mar 2022
Key features
- Extend the user identity schema
-
You can now extend the user identity schema by adding your own custom attributes. This lets you store more useful information about each user such as the user’s department, cost centers, application preferences, device lists, and so on.
11 Mar 2022
Key features
- Set categories for end-user journeys
-
You can now set up categories for your end-user journeys in the UI. This helps you manage your trees by grouping them in the list view. For example, you may want to group all your registration journeys together so that you can find them in the list more easily.
- Ability to debug end-user journeys
-
You now have the ability to debug end-user journeys in your development environment, as you create them. By setting a journey to debug mode, you can view information stored in shared, transient, and secure state, as you navigate the journey. This lets you confirm that information is being passed correctly from node to node in the journey.
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-8289 |
Add ability to set categories for a journey |
FRAAS-9382 |
Trailing space after the T&C link on the self registration journey |
IAM-1711 |
Invited tenant administrators have doubled usernames |
IAM-1536 |
Add debug controls to journey editor |
IAM-1896 |
Creating consecutive applications with a different type shows the wrong logo and headline |
IAM-1903 |
Unable to localize the display of 2FA and push authentication device names |
OPENIDM-17479 |
Recognize IDM static role naming convention when assigning UI roles |
02 Mar 2022
Key features
- Scripted Plugin for SAML 2.0 IdP adapter
-
The new scripted SAML 2.0 IdP adapter lets you introduce your own business logic during a SAML 2.0 authentication flow. You can use it to look up session, policy, or identity related information, and make routing decisions before sending the SAML 2 assertion to the service provider. Refer to Customize SAML 2.0.
- Support for OAuth 2.0 Pushed Authorization Requests (PAR)
-
The OAuth 2.0 Pushed Authorization Request (PAR) is an RFC specification that allows a secure way of initiating an OAuth or OIDC authorization flow. PAR enables you to move the authorization request data from the URL query string to the request object. This protects the authorization request from any potential tampering. Confidential clients are also authenticated when registering the PAR and this enables the platform to refuse any unauthorized or malformed requests early in the process, reducing the load from any malicious attacks. Refer to Authorization code grant with PAR.
Resolved issues
| Issue ID | Summary |
|---|---|
AME-21830 |
Remove feature flag for PAR endpoint |
AME-21943 |
Add OAuth2 Provider config options for plugin types |
AME-21947 |
OAuth2 scripted plugin selection improvements |
AME-22060 |
OAuth2 authorize endpoint throws NPE for a query parameter without a value |
AME-22066 |
Scripted plugin for SAML 2.0 IDP adapter |
OPENAM-17590 |
OIDC login hint cookie using deprecated Set-Cookie2 header |
OPENAM-18185 |
Add support for PKCE to OAuth2 device code grant |
OPENAM-18264 |
Update Apple profile normalization script template for sign-in with Apple |
OPENAM-18459 |
IdTokenInfo endpoint fails when using client ID in POST |
OPENAM-18527 |
Add ability to track suspended authentication session |
OPENAM-18918 |
Unable to add scopes in the modification script when using OAuth2 with Grant Set storage scheme |
OPENIDM-16833 |
Implement conditionally assigned relationships dependent on RDVPs |
OPENIDM-17002 |
Can’t tune hash settings from openidm.hash script invocations |
OPENIDM-17007 |
Security questions with multiple answers can only be created in Latin charset |
OPENIDM-17051 |
Implement a mechanism to derive grantor RDVP dependencies |
23 Feb 2022
Key features
- Custom endpoints UI
-
A single UI now lets you create custom endpoints, edit their scripts within a syntax highlighting editor, and then run and test them directly. You can consume custom endpoints within Advanced Identity Cloud, or integrate them into your external UIs or system applications.
10 Feb 2022
Resolved issues
Hotfix release:
| Issue ID | Summary |
|---|---|
IAM-1818 |
End User UI for delegated admin cannot be fully translated |
IAM-1873 |
Add support to Login UI for WebView browser |
Hotfix release:
| Issue ID | Summary |
|---|---|
OPENAM-18952 |
Security questions are not always falling back to the default locale |
OPENIDM-17367 |
Target phase is running for reconciliation to a specific ID when using clustered reconciliation |
08 Feb 2022
-
Added dashboard counts to let you quickly view the number of users, applications, and organizations in each realm.
-
Added UI improvements to date and time input fields.
-
Added language localization for headers and footers in hosted pages.
| Issue ID | Summary |
|---|---|
IAM-1513 |
Allow customers to localize header and footer in Hosted Pages |
IAM-1596 |
Implement simple dashboard counts |
IAM-1597 |
Add tenant region information to tenant settings page |
IAM-1716 |
Tenant administrator account details not loaded correctly after refresh |
IAM-1725 |
Add date-time chooser to date-time fields |
IAM-1726 |
Add time chooser to time fields |
IAM-1808 |
Preview URL should be scrollable inside preview input |
IAM-1844 |
PollingWaitCallback not always returning a callback |
IAM-1848 |
Journeys with large themes cause a refresh loop |
07 Feb 2022
Hotfix release:
| Issue ID | Summary |
|---|---|
OPENAM-18341 |
Importing entity IDs from an external SP can cause invalid request URIs |
OPENAM-18661 |
Two or more OAuth2 clients with duplicate origins causes CORS filter to be aborted |
OPENAM-18764 |
API incompatibility in systemEnv.getProperty |
OPENAM-18887 |
Security questions password reset causes login failure |
OPENAM-18915 |
Unable to add scopes in the modification script when using OAuth2 with Grant Set storage scheme |
04 Feb 2022
Hotfix release:
| Issue ID | Summary |
|---|---|
FRAAS-9295 |
Prevent initial loading of identities in UI when a minimum search string length is configured |
03 Feb 2022
Hotfix release:
| Issue ID | Summary |
|---|---|
FRAAS-9045 |
Add account lockout for tenant administrators |
25 Jan 2022
-
Updated the staging environment information on the tenant status page. Individual service statuses are now combined into a single status.
21 Jan 2022
| Issue ID | Summary |
|---|---|
IAM-1687 |
Use the first populated locale when duplicating Terms and Conditions |
IAM-1723 |
Add datepicker to date fields |
IAM-1724 |
Add duration chooser to duration fields |
IAM-1747 |
Optional node attributes default to empty strings in request JSON when saving journey |
IAM-1757 |
Adding security question translation causes KbaCreateNode to loop |
IAM-1762 |
Show all available page numbers in pagination for application and script list views |
IAM-1764 |
Default starter theme UI in security question picker is too dark |
IAM-1769 |
Policy list has console scrollIntoView error |
IAM-1774 |
Add translated values to alt text entries and aria-label entries |
IAM-1788 |
Incorrect URL is copied for journeys after search filtering |
IAM-1792 |
Goto param in start over link is not URL encoded |
IAM-1813 |
Journey list page flashes empty state instead of loading state |
IAM-1825 |
Show user avatar and name for user identities |
19 Jan 2022
-
Added new built-in connector for Microsoft Graph.
| Issue ID | Summary |
|---|---|
AME-22153 |
Default client-side authentication script is incorrect |
OPENAM-18241 |
Permit OAuth2 Modification Script to return scopes as space-delimited string |
2021
22 Dec 2021
| Issue ID | Summary |
|---|---|
IAM-1757 |
Adding security question translation causes KbaCreateNode to loop |
IAM-1792 |
Goto param in start over link is not URL encoded |
17 Dec 2021
-
Added ability to manage security questions to UI.
| Issue ID | Summary |
|---|---|
FRAAS-4765 |
Tenant administrators should not have the option in the UI to delete or disable themselves |
FRAAS-8290 |
Tenant administrator list needs to show if MFA is activated |
FRAAS-8437 |
Admin UI encoding IDM system property specifiers in email templates |
FRAAS-8584 |
Cannot apply dark theme on security question picker |
FRAAS-8754 |
Display preview URL in the journey editor |
IAM-1592 |
User is redirected to error page after trying to invite already invited admin |
IAM-1621 |
Add security questions configuration to Admin UI |
IAM-1685 |
WCAG 2.2 UI Compliance |
IAM-1690 |
Remove ghost in Not Found page |
IAM-1697 |
Theme transition flickering between journeys |
IAM-1699 |
End user profile picture is not shown in top navigation bar |
IAM-1716 |
Tenant administrator account details not loaded correctly after refresh |
IAM-1739 |
Allow subsequent login attempts to enable next button |
IAM-1740 |
Default provider setup should keep 'Use my own provider' toggled off |
IAM-1753 |
Allow login theme to be set properly for URLs with both query parameters and route parameters |
IAM-1765 |
Paging error on tenant administrator list |
OPENAM-18511 |
Missing navigation options when an expired link from "Email Suspend" node is used |
15 Dec 2021
| Issue ID | Summary |
|---|---|
AME-21617 |
Create Scripted implementation for SAML 2.0 IDP Attribute Mapper |
AME-21303 |
Create Scripted implementation of ScopeValidator#additionalDataToReturnFromEndpoint methods |
AME-21265 |
Scope Implementation Class per Client not just per Provider |
AME-21262 |
OAuth2 Scripts per Client not just per Provider |
OPENAM-18167 |
OIDC requests with request parameter fail with 500 error when there is no session using POST |
OPENAM-18154 |
Wrong AMR returned with prompt=login and force authn setting enabled |
OPENAM-18121 |
Slow loading in Authentication Tree |
OPENAM-18120 |
Audit logging service does not correctly reflect the "prompt" URL parameter |
OPENAM-18119 |
Audit log no longer shows the userID of session being invalidated by amadmin |
OPENAM-18043 |
Device Match module not setting correct AuthLevel |
OPENAM-17979 |
Backchannel authentication - auth_req_id can be used to obtain multiple access tokens |
OPENAM-17968 |
Scripting engine breaks when you create script with empty name |
OPENAM-17923 |
Retry Limit Decision Should Not Have User Involvement when Save Retry Limit to User is Disabled |
OPENAM-17783 |
Language tag limited to 5 characters instead of 8 |
OPENAM-17826 |
Introspect endpoint returns a static value for "expires_in" when using client based tokens |
OPENAM-17610 |
OTP Email Sender node does not allow to specify connect timeout and IO/read timeout for underlying transport. |
OPENAM-17458 |
Enable access to hasResumedFromSuspend within a script |
OPENAM-16560 |
OAuth2 scope validation using policy engine should be configurable per OAuth2 client |
OPENAM-16149 |
Allow JWT bearer client authn unreasonable lifetime limit to be configurable |
OPENAM-15877 |
Support for Google reCAPTCHA v3 |
OPENAM-15340 |
OAuth2 RT - Ability to obtain original custom claim when regenerate the token |
OPENIDM-16677 |
Cannot retrieve entries from /recon endpoint when using DS as a repo if reconprogressstate size exceeds index limits |
10 Dec 2021
-
Added ability to manage environment secrets and variables (ESVs) to API and UI.
22 Nov 2021
| Issue ID | Summary |
|---|---|
FRAAS-4276 |
Social Provider Handler node should default to "Normalized Profile to Managed User" transformation script |
FRAAS-6275 |
During registration the "Next" button should be greyed out until all mandatory fields are completed |
FRAAS-7827 |
Hyperlinks cannot link to header elements in T&Cs |
FRAAS-8288 |
Add ability to search for a journey by name |
FRAAS-8317 |
Hard browser cache reset required when switching default theme in realm |
FRAAS-8367 |
Platform UI doesn’t allow "from name" to be configured in email templates |
FRAAS-8613 |
Social IDP CSS is overridden by themes |
FRAAS-8683 |
Stage field not showing on page nodes when value set to "themeId=name" prior to the new theme selector UI enhancement |
IAM-1548 |
Enduser UI not hiding side menu and nav bar |
IAM-1644 |
Create multiple locales at same time when adding a new T&C |
IAM-1650 |
Update Gateway and Agents page when in no data state |
IAM-1652 |
Use journey name to set page title in Login UI |
IAM-1689 |
Text from push authentication node cannot be overriden via config translation override |
IAM-1695 |
Clicking column header with no sorting enabled throws error |
IAM-1713 |
Hosted Pages tenant settings view has incorrect description |
OPENAM-18511 |
Missing navigation options when an expired link from "Email Suspend" node is used |
11 Nov 2021
| Issue ID | Summary |
|---|---|
AME-21261 |
Allow configuring "Issue Refresh Token" at OAuth client level |
AME-21263 |
Overridable Id_Token claims per client not just per provider |
IAM-1074 |
Provide Javascript defaults for AM scripts in Identity Cloud |
OPENAM-12995 |
Allow configuration of 'Custom Login URL Template' at client level |
OPENAM-14159 |
OAuth2 token storage to be configured per client |
OPENAM-15381 |
Allow configuring "Issue Refresh Tokens on Refreshing Access Tokens" per client |
OPENAM-16418 |
Client auth using private_key_jwt fails with 500 if claim format is wrong |
OPENAM-17185 |
Need ability to configure Remote Consent Service at the client level |
OPENAM-17262 |
Subname claim inconsistences |
OPENAM-17548 |
Can’t go back to login page after invoking Social Authentication Nodes |
OPENAM-17663 |
Improve the error response code for "Failed to revoke access token" |
OPENAM-17669 |
Ability to encrypt or sign access tokens based on client IDs |
OPENAM-17773 |
The acr_values parameter is mandatory on CIBA bc-authorize endpoint |
OPENAM-17782 |
Policy evaluation fails with 400 error when user does not exist |
OPENAM-17784 |
Session timeouts (maximum session time, maximum idle timeout) set incorrectly if username is dynamically created in a tree. |
OPENAM-17801 |
OIDC userinfo subname claim returns incorrect value |
OPENAM-17813 |
Allow /userinfo endpoint to include 'aud' claim in response |
OPENAM-17814 |
Auth Tree step-up fails if username case does not match |
OPENAM-17863 |
Authorization code is not issued when nonce is not supplied when using OpenID Hybrid profile |
OPENAM-17912 |
Account lockout count is not reset correctly |
04 Nov 2021
| Issue ID | Summary |
|---|---|
FRAAS-8502 |
Unable to set default theme to a theme not on the first page of themes in Hosted Pages |
IAM-673 |
Identity tabs in Platform UI not correctly positioned on small screens |
IAM-1495 |
Platform admin theme editor has confusing modal behaviour |
IAM-1499 |
Add theming to Platform UI to control color of login card: background, input, text... |
IAM-1501 |
Add ability to configure theme on a page node in journey editor |
IAM-1517 |
Terms and Conditions published version should just display rendered text |
IAM-1529 |
Links from non authorized page do not redirect user |
21 Oct 2021
| Issue ID | Summary |
|---|---|
FRAAS-7669 |
Page unresponsive message shown in End User UI when an organisation admin selects the password reset button for an organisation user |
FRAAS-7960 |
Terms and Conditions UI does not list the locales already created |
FRAAS-8048 |
Applications created without status don’t show default active status |
FRAAS-8050 |
Allow Platform Admin UI to display all application types |
FRAAS-8089 |
Theme layout overlays login box in theme designer |
FRAAS-8138 |
Discovery URI missing from OAuth client |
IAM-1117 |
Display data from linked systems when editing a user in Platform Admin UI |
IAM-1204 |
Journey editor lines too light |
IAM-1495 |
Platform admin theme editor has confusing modal behaviour |
IAM-1498 |
Add font family drop-down to theme editor |
IAM-1525 |
Application URL text is curtailed |
12 Oct 2021
-
Added ability to manage Java and Web Agents to UI.
| Issue ID | Summary |
|---|---|
IAM-1435 |
Add ability to create Java/Web Agents in Platform Admin UI |
IAM-1613 |
Allow configuration and display of password policy where at least 1–4 of 4 character sets are required |
06 Oct 2021
-
Added ability to validate passwords with a remote service using pass-through authentication.
| Issue ID | Summary |
|---|---|
AME-21058 |
Roll the config option for signing Request Object and Private Key JWT into one |
AME-21411 |
Create an IDM passthrough authentication node |
OPENAM-17405 |
Token introspection response not spec compliant |
OPENAM-17515 |
Sub attribute in access token can be in wrong casing |
OPENAM-17591 |
Session quota destroy next expiring action can fail when two new sessions attempt to read and update the same expiring session |
OPENAM-17595 |
Calling endSession endpoint should fail gracefully instead of Unknown JWT error |
OPENAM-17666 |
Update Scripted Decision Node bindings to deprecate "sharedState" and "transientState" and add new "state" |
OPENAM-17683 |
Selfservice user registration auto login fails for a sub-realm |
OPENAM-17828 |
Apostrophe in username breaks Push/OATH device registration |
OPENAM-18233 |
Social Provider Configuration for Google (Native iOS) does not work without a client secret |
OPENDJ-8178 |
Change of data format in date fields: trailing zeros on milliseconds are now truncated |
OPENIDM-15951 |
Support additional mime types for CSV bulk import |
OPENIDM-16081 |
Prevent users saving managed objects with invalid names |
OPENIDM-16089 |
Enhance error message for failed config property substitution in email templates |
OPENIDM-16473 |
Task scanner job fails on null top level objects |
29 Sep 2021
| Issue ID | Summary |
|---|---|
FRAAS-8110 |
Spinning wheel displayed when using an expired link from email suspend node |
FRAAS-8133 |
Login UI flashes with ForgeRock logo before loading the End User UI |
IAM-1398 |
Accessing platform UI with old token redirects user |
22 Sep 2021
| Issue ID | Summary |
|---|---|
FRAAS-5860 |
Table markup issue in email templates |
IAM-1409 |
Password Policy on Self-Service Registration page does not reset when blanking entered text |
IAM-1544 |
Platform UI allows creating scripts without any name |
IAM-1558 |
Assignment console errors caused by deleted managed object mapping |
IAM-1576 |
Cannot delete email template from preview page |
IAM-1577 |
Styles not being shown on edit email template page |
15 Sep 2021
| Issue ID | Summary |
|---|---|
IAM-1150 |
Remove data table component in favor of adding cell specific components |
IAM-1547 |
End-User Password Update changes session cookie and breaks logout |
IAM-1559 |
Admin and Enduser UIs not loading in IE11 |
IAM-1562 |
Sanitize postLogoutUrlClaim on redirection after Logout |
IAM-1563 |
403 when attempting to read password policy for delgated admin reset password |
10 Sep 2021
| Issue ID | Summary |
|---|---|
FRAAS-7890 |
Validation of custom domains allows upper case domain names |
FRAAS-8064 |
OATH Device not shown in End-User Profile Dashboard |
IAM-1475 |
Issue with enduser platform-ui when compiled from source |
IAM-1542 |
End users are unable to update their KBA info |
IAM-1545 |
KBA Create node does not send custom question as part of payload |
08 Sep 2021
-
Added Apple as a social identity provider for native applications.
| Issue ID | Summary |
|---|---|
AME-20499 |
Using Social Identity Provider Selector node and having disabled social IDPs causes massive amounts of exceptions and errors in the logs |
AME-20895 |
Request Object Encryption |
AME-21056 |
Make request object 'aud' configurable |
AME-21133 |
Apple Sign In Form POST Endpoint Compatibility with Custom Login Apps |
OPENAM-16314 |
Create OAuth2/OIDC Node to allow same authentication methods used and supported by our own OpenID Connect provider and clients |
OPENAM-17286 |
Add additional configuration options required for private key jwt feature |
OPENAM-17494 |
Other ways to allow OTP SMS Sender and OTP Email Sender nodes to send custom message |
OPENAM-17527 |
Support KMS/AM-encryption of PEM-format secrets |
OPENAM-17581 |
Scripted decision node on /authentication/authenticationtrees/trees PUT breaks tree save |
OPENAM-17625 |
No trees shown in inner tree selection box when another tree is misconfigured |
OPENAM-17672 |
Page Node does not expose inner nodes inputs or outputs |
OPENAM-17673 |
Nodes within a Page node do not have access to secure state |
OPENIDM-16113 |
rsFilter is case sensitive, which triggers authentication errors |
OPENIDM-16191 |
New live sync schedule created from UI is missing invokeContext.source |
OPENIDM-16275 |
UI does not display Progressive Profile Query Filter Condition properly |
OPENIDM-16322 |
Unable to create new LDAP connector through admin UI |
OPENIDM-16335 |
NPE on org model children endpoint when making a request that contains an error |
OPENIDM-16343 |
Unable to save powershell connector config through admin UI |
OPENIDM-16388 |
LDAP Connector created through Admin UI not setting credentials and baseContexts |
02 Sep 2021
| Issue ID | Summary |
|---|---|
FRAAS-7996 |
Cannot remove org members when logged in as org admin |
IAM-1421 |
Application Token lifetime input textbox not visible in some ID Cloud environments |
IAM-1424 |
Platform UI application list page shows errors when viewed from a sub-sub-realm |
IAM-1441 |
Custom Domain previous button is misplaced |
IAM-1442 |
Too much space between realm avatar on realm title |
IAM-1496 |
Platform admin theme editor missing default values for logo url/alt text |
IAM-1514 |
In a list view, clicking directly on checkbox does not select row |
IAM-1533 |
UI labels missing from ID Cloud registration UI |
IAM-1537 |
Platform UI: Not able to update user when email is an optional attribute |
IAM-1538 |
After changing password on a user in the admin ui any subsequent changes to the object results in an error on save |
23 Aug 2021
| Issue ID | Summary |
|---|---|
IAM-1473 |
Unable to access links to native consoles if platform dashboard page not large enough |
IAM-1492 |
Using 'reset to defaults' on theme admin wipes out theme name |
IAM-1508 |
Edit managed user page has bad formatting when ListField inputs contain long entries |
IAM-1509 |
Social login failure does not return to initial journey step |
IAM-1515 |
Ensure login theme background covers entire height |
17 Aug 2021
| Issue ID | Summary |
|---|---|
FRAAS-7936 |
Email templates missing from console |
IAM-1476 |
Change Consent menu item and related text to Terms & Conditions |
16 Aug 2021
-
Updated End User UI to support WCAG accessibility best practices.
-
Updated End User UI and Login UI to support localization.
-
Updated End User UI theming and customization for user journeys:
-
Added ability to apply a different theme and logo to each user journey.
-
Added ability to provide a different user journey to each brand.
-
Added ability to add custom footers to end-user login and account management pages.
-
Added ability to configure the layout of the end-user account management page by adding and removing sections.
-
-
Updated End User UI terms and conditions management:
-
Added versioning and localization.
-
Added ability to track end-user version history.
-
| Issue ID | Summary |
|---|---|
IAM-1259 |
EndUser-UI WCAG updates |
IAM-1264 |
End user stored state returns different user to previous users page |
IAM-1289 |
Platform-ui not rendering in IE11 because Postcss v8+ only serves ES6+ sources |
IAM-1291 |
End user delegated admin should not display raw JSON option |
30 Jul 2021
| Issue ID | Summary |
|---|---|
FRAAS-7721 |
Unable to save a new LDAP connector configuration in the Platform UI |
15 Jul 2021
| Issue ID | Summary |
|---|---|
AME-20475 |
OpenID Connect Back-Channel Logout |
AME-20499 |
Using Social Identity Provider Selector node and having disabled social IDPs causes massive amounts of exceptions and errors in the logs |
AME-20600 |
Grant Types UI field the OAuth2 Provider shows as supportedGrantTypes |
AME-20994 |
Rename StoreOps tokens to OIDC Session Management |
IAM-1096 |
Scripted decision node description has a typo |
OPENAM-14402 |
Access/ID tokens only include short username for "sub" claim |
OPENAM-15214 |
Auth Tree - Clicking save with no changes causes render problem with node attributes inside page node |
OPENAM-16314 |
Create OAuth2/OIDC Node to allow same authentication methods used and supported by our own OpenID Connect provider and clients |
OPENAM-16653 |
Identity using fr-idm-uuid has wrong account ID in FR Authenticator |
OPENAM-16959 |
Failed to authenticate with Twitter as Social Login Provider |
OPENAM-17297 |
HOTP Generator Node adds cleartext OTP to sharedState |
OPENAM-17436 |
JS version of the OIDC Claims script does not work due to a casting error. |
OPENAM-17489 |
Add new form_post endpoint |
OPENAM-17494 |
Other ways to allow OTP SMS Sender and OTP Email Sender nodes to send custom message |
OPENAM-17517 |
JS versions of Social Identity Provider Profile Transformation scripts do not work due to a casting error. |
OPENAM-17595 |
endSession should fail gracefully instead of Unknown JWT error |
OPENAM-17625 |
No trees shown in inner tree selection box when another tree is misconfigured |
OPENAM-17659 |
Select Identity Provider Node does not load social IDPs that do not define a client secret |
OPENAM-17672 |
Page Node does not expose inner nodes inputs or outputs |
OPENAM-17828 |
Apostrophe in username breaks Push/OATH device registration |
OPENIDM-14525 |
Customer would like to define a default value for a property on a managed object. |
OPENIDM-15220 |
Temporal constraints on internal role grants with privileges are not reflected in the end-user UI |
OPENIDM-16192 |
Under certain conditions it is possible to generate two users with the same userName |
OPENIDM-16206 |
TaskScanner tries to read object after deletion |
OPENIDM-16266 |
ICF service retry during livesync network failures |
OPENIDM-16326 |
SchemaService does not allow filtering on _id |
OPENIDM-16334 |
Managed object schema editor fails on properties with "pattern : null" |
23 Jun 2021
| Issue ID | Summary |
|---|---|
FRAAS-4877 |
Attempting to Import a CSV file that contains a number in an frUnindexedInteger field fails |
15 Jun 2021
| Issue ID | Summary |
|---|---|
FRAAS-7322 |
Common passwords policy errors now show in bulleted list below password field |
IAM-1264 |
Logging out and logging back in now returns user to dashboard instead of last route visited |
IAM-1319 |
Allow disabling of sorting and searching on relationship array grids |
IAM-1321 |
Allow UI to use |
10 Jun 2021
| Issue ID | Summary |
|---|---|
FRAAS-6504 |
Terms and Conditions do not render correctly when using HTML formatting directives |
IAM-1081 |
Using the back button in some UI contexts causes an session termination |
OPENAM-17297 |
HOTP Generator Node adds cleartext OTP to sharedState |
OPENAM-17343 |
Access token call returns 500 error if password needs to be changed or has expired |
OPENAM-17349 |
OIDC Refresh token - Ops token is deleted from the CTS during refresh EDISON |
OPENAM-17352 |
OAuth Introspection Endpoint can be accessed by public clients providing an empty client secret |
OPENAM-17359 |
Unfriendly error message displayed when an expired link from "email suspend" node is used |
OPENAM-17396 |
Terms of Service URI Link does not Display in Consent Page |
OPENAM-17426 |
No validation for attribute collector node |
OPENAM-17436 |
JS version of the OIDC Claims script does not work due to a casting error. |
OPENAM-17494 |
Other ways to allow OTP SMS Sender and OTP Email Sender nodes to send custom message |
OPENAM-17517 |
JS versions of Social Identity Provider Profile Transformation scripts do not work due to a casting error |
OPENAM-17595 |
endSession should fail gracefully instead of Unknown JWT error |
OPENAM-17625 |
No trees shown in inner tree selection box when another tree is misconfigured |
OPENAM-17672 |
Page Node does not expose inner nodes inputs or outputs |
OPENAM-17673 |
Nodes within a Page node do not have access to secure state |
OPENAM-17828 |
Apostrophe in username breaks Push/OATH device registration |
OPENIDM-15953 |
Connector Config Disappears from UI in IDCloud for RCS Connectors |
OPENIDM-15903 |
Grant Type not shown in the Grant Column for Assigned Roles |
OPENIDM-16134 |
/system?_action=createFullConfig unexpectedly replaces variables |
OPENIDM-16150 |
Identity Connect UI - Manage Admin Groups modal does not have cancel button after adding new Group Base Contexts |
OPENIDM-16180 |
Removed Properties cannot be Re-Added Until Page Refresh in User Registration |
04 Jun 2021
| Issue ID | Summary |
|---|---|
IAM-1219 |
JS error when assigning multiple relationships |
IAM-1261 |
Adding relationship via UI fails when large user populations |
IAM-1263 |
Need some default data in managed object lists when search filter on UI |
IAM-1290 |
Managed identities configuration cosmetic improvements |
20 May 2021
-
Added ability to add multiple domains per realm.
-
Added Access Management scripting user interface.
-
Added Cross-Origin Resource Sharing (CORS) setup UI.
-
Added optimized search option.
-
Advanced Identity Cloud admin console now displays Alpha and Bravo entities separately.
| Issue ID | Summary |
|---|---|
FRAAS-6854 |
When the commonly-used passwords option is selected for password policy...option unusable |
FRAAS-6012 |
Remove Restriction in UI of Only Allowing One Domain |
FRAAS-5525 |
Add CORs Settings to New Platform UI |
FRAAS-4017 |
On all journey drag-and-drop UIs, links to SDK/API Docs are broken |
IAM-1242 |
SDK config for CORS settings doesn’t properly set allowCredentials |
IAM-1240 |
Fix styling of multiselect drop-down and tags |
IAM-1228 |
Platform ui scripting issues seen in ID cloud testing |
IAM-1227 |
remove dependency that requires 'parent required' for UI to handle orgs properly |
IAM-1213 |
Input Label and Placeholder doubling up on all input fields |
IAM-1212 |
Unable to use Webauth TouchID or FaceID on Safari MacOS/iOS |
IAM-1205 |
Update copyright bot copyright message GoodFirstIssue |
IAM-1195 |
Adding a temporal constraint to a role member relationship does not work |
IAM-1181 |
IDM policies not displayed in policy panel for password |
IAM-1177 |
Update grids to handle large datasets based on managed object schema flag |
IAM-1160 |
Server list doesn’t update on new server cluster modal |
IAM-1155 |
Improve code coverage display in PR testing |
IAM-1151 |
Multiselect Does Not Remove Entry If Removed When Entering New Value GoodFirstIssue |
IAM-1148 |
Remove JEST snapshot testing |
IAM-1105 |
Disable save button on new connector server modal after first click GoodFirstIssue |
IAM-1076 |
When in cloud env hide bravo_user, bravo_role, and bravo_assignment when realm is alpha and vice versa |
IAM-1065 |
E2E Tests - Admin - Import Identities |
IAM-1039 |
Platform Scripting Usability (UI Only) |
IAM-1024 |
Adjust app detail header top margin |
IAM-375 |
Refreshing Page on Alias Doesn’t Highlight Side Menu Item |
28 Apr 2021
-
Added ability to activate or deactivate hosted pages.
| Issue ID | Summary |
|---|---|
FRAAS-6503 |
Turn Off The End User Hosted hosted profile page |
IAM-1001 |
Remove extra padding on login error |
IAM-1144 |
Email Templates - Create Email Provider View |
IAM-996 |
Remove extra spacing on Agent profile status button |
12 Apr 2021
-
Added multi-factor authentication (MFA) option to tenant administrator profiles.
-
Added ability to configure your own email service provider.
| Issue ID | Summary |
|---|---|
FRAAS-6573 |
SAML 2.0 login flow ends with error: “No mapping organization found for organization identifier” |
FRAAS-6465 |
Social login seems to break expected goto URL behavior when protecting apps with IG |
IAM-1165 |
Sidebar-shim Does not Dynamically Change on Resolution Change |
IAM-1120 |
End user account controls throwing invalid argument error on profile page load |
IAM-1080 |
Convert switches to checkboxes in journey editor |
OPENAM-17625 |
No trees shown in inner tree selection box when another tree is misconfigured |
OPENAM-17517 |
JS versions of Social Identity Provider Profile Transformation scripts do not work due to a casting error |
OPENAM-17494 |
Other ways to allow OTP SMS Sender and OTP Email Sender nodes to send custom message |
OPENAM-17436 |
JS version of the OIDC Claims script does not work due to a casting error |
01 Apr 2021
| Issue ID | Summary |
|---|---|
FRAAS-6504 |
Updated terms callback to sanitize html from backend |
FRAAS-6431 |
End User UI calls ../authenticate endpoint switch at login |
FRAAS-6399 |
ID Cloud UI Multiselect spinner |
FRAAS-6255 |
Tenant Admin List does not always Show Entire List of Admins |
FRAAS-5968 |
End User Profile Page Displays "ForgeRock" Specific Information |
FRAAS-5585 |
Custom Domain - UI Re-Verify Flow |
IAM-1179 |
Fix issue with managed identities table not displaying properly |
IAM-1171 |
Drag selection in the journey editor can cause console errors cause saving to hang |
IAM-1165 |
Sidebar-shim Does not Dynamically Change on Resolution Change |
IAM-1142 |
Duplicate Journey modal breaks if initially dismissed |
IAM-1141 |
Update password policy messages to a more user friendly format in the Platform-UI. |
IAM-1128 |
Resource view cutting off drop-down menu |
IAM-1126 |
Login-UI doesn’t change locale language to browser default |
IAM-1109 |
Realm theme logo preview doesn’t update |
IAM-1104 |
Not possible to change or remove the default locale of email templates. |
IAM-1083 |
Email template "From" input field limited to email addresses while label suggests otherwise |
IAM-1080 |
Swap toggle w/ checkbox in journey editor |
IAM-1040 |
Journey list page displays javascript errors when expanding a journey |
OPENIDM-15019 |
End-user UI displays user name without accents (umlaut etc) |
11 Mar 2021
-
Added Salted SHA-256 support.
| Issue ID | Summary |
|---|---|
FRAAS-6209 |
Theme Editor popover() does not display using Firefox on MacOS |
FRAAS-6199 |
Ugly Error Messaging in UI when Password Policy Fails |
FRAAS-6099 |
AM Authorization with Advices broken |
FRAAS-6013 |
When you enter a domain in the Domain Modal, and it Fails Validation, you cannot add a Domain that is Valid |
FRAAS-5968 |
End User Profile Page Displays “ForgeRock” Specific Information |
FRAAS-5938 |
Platform UI generates forbidden Journey title and cannot be deleted |
FRAAS-5843 |
Current password policy limits passwords to a maximum of 64 characters |
FRAAS-5756 |
Authentication Trees Don’t Respect reentry Cookie |
FRAAS-5340 |
Hashed passwords synchronization fails |
IAM-794 |
Platform login UI has hard-coded “/am” path assumed for default path behavior |
IAM-1124 |
Can’t save Agent type RCS on edit page |
IAM-1103 |
Password policy shows ‘must be less than 0 characters long’ when max length is 0 |
IAM-1097 |
Incorrect instruction link for RCS in IDCloud docs |
IAM-1088 |
Add show columns, sort, and search capability to relationship array grid |
IAM-1087 |
Admin create resource modal should handle required relationship array properties |
IAM-1081 |
Using the back button in some UI contexts causes an session termination |
IAM-1021 |
Ability to copy and paste values from multiselect component |
IAM-1017 |
Force Use SSL option for Connector Servers in Cloud |
OPENAM-16949 |
Cannot create a policy for subject type group |
17 Feb 2021
-
New UI lets you configure a custom domain name.
-
New Admin profile UI lets admins edit their own tenant administrator profiles.
-
Added ability to end a user session for testing and troubleshooting purposes.
| Issue ID | Summary |
|---|---|
IAM-1066 |
Links for delegated admin objects not showing in end-user UI when a user has correct privileges |
IAM-1064 |
Incomplete provisioner file makes it impossible to create clusters |
IAM-887 |
Admin UI does not display in the Firefox web browser when Private Browsing is enabled. (Will not fix) |
04 Feb 2021
-
New, shorter URL for Identity Cloud Docs: https://backstage.forgerock.com/docs/idcloud/latest/overview.html.
| Issue ID | Summary |
|---|---|
OPENAM-17289 |
Generated |
OPENIDM-15892 |
Persisted schedules not being displayed in IDM Native UI |
29 Jan 2021
-
Added email notification templates.
13 Jan 2021
| Issue ID | Summary |
|---|---|
AME-20719 |
RelayState Not Being Used on Identity Cloud with SAML tree node |
AME-13690 |
Create an OATH authentication node |
FRAAS-5257 |
Cannot disconnect social identity provider |
IAM-1003 |
IE11 does not search for user on End User page |
IAM-989 |
Update connection status for servers on server cluster pages |
IAM-988 |
Platform UI error for end users when resizing in IE 11 |
IAM-978 |
ConnectorServers generates browser console errors when connector servers are present |
IAM-958 |
Backend scripts updating hiddenValueCallback values don’t propagate to step requests |
IAM-952 |
ID cloud new server cluster modal allows going back to select adding servers when it should not |
IAM-947 |
Platform UI: support 'default' values in Managed Object create/edit screens |
IAM-907 |
Adding IG Agent with non-unique name breaks UI |
OPENAM-16965 |
Alignment of shared state with self-service object nodes |
OPENAM-16961 |
OIDC Claims Script - /userinfo to access clientProperties |
OPENAM-16919 |
SAML JSP Flows not working |
OPENIDM-15686 |
Cannot delete a mapping in an Identity Cloud tenant |
OPENIDM-15576 |
Unable to save the 'Reconciliation Query Filters' under Mappings in the Admin UI. |
OPENIDM-15511 |
IDM Admin console - Paging controls in managed objects are disabled |
OPENIDM-15507 |
Paging controls in connector data tab are disabled and should not be |
OPENIDM-15368 |
Value of ldapGroups isn’t visible in the admin UI as an assignement attribute |
OPENIDM-15150 |
IE11 script error in End-User UI |
OPENIDM-14750 |
Managed Object schema editor scripts tab not saving scripts on relationship type properties |
OPENIDM-14411 |
Unable to create a user with a previously used password |
2020
08 Nov 2020
-
Added ability to use organization name as part of the tenant name.
-
Added ability to set a default end-user journey.
| Issue ID | Summary |
|---|---|
AME-20500 |
Users cannot authenticate using local authentication and the Social IDP Selector node |
FRAAS-4856 |
Cannot create API keys using Safari 14.0 |
FRAAS-4767 |
Identity Cloud UI does not display user properties according to managed object settings |
FRAAS-4699 |
Connector server (RCS) connection status inaccurate |
FRAAS-4481 |
Enduser UI - Password required in Edit Personal Info |
FRAAS-4070 |
Update tenant naming convention |
IAM-906 |
Cannot create an assignment when the mapping target is a system object |
IAM-885 |
ID cloud journeys list has visual errors for journeys created in AM native console |
IAM-882 |
Breadcrumb needs to update upon navigating away from page |
IAM-881 |
End-user profile doesn’t render multi-value fields |
IAM-862 |
Footer has wrong logo |
IAM-861 |
Change managed object toggle to show object value instead of entire schema |
IAM-795 |
Bulk Import: improve error messages in Advanced Identity Cloud admin console |
IAM-784 |
Add dynamic theme for end user |
IAM-759 |
Incorrect URL for legacy AM admin console |
IAM-697 |
Platform-admin Unit tests: Applications |
IAM-606 |
Allow Password entry in 'New Identity' Modal |
IAM-589 |
Accessibility: CardRadioInput is not navigable and doesn’t report as a radio input correctly |
13 Oct 2020
-
Added ability to customize an end-user UI theme.
-
Added administrators list page.
02 Oct 2020
-
Improved IDM debug logging.
-
Custom attributes can be used in scripts.
-
Added Gateways & Agents list and profile page.
-
Journey edit page indicates required fields.
-
Updated dark theme.
-
Added the ability to theme the login UI from config.
| Issue ID | Summary |
|---|---|
FRAAS-4610 |
Filename with a space gets converted to an null pointer |
FRAAS-4558 |
Admin invite doesn’t work |
FRAAS-4550 |
User profile attributes are inaccessible to token modification scripts |
FRAAS-4549 |
Base URL Source service should be part of quickstart config |
FRAAS-4522 |
Cannot save "Generic Indexed String" attributes in user profile |
FRAAS-4520 |
Cannot save "Address 1" field in user profile properties |
FRAAS-4477 |
Password-related failures at onboarding |
FRAAS-4459 |
Make createResource behave more consistently with repeat use. |
FRAAS-4440 |
Broken create assignment functionality |
FRAAS-4379 |
UI issues with OAuth 2.0 related interfaces (Consent page, OAuth 2.0 client error pages, and the device code grant page |
FRAAS-4319 |
Alpha/Bravo Realm Users cannot edit personal info in the Enduser UI |
FRAAS-4277 |
Hide incompatible tree nodes |
FRAAS-3928 |
Remove on-prem connectors from PaaS IDM instance |
IAM-789 |
Password policy rules should display in platform-admin password reset UI |
IAM-603 |
403/404 errors in platform-admin when user has insufficient privileges |
Rapid channel changelog
Subscribe to get automatic updates: Rapid channel changelog RSS feed
For release notes published before December 2024, refer to the Rapid channel changelog archive.
April 2025
28 Apr 2025
Versions 17434.0, 17436.0
No customer-facing features, enhancements, or fixes released.[5]
23 Apr 2025
Version 17384.0
Enhancements
-
IAM-987: Added support for enums (drop-down lists) to hosted account pages.
-
IAM-1116: Added support for enums (drop-down lists) to the Advanced Identity Cloud admin console.
-
IAM-2103: Added support for enums (drop-down lists) to hosted journey pages.
-
IAM-6822: Added the ability to manage cookie domains in the Advanced Identity Cloud admin console.
-
IAM-7412/IAM-8535: Enabled custom values for minimum length of excluded user attribute values in passwords. The default is still 5 characters, but can be reduced to 3 to catch shorter string matches.
-
IAM-7794[7]: Added support for using custom identity objects in the the form builder.
-
IAM-7919: Improved color contrast ratio of the Delete Account button text when focused.
-
IAM-7934: Improved color contrast ratio of date fields when focused.
-
IAM-7957: Improved color contrast ratio of the Deselect button text when focused.
-
IAM-7966: Improved color contrast ratio of In Progress text.
-
IAM-8016[7]: Allow form authors to specify a user filter when dynamic enums are selected.
-
IAM-8085: Updated the Add a Parameter reports modal to use entity attributes for input.
Fixes
-
FRAAS-15518: Fixed issue that prevented custom localization of Session timed out message in certain locales.
-
IAM-5834: Fixed a double-encoding issue in the SAML app that affected IdP-initiated sign on.
-
IAM-6796: Prevented jobs being scheduled with frequencies that caused invalid date errors.
-
IAM-7855: Fixed a typo in the help text returned when there are no results to display.
-
IAM-8237: Corrected floating labels in the date picker in the Platform UI Login application.
-
IAM-8361: Fixed the Save button in the Edit Bookmark application to be inactive while checking if the ESV exists.
-
IAM-8364: Fixed issues in SAML end-to-end scenarios.
-
IAM-8378: Fixed an issue that stripped HTML elements from email templates.
-
IAM-8403: Fixed border focus location and floating label issues in Tag fields.
-
IAM-8434: Fixed an issue that prevented duplication of new themes that contain special characters.
16 Apr 2025
Versions 17283.0, 17299.0
No customer-facing features, enhancements, or fixes released.[5]
08 Apr 2025
Versions 17178.0, 17186.0
Enhancements
-
OPENDJ-11175: The password validation mechanism has been enhanced to include checks for attribute values shorter than the
min-substring-length(the default is 5).For example, if the password contains
Bobfor a user named Bob, the password is rejected, even ifmin-substring-lengthis set to 5.
March 2025
28 Mar 2025
Versions 17072.0, 17079.0
Enhancements
-
ANALYTICS-846: You can now select the attribute type and value for report entity attributes.
-
ANALYTICS-983[4]: You can now use regular expression operators in Advanced Reporting.
21 Mar 2025
Key Features
- Custom attributes for user entity in Advanced Reports (ANALYTICS-863)[4][22]
-
When a tenant administrator modifies the
usersidentity object from the native console and adds a new custom attribute, the attribute is immediately available on the Create Report page. Administrators can use the custom attribute for their reports and filters.Learn more in Custom attributes in Advanced Reporting.
20 Mar 2025
Versions 17002.0, 17015.0
No customer-facing features, enhancements, or fixes released.[5]
19 Mar 2025
Versions 16981.0, 16989.0
No customer-facing features, enhancements, or fixes released.[5]
17 Mar 2025
Version 16940.0
Key Features
- Tenant auditors (IAM-8086)
-
Advanced Identity Cloud now lets you invite tenant auditors to access the Advanced Identity Cloud admin console. Tenant auditors can view settings, configuration, and data but cannot modify them.
Enhancements
-
IAM-6996: Added the ability to create a specific OAuth 2.0 client when creating a connector server, rather than relying on the default RCSClient.
-
IAM-7109: You can now use an ESV to set the From Address in the email provider configuration.
-
IAM-7827/ANALYTICS-835[4]: In the analytics report editor in Advanced Reporting, you can now reorder columns by dragging and dropping them.
-
IAM-7841/ANALYTICS-840[4]: The reports page in Advanced Reporting is now a list view with pagination and search.
-
IAM-8321: In the journey editor, the node titles now wrap within the left nodes panel.
13 Mar 2025
Version 16885.0, 16887.0
No customer-facing features, enhancements, or fixes released.[5]
February 2025
27 Feb 2025
Version 16747.0
Key Features
- Flow Control node (AME-30017)
-
You can now randomly direct users down different journey paths. Learn more in Flow Control node.
- OIDC application journeys (AME-28650)
-
You can now configure OAuth 2.0 / OIDC client applications to redirect authentication requests to a specified journey. Learn more in Redirect an OAuth 2.0 or OIDC client application to a journey.
Enhancements
-
AME-27705: Extend the
utilsbinding for all next-generation scripts to support low-level cryptographic operations. These operations include encryption, decryption, hashing, signing, verification, and key generation.Find more information in Perform low-level cryptographic operations in next-generation scripts.
-
AME-28780: Added an IDM policy condition that can assert conditions against an IDM resource type such as user identities.
-
AME-28954: Modified the import metadata endpoint to support updating signing and encryption certificates for existing SAML service providers (SPs) without requiring the deletion or recreation of SP configurations.
-
AME-29307: You can now use DER-encoded certificates for OAuth 2.0 client authentication.
-
AME-29810: The realm default authentication service can no longer be a journey with
mustRunenabled. Also,mustRuncan no longer be enabled on journeys that are set as the realm default authentication service. -
AME-29835: Configuration Provider Node scripts can now use the next-generation scripting engine, which gives them access to common bindings such as
openidmandhttpClient. -
AME-30076: New
getApplicationId()method provides a consistent way to retrieve the application ID from both SAML and OAuth 2.0 applications.
Fixes
-
AME-29504: The
scriptNameandloggerbindings in library scripts referenced the same default script name and ID. Their previous behavior has now been restored by inheriting values from the referencing script. -
AME-29965: The Configuration Provider node now works with the Inner Tree Evaluator for nested inner journeys.
-
AME-30377: The following two warning level log messages have been reduced to debug level because they’re rarely useful and appear frequently, drowning out more useful log entries:
-
No users have been identified. -
Ignoring the new universal id as that is empty and the current universal id is already set.
-
-
OPENAM-22120: Back-channel logout tokens now include the
expclaim. -
OPENAM-23077: The
access_tokenendpoint now responds with the correct error code when thecode_verifierisn’t supplied (for example,invalid_grant).
20 Feb 2025
Version 16676.0
Key features
- Advanced sync (IAM-8090)
-
Many of the mapping synchronization features available in the IDM admin console are now exposed in the Advanced Sync tab when viewing an application. You can create additional mappings between applications or between applications and identity profiles.
Enhancements
-
IAM-7967[7]: Added an image description for the approvals Low Priority icon.
-
IAM-7977: Improved the font color contrast ratio of the email address displayed in Advanced Identity Cloud admin console user profiles.
-
IAM-8053: The Advanced Identity Cloud end-user UI can now use
defaultTextvalue as a fallback value when the actual value of a field returns empty. -
OPENIDM-20139: Applications can now use
postActionscripts for theONBOARDaction.
Fixes
-
IAM-7719[7]: Users are now redirected back to the compliance Policy Rules tab after creating or editing a policy rule.
04 Feb 2025
Version 16508.0
Enhancements
-
IAM-4692: Managed identity boolean fields now use a checkbox instead of a toggle.
-
IAM-6581: SAML 2.0 application journeys can now be configured in the Advanced Identity Cloud admin console.
-
IAM-7248[7]: In IGA sources, the
displayNameandlogocan now be obtained from the CDN. -
IAM-7874[7]: The Governance > Requests > Settings tab now lets you activate or deactivate Governance LCM.
January 2025
31 Jan 2025
Versions 16460.0, 16466.0
No customer-facing features, enhancements, or fixes released.[5]
29 Jan 2025
Versions 16437.0, 16441.0
No customer-facing features, enhancements, or fixes released.[5]
24 Jan 2025
Versions 16410.0, 16412.0
Enhancements
-
FRAAS-23002: Improvements to OATH support for MFA authenticators
-
Update the default OATH shared secret length from 32 to 40 for existing and new tenants so that tenant administrators can use Google Authenticator with MFA when signing on using their Advanced Identity Cloud native accounts.
-
Make the OATH shared secret length configurable (using a support request) to support other MFA authenticators.
-
23 Jan 2025
Versions 16386.0, 16388.0
No customer-facing features, enhancements, or fixes released.[5]
22 Jan 2025
Versions 16368.0, 16376.0
No customer-facing features, enhancements, or fixes released.[5]
20 Jan 2025
Versions 16345.0, 16348.0
15 Jan 2025
Versions 16294.0, 16297.0
Enhancements
-
FRAAS-23375: You can now obtain the HTTP client location from the
X-Client-City&X-Client-City-Lat-LongHTTP headers in Advanced Identity Cloud scripts and journeys.X-Client-Citycontains the name of the city from which the request originated, for example,Mountain Viewfor Mountain View, California. There is no canonical list of valid values for this variable. The city names can contain US-ASCII letters, numbers, spaces, and the following characters:"!#$%&'*+-.^_`|~".X-Client-City-Lat-Longcontains the latitude and longitude of the city from which the request originated, for example,37.386051,-122.083851for a request from Mountain View.
14 Jan 2025
Versions 16276.0, 16278.0
No customer-facing features, enhancements, or fixes released.[5]
10 Jan 2025
Versions 16216.0, 16229.0
Enhancements
-
IAM-6833: Made existing synchronization tokens editable for incremental reconciliations.
-
IAM-7223[7]: Added the ability to set user, role, organization, application, or entitlement objects to provide predefined values for select and multiselect fields in request forms.
03 Jan 2025
Version 15989.0
Enhancements
-
ANALYTICS-459[23]: Report query data is now retained for 30 days for customers using OOTB reports and 90 days for customers with Advanced Reporting[11].
-
ANALYTICS-495[23]: Replace
emailwithusernamein User Last Login report. -
ANALYTICS-817[23][4]: Report authors can now query on "Password Last Changed Time" for user entity.
-
ANALYTICS-818[23][4]: Report authors can now query on "Password Expiration Time" for user entity.
Fixes
-
ANALYTICS-474[23]: The User Journey Stats report now provides aggregates by outcome in the report result when more than one outcome is selected.
-
ANALYTICS-837[23]: The User Count by Status report now provides aggregates by status in the report result when more than one outcome is selected
-
ANALYTICS-585[23][4]: Remove Report Admin and Report Owner group selection when creating a new report.
December 2024
17 Dec 2024
Version 16028.0
Enhancements
-
OPENDJ-9287: The password validation mechanism has been enhanced to include checks for portions of attribute values within passwords. This improvement ensures that even partial matches between portions of passwords and portions of attribute values are identified and restricted, thereby enhancing security.
For example, if the password is
abcdefand the attribute value isabcdef123, the password is rejected. Similarly, if the password isabcdefAZERTYand the attribute value isabcdef123, the password is rejected.
16 Dec 2024
Version 15989.0
This release reintroduces many features, enhancements, and fixes previously present in reverted versions.
Key features
- PingOne Authorize node (TNTP-183)
-
Use this node to send a decision request to a specified decision endpoint in your PingOne Authorize environment.
- PingOne node improvements (SDKS-3468)
-
- PingOne Create, Identify, and Delete Nodes
-
The following PingOne nodes are now available:
- PingOne Identity Match node
-
Use the PingOne Identity Match node to identify if a user exists both in the user repository and in PingOne, using defined attributes.
- PingOne Create User node
-
Create new users in the PingOne platform using the PingOne Create User node. Create users based on an existing user’s properties or choose to create the user anonymously. For example, when used in conjunction with PingOne Verify.
- PingOne Delete User node
-
Delete users from the PingOne platform with the PingOne Delete User node.
- PingOne Verify nodes
-
Use the following PingOne Verify nodes in conjunction with the PingOne Identity Match node, PingOne Create User node, and PingOne Delete User node to create a seamless verification process in your journey:
- PingOne Verify Evaluation node
-
Leverage PingOne Verify to initiate or continue a verification transaction with the PingOne Verify Evaluation Node.
- PingOne Verify Completion Decision node
-
Determine the completion status of the most recent identity verification transaction for an end user.
Use before the PingOne Verify Evaluation node to determine the status of the verification process or after the PingOne Verify Evaluation node using a script to evaluate the transaction.
For example, you can evaluate if the transaction was completed using a passport and route your journey accordingly.
Use these nodes in place of the PingOne Verify Marketplace nodes. - reCAPTCHA Enterprise node (SDKS-3322)
-
The reCAPTCHA Enterprise node node adds Google reCAPTCHA Enterprise support to your journeys.
- SAML application journeys (AME-27850)
-
Added support for SAML application journeys with a new setting on the remote SP. Configure a specific authentication journey that always runs for users authenticating with your SAML 2.0 app, regardless of existing sessions or configured authentication context.
Learn more in Configure a SAML 2.0 application journey.
- Set Failure Details node (AME-27871)
-
Use the Set Failure Details node to configure a localized error message on journey failure. You can also configure extra details in the response body of the failure request.
- Set Success Details node (OPENAM-12335)
-
Use the Set Success Details node to add additional details to the success response of a journey.
- UI support for managing certificates (IAM-5813)
-
You can now use the Advanced Identity Cloud admin console to generate CSRs and upload SSL certificates in your tenant environments.
Learn more in Manage SSL certificates using the admin console.
Enhancements
-
AME-26050: You can now create Next-generation Policy Condition scripts that have access to all common bindings, such as
openidmandhttpClient. Additionally, some existing bindings have been wrapped to improve usability in scripts. -
AME-28228: OAuth 2.0 audit logs now include the OAuth 2.0 client ID and any journey associated with the client.
-
AME-29009: When using the new FIDO Metadata Service, if you link to the FIDO metadata using a URL, Advanced Identity Cloud periodically downloads and updates the latest FIDO metadata based on the
nextUpdatedate specified in the downloaded data. -
AME-29093: Added configuration for integration with WebAuthn Metadata Services (such as the FIDO Metadata Service). This includes a realm-level WebAuthn Metadata service and a new FIDO Certification Level configuration attribute in the WebAuthn Registration Node.
-
FRAAS-22321: You can now obtain the HTTP client location from the
X-Client-RegionHTTP header within your scripts and journeys. TheX-Client-Regionheader contains the country (or region) associated with the client’s IP address in the form of a Unicode CLDR region code, such asUSorFR. For most countries, these codes correspond directly to ISO-3166-2 codes. -
FRAAS-23073: The SAML scripting adapter now lets scripts access
org.forgerock.http.protocol.*. -
IAM-3323: You can now use XPath transformation functions with additional Workday application template attributes.
-
IAM-4540: You can now change the border color of a selected input field in journey and end-user pages.
-
IAM-6397: The Advanced Identity Cloud admin console now lets you page through the list of OAuth 2.0 client profiles.
-
OPENAM-23109: During a WebAuthn registration flow, if Store data in transient state is enabled, the Authenticator Attestation Global Unique Identifier (AAGUID) is now added to the node state under the
webauthnDatakey.
Fixes
-
AME-28016: When an invalid redirect URI is provided to the
/parendpoint, the URI mismatch error is nowredirect_uri_mismatchinstead ofinvalid_request. -
AME-28017: Advanced Identity Cloud now accepts the requested OAuth 2.0 endpoint as a valid JWT audience claim, as per RFC 7519 and RFC 9126.
-
AME-29170: On LDAP Decision node login failure, stack traces are now logged at
debuglevel. -
AME-29965: The Configuration Provider node now works with the Inner Tree Evaluator node for nested inner journeys.
-
IAM-1782: Long gateway and agent IDs no longer overflow in the Advanced Identity Cloud admin console.
-
IAM-7523[7]: A user receiving a forwarded fulfillment task now has permission to approve or reject the task.
-
IAM-7537[7]: Governance functionality is now only shown for the
alpharealm. -
IAM-7689[7]: The Advanced Identity Cloud admin console now displays the Assigned To value in the task list for a user assigned to a role who receives a forwarded fulfillment task.
-
OPENAM-18252: Journeys acting on multiple identities now successfully update
universalIdin the journey context during the authentication flow. -
OPENAM-20314: Added the ability to indicate whether an OIDC provider doesn’t return a unique value for the
subclaim. -
OPENAM-22966: Social IDPs now support NONE as a client authentication method. This option should be used if the provider doesn’t require client authentication at the token endpoint.
03 Dec 2024
02 Dec 2024
Version 15824.0
This release reintroduces many features, enhancements, and fixes previously present in reverted versions.
Key features
- PingOne Authorize node
-
Use this node to send a decision request to a specified decision endpoint in your PingOne Authorize environment.
- PingOne Create, Identify, and Delete Nodes
-
The following PingOne nodes are now available:
- PingOne Identity Match node
-
Use the PingOne Identity Match node to identify if a user exists both in the user repository and in PingOne, using defined attributes.
- PingOne Create User node
-
Create new users in the PingOne platform using the PingOne Create User node. Create users based off of an existing user’s properties or choose to create the user anonymously. For example, when used in conjunction with PingOne Verify.
- PingOne Delete User node
-
Delete users from the PingOne platform with the PingOne Delete User node.
- PingOne Verify Nodes
-
Use the following PingOne Verify nodes in conjunction with the PingOne Identity Match node, PingOne Create User node, and PingOne Delete User node to create a seamless verification process in your journey:
- PingOne Verify Evaluation node
-
Leverage PingOne Verify to initiate or continue a verification transaction with the PingOne Verify Evaluation Node.
- PingOne Verify Completion Decision node
-
Determine the completion status of the most recent identity verification transaction for an end user.
Use before the PingOne Verify Evaluation node to determine the status of the verification process or after the PingOne Verify Evaluation node using a script to evaluate the transaction.
For example, you can evaluate if the transaction was completed using a passport and route your journey accordingly.
Use these nodes in place of the PingOne Verify Marketplace nodes. - reCAPTCHA Enterprise node
-
The reCAPTCHA Enterprise node node adds Google reCAPTCHA Enterprise support to your journeys.
- SAML application journeys (AME-27850)
-
Added support for SAML application journeys with a new setting on the remote SP. Configure a specific authentication journey that always runs for users authenticating with your SAML 2.0 app, regardless of existing sessions or configured authentication context.
Learn more in Configure a SAML 2.0 application journey.
- Set Failure Details node (AME-27871)
-
Use the Set Failure Details node to configure a localized error message on journey failure. You can also configure extra details in the response body of the failure request.
- Set Success Details node (OPENAM-12335)
-
Use the Set Success Details node to add additional details to the success response of a journey.
Enhancements
-
AME-26050: You can now create Next-generation Policy Condition scripts that have access to all common bindings, such as
openidmandhttpClient. Additionally, some existing bindings have been wrapped to improve usability in scripts. -
AME-28228: OAuth 2.0 audit logs now include the OAuth 2.0 client ID and any journey associated with the client.
-
AME-29009: When using the new FIDO Metadata Service, if you link to the FIDO metadata using a URL, Advanced Identity Cloud periodically downloads and updates the latest FIDO metadata based on the
nextUpdatedate specified in the downloaded data. -
AME-29093: Added configuration for integration with WebAuthn Metadata Services (such as the FIDO Metadata Service). This includes a realm-level WebAuthn Metadata service and a new FIDO Certification Level configuration attribute in the WebAuthn Registration Node.
-
AME-29769: The Social Provider Handler node has a new configuration option, Store Tokens, that allows access and refresh tokens to be stored in the transient state.
-
FRAAS-22321: You can now obtain the HTTP client location from the
X-Client-RegionHTTP header within your scripts and journeys. TheX-Client-Regionheader contains the country (or region) associated with the client’s IP address in the form of a Unicode CLDR region code, such asUSorFR. For most countries, these codes correspond directly to ISO-3166-2 codes. -
IAM-3323: You can now use XPath transformation functions with additional Workday application template attributes.
-
IAM-4540: You can now change the border color of a selected input field in journey and end-user pages.
-
OPENAM-23109: During a WebAuthn registration flow, if Store data in transient state is enabled, the Authenticator Attestation Global Unique Identifier (AAGUID) is now added to the node state under the
webauthnDatakey.
Fixes
-
AME-28016: When an invalid redirect URI is provided to the
/parendpoint, the URI mismatch error is nowredirect_uri_mismatchinstead ofinvalid_request. -
AME-28017: Advanced Identity Cloud now accepts the requested OAuth 2.0 endpoint as a valid JWT audience claim, as per RFC 7519 and RFC 9126.
-
AME-28906: The stack trace of an authentication exception generated on login failure is now logged only when
debuglevel logging is enabled. -
AME-29170: On LDAP Decision node login failure, stack traces are now logged at
debuglevel. -
IAM-7523[7]: A user receiving a forwarded fulfillment task now has permission to approve or reject the task.
-
IAM-7537[7]: Governance functionality is now only shown for the
alpharealm. -
OPENAM-18252: Journeys acting on multiple identities now successfully update
universalIdin the journey context during the authentication flow. -
OPENAM-20314: Added the ability to indicate whether an OIDC provider doesn’t return a unique value for the
subclaim. -
OPENAM-22966: Social IDPs now support
NONEas a client authentication method. Use this option if the provider doesn’t require client authentication at the token endpoint.
Rapid channel changelog archive
2024
26 Nov 2024
25 Nov 2024
Version 15770.0
Enhancements
-
FRAAS-22321: You can now obtain the HTTP client location from the
X-Client-RegionHTTP header within your scripts and journeys. TheX-Client-Regionheader contains the country (or region) associated with the client’s IP address in the form of a Unicode CLDR region code, such asUSorFR. For most countries, these codes correspond directly to ISO-3166-2 codes.
21 Nov 2024
Version 15726.0 (supplementary)
| This version has been reverted and all associated changes withdrawn. |
Key features
- PingOne Create, Identify, and Delete Nodes [24]
-
The following PingOne nodes are now available:
- PingOne Identity Match node
-
Use the PingOne Identity Match node to identify if a user exists both in the user repository as well as in PingOne, using defined attributes.
- PingOne Create User node
-
Create new users in the PingOne platform using the PingOne Create User node. Create users based off of an existing user’s properties or choose to create the user anonymously. For example, when used in conjunction with PingOne Verify.
- PingOne Delete User node
-
Delete users from the PingOne platform with the PingOne Delete User node.
- PingOne Verify Nodes [24]
-
Use the following PingOne Verify nodes in conjunction with the PingOne Identity Match node, PingOne Create User node, and PingOne Delete User node to create a seamless verification process in your journey:
- PingOne Verify Evaluation node
-
Leverage PingOne Verify to initiate or continue a verification transaction with the PingOne Verify Evaluation Node.
- PingOne Verify Completion Decision node
-
Determine the completion status of the most recent identity verification transaction for an end user.
Use before the PingOne Verify Evaluation node to determine the status of the verification process, or after the PingOne Verify Evaluation node using a script to evaluate the transaction.
For example, you can evaluate if the transaction was completed using a passport and route your journey accordingly.
Use these nodes in place of the PingOne Verify Marketplace nodes. - reCAPTCHA Enterprise node [24]
-
The reCAPTCHA Enterprise node node adds Google reCAPTCHA Enterprise support to your journeys.
20 Nov 2024
Version 15726.0
| This version has been reverted and all associated changes withdrawn. |
Key features
- Set Success Details node (OPENAM-12335)
-
Use the Set Success Details node to add additional details to the success response of a journey.
- Set Failure Details node (AME-27871)
-
Use the Set Failure Details node to configure a localized error message on journey failure. You can also configure extra details in the response body of the failure request.
Enhancements
-
AME-29769: The Social Provider Handler node has a new configuration option, Store Tokens, that allows access and refresh tokens to be stored in the transient state.
-
AME-29009: When using the new FIDO Metadata Service, if you link to the FIDO metadata using a URL, Advanced Identity Cloud periodically downloads and updates the latest FIDO metadata based upon the
nextUpdatedate specified in the downloaded data. -
AME-29093: Added configuration for integration with WebAuthn Metadata Services (such as the FIDO Metadata Service). This includes a realm-level WebAuthn Metadata service and a new FIDO Certification Level configuration attribute in the WebAuthn Registration Node.
-
AME-26050: You can now create Next-generation Policy Condition scripts that have access to all common bindings, such as
openidmandhttpClient. Additionally, some existing bindings have been wrapped to improve usability in scripts. -
OPENAM-23109: During a WebAuthn registration flow, if Store data in transient state is enabled, the Authenticator Attestation Global Unique Identifier (AAGUID) is now added to the node state under the
webauthnDatakey.
Fixes
-
AME-28016: When an invalid redirect URI is provided to the
/parendpoint, the URI mismatch error is nowredirect_uri_mismatchinstead ofinvalid_request. -
AME-28017: Advanced Identity Cloud now accepts the requested OAuth 2.0 endpoint as a valid JWT audience claim, as per RFC 7519 and RFC 9126.
-
AME-28906: The stack trace of an authentication exception generated on login failure is now logged only when
debuglevel logging is enabled. -
AME-29170: On LDAP Decision node login failure, stack traces are now logged at
debuglevel. -
OPENAM-18252: Journeys acting on multiple identities now successfully update
universalIdin the journey context during the authentication flow. -
OPENAM-22966: Social IDPs now support
NONEas a client authentication method. Use this option if the provider doesn’t require client authentication at the token endpoint. -
OPENAM-20314: Added the ability to indicate whether an OIDC provider doesn’t return a unique value for the
subclaim.
19 Nov 2024
Versions 15711.0, 15715.0
No customer-facing features, enhancements, or fixes released.[5]
18 Nov 2024
Versions 15703.0, 15708.0
No customer-facing features, enhancements, or fixes released.[5]
15 Nov 2024
Versions 15687.0, 15696.0, 15699.0
No customer-facing features, enhancements, or fixes released.[5]
06 Nov 2024
Version 15572.0
Key features
- Configure journey to always run[25] (AME-27848)
-
Added a new setting for journeys to always run regardless of existing user sessions.
Learn more in Configure an authentication journey to always run.
- SAML application journeys (AME-27850)
-
Added support for SAML application journeys with a new setting on the remote SP. Configure a specific authentication journey that always runs for users authenticating with your SAML 2.0 app, regardless of existing sessions or configured authentication context.
Learn more in Configure a SAML 2.0 application journey.
- SAML application script binding[25] (AME-28012)
-
Added a new
samlApplicationbinding for querying the SAML 2.0 authentication request properties and IdP and SP configuration attributes.Learn more in Query SAML application and authentication request.
- Suspend and resume journeys (OPENAM-21806)
-
Next-generation decision node scripts can now use the new
action.suspend()method to suspend the current authentication session and send a message to the user. Implement custom logic with the resume URI, for example, to send an email or SMS using the HTTP client service.Learn more in Suspend and resume journeys.
Enhancements
-
AME-27074: Added a new
configProviderScriptaction to each authentication node endpoint to generate a configuration provider template script, for example:authentication/authenticationtrees/nodes/MessageNode?_action=configProviderScript. -
AME-28258: Added a new "webAuthnExtensions" input to the WebAuthn Registration and Authentication nodes. This can be set via a Scripted Decision node. It is expected to contain a map of extension name to input. Output is currently not available.
-
AME-28384: The outcome of a Scripted Decision node can now also be a
CharSequencetype. -
AME-28777: The refresh token grace period now applies to both client-side refresh tokens and server-side refresh tokens.
-
AME-29157: Authentication nodes with limited possible outcomes are now available to the Configuration Provider node, including:
The Identity Assertion node, Push Wait node, and Enable Device Management node nodes with fixed outcomes are also now available to the Configuration Provider node.
-
OPENAM-22601: You can now use the next-generation script binding,
utils, to generate secure random numbers. -
OPENAM-22811: NodeState has two new methods:
mergeShared(Map<String, Object>)andmergeTransient(Map<String, Object>). Use them to merge keys into the shared/transient state, including "objectAttributes" keys.
Fixes
-
AME-25491: The Configuration Provider node script now correctly reads node state after an inner tree callback.
-
AME-28786: Removed several unused UI properties from default social identity provider profiles.
-
AME-29027: WebAuthN attestations containing a self-signed root CA are now rejected instead of silently removed.
-
OPENAM-22465: Fixed error to return
invalid_resource_uriwhen request_uri client doesn’t match request parameter client in PAR authorise request. -
OPENAM-22675: In next-generation scripting, you can now set a default name correctly when creating a NameCallback.
-
OPENAM-22688: Fixed Page node localization to default to correct locale when the incoming
accepted-languageheader doesn’t match the node’s language configuration.
29 Oct 2024
Versions 15466.0, 15472.0
17 Oct 2024
Versions 15335.0, 15337.0
No customer-facing features, enhancements, or fixes released.[5]
15 Oct 2024
Versions 15310.0, 15312.0
No customer-facing features, enhancements, or fixes released.[5]
14 Oct 2024
Version 15300.0
Enhancements
-
IAM-7187: Integration of SAP app template with IDM scripts.
-
IAM-7243[7]: Added text field to utilities category in IGA access request forms.
20 Sept 2024
Versions 15044.0, 15052.0
Key features
- Support for LINE as a social identity provider (AME-28672)
-
You can now configure a social provider authentication with LINE Login when signing in from a browser. There is a separate configuration for authenticating from a mobile app.
Learn more in Social authentication.
- Identity Governance request and approval forms[7] (IAM-6358)
-
Identity Governance now lets you create request and approval forms to make it easier for end users to request access to applications.
Learn more in Identity Governance forms.
16 Sept 2024
Version 14975.0
Key features
- Additional cloud connectors
-
The following connectors are now bundled with Advanced Identity Cloud:
-
AWS IAM Identity Center Connector v1.5.20.23 (OPENIDM-20038)
-
Box Connector v1.5.20.23 (OPENIDM-20367)
Learn more in the ICF documentation.
-
13 Sept 2024
Version 14962.0
Key features
- Advanced Reporting[11] (ANALYTICS-763)
-
Advanced Identity Cloud now offers Advanced Reporting to let you create custom reports on activity in your tenant environments. You can query a number of metrics to create useful reports for your company.
Learn more in Advanced Reporting.
09 Sept 2024
Versions 14868.0, 14888.0
Key features
- Scripted SAML v2.0 NameID values(AME-25921)
-
The NameID mapper script lets you customize SAML v2.0 NameID values per application.
- Set State node (AME-26443)
-
The Set State node lets you add attributes to the journey state.
- Http Client service (AME-27936)
-
The new Http Client service lets you create named instances that you can reference from a next-generation script to make mTLS connections to external services.
Learn more in Access HTTP services.
- Enable Device Management node (SDKS-2919)
-
The new Enable Device Management node lets end users manage devices from their account.
Enhancements
-
FRAAS-21728: Updated the cookie domain API to add default values for GET requests where cookie domain values haven’t been overridden by a PUT request. The default values are derived from the existing tenant cookie domain configuration, so are backward compatible.
-
AME-26594: Added secrets API binding to all next-generation script contexts.
-
AME-27129: Added option to exclude client certificate from SAML hosted SP metadata.
-
AME-27792: Added
AM-TREE-LOGIN-COMPLETEDaudit log event that outputs aresultofFAILED. when a journey ends with an error. -
AME-27839: Added the ability to specify connection and response timeouts for Http Client service instances.
-
AME-28008: You can now disable certificate revocation checks, or all certificate checks entirely, on your Http Client service instances.
Fixes
-
OPENAM-15410: Fixed an issue that prevented customization of claims if
profileandopenidscopes are requested. -
OPENAM-20609: Fixed inconsistent error message when generating access token using refresh token after changing username.
-
OPENAM-21974: Adds an OAuth 2.0 client configuration for the new version of the LinkedIn provider.
-
OPENAM-22298: Log unretrieved SP and IdP descriptors in SAML2 Authentication node.
29 Aug 2024
Version 14741.0
Key features
- DocuSign application template (IAM-6194)
-
The DocuSign application lets you manage DocuSign service accounts and synchronize DocuSign accounts and Advanced Identity Cloud identities.
Enhancements
-
IAM-6493: The PingOne application template now supports specifying an LDAP gateway.
-
IAM-6868: Added screen reader label to end-user access approval button.
-
IAM-6870: Added screen reader label to end-user access request button.
-
IAM-6880: Added a toggle in the hosted pages journey settings to disable the error heading fallback that displays if there is no heading in the page content. (FORGEROCK-1582)
21 Aug 2024
Version 14626.0
Key features
- BeyondTrust application template (IAM-6492)
-
The BeyondTrust application lets you manage and synchronize data from Advanced Identity Cloud to BeyondTrust.
02 Aug 2024
Versions 14410.0, 14417.0
19 Jul 2024
Version 14225.0
Key features
- Adobe Admin Console application template (IAM-6195)
-
The Advanced Identity Cloud Adobe Admin Console application lets you manage users, groups, and user group memberships between Adobe Admin Console and Advanced Identity Cloud.
02 Jul 2024
Version 14013.0
Fixes
-
FRAAS-20970: The
/monitoring/logsendpoint now returns anX-Ratelimit-Limitheader with a fixed value of 60. Previously, the value was misleading due to the way it was calculated when scaling an environment’s resources. TheX-Ratelimit-Remainingheader continues to report the number of requests that may be sent before receiving a rate limited response.
27 Jun 2024
Versions 13964.0, 13966.0
Key features
- Additional cloud connectors
-
The following connectors are now bundled with Advanced Identity Cloud:
-
Adobe Admin Console connector (OPENIDM-19843)
-
DocuSign connector (OPENIDM-20190)
For more information, refer to the ICF documentation.
-
Fixes
-
OPENIDM-20142: Resolved a communication failure between Advanced Identity Cloud and RCS instances that could result in a prolonged failure to activate remote connectors.
Changed functionality
-
OPENIDM-20178: You can’t use scope private fields in query filters. For more information, refer to link:Security Advisory #202402.
24 Jun 2024
Versions 13937.0
Key features
- Product name change for Identity Cloud (FRAAS-20178)
-
To align ForgeRock products with Ping family names, ForgeRock Identity Cloud has been renamed to PingOne Advanced Identity Cloud. Name and logo changes have been updated throughout the user interfaces, and documentation updates will occur when the UI changes are released to the regular channel.
For more information, refer to the New names for ForgeRock products FAQ.
Enhancements
-
IAM-4785: Synchronize only the modified properties on a target source during reconciliation of applications.
-
IAM-5237[7]: Add ability for B2B business partners to certify access for their users using organizational-based certification.
-
IAM-5487: Correlation rules moved to the top of the reconciliation settings page.
-
IAM-5629[7]: Add ability to create scoping rules in Identity Governance.
-
IAM-6231: Scripted Decision Node now updates the list of scripts when a script is added or edited.
-
IAM-6544[7]: Add reviewer column to administrator list view of compliance violations.
Fixes
-
IAM-6135: ESV values containing accents get corrupted by encoding process.
-
IAM-6562: Label duplicated for OAuth 2.0 access token and ID token endpoints.
-
IAM-6669[7]: Badge count of violations in end-user navigation doesn’t update when an action is performed.
18 Jun 2024
Versions 13896.0, 13900.0
Key features
- PingOne Protect nodes[26] (TNTP-180)
-
The new PingOne Protect nodes replace the deprecated PingOne Protect Marketplace nodes.
Fixes
-
FRAAS-20604: Removed superfluous AM metrics related to token store internals:
-
am_cts_connection_count -
am_cts_connection_seconds -
am_cts_connection_seconds_total -
am_cts_connection_state -
am_cts_reaper_cache_size -
am_cts_reaper_deletion -
am_cts_reaper_deletion_count -
am_cts_reaper_deletion_total
-
-
FRAAS-20786: Fix promotion issue where an attempt was made to delete an already deleted application.
12 Jun 2024
Version 13848.0
Key features
- New utility binding available for scripting (AME-25519)
-
You can now use a new utility binding in your scripts to access several common utility classes. For example, the utility binding includes classes for generating random UUIDs and for base64 encoding and decoding.
Enhancements
-
AME-26199: Added the ability to set additional claims, including non-registered claims, during JWT assertion and generation, as per the specification.
-
AME-26820: Provided library scripts with access to all common script bindings.
-
AME-26993: Enhanced secret mapping for agents. Updating a secret label identifier value now causes any corresponding secret mapping for the previous identifier to also be updated, provided no other agent shares that secret mapping. If another agent shares the secret mapping, Advanced Identity Cloud creates a new secret mapping for the updated identifier and copies its aliases from the previously shared secret mapping.
-
AME-27346: Renamed Secret ID Identifier to Secret Label Identifier in the SAML remote entity provider configuration.
-
AME-27478: Renamed Client ID Token Public Encryption Key property to ID Token Encryption Public Key in the OAuth 2.0 client configuration.
-
AME-27775: Added scripting thread pool metrics per script context.
-
OPENAM-16564: Enabled next-generation scripts to access the cookies in incoming requests.
-
OPENAM-21800: Added page node functionality to next-generation scripts.
-
OPENAM-21933: Enabled auto-encoding of the
httpClientform body in next-generation scripts.
Fixes
-
FRAAS-19461: Fixed an issue where large audit logs could be missing from IGA events and processing.
-
OPENAM-21748: Restored the missing
getwrapper function forHiddenValueCallbackin next-generation scripting. -
OPENAM-21864: Fixed an issue that prevented setting the tracking cookie to resume a journey after returning from a redirect flow.
-
OPENAM-21897: Corrected inconsistent results from the policy
evaluateTreeendpoint. -
OPENAM-21951: Enabled setting of the
selectedIndexproperty in aChoiceCallbackin next-generation scripts. -
OPENAM-22181: Corrected an issue with UMA
approveandapproveAllrequests failing.
05 Jun 2024
Version 13760.0
Enhancements
-
FRAAS-20048: Configuration promotions can now be rolled back using the API. An environment can be rolled back successively to revert as many previous promotion changes as needed.
This feature can’t be used in sandbox environments; a promotion or a rollback can only be run between development, UAT[2], staging, and production environments.
22 May 2024
Versions 13570.0
Key features
- Oracle E-Business Suite app template (IAM-6342)
-
The Oracle E-Business Suite (EBS) application lets you manage and synchronize accounts between EBS and Advanced Identity Cloud.
Enhancements
-
IAM-6376: In the applications rules tab, you can now configure custom logic to perform specific actions, such as sending an email, when an account is successfully created or updated.
-
IAM-6380: In the applications rules tab, you can now use the provisioning failure rule to configure custom logic to perform specific actions when provisioning fails.
20 May 2024
Version 13528.0
03 May 2024
Key features
- Webex application template (IAM-5234[28])
-
The Advanced Identity Cloud Webex application lets you manage and synchronize data between Webex Control Hub and Advanced Identity Cloud.
- Epic EMP application template (IAM-2407)
-
The Epic EMP application lets you manage and synchronize data between Epic EMP and Advanced Identity Cloud.
Enhancements
-
IAM-2653: Configure object properties with user-friendly display names.
-
IAM-3857: Application list view displays enabled/disabled status of enterprise apps.
-
IAM-5913[7]: Create custom access request workflows.
17 Apr 2024
Version 13218.0
Key features
- Event-based certification[7] (IAM-5148)
-
Identity Governance now allows tenant administrators to configure certifications that are triggered by specific governance events, a process referred to as event-based certification. This method offers faster certification resolution compared to scheduled—and often lengthy—campaigns spanning weeks or months and involving numerous applications, intricate rules, and hundreds of reviewers.
The event-based certifications feature kicks off an identity certification for the following events:
-
User create. Advanced Identity Cloud detects when a user account has been created.
-
User modify. Advanced Identity Cloud detects when an existing user account has been modified or updated.
-
Attribute change. Advanced Identity Cloud detects changes in the attributes of an existing user account.
-
User delete/deactivate. Advanced Identity Cloud detects if a user account has been deleted or deactivated.
For more information, refer to Certify access by event.
-
- Grant entitlements to users and roles[7] (IAM-5146)
-
Identity Governance now allows tenant administrators to carry out more fine-grained entitlement grants for their user accounts. Tenant administrators can now:
-
Create a role and grant entitlements to the role.
-
Revoke entitlements in a role.
-
Grant entitlements to a user account.
-
Revoke entitlements from a user account.
For more information, refer to Manage entitlements.
-
- Identity Assertion node (AME-26821)
-
The new Identity Assertion node provides a secure communication channel for authentication journeys to communicate directly with PingGateway.
- PingOne application template (IAM-5232)
-
The PingOne application lets you manage and synchronize data between PingOne and Advanced Identity Cloud.
- Authenticate gateway and agent profiles with a shared secret (IAM-5833)
-
The Advanced Identity Cloud admin console for gateways and agents now lets you authenticate with a shared secret instead of a password. Use this to set the label for the shared secret.
- Authenticate OAuth 2.0 applications with a shared secret (IAM-6028)
-
The Advanced Identity Cloud admin console for OAuth 2.0 applications now lets you authenticate with a shared secret instead of a password. Use this to set the label for the shared secret.
Enhancements
-
OPENAM-21031: The performance of Google KMS has been improved by the introduction of caching.
-
AME-27126: A SAML SP can now authenticate to IDPs using mutual TLS (mTLS) when making an artifact resolution request.
-
IAM-3199: HTML styling in the Message node journey editor allows you to left justify text.
Fixes
-
FRAAS-19334: Failure to look up service account names following changes applied through the ESV API.
-
IAM-5079[7]: End-user roles page sometimes shows role grants as conditional even when the grants are direct.
-
IAM-5363[7]: Show the total number of approvals and access reviews in the inbox.
-
IAM-5858[7]: Missing support for access request global configuration options.
-
IAM-6138[7]: The governance events filter builder incorrectly validates
beforeandafterproperties in the user created state. -
IAM-6176[7]: The end-user access request rejection is missing a justification message.
-
IAM-6203[7]: The governance events filter doesn’t use
aftertemporal values for user created flows. -
IAM-6209: The Advanced Identity Cloud admin console navigation panel text appears when the panel is collapsed.
-
OPENAM-21473: If you set the collection method of a Certificate Collector node to
REQUEST,HEADER, orEITHER, and the certificate is not provided in the request or in the header, the node now returns a status ofNot collected.This node is currently not supported in Advanced Identity Cloud. -
SDKS-2935: The Device Binding node now gracefully handles the case of a user being set to
inactive.
11 Apr 2024
Version 13149.0
Enhancements
-
AME-26085: SAML v2.0
NameIDmapping can be configured per SP -
AME-27133: "Secret ID" has been renamed to "Secret Label" for secret mappings
-
The following services now support configuration using the Secrets API:
-
AME-16536: The OAuth 2.0 provider hash salt secret
-
AME-25885: The persistent cookie core authentication attribute
-
AME-26110: The client-side session signing key
-
AME-26134: The social provider service
-
AME-26441: The new CAPTCHA node (replaces the legacy CAPTCHA node)
-
AME-26442: The OIDC Token Validator node now lets you store the client secret in any type of secret store
-
AME-26633: The OAuth 2.0 client
clientJwtPublicKey -
AME-26637: The OAuth 2.0 client
idTokenPublicEncryptionKey -
AME-26639: OAuth 2.0 client mTLS self-signed certificates
-
AME-26668: The post authentication process (PAP) replay password
-
AME-26670: The web agents replay password key
-
AME-26998: The OAuth 2.0 client secret
-
-
The following services now support rotation of secrets using secret versions:
-
AME-25988: The persistent cookie encryption secret
-
AME-26999: OAuth 2.0 client secrets
-
AME-27000: OAuth 2.0 client
clientJwtPublicKey -
AME-27001: OAuth 2.0 client mTLS self-signed certificates
-
09 Apr 2024
Version 13122.0
Key features
- PingOne Verify service (TNTP-118)
-
The PingOne Verify service lets you configure and use PingOne Verify nodes (PingOne Verify Authentication node and PingOne Verify Proofing node) in your authentication journeys.
For more information, refer to PingOne Verify service.
26 Mar 2024
Versions 12899.0
Key features
- Social Provider Handler node[29] (OPENAM-20924)
-
The new Social Provider Handler node adds an outcome to better handle interruptions in a social authentication journey after requesting profile information.
- Event-based certification[7] (IGA-2357)
-
Identity Governance now allows tenant administrators to configure certifications that are triggered by specific governance events, a process referred to as event-based certification. This method offers faster certification resolution compared to scheduled—and often lengthy—campaigns spanning weeks or months and involving numerous applications, intricate rules, and hundreds of reviewers.
The event-based certifications feature kicks off an identity certification for the following events:
-
User create. Advanced Identity Cloud detects when a user account has been created.
-
User modify. Advanced Identity Cloud detects when an existing user account has been modified or updated.
-
Attribute change. Advanced Identity Cloud detects changes in the attributes of an existing user account.
-
User delete/deactivate. Advanced Identity Cloud detects if a user account has been deleted or deactivated.
For more information, refer to Certify access by event.
-
- Grant entitlements to users and roles[7] (IAM-5146)
-
Identity Governance now allows tenant administrators to carry out more fine-grained entitlement grants for their user accounts. Tenant administrators can now:
-
Create a role and grant entitlements to the role.
-
Revoke entitlements in a role.
-
Grant entitlements to a user account.
-
Revoke entitlements from a user account.
For more information, refer to Manage entitlements.
-
Enhancements
-
AME-26130[29]: Updated the PUSH Notification service to store access keys as a secret
-
AME-25906[29]: Updated Identity Gateway agents to store credentials as a secret
-
IAM-4585: Request and approvals page now shows the current and past approvers, their decisions, and the dates
-
IAM-4968: Expose additional top-level parameters in the advanced section of mapping pages
-
IAM-5769: Add grouping logic to journey node items
-
IAM-5674: Target application can use ONBOARD action for FOUND situation
-
IAM-5814: Allow fixed application usernames to be chosen for custom SAML apps
-
OPENAM-21575[29]: Added
org.forgerock.json.jose.jwe.JweHeaderto the allowlist for Scripted Decision nodes
Fixes
-
AME-25915[29]: Assertion consumer processing fails if NameID format not present in the assertion response
-
IAM-3927[7]: Identity Governance now enforces mandatory comments (if configured) for revoke and allow exceptions
-
IAM-4309: Access reviews no longer display the internal
lastSyncuser attribute -
IAM-4762: Authoritative apps are now requestable
-
IAM-4986: Platform UI can now determine whether to use a pagedResultsCookie or offset for paging results
-
IAM-5076: "Abstain from action" option no longer displays when a campaign has expired
-
IAM-5362: Marking a property as an authoritative app entitlement no longer causes target app config to be generated
-
IAM-5413: Account deprovisioning now works in AD/LDAP after deleting a user identity
-
IAM-5794: Border color of sign-in input fields in hosted pages can now be overridden in themes
-
IAM-5875: Journey editor no longer orphans deleted nodes
21 Mar 2024
Versions 12899.0, 12863.0, 12855.0
Key features
- Additional cloud connectors
-
The following connectors are now bundled with Advanced Identity Cloud:
-
Dropbox connector (OPENIDM-19838)
-
PingOne connector (OPENIDM-19736)
-
Webex connector (OPENIDM-19920)
For more information, refer to the ICF documentation.
-
Enhancements
-
OPENIDM-19921: The following connectors included with Advanced Identity Cloud were upgraded to 1.5.20.21:
-
Google Apps connector
-
Microsoft Graph API connector
-
AWS connector
For details, refer to 1.5.20.21 Connector changes.
-
18 Mar 2024
Versions 12873.0, 12784.0
Enhancements
-
FRAAS-19341: ESV support for AES keys through the
base64aesencoding typeFor more information, refer to Encoding format.
15 Mar 2024
Versions 12754.0
Key features
- PingOne Service (TNTP-148)
-
The PingOne Service lets you set up the PingOne service in your Advanced Identity Cloud tenant so you can add Ping Identity nodes to your authentication journeys.
For more information, refer to PingOne Service.
- PingOne nodes (TNTP-119)
-
- PingOne node
-
The PingOne node node establishes trust between PingOne and Advanced Identity Cloud by leveraging a federated connection. For more information, refer to PingOne node.
- PingOne DaVinci API node
-
The PingOne DaVinci API node node lets an Advanced Identity Cloud journey trigger a PingOne DaVinci flow through the API integration method. For more information, refer to PingOne DaVinci API node.
- PingOne Protect nodes (TNTP-127)
-
Ping Identity’s PingOne Protect is a centralized identity threat protection service, for securing your digital assets against online fraud attempts.
For more information, refer to PingOne Protect > How it Works.
13 Mar 2024
Version 12714.0
Key features
- HTTP Client node (TNTP-136)
-
The HTTP Client node lets you make HTTP(S) requests to APIs and services external to Advanced Identity Cloud from within a journey.
Use the HTTP Client node to simplify the integration with a broad range of external services by making direct HTTP(S) requests.
For more information, refer to HTTP Client node.
02 Mar 2024
Version 12580.0
Enhancements
-
The following services now support setting secrets using the secrets API rather than setting secrets in the service configuration:
-
AME-25709: AuthId signing key
-
AME-25907: Java agents
-
AME-25908: Web agents
-
AME-26014: Rotatable secrets for agents
-
AME-26301: SAML remote entities
-
AME-26241: OATH, Push, Web AuthN devices and the device binding, device ID, and Device profile services
-
-
The following nodes now support setting their secrets using the secrets API rather than setting secrets in the node configuration:
-
AME-26117: OTP SMS Sender and OTP SMTP Sender nodes
-
AME-16535: Set Persistent Cookie node
-
-
AME-26041: Enhanced handling of agents secret mappings – if you update or delete a secret label identifier, any corresponding secret mapping for the previous identifier is updated or deleted, provided no other agent shares that secret mapping
-
AME-25434: New Request Header node lets you inject values into shared state based on request header values
-
AME-26039: Added LDAP Affinity Level configuration option to the LDAP Decision node, to enable affinity-based load balancing for BIND requests
-
OPENAM-21768: Added
org.forgerock.opendj.ldap.Rdnandorg.forgerock.opendj.ldap.Dnclasses to the allowlist for all script contexts
Fixes
-
AME-24760: Inner nodes of a PageNode don’t independently audit node-login-complete events
-
AME-26158: Exception thrown when generating a Signed JWT with no encryption within a next-gen script called by a Scripted Journey node
-
OPENAM-17315: Scripts used to call 'response.getEntity()' in the past should now use 'response.getEntity().getString()' instead
-
OPENAM-21856: Introspecting stateless token with IG/Web agents causes
OAuth2ChfException
29 Feb 2024
Version 12560.0
Enhancements
-
IAM-4257: Azure AD app template updates
-
IAM-4342: MSGraphAPI connector includes a new optional
licenseCacheExpiryTimeconfiguration property -
IAM-4892: Salesforce app template updates
-
IAM-4900: UI has been updated to show the Advanced Identity Cloud build number
-
IAM-5033: Added new "Remember my username" checkbox to authentication trees
-
IAM-5287: Updated username, password, and KBA heading size on the profile page to improve accessibility
-
IAM-5334: Expose "Guarded String" as an object type property for Scripted Groovy, ScriptedREST, ScriptedSQL, CSV, Database table, and SCIM connectors
-
IAM-5459: KBA answer field now contains question context
-
IAM-5461: Custom errors sent as
TextOutputCallback.ERRORare now rendered as primary login errors, improving screen reader accessibility feature -
IAM-5503: Rename Orchestrations to Workflows
-
IAM-5563: Google Apps app template updates
-
IAM-5603: Create device details modal for managed user identities
-
IAM-5606: Add "POWERED BY" metadata to marketplace nodes
-
IAM-5748: Make "PingOne" a special case on the federation providers page
Fixes
-
IAM-5598: Styled terms and conditions included in a journey causes authenticate calls to fail
-
IAM-5611: Can’t revoke custom apps from roles or edit them from the role view
-
IAM-5641: Custom endpoints search returns endpoints created by other areas of the UI
-
IAM-5692: Console errors when opening the Add user modal for Bravo realm
-
IAM-5767: SAML SSO is not used when an application is saved from another tab after SSO setup
-
IAM-5873: Hosted page may fail to match user locale
28 Feb 2024
Version 12547.0
Enhancements
-
OPENIDM-19405: Allow email addresses to contain non-ASCII characters for supported SMTP providers
24 Jan 2024
Fixes
-
OPENIDM-18743[30]: Attempts to use connectors fail with null pointer exceptions when
operationOptionsis defined in the provisioner configuration
23 Jan 2024
Key features
- iProov Authentication node (TNTP-131)
-
The iProov authentication node integrates Advanced Identity Cloud authentication journeys with the Genuine Presence Assurance and Liveness Assurance products from iProov.
22 Jan 2024 (supplementary)
Key features
- Fingerprint Profiler and Fingerprint Response nodes (TNTP-130)
-
The Fingerprint nodes nodes let you integrate your Advanced Identity Cloud environment with the Fingerprint platform to help reduce fraud and improve customer experience.
Enhancements
-
AME-25906: Add the ability to configure the password for authenticating to an Identity Gateway agent as an ESV secret
-
AME-26130: Add the ability to configure the SNS access key secret for the push notification service to use an ESV secret
-
OPENAM-21575: Add
org.forgerock.json.jose.jwe.JweHeaderto the class allowlist for Scripted Decision node
Fixes
-
AME-25915: SAML flow fails if a
NameIDFormatelement is not present in an assertion response -
FRAAS-18464: Sandbox debug logging level set to
WARNinstead ofDEBUG -
IAM-5656: Fix alignment of text, buttons, and links in Message nodes
-
IAM-5660: Hosted pages not displaying list of themes
-
OPENAM-20924: Social Provider Handler node does not let end user switch to a different IdP
22 Jan 2024
Enhancements
-
AME-26117: Updated nodes relating to one-time passwords to use secret labels for passwords. Refer to OTP Email Sender node and OTP SMS Sender node.
19 Jan 2024
Key features
- RSA SecurID node (FRAAS-18037)
-
The RSA SecurID lets you use the RSA Cloud Authentication Service (RSA ID Plus) or RSA Authentication Manager from within an authentication journey on your Advanced Identity Cloud environment.
- Advanced Identity Cloud use case catalog
-
Introducing the release of the Advanced Identity Cloud use case catalog, a collection of guides that focus on tenant administrator use cases and third-party integrations.
18 Jan 2024
Key features
- Create and manage custom relationship properties (OPENIDM-19106, OPENIDM-19109)
-
You can now create and manage custom relationship properties using the Advanced Identity Cloud admin console.
- Schema API improvements (OPENIDM-19107)
-
You can now directly modify managed object schemas over REST using the schema API. This capability includes configuring custom relationship properties.
- Password timestamps (OPENIDM-19262)
-
Enabling this new feature lets you view or query when a user password was last changed and when it is set to expire.
Enhancements
-
OPENIDM-19674: The relationship-defined virtual property (RDVP) schema editor allows you to edit the
flattenPropertiesproperty. The managed object schema editor allows you to edit thenotifyRelationshipsproperty.
Fixes
-
OPENIDM-18957: The scheduler now attempts to release any triggers it attempted to acquire during a timeout due to an unresponsive repository
-
OPENIDM-19141: Workflow engine queries now properly honor
tablePrefixandtablePrefixIsSchemaconfiguration options -
OPENIDM-19279: Resource collection is required to create a relationship
-
OPENIDM-19565: The default
apiVersionconfiguration has been updated with additional resource paths
2023
19 Dec 2023
Key features
- Schedule jobs directly in the Advanced Identity Cloud admin console (IAM-3489)
-
You can now schedule the following jobs directly in the Advanced Identity Cloud admin console without using the IDM native admin console:
-
Scripts: Execute a script at a regular interval.
-
Task scanner: Execute a scan of identities using a complex query filter at a regular interval. The scan can then execute a script on the identities returned by the query filter.
-
- New Identity Governance capabilities[7] (IAM-4617, IGA-1664)
-
The Workflow UI lets you define custom workflow definitions for all access request types.
Role membership certification, a new certification type for access reviews, lets you review and certify roles and the users who have access to roles. Primary reviewers are role owners, a single user, or users assigned to a role.
Enhancements
-
FRAAS-7382: Add ability to include JavaScript snippets in login and end-user UIs
-
IAM-4514[7]: Allow reviewers to add user, entitlement, and role columns to an access review
-
IAM-4739: Add read schema option to SCIM application template to discover custom schemas/attributes
-
IAM-5201: Focus on first input field or button automatically upon page load
-
IAM-5268: Add source-missing situation rule to authoritative applications
Fixes
-
FRAAS-16659: ESV mapping updates aren’t captured in promotions report
-
IAM-4810: Custom endpoint UI missing context option
-
IAM-5072: Inbound mapping tab shows in target applications
-
IAM-5171: Azure Active Directory application template doesn’t return a user’s role membership
-
IAM-5187: LDAP v2.1 application template doesn’t clear
dc=example,dc=combase DN -
IAM-5238: LDAP application template is missing the group object classes property
-
IAM-5422[7]: Entitlement owner doesn’t show in the entitlement list
12 Dec 2023
Enhancements
-
AME-22326[31]: The
httpClientavailable in scripts now automatically adds the currenttransactionIdas an HTTP header. This lets you correlate caller and receiver logs to make requests to other ForgeRock products and services. -
AME-25392[31]: Add
org.forgerock.openam.scripting.api.PrefixedScriptPropertyResolver, used for accessing ESVs from scripts, to the allowlist forSAML2_SP_ADAPTERandSAML2_IDP_ADAPTERscript types -
AME-25433[31]: Add
com.sun.crypto.provider.PBKDF2KeyImpl,javax.crypto.SecretKeyFactory, andjavax.crypto.spec.PBEKeySpecto the allowlists for Scripted Decision nodes and Configuration Provider nodes -
AME-25608[31]: Add auditing for opening and closing connections for the LDAP decision node, ID Repo service, and Policy Configuration service
-
AME-25630[31]: Add
java.security.spec.InvalidKeySpecExceptionto the allowlist for the Scripted Decision and Configuration Provider nodes -
OPENAM-16897[31]: The OAuth 2.0 Device grant flow can now return either JSON or HTML
Fixes
-
COMMONS-1397[31]: Audit event log entries not logged due to thread contention
-
FRAAS-17686[32]: Add
org.forgerock.json.jose.jwe.JweHeaderto the allowlists for theAUTHENTICATION_TREE_DECISION_NODEandCONFIG_PROVIDER_NODEscript types -
IAM-4401[31]: Disabling
Clear-Site-Dataheader breaks realm login -
OPENAM-17331[31]: Disabled SNS endpoints can now be re-enabled
-
OPENAM-17816[31]: OAuth 2.0 requests without a
Content-Typeheader fail with a 500 error -
OPENAM-19282[31]: Recovery Code Display node only works immediately after a registration node
-
OPENAM-19889[31]: Policy evaluation fails when subject is agent access token JWT
-
OPENAM-20026[31]: Social IDP with trailing whitespace in the name can’t be deleted using the UI
-
OPENAM-20329[31]: Issuer missing from OAuth 2.0 JARM response
-
OPENAM-21053[31]: Missing
userIdfrom access audit log whenorg.forgerock.security.oauth2.enforce.sub.claim.uniqueness=falsein JWT client authentication flow -
OPENAM-21421[31]: Scripting logger name isn’t based on logging hierarchy convention
-
OPENAM-21476[31]: Persistent cookie is not created when using Configuration Provider node
-
OPENAM-21484[31]: Introspection of a stateful refresh token for claims field for known OAuth2 fields is now a string and not nested in a list
30 Nov 2023
Fixes
-
IAM-5275[31]: Advanced Identity Cloud admin console doesn’t add query parameters to the logout URL
Notices
ForgeRock deprecated the option to let Advanced Identity Cloud tenant administrators skip 2-step verification on Friday, February 3, 2023.
The end-of-life date for this deprecation is Friday, March 1, 2024, when the skip option functionality will be removed from Advanced Identity Cloud. You have until this date to update your tenants to make 2-step verification mandatory for all tenant administrators. For more information, refer to Tenant administrator mandatory 2-step verification FAQ.
28 Nov 2023
Key features
- Duo Universal Prompt node (FRAAS-15675)
-
The Duo Universal Prompt node lets you provide two-factor authentication using Duo’s Universal Prompt authentication interface. You can integrate Universal Prompt with your web applications using the Duo Web v4 SDK.
For details, refer to Duo Universal Prompt node.
27 Nov 2023
Enhancements
-
FRAAS-17939[33]: Some connectors included with Advanced Identity Cloud were upgraded to the following versions:
1.5.20.19For details, refer to 1.5.20.19 Connector changes.
-
Microsoft Graph API connector
-
SCIM connector
1.5.20.18For details, refer to 1.5.20.18 Connector changes.
-
Google Apps connector
-
Microsoft Graph API connector
-
Salesforce connector
-
SCIM connector
-
Workday connector
-
-
OPENIDM-19037: Update property value substitution to reflect boolean value in the UI
17 Nov 2023
13 Nov 2023
Fixes
-
FRAAS-17883: Tenant administrators cannot save edits to their personal information
-
IAM-5226: Tenant administrator security questions should not be shown when editing personal information
-
IAM-5240: No error message displays when a tenant administrator fails to save edits to their personal information
31 Oct 2023
Key features
- next-generation scripting enhancements (AME-25928)
-
The next-generation scripting engine for journey decision node scripts lets you:
-
Reduce the need to allowlist Java classes with a stable set of enhanced bindings.
-
Simplify scripts with fewer imports and more intuitive return types that require less code.
-
Debug efficiently with clear log messages and a simple logging interface based on SLF4J.
-
Make requests to other APIs from within scripts with a more intuitive HTTP client.
-
Modularize your scripts by reusing common code snippets, including external libraries such as CommonJS, with library scripts.
-
Access identity management information seamlessly through the
openidmbinding.
The next-generation engine can’t use legacy scripts.
If your Scripted Decision node uses legacy scripts, you must convert them to use updated bindings to take advantage of the benefits of the next-generation scripting engine.
Where possible, you should migrate legacy scripts to take advantage of next-generation stability.
For more information, refer to Next-generation scripts.
-
Enhancements
-
FRAAS-3841: Activate and deactivate journeys in the Advanced Identity Cloud admin console. Refer to Deactivate journeys.
-
IAM-4191: Allow tenant session cookie name to be configured. Refer to Session cookie name.
-
IAM-4735: Add support for schema discovery in application templates
-
IAM-4806: Show outbound tenant IP addresses in Advanced Identity Cloud admin console. Refer to Access global settings.
-
IAM-4853: Add AS400 application template. Refer to the AS400 section in Provision an application.
Fixes
-
FRAAS-16785: Incorrect positioning of reCAPTCHA v2 elements
-
IAM-2936: Journeys hang indefinitely when using a State Metadata node within a Page node
-
IAM-4521: Screen readers announce field labels twice
-
IAM-4956: Advanced Identity Cloud admin console doesn’t use the current realm when logging out
-
IAM-5113: Unable to remove an NAO assignment from a user in Advanced Identity Cloud admin console
19 Oct 2023
Key features
- Gateway Communication node (FRAAS-17380)
-
Lets Advanced Identity Cloud authentication journeys communicate directly with the PingGateway (PingGateway).
This secure communication channel extends the Advanced Identity Cloud capabilities with PingGateway features, such as validating a Kerberos ticket and performing other certificate handshakes.
For details, refer to Gateway Communication overview.
16 Oct 2023
Key features
- New Autonomous Access capabilities[16] (DATASCI-1269)
-
Autonomous Access User access behavior and tenant access behavior let end users understand their "normal" login behavior for the past six months by graphically displaying key access metrics on a UI. Users can filter the UI to show certain login metrics, like time of day, city, country, day of week, device used for login, operating system, and browser type. Users can also compare an individual user’s login behavior to that of the access attempts for all other users.
Enhancements
-
IAM-4211: Display disaster recovery region in the Advanced Identity Cloud admin console
-
IAM-4369: Remove AM applications from application list view
-
IAM-5045: Display pop-up warning when an end user is about to be logged out of an Advanced Identity Cloud hosted page
Fixes
-
IAM-4812: Correctly save array ESVs containing newline characters
-
IAM-4863: Display ESV buttons properly when the user gives them focus
-
IAM-4877: Display ESV selection button properly while user is modifying a script associated with a Scripted Decision node
-
IAM-4698: Fix accessibility issues with messages in page nodes
13 Oct 2023
Enhancements
-
FRAAS-17373[17]: The following connectors included with Advanced Identity Cloud were upgraded from 1.5.20.15 to 1.5.20.17:
-
Adobe Marketing Cloud connector
-
Google Apps connector
-
Microsoft Graph API connector
-
Salesforce connector
-
SCIM connector
Some highlights include:
-
OPENICF-900: SCIM connector: Add support for dynamically generated SCIM schemas
-
OPENICF-2453: SCIM connector: Persist optional refresh token upon successful access token renewal
For a complete list of enhancements and fixes, refer to Connector changes.
-
Fixes
-
ANALYTICS-311: The
USER-LAST-LOGINreport doesn’t show results if the last journey failed -
FRAAS-17413: Improve IDM service reliability during upgrades and routine maintenance
-
OPENICF-1723: Salesforce connector: Clarify usage of
proxyUriconfiguration property -
OPENICF-2297: SCIM connector: Roles attribute should be a list of
Strings, not a list ofObjects -
OPENICF-2482: SCIM connector: Dynamic schema doesn’t default to static schema on all exceptions
-
OPENICF-2483: SCIM connector: Creating a user with special attributes fails with dynamically generated schema
-
OPENICF-2484: SCIM connector: PUT with
schemasattribute fails for providers that support PATCH -
OPENICF-2448: SCIM connector: HTTP client fails to handle OAuth 2.0 errors
12 Oct 2023
Key features
- OneSpan Get User Authenticator node (FRAAS-17378)
-
Retrieves the authenticators assigned to a user and helps enable user’s authentication and security levels.
For details, refer to OneSpan Get User Authenticator node.
- OneSpan Identity Verification node (FRAAS-17378)
-
Sends request to OneSpan to analyze the image and determine whether the document is genuine or fraudulent.
For details, refer to OneSpan Identity Verification node.
03 Oct 2023
Fixes
-
FRAAS-17283: Tenant status pages not automatically updated during downtime
-
IAM-4235: Passthrough authentication using AD connector fails if set up in UI and user DN includes a space
-
IAM-4903: API calls to IGA endpoints not working with custom domain
-
IAM-4915: User details modal for IGA access review shows manager details as JSON object
-
OPENIDM-19192: Personal information is still editable by end users when User Editable is set to
false
25 Sep 2023
Enhancements
-
IAM-4515[34]: Include autocomplete attribute with login form fields
-
IAM-4525[34]: Update profile picture modal with accessibility improvements for screen readers
-
IAM-4576[34]: Increase time on screen for loading spinner so that screen readers can announce it
-
IAM-4616[34]: Include contextual information with the show/hide buttons for improved accessibility
Fixes
-
FRAAS-17278: Health status reports for
AM,IDM, andplatform-adminservices incorrectly reported as available in some situations -
IAM-4460[34]: Screen readers read show/hide buttons for security questions as show/hide password
-
IAM-4523[34]: Screen readers read avatar alt text when tabbing to action menu
-
IAM-4524[34]: Two buttons with different labels open the same dialog
20 Sep 2023
Key features
- New Identity Governance capabilities[7] (IGA-1691)
-
Access requests let end users request access to resources and let managers request that access be removed from their delegates. The list of resources an end user can request access to is referred to as the access catalog.
Manage access request workflows is a new feature that lets you optionally define flows to include business logic, decisions, and approvals. For example, decide what happens when an approver rejects an access request for an application. Workflows currently only supports access request-related features.
New options in the Advanced Identity Cloud end-user UI let end users submit access requests, submit requests to remove access, and review assigned request items:
-
The My Requests option lets you view and create access requests to resources (applications, roles, entitlements) for yourself or on behalf of others.
-
The My Directory > Direct Reports option lets managers submit access removal requests.
-
The Inbox > Approvals option lists request items (requests an end user submits) for an approver (designated owner) to act on.
-
Enhancements
-
IAM-3648: ESV placeholders can now be entered from a drop-down list
-
IAM-3651: ESV placeholders can now be entered from key-value input fields
-
IAM-4236: Improve layout of the applications reconciliation tab
-
IAM-4367: Separate the connection status of OAuth 2.0 client applications into a dedicated list
-
IAM-4662: ESV placeholders can now be entered from tag input fields
-
IAM-4717: Added date, datetime, and time fields to the login UI
-
IAM-4789: Grant roles now show temporal constraints
-
OPENAM-20847: Sanitized HTML can now be added into messages for the Email Suspend node
Fixes
-
IAM-4418: Fix accessibility issues with multi-select input fields
-
IAM-4489: Align checkbox color with other form elements
-
IAM-4491: Correctly label sidebar buttons when expanded or collapsed
-
IAM-4492: Make navigation bars in end-user UI accessible for screen readers
-
IAM-4798: The
aria-labelis now correctly displayed for all component types on sidebar buttons -
IAM-4843: The user column in the certification task list now shows a user’s full name instead of only the first name
-
IAM-4528: Outbound reconciliation mapping preview shows generated password value
15 Sep 2023
Key features
- Query Parameter node (AME-24069)
-
Allows you to insert query parameter values from a journey URL into configurable node state properties. This lets you customize journeys based on the query parameter values.
For details, refer to Query Parameter node.
Enhancements
-
OPENAM-21073: Request headers are now accessible in OAuth 2.0/OIDC scripts for
OIDC_CLAIMS,OAUTH2_ACCESS_TOKEN_MODIFICATION, andOAUTH2_MAY_ACTscript contexts using therequestPropertiesbinding -
OPENAM-21355: Jakarta AWS region (ap-southeast-3) enabled for the PingAM push notification service
Fixes
-
IAM-4639: String/password field button is highlighted in the UI
-
IAM-4829: Eye icon displays over the password field highlight box in the UI
-
OPENAM-18599: Allow customization of the error message that displays to end users when their account is locked or inactive using
.withErrorMessage()in a Scripted Decision node -
OPENAM-18685: Use the OAuth2 Provider service in the AM admin console to specify if tokens issued should contain the
subnameclaim -
OPENAM-19261: Errors are incorrectly logged when triggered by introspection of tokens using OAuth 2.0 client credentials grant
-
OPENAM-20451: The WebAuthn Registration node now displays an end user’s
userNamewhen registering a device when the identity’s name isn’t human-readable -
OPENAM-21158: Add support for trusted platform module (TPM) attestation using elliptic curve cryptography (ECC) unique parameter validation starting with Windows 11 version 22H2
-
OPENAM-21304: The
request_urisfield does not populate when OAuth 2.0 clients register using dynamic client registration -
OPENAM-21390: Fix caching error to correctly provide data to
nodeStatewhen a journey switches server instances
11 Sep 2023
Enhancements
-
IAM-3650: Add a drop-down menu to checkbox inputs for selecting ESV placeholders
-
IAM-3826: Add the ability to specify a source and transformation script when mapping application properties. For details, refer to app-management:provision-an-application.adoc#apply-a-transformation-script-to-a-mapping.
-
IAM-4567: Add a warning when running reconciliations and selecting the
persistAssociationsoption. For details, refer to View a report about the last reconciliation.
Fixes
-
IAM-4366: Provide browser-specific logic to handle alternative CSS for accessibility
-
IAM-4409: Require at least three characters before running identity searches when there are more than 1000 identities of that type
-
IAM-4478: Only allow certain combinations of properties in a mapping transformation script
-
IAM-4493: Fix the heading hierarchy in the UI
-
IAM-4568: Do not enable the option to change a user association in the UI
-
IAM-4703: Fix display of password fields in some themes
-
IAM-4710: Fix rounded border of password fields in hosted pages
22 Aug 2023
Key features
- Salesforce Community User application template (IAM-4340)
-
Provision, reconcile, and synchronize Salesforce, Salesforce Portal, and Salesforce Community accounts.
For details, refer to Salesforce application template or Salesforce Community User application template
- Add preference-based provisioning to Privacy and Consent settings (IAM-4243)
-
End users in target applications can share their data with other applications. After the end user configures a preference to share data with other applications, data from the target application is synchronized with Advanced Identity Cloud.
For details, refer to End-user data sharing
18 Aug 2023
Key features
- OneSpan Auth VDP User Register node (FRAAS-15426)
-
Registers users to authenticate using the virtual one-time password (VOTP). For details, refer to OneSpan Auth VDP User Register node.
- OneSpan Auth Assign Authenticator node (FRAAS-15426)
-
Assigns VIR10 authenticator to the user when there’s a VIR10 authenticator available in the tenant and the user isn’t assigned a VIR10 authenticator. For details, refer to OneSpan Auth Assign Authenticator node.
- OneSpan Auth Generate VOTP node (FRAAS-15426)
-
Generates and delivers a virtual one-time password (VOTP) through the delivery method configured in the node if there’s a VIR10 authenticator assigned to the user. For details, refer to OneSpan Auth Generate VOTP node.
09 Aug 2023
Fixes
-
OPENAM-18004[35]: Audit logging does not specify transaction IDs correctly for internal requests to certain APIs
-
OPENAM-18709[35]: Calls to the
nodeState.get()method in Scripted Decision nodes do not return values in shared state when a variable is stored in both shared state and secure state -
OPENAM-20230[35]: Calls to classes in the allowlist fail occasionally with access prohibited messages
-
OPENAM-20682[35]: Unable to encrypt
id_tokenerror when there are multiple JWKs with the same key ID but different encryption algorithms -
OPENAM-20691[35]: Session quota reached when oldest session is not destroyed due to race condition
-
OPENAM-20783[35]: Logging is incorrect when the authorization code grant flow is used successfully
-
OPENAM-20920[35]: Null pointer exceptions when a SAML v2.0 binding is null and the SSO endpoint list contains non-SAML v2.0 entries
-
OPENAM-20953[35]: Policy evaluation with a subject type
JwtClaimreturns HTTP response code 500 -
OPENAM-20980[35]: The OIDC social provider is unable to use an issuer’s comparison check regex
-
OPENAM-21001[35]: Custom scripted SAML v2.0 IDP account mappers are determined incorrectly
-
OPENAM-21004[35]: Invalid session ID error when session management is disabled in an OIDC provider
-
OPENAM-21046[35]: The Create Object and Patch Object nodes do not log exception stack traces when they can’t retrieve the object schema
-
OPENAM-21164[35]: XML string formatted incorrectly when using a custom adapter to get the assertion from a SAML v2.0 response
31 Jul 2023
Enhancements
-
IAM-3502: Add the ability to set and reset a sync token for identity management account object type. For details, refer to Reset the last reconciliation job.
-
IAM-3678: Update error messages and labels in login and signup pages
-
IAM-3962: Improve design of push number challenge page for Push Wait node
-
IAM-4248: Add three additional non-account objects to ServiceNow page
-
IAM-4326: Improve onLink script to handle mapped properties of type array and object
-
IAM-4334: Update SuccessFactors application templates to support Advanced Identity Cloud built-in SuccessFactors connector
Fixes
-
IAM-3877: UI loader spins indefinitely when realm is deactivated
-
IAM-4093: Replace Google Fonts in the login UI to meet GDPR compliancy requirements
-
IAM-4176: Advanced setting query filter does not show all available properties
-
IAM-4240: Accessibility issues in Page node when NVDA readers are used
-
IAM-4261: Accessing end-user UI with query parameter "code" displays empty page
-
IAM-4371: Unable to create applications due to
userpasswordproperty set -
IAM-4384: Platform UI does not resume journeys with custom redirect logic
-
IAM-4427: Platform UI does not show assignments for tenants running deprecated application management
-
IAM-4475: Platform UI does not load after tenant administrator signs into an upper tenant during promotion
17 Jul 2023
Fixes
-
OPENIDM-18292[36]: Add support for the
_fieldsrequest parameter to the syncgetTargetPreviewendpoint -
OPENIDM-18898[36]: Add support for the
_countOnlyparameter in identity management scripts -
OPENIDM-18980[36]: Add a new metric to measure the duration of a LiveSync event
-
OPENIDM-19098[36]: Enable ES6 support for identity management scripts
22 Jun 2023
Enhancements
-
DATASCI-1331[37]: Distributed attack heuristics
-
DATASCI-1677[37]: Support the right to access or be forgotten (GDPR compliance)
-
IAM-2026: Support versioning of the application and connector templates
-
IAM-3408: Let provisioners use a range of connector versions
-
IAM-4074: Add a loading animation to the pie chart component
-
IAM-4242: Add "Conflicting changes" category to reconciliation summary
Fixes
-
FRAAS-9230: Sanitize
aria-hiddenfields -
FRAAS-16041: Users can choose Basic Auth for Identity Cloud logging endpoints
-
IAM-2972: Route users to the correct realm after granting Salesforce permissions
-
IAM-3719: Modals not showing display access review comments and activity
-
IAM-4116: Don’t let access review users add reviewers with greater privileges than they themselves have
-
IAM-4134: User pop-up is visible in "Entitlement" tab
-
IAM-4200: Last certified date, decision, and actor displaying incorrectly in Governance account details
14 Jun 2023
Key features
- New Identity Governance capabilities[7] (IGA-1592)
-
Entitlements are specific permissions given to an account in an onboarded target application. Each entitlement correlates to a permission. Pull in entitlements from all onboarded target applications into Advanced Identity Cloud for use in certifications.
Entitlement assignment certification, a new certification type for access reviews, lets you review and certify entitlements and the users who have access to entitlements on some or all applications. Primary reviewers are entitlement owners, a single user, or users assigned to a role.
The governance glossary lets you attach business-friendly attributes to applications, entitlements, and roles to add more specificity to the data you review in access certifications.
New options in the Advanced Identity Cloud end-user UI let you view your access, your direct reports, and the access your direct reports have:
-
The My Access option lets you view your access in Advanced Identity Cloud and onboarded target applications. This includes accounts from onboarded target applications, roles you are assigned in Advanced Identity Cloud, and entitlements or privileges you have in onboarded target applications.
-
The Direct Reports option lets you get access information for individuals you manage. This includes their profile information, accounts from onboarded target applications, roles they are assigned in Advanced Identity Cloud, and entitlements or privileges they have in onboarded target applications.
-
- Microsoft Graph API email client (OPENIDM-17899)
-
Configure the email client to use the MS Graph API Client for sending email.
For more information, refer to Microsoft Graph API email client.
Enhancements
-
IAM-2826: Filter the "Assignments" tab for identities so that it does not show overrides, entitlements, or resources
-
IAM-3677: Remove increment/decrement arrows from numeric input fields
-
IAM-3982: Let users filter risk activity using distributed attack as a risk reason
-
IAM-3983: Show distributed attack as a risk reason in the risk dashboard
-
IAM-4136: Use the tab key to move focus and remove tags in multi-select components
Fixes
-
FRAAS-14262: Include changes to group privileges in the configuration promotions report
-
IAM-2713: Prohibit editing of managed application objects
-
IAM-3594: Correctly redirect control to the End User UI after authenticating with itsme
-
IAM-3939: Let end users switch to a different authentication journey
-
IAM-4013: When using a custom domain,
originalLoginRealmis set incorrectly -
OPENIDM-17481: Managed object schema can now describe a field as a nullable array and specify a default value for this field if not provided in a create request
-
OPENIDM-17771: Processing of a large number of scheduled jobs no longer causes all scheduled tasks to continuously misfire
-
OPENIDM-18192: Updating a relationship-defined virtual property (RDVP) on a managed object by signal receipt no longer causes other RDVP state within that object to be lost
-
OPENIDM-18360: Use the full object state when validating requests made by a delegated administrator to modify a relationship
-
OPENIDM-18613: Provide the ability to remove the
userPasswordattribute -
OPENIDM-18644: Correctly determine whether it’s possible to configure clustered reconciliation
-
OPENIDM-18895: Fixes support for multi-version concurrency control on managed object patches and updates
08 Jun 2023
Key features
- Lexis-Nexis ThreatMetrix Authentication nodes (FRAAS-15325)
-
Integrate Lexis-Nexis ThreatMetrix decision tools and enable device intelligence and risk assessment in Advanced Identity Cloud.
For details, refer to ThreatMetrix Authentication nodes.
05 Jun 2023
Key features
- Filter log results
-
Use the
_queryFilterparameter to filter log results on any field or combination of fields in a payload. For details, refer to Filter log results.
30 May 2023
Key features
- Scripted SAML 2.0 SP adapter
-
Customize the SAML 2.0 SP adapter using a script.
For details, refer to SP adapter.
- OIDC ID Token Validator node
-
The new OIDC ID Token Validator node lets Advanced Identity Cloud rely on an OIDC provider’s ID token to authenticate an end user. The node evaluates whether the ID token is valid according to the OIDC specification.
For details, refer to OIDC ID Token Validator node.
Fixes
-
AME-21638: Customize an SP adapter by using a script
-
AME-24026: Allow specifying inputs required by the provider scripts in the Configuration Provider node
-
AME-24073: Expose the
prompt_values_supportedparameter of the provider configuration at the OIDC well-known endpoint -
AME-24175: Provide additional classes in the allowlist that scripts used in the Scripted Decision node
-
OPENAM-12030: Authentication node instances are deleted when journeys containing them are deleted
-
OPENAM-13293: New OIDC ID Token Validator node evaluates whether the ID token is valid according to the OIDC specification
-
OPENAM-13329: Display journeys with spaces in their name in the Authentication Configuration drop-down menu
-
OPENAM-13766: Route user session based on whether policy evaluation is requested or not
-
OPENAM-17179: Correctly delete a script if its referring journey is deleted
-
OPENAM-17566: Display account name instead of UUID in the ForgeRock Authenticator when using MFA
-
OPENAM-18488: Support certificate-based attestation in certificate chains terminating at an intermediate CA
-
OPENAM-18692: Set the minimum value for the Default Max Age property to 0
-
OPENAM-19745: Add support for EdDSA signing algorithm to WebAuthn Registration node
-
OPENAM-20082: Show correct error message to locked out users
-
OPENAM-20104: Fix the fragment response mode for the OAuth 2.0 authorize endpoint
-
OPENAM-20187: Fix the "waiting for response" page so that it fails authentication as configured in the authentication journey
-
OPENAM-20230: Prevent class allowlist from failing for classes already on the allowlist
-
OPENAM-20318: Allow a restricted set of HTML tags to be rendered in page node headers and descriptions
-
OPENAM-20360: Fix default URL encoding to ensure ampersand characters are not double encoded in a SAML assertion
-
OPENAM-20386: Fix authentication node state reconciliation in some complex journeys
-
OPENAM-20396: Preserve ordering of ACR to chain mapping configuration of OIDC provider after a restart
-
OPENAM-20451: Fix WebAuthn registration node to return a human-readable username
-
OPENAM-20457: Route Device Location Match node to "Unknown Device" outcome when the previously stored location of the device is not provided
-
OPENAM-20479: Enhance OIDC authentication to handle unsecured JWS requests
-
OPENAM-20541: Add additional inner classes to scripting allowlist to support RSA keypair generation
18 May 2023
Key features
- Administrator federation enhancements
-
Groups support: The new groups feature allows you to add and remove administrators depending on group membership in your identity provider. Using administration groups lets you automate the granting and removing of access for administrators that are being on-boarded, switching roles, or leaving your organization.
OIDC Federation: OIDC is now supported as a federation identity provider, along with Microsoft ADFS and Microsoft Azure.
For more information, refer to Configure federated access for tenant administrators.
17 May 2023
Fixes
-
FRAAS-13293: Provide more accurate and granular information in promotion reports
-
FRAAS-14063: Remove orphaned unused scripts during promotion
-
FRAAS-15022: Improve promotion reports
-
FRAAS-15188: Ensure environments can be recreated after deletion
-
IAM-2561: Allow adding applications to a user or role from the Identities > Manage page
-
IAM-3550: When attempting to validate Office 365 applications, a blank screen appears
-
IAM-3580: Improve service accounts UI including error handling
-
IAM-3666: Add alternative text to QR code image
-
IAM-3676: Add keyboard controls to UI to select multiple values in multivalued lists
-
IAM-4030: Improve handling of identity provider and groups claims
-
IAM-4031: Generic OIDC configuration returns HTTP 400 Bad Request
-
IAM-4032: Federation enforcement is missing from the UI
-
IAM-4058: Admin UI routing for locked tenants is no longer working correctly
05 May 2023
Fixes
| Issue ID[39] | Summary |
|---|---|
IAM-3043 |
CAPTCHA node not behaving properly when false |
26 Apr 2023
Key features
- PowerShell connector
-
Use the PowerShell Connector Toolkit to register a connector that can provision any Microsoft system.
For details, refer to PowerShell.
- SAP SuccessFactors Account or SAP SuccessFactors HR connector
-
Use the SAP SuccessFactors connectors to synchronize SAP SuccessFactors users with Advanced Identity Cloud users.
For details, refer to SAP SuccessFactors Account or SAP SuccessFactors HR.
- Bookmark application
-
You can now register a bookmark application - for example, OneNote, Evernote, Google Bookmarks, or raindrop.io - to direct users to specific URLs. A bookmark application displays shortcut links on dashboards. When you click one of the links, the browser opens a new tab.
For details, refer to Bookmark.
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2911 |
Add support for bookmark apps in application management |
IAM-3472 |
Update promotions UI to set tenant color dynamically based on the tenant name |
IAM-3630 |
Add SuccessFactors template and connector configuration |
IAM-3666 |
Add alt text to QR code |
IAM-3667 |
Add visual indication of keyboard focus on input fields |
IAM-3681 |
Improve accessibility of the |
IAM-3778 |
Allow login UI to work when browser session storage is unavailable |
IAM-3792 |
Prevent login UI rendering extra whitespace character in front of text on suspended nodes |
IAM-3806 |
Remove beta indicator from the trends chart in admin UI dashboard |
IAM-3840 |
Change color of radio button changed in Choice Collector node |
IAM-3879 |
Ensure global variable |
IAM-3910 |
New PowerShell configuration properties |
OPENAM-18895 |
Fix API request timeout errors for slow connections |
OPENIDM-18917 |
Display last name instead of user ID on user profile when no first name is provided |
OPENAM-20815 |
Add missing footer to Page node when session expired |
24 Apr 2023
Key features
- Microsoft Intune node
-
Integrates Microsoft Intune to control features and settings on Android, Android Enterprise, iOS/iPadOS, macOS, and Windows 10/11 devices in your organization.
For details, refer to Microsoft Intune node.
- Secret Double Octopus (SDO) nodes
-
PingOne Advanced Identity Cloud integrates with Secret Double Octopus (SDO) to provide high-assurance, passwordless authentication systems that address the diverse authentication needs of a real-world, working enterprise.
For details, refer to Secret Double Octopus (SDO) nodes.
06 Apr 2023
Key features
- Support for all Google Fonts for hosted pages
-
Meet your organization’s brand guidelines by using any Google Font in your hosted pages.
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-1686 |
Allow any Google Font to be used on hosted pages |
IAM-3164 |
Prevent table columns from stacking vertically on smaller viewports |
IAM-3313[7] |
Additional Options section missing from Identity Certification campaign template |
30 Mar 2023
Key features
- IP allowlisting
-
Enterprises often need to ensure that requests entering their network come from trusted sources. PingOne Advanced Identity Cloud now offers outbound static IP addressess for sandbox environments.
Outbound static IP addresses let you implement network security policies by setting up allowlists of IPs originating from Advanced Identity Cloud. This adds an extra layer of security to outbound calls to your APIs or SMTP servers.
For more information, refer to Outbound static IP addresses.
20 Mar 2023
Resolved issues
| Issue ID | Summary |
|---|---|
OPENIDM-18476 |
The IDM admin UI now defaults identity object number fields to |
OPENIDM-18216 |
IDM admin UI should query recon association data instead of audit data |
OPENIDM-18870 |
Inability to delete an inline reconciliation or schedule script |
OPENIDM-18868 |
Inability to save a schedule when you add or remove a passed variable |
OPENIDM-18865 |
Script changes cannot be saved unless you click outside the Inline Script box |
FRAAS-14097 |
Promotion report should identify journeys by their name |
FRAAS-13522 |
Promotion report does not include changes to custom email provider |
FRAAS-14353 |
Configuration placeholder replacement assumes a string value |
16 Mar 2023
Key features
- PingOne® Identity Governance (add-on capability)
-
PingOne Identity Governance is a new add-on capability of PingOne Advanced Identity Cloud. Identity Governance allows you to centrally administer and manage user access to applications and data across your organization to support regulatory compliance.
With Identity Governance you can:
-
Work with onboarded target applications when reviewing user data. This allows you to review user data for onboarded applications.
-
Define and launch reviews of data using certification campaigns.
-
Review and manage user access to applications. This includes managers reviewing the access their direct reports have.
For more information, refer to About Identity Governance.
To purchase an Identity Governance subscription, contact your ForgeRock representative.
-
10 Mar 2023
Key features
- Support for Scripted Groovy connector applications
-
Application management now lets you register, provision, and manage Scripted Groovy connector applications.
For details, refer to Scripted Groovy connector.
Resolved issues
| Issue ID[40] | Summary |
|---|---|
IAM-662 |
Fixed agent logout in platform UI |
IAM-3160 |
Added ability to configure the scripted Groovy connector |
IAM-3180 |
Hide the SSO tab when an application is authoritative |
IAM-3193 |
Updated SCIM app template to only show the refresh token property for OAuth authentication |
IAM-3303 |
Enable clicking a row to edit entries on the service accounts page |
IAM-3304 |
Added breadcrumbs to the service accounts page |
IAM-3305 |
Added a search field to the service accounts page |
IAM-3462 |
Corrected AD template property from |
IAM-3478 |
Addressed accessibility concerns when displaying password policy validation |
IAM-3642 |
Fixed an issue with unselected applications being imported when promoting, and improved the user experience for selecting and deselecting applications in the promotions UI |
IAM-3669 |
Fixed drop-down lists to show the value of the selected option in the form |
IAM-3694 |
Added ability to customize the success color in hosted pages |
08 Mar 2023
Key features
- Administrator federation
-
Administrator federation allows administrators to use single sign-on (SSO) to log in to an Advanced Identity Cloud tenant.
By using federation to authenticate your administrators to Advanced Identity Cloud, you can quickly and easily deprovision an administrator by removing their access from your centralized identity provider.
For details, refer to Configure federated access for tenant administrators.
06 Mar 2023
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2921 |
In the Dashboard, the total number of applications that display in the Applications box now includes those applications registered using the new app catalog in tenants created on or after January 12, 2023. |
IAM-3760 |
Apple social authentication works with other authentication methods |
03 Mar 2023
Key features
- SCIM built-in connector
-
You can now use the SCIM built-in connector to manage user and group accounts on any SCIM-compliant resource provider.
- Promotions API documentation
-
The promotions API documentation is now publicly available at https://apidocs.id.forgerock.io/#tag/Promotion.
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-8225 |
The promotions API documentation is now publicly available at https://apidocs.id.forgerock.io/#tag/Promotion |
FRAAS-8709 |
Include the log sources in the logged events |
FRAAS-12402 |
Add /platform/oauthReturn route to support authentication for Salesforce and Google Apps |
FRAAS-12413 |
OIDC login from a custom domain results in blank page |
OPENICF-400 |
The LDAP connector now correctly reads the AD Account tokenGroups attribute |
OPENICF-1858 |
Add group owners management support to the Microsoft Graph API connector |
OPENICF-2039 |
Add archived, languages, isEnrolledIn2Sv, and isEnforcedIn2Sv fields to the Google Apps connector |
OPENICF-2067 |
Adjust license assignments as part of the user creation and update operations in the Google Apps connector |
OPENICF-2068 |
The Microsoft Graph API connector now lets you assign and revoke directory roles to an Azure AD user account and query the target instance for roles |
OPENICF-2088 |
The Microsoft Graph API connector now lets you assign and revoke custom roles to an Azure AD user account and query the target instance for roles |
OPENICF-2102 |
Assign and revoke PermissionSets and Groups to Salesforce user accounts in the Salesforce connector |
OPENICF-2110 |
Expose groups and roles through user object in the ServiceNow connector |
OPENICF-2111 |
View, update, and remove a group’s roles through the role object in the ServiceNow connector |
OPENICF-2129 |
The LDAP connector now includes a parameter to use isMemberOf by ldapGroups |
OPENICF-2192 |
In the Google Apps connector, don’t throw an NPE when updating a user with a change to license assignments if _NAME_ is not specified |
OPENIDM-17876 |
Query filter editor no longer removes double quotes from all properties that aren’t of type string |
OPENIDM-17936 |
Saving changes to the authzRoles field on users no longer overrides the field type |
OPENIDM-18001 |
Country codes in locales are no longer ignored when sending emails |
OPENIDM-18077 |
Added new default policy, cannot-contain-others-case-insensitive |
OPENIDM-18153 |
Custom script exception messages are no longer incorrectly truncated in REST responses |
OPENIDM-18238 |
Improved resiliency of clustered reconciliations |
OPENIDM-18243 |
Validate that connector names are alphanumeric |
OPENIDM-18260 |
New sync mapping fields, defaultSourceFields and defaultTargetFields, let you specify which fields to use for read and query requests |
OPENIDM-18261 |
Endpoints within /system now support specifying additional fields when using wildcards |
OPENIDM-18275 |
The groups' name field is now searchable |
OPENIDM-18319 |
An up-to-date target object state is now provided in sync script bindings and sync audit mechanisms |
OPENIDM-18336 |
The default assignment object schema now contains a "condition" field |
OPENIDM-18498 |
Queued sync not triggered if target is a CREST proxy endpoint |
OPENIDM-18501 |
Tenant administrator password policy no longer restricts passwords to a maximum length |
OPENIDM-18629 |
Reconciliation job identifiers now use a more precise timestamp |
OPENIDM-18650 |
Add new SCIM connector; applications now support creating connections to SCIM services |
01 Mar 2023
| Issue ID | Summary |
|---|---|
IAM-3089[41] |
Unable to exit a social provider and select a different social provider in a journey |
22 Feb 2023
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-14069 |
Add |
FRAAS-14030 |
Add inner classes from |
FRAAS-13974 |
Add class |
FRAAS-13597 |
Remove unexpected changes from promotion reports |
14 Feb 2023
Key features
- Support for REST connector applications
-
Application management now lets you register, provision, and manage REST connector applications.
For details, refer to Scripted REST connector.
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2879 |
Allow properties in forms to be reordered |
IAM-3094 |
Add support for enumerated values in array attributes |
IAM-3156 |
Update the descriptive text in the "Add Property" modal to be more accurate |
IAM-3261 |
Adjust Autonomous Access risk filter to better handle scoring edge cases |
IAM-3262 |
Adjust menu width on the Autonomous Access Risk Administration page |
IAM-3461 |
Fix display of OAuth 2.0 applications with a UUID for a name |
IAM-3492 |
Fix objects ending in |
09 Feb 2023
Key features
- OneSpan authentication journey nodes
-
The new OneSpan authentication journey nodes integrate OneSpan Intelligent Adaptive Authentication (IAA) scoring for identity proofing, continuous authentication, and fraud protection.
For details about OneSpan authentication integration set up, refer to OneSpan.
- Jumio identity verification
-
The new Jumio identity verification integrates with Jumio’s NetVerify service to easily and securely verify identity by using facial recognition to authenticate against government issued IDs.
For details about Jumio identity verification, refer to Jumio identity verification.
- Logout for all server-side sessions for a user or set of users
-
Administrators can now invalidate (log out) all server-side sessions for a user by sending a POST request to the
json/sessionsendpoint with thelogoutByUseraction, specifying the username in the request payload. - Composite advice with an AuthLevelCondition in journeys
-
Composite advice gives AM hints about which authentication services to use when logging in a user. Journeys now take into account the AuthLevelCondition composite advice.
For example, you can now use AuthLevelCondition composite advice so that AM uses a journey that provides an authentication level of 10 or higher.
Resolved issues
| Issue ID | Summary |
|---|---|
AME-22942 |
Log out all server-side sessions for a user or set of users so that they have to reauthenticate |
FRAAS-13454 |
Integrate Jumio identity verification journey nodes |
FRAAS-13555 |
Integrate OneSpan authentication nodes |
FRAAS-13809 |
Autonomous log filters fail in connected environments |
OPENAM-11319 |
Add description key to the JSON response from OAuth2UserApplications#getResourceResponse |
OPENAM-16374 |
Add support for composite advices with a AuthLevelCondition to journeys |
OPENAM-18270 |
Don’t raise errors when calls to the access_token endpoint specify the scope parameter in OAuth2 authorization_code exchange |
OPENAM-18488 |
Handle the CA certificate correctly for Windows Hello attestations |
31 Jan 2023
Resolved issues
| Issue ID[42] | Summary |
|---|---|
FRAAS-13011 |
Security improvements |
IAM-2025 |
Add Uncategorized to the journey category filter |
IAM-3107 |
Remove bitwise filter on Active Directory page |
IAM-3108 |
Update Maintain LDAP Group Membership option to not be selected by default |
IAM-3109 |
Update cn property to be optional in Active Directory target mode |
IAM-3110 |
Update ldapGroups property to be available by default in Active Directory target mode |
IAM-3111 |
Fix password hash algorithm |
IAM-3139 |
Fix Revoke button in users and roles to revoke users, and not be clickable when there are no users to revoke |
IAM-3142 |
Fix Active Directory user filter anomaly when deleting a row |
IAM-3146 |
Update user-specific attributes to be editable by administrators |
IAM-3257 |
Fix escaping of ESV placeholders in the advanced email editor |
27 Jan 2023
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-13464 |
Adjust sandbox environment migration to not use development environment migration steps |
FRAAS-13478 |
Remove unrelated AM root realm changes from promotion reports |
FRAAS-13620 |
Improve performance of promotion report generation by removing unrelated data |
IAM-2305[42] |
Add support for localized logos in end-user UI |
IAM-3091[42] |
Fix localized headers rendering as [object Object] |
25 Jan 2023
Key features
- Improved access control for hosted pages
-
You can now block access separately for hosted end user account and journey pages:
-
Advanced Identity Cloud displays account pages after authentication for user profile and delegated administration details.
-
Advanced Identity Cloud displays journey pages during authentication for login, registration, password reset, and more.
By default, Advanced Identity Cloud hosted pages are active and accessible for accounts and journeys.
To disable access through the Advanced Identity Cloud admin console, go to Tenant Settings > Global Settings > End User UI and select the pages to disable.
-
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2735 |
SAML application improvements, including adding ability to update metadata without recreating application and adding ability to download IdP certificate from application |
IAM-3044 |
Applications list overflows when screen size is reduced |
IAM-3084 |
Only allow unique values when adding application owners |
IAM-3141 |
Add the ability to promote dynamic configuration attached to application |
IAM-3151 |
Remove redirect to global settings during administrator login |
IAM-3183 |
Let users filter the trends dashboard by date without resetting the journeys dashboard |
IAM-3339 |
After refreshing the realm settings page, set the current tab using the identifier specified in the URL fragment |
FRAAS-7542 |
Control access to hosted account and journey pages |
FRAAS-11599 |
Don’t allow changes to scripts in staging and production environments |
13 Jan 2023
Key features
- Service accounts
-
You can now use service accounts to request access tokens for most Advanced Identity Cloud REST API endpoints without relying on a particular identity in your system:
-
Call Identity Cloud APIs programmatically without needing a human identity.
-
Access AM or IDM APIs in the same way using a signed JWT.
-
Set scopes on each service account to assign only necessary permissions to access tokens.
-
Use for automation and CI/CD tooling.
For details, refer to Service accounts.
-
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-8477 |
Service accounts |
IAM-1939 |
Fix hCaptcha support in Platform UI |
IAM-2224 |
Replace bullets with checkmarks when validating password policy |
IAM-2847 |
Increase the size of the terms and conditions modal window |
IAM-2912 |
Enable promotions UI to ignore encrypted secrets |
IAM-3011 |
Update risk configuration UI to show only user-modifiable configuration |
IAM-3012 |
Add new |
IAM-3015 |
Update risk configuration evaluation UI so that updates use the new APIs |
IAM-3016 |
Fix the |
IAM-3041 |
Prevent proceeding from the Active Directory modal window without entering base DNs |
IAM-3076 |
Fix Salesforce provisioning connection |
IAM-3079 |
Fix single sign-on (SSO) setup when app name has a space |
IAM-3088 |
Enable suppression of the login failure message from the failure node |
IAM-3122 |
Fix font weight of the title text on provisioning tab |
IAM-3145 |
Fix Active Directory assignment on array attributes to be a merge and not replace |
IAM-3177 |
Add paging back to application list view if workforce feature is not enabled |
IAM-3335 |
Fixed display of localized favicon |
04 Jan 2023
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-13242 |
Improve invalid page size error message |
OPENAM-19485[43] |
Access multi-tenant social providers without requiring multiple secondary configurations |
OPENIDM-17392 |
Prevent script typos that cause services to fail from being introduced into the system |
OPENIDM-17953 |
Support email addresses that contain non-ASCII UTF-8 characters |
2022
20 Dec 2022
Key features
- BioCatch authentication nodes
-
The new BioCatch authentication nodes integrate BioCatch scoring for identity proofing, continuous authentication, and fraud protection.
For details, refer to Marketplace.
09 Dec 2022
Key features
- Event hooks
-
Event hooks let you trigger scripts during various stages of the lifecycle of users, roles, assignments, and organizations.
You can trigger scripts when one of these identity objects is created, updated, retrieved, deleted, validated, or stored in the repository. You can also trigger a script when a change to an identity object triggers an implicit synchronization operation.
Post-action scripts let you manipulate identity objects after they are created, updated, or deleted.
For details, refer to Event hooks.
07 Dec 2022
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-12494 |
Unlock the environment and stop checking progress after successfully promoting an environment |
FRAAS-12988 |
Prevent placeholder support being enabled unless a specific migration flag value is set |
OPENIDM-17556 |
Ensure RDVPs are not erased for all types of managed objects for all types of PUT operations |
06 Dec 2022
Key features
- Workforce application and connector management
-
In new tenants created on or after January 12, 2023, you can use the improved applications page to integrate Advanced Identity Cloud with external data stores or identity providers. The applications page acts as a one-stop location where you can:
-
Register and provision popular federation-capable applications quickly and easily by choosing from a library of templates, such as Salesforce and Workday.
-
Register and provision your organization’s custom applications.
-
Manage data, properties, rules, SSO, provisioning, users, and groups for an application.
-
View the connection status of each application.
-
Activate and deactivate an application.
For details, refer to Application management improvements (new tenants only).
-
- Daon IdentityX authentication nodes
-
The new Daon authentication nodes let you integrate with the Daon IdentityX platform for MFA with mobile authentication or out-of-band authentication using a separate, secure channel.
For details, refer to Marketplace.
Resolved issues
| Issue ID | Summary |
|---|---|
FRAAS-11574 |
Integrate Daon authentication journey nodes |
IAM-2658 |
Application management improvements |
DATASCI-1548 |
Update the filter text on the Autonomous Access dashboard from "All Risk Scores" to "Risk Score" |
DATASCI-1550 |
Update text on the Autonomous Access dashboard’s Copy on User Detail page |
29 Nov 2022
Key features
- Onfido authentication nodes
-
The new Onfido authentication nodes let you use Onfido’s solution for collecting and sending document identification and, optionally, biometrics to the Onfido backend for verification.
For details, refer to Marketplace.
23 Nov 2022
Resolved issues
| Issue ID | Summary |
|---|---|
IAM-2354 |
Add system notification capability to UI |
IAM-2355 |
Self-service promotions migration UI |
IAM-2465 |
Password policy to force password expiry not working |
IAM-2706 |
Embedding images in the theme editor only displays alternative text |
IAM-2739 |
Email suspend message displayed without line breaks |
IAM-2939 |
Add translation configuration key for "Passwords do not match" message |
IAM-2973 |
Self-service promotions migration UI flow should enable promotions UI features |
08 Nov 2022
Key features
- Group management
-
You can now create and manage groups that are shared across AM and IDM within your Advanced Identity Cloud instance. New tenants have group management enabled by default, and existing tenants can follow an upgrade path to enable it.
For more information, refer to Group management.
02 Nov 2022
Key features
- ID Cloud Analytics Dashboard enhancements
-
You can now take advantage of the following enhancements to the analytics dashboard:
-
The journey chart now lets users drill down at specific points on a trend line to view individual journey outcomes for that date/hour. Journeys are sorted by a ranking of percentage failures, but can also be sorted based on number ranking.
-
Two new widgets — Top Five Journeys by Outcome and Top Five Journeys by Usage — that rank trending journeys based on outcomes and usages are now available.
For more information, refer to Advanced Identity Cloud analytics dashboard.
-
25 Oct 2022
Key features
- Self-service promotions
-
Self-service promotions let you promote configuration between environments without raising a support ticket. You can perform self-service promotions from development to staging tenant environments, and from staging to production tenant environments. You cannot promote sandbox environments.
For more information, refer to Introduction to self-service promotions.
- Configuration placeholders visible in all APIs
-
Configuration placeholders let you set ESVs in your configuration.
For more information, refer to Manage configuration placeholders using the API.
19 Oct 2022
Key features
- Duo authentication node
-
The new Duo authentication node lets you use Duo’s solution for adaptive authentication, bring your own device security, cloud security, endpoint security, mobile security, and two-factor authentication.
- Twilio authentication node
-
The new Twilio authentication node allows you to use Twilio for two-factor authentication during account setup, sign-on, and other scenarios. The node lets you integrate Twilio’s APIs to build solutions for SMS and WhatsApp messaging, voice, video, and email. The node uses Twilio’s latest Lookup API, which uses real-time risk signals to detect fraud and trigger step-up authentication when needed.
For details, refer to Marketplace.
Resolved issues
| Issue ID | Summary |
|---|---|
ANALYTICS-52 |
Correct the value in the All Journeys field |
DATASCI-1437 |
Correct prefilled username fields in Filters window |
DATASCI-1474 |
Don’t show explainability if not specified in response after applying Unusual Day of Week filter |
DATASCI-1497 |
Let users see previously selected risk reasons after closing the Filter window |
DATASCI-1504 |
Prevent the truncation of text on the right side of pages |
FRAAS-11570 |
Add Duo authentication node |
FRAAS-11571 |
Add Twilio authentication node |
FRAAS-11825 |
Add translation configuration key for no search results message |
FRAAS-12301 |
Add Marketplace nodes to journey editor menu |
FRAAS-12413 |
Remove blank page shown when user returns to login page following successful login to custom domain |
IAM-1935 |
Expose ESV variable type in the UI |
IAM-2038 |
Prevent theme styles rendering in the hosted pages editor |
IAM-2066 |
Show the entire answer to a long security question after clicking the visibility icon |
IAM-2259 |
Do not let users save email templates that contain JavaScript |
IAM-2312 |
Render SVG images correctly |
IAM-2411 |
ForgeRock favicon displays briefly before the customer’s favicon |
IAM-2502 |
Remove flashing red text from security questions window |
IAM-2633 |
Support localization for radio display fields in Choice Collector node |
IAM-2696 |
Remove legend from Risk Score window |
IAM-2869 |
Update UI regex validation for ESV list type |
22 Sep 2022
Resolved issues
| Issue ID | Summary |
|---|---|
AME-22684 |
Include grace period configuration in the OAuth2 provider settings |
OPENAM-18112 |
Provide better error message when an LDAP authentication node encounters a TLS connection issue |
OPENAM-19196 |
Do not wait for cache timeout before OAuth2 clients reflect changes to Javascript origins |
OPENIDM-16420 |
Update the default email validation policy to conform with RFC 5322 |
OPENIDM-17533 |
Allow configuration changes to the repo.ds.json file to take effect without restarting IDM |
OPENIDM-17720 |
Fix null pointer exception when the repo.ds.json file is misconfigured |
OPENIDM-17836 |
Fix for startup error message caused by ObjectMapping constructor exception |
OPENIDM-17911 |
Fix email validation errors in the IDM admin UI (native console) |
20 Sep 2022
Resolved issues
| Issue ID | Summary |
|---|---|
DATASCI-1165 |
Remove Automated User Agent from the list of risk reasons filters |
DATASCI-1358 |
Let users filter dashboards by date, risk scores and features |
DATASCI-1365 |
Update the Risk Activity page when applying a filter without requiring users to refresh the page |
DATASCI-1394 |
Show the times that events occurred correctly without requiring users to refresh the display |
DATASCI-1395 |
Let users see their last five risky authentication attempts |
DATASCI-1397 |
Remove risk administration options from end users' navigation menus |
DATASCI-1406 |
When filtering activities using a date range, include the activities that occur on the end date |
IAM-1678 |
Allow login journey attributes that are not required to have empty values |
IAM-1682 |
When editing email templates, cut text correctly |
IAM-1932 |
When placeholders are used, display read-only strings in the Platform UI |
IAM-2028 |
Remove excess space from journey editor fields that do not require floating labels |
IAM-2064 |
Replace fields for specifying numeric thresholds with a risk score definition slider in Autonomous Access Decision nodes |
IAM-2080 |
Let users create customized footers on Page nodes |
IAM-2141 |
Add option to customize Page node background color |
IAM-2142 |
Add option to customize Page node button width |
IAM-2143 |
Add option to customize label text for Page node fields |
IAM-2227 |
Remove spurious "No configuration exists for id external.email" pop-up warning |
IAM-2249 |
Add option to display Message node as a link |
IAM-2250 |
After importing journeys, let user delete all imported journeys with a single delete action |
IAM-2251 |
Provide a value when the object.password variable is specified in an email template |
IAM-2258 |
Remove tenant information from the Realm menu |
IAM-2285 |
Make H2, H3, and H4 HTML headings bigger when there’s no higher-level predecessor heading |
IAM-2290 |
Show the correct number of events per country on the Activity Risk dashboard |
IAM-2294 |
Show previous authentication attempts when doing anomaly lookups |
IAM-2320 |
Change the default navigation background color of Account pages without changing the dashboard color |
IAM-2329 |
Change the color of the Autonomous Access event log indicator to red |
IAM-2351 |
Correct pagination on the Autonomous Access Risk page |
IAM-2373 |
Make dashboard analytics pipeline logs in Autonomous Access work as expected |
IAM-2468 |
Wrap long security questions |
IAM-2521 |
Don’t reuse authId during password validation |
OPENAM-18933 |
Do not override the Success URL node’s value |
SDKS-1720 |
Point developers to the ForgeRock SDKs when they create an OAuth2.0 client in the Platform UI |
SDKS-1721 |
Point developers to the ForgeRock SDKs when they configure CORS in the Platform UI |
Rapid channel features
This page links to early access documentation for features available in the rapid channel and not in the regular channel. As these features become available in the regular channel, we update the links to refer to the main body of the PingOne Advanced Identity Cloud documentation.
| These topics are draft documentation and subject to change. |
Google Chrome Device Trust node
Use the Google Chrome Device Trust node to establish device trust with Chrome Enterprise.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the challengeresponse property from the journey state.
This property is populated by a Scripted Decision node that retrieves the
value from PingGateway.
Dependencies
This node requires:
Set up PingGateway
-
Install PingGateway as indicated in the Quick Install Guide.
-
Configure the
admin.jsonfile to run PingGateway on ports 9090 / 9443. Learn more about starting up PingGateway with custom settings.If 9443 is for HTTPS, then readers need to configure PingGateway for server-side HTTPS. Learn more in Configure PingGateway for TLS.
-
Download the generate_challenge.json and challengeresponse.json JSON route files.
-
Store the two JSON route files in your
routesdirectory, for example:-
$HOME/.openig/config/routes (on Mac or Linx) or
-
%appdata%\OpenIG\config\routes (on Windows).
-
-
Download and store the getChallenge.groovy Groovy script file in your
groovydirectory, for example:-
$HOME/.openig/scripts/groovy (on Mac or Linux), or
-
%appdata%\OpenIG\scripts\groovy (on Windows).
If you do not have the
groovydirectory, create one.
-
About PingGateway routes
The generate_challenge.json route executes the getChallenge.groovy Groovy
script to perform the following tasks:
-
Make an
HTTP POSTrequest to the Google Chrome Verified Access API to generate the challenge. -
Get the challenge from the API response.
-
Set the challenge as the value of the x-verified-access-challenge custom HTTP response header.
Google Chrome recognizes the custom HTTP response header and uses the challenge value to calculate a challenge-response.
-
Finally, Google Chrome creates a new custom HTTP request header, x-verified-access-challenge, and sets the challenge-response as the header value.
The generate_challenge.json route redirects the user to the challengeresponse.json route to perform these tasks:
-
Get the challenge-response from the request headers.
-
Set the challenge-response value in the query parameter of the redirect URL as the
challengeresponsekey. -
Redirect back to Advanced Identity Cloud.
Set up Scripted Decision node
This node requires a
Scripted Decision node earlier in the
journey to redirect the end user to PingGateway to generate and retrieve the
challengeresponse.
-
Configure a Script Decision node. The following is an example script used in the Script Decision node.
Example Script Decision Node redirect script.
try { var redirectMethod = "GET"; var redirectUrl = "https://ig.example.com:9443/pinggateway-route-name"; if (!requestParameters.get("challengeresponse")) { callbacksBuilder.redirectCallback(redirectUrl, {}, redirectMethod, true); } else { var challenge = requestParameters.get("challengeresponse"); nodeState.putShared("x-verified-access-challenge", challenge); action.goTo("true"); } } catch (error) { nodeState.putShared("errorMessage", error.toString()); action.goTo('false').withErrorMessage(error); }-
The above script uses the Next Generation Script Engine.
-
The
challengeresponseparameter must be in the redirect to Advanced Identity Cloud as a query parameter from PingGateway. -
The Google Chrome Device Trust node retrieves the
challengeresponsevalue from the request parameters.
-
Configuration
| Property | Usage |
|---|---|
API Key |
The Google Cloud API key. |
Private Key |
Google Cloud administrator credential’s private key. |
Key ID |
The credential used to verify the authenticity and integrity of the JWT. |
Credentials Client Email |
The email ID of the client with Google Cloud administrator credentials. |
Outcomes
Continue-
Successfully authenticated the user.
Error-
The journey follows this outcome path if the node is unable to obtain the device trust signals.
Troubleshooting
If this node logged an error, review the log messages for the transaction to find the reason for the exception. Review the GCP configuration for the Chrome Enterprise Device Trust node and contact Google Support for further information.
Example
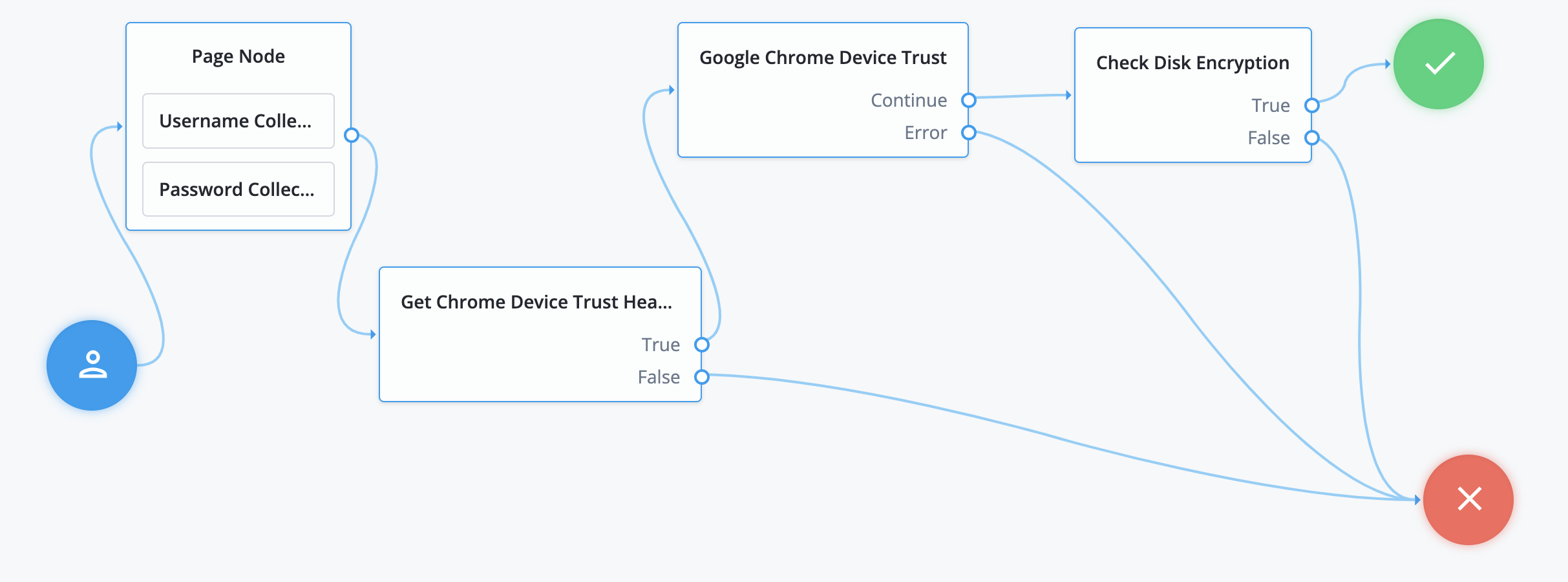
The example journey shows the following:
-
A user logs in.
-
The Chrome Device Trust Headers node, a Scripted Decision node, redirects to PingGateway to handle the Google Chrome challenge-response process.
-
PingGateway generates the challenge, retrieves the challenge response, and sets it as a request parameter before redirecting back to the journey.
-
The Google Chrome Device Trust node uses the challenge response to retrieve Chrome Device Trust signals, storing them in transient state.
-
The Check Disk Encryption node, another Scripted Decision node, determines if the
diskEncryptionsignal is disabled or enabled and makes an informed access decision.The sample script used in this node.
var diskEncrypted = nodeState.get("deviceSignals").get("diskEncryption"); if(diskEncrypted === "DISK_ENCRYPTION_DISABLED") { outcome = "true" } else { outcome = "false" }
CLEAR ID Verification node
Use the CLEAR ID Verification node to integrate CLEAR verification in your authentication journey.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Dependencies
To use this node, you must have access to a CLEAR Verified tenant. Learn more about setting up a CLEAR tenant.
Configuration
| Property | Usage |
|---|---|
CLEAR API Key |
Environment API Key for CLEAR. |
CLEAR Project ID |
Google Cloud administrator’s private key. |
Key ID |
The tenant ID for the CLEAR project used for integration. |
Redirect URL |
The target URL for redirection after verification. |
Use Secure Endpoint |
If this toggle is enabled, the node uses the secure endpoint to retrieve user verification results; otherwise, the node uses the standard endpoint. |
Outputs
The ID Verification results are stored in the verificationResults shared
state attribute. An example of data is provided
here.
Outcomes
Continue-
Successfully authenticated the user.
Error-
An error message is output to the shared state.
Troubleshooting
If this node logged an error, review the log messages for the transaction and contact CLEAR support for further troubleshooting.
Example
The example journey shows the following:
-
The journey starts with user registration.
-
CLEAR ID Verification node verifies the user credentials.
-
The Scripted Decision node is a scripted decision node extracts the document number from the CLEAR verification response stored in shared state and stores it on the user object.

Redirect an OAuth 2.0 or OIDC client application to a journey
You can configure OAuth 2.0 / OIDC client applications to redirect authentication requests to a specified journey.
The redirect contains a transaction condition advice to ensure the journey always runs,
regardless of existing sessions and configured authentication context class reference (acr) values.
You can only associate a journey with OAuth 2.0 applications configured for the Authorization Code, Implicit, and Device Code grant types.
When a journey is associated with an application, it overrides other authentication settings, including acr claims.
If a relying party (RP) requests an acr claim (voluntary or essential) or
if default acr values are set in the OIDC client profile, the claim is returned in the ID token
regardless of the provider configuration.
|
You can’t delete a journey if it’s referenced by an OAuth 2.0 / OIDC application. |
Configure a client application journey
-
Under Native Consoles > Access Management, go to Realms > Realm Name > Applications > OAuth 2.0 > Clients > Client ID.
-
On the Advanced tab, select the journey from the Tree Name list.
-
Save your changes.
-
To verify that Advanced Identity Cloud uses the associated journey for authentication, check the log messages written to the am-access and am-authentication log files.
|
You can use a script to access information about the incoming OAuth 2.0 request. Configure your journey to include a Scripted Decision node that queries the oauthApplication script binding. |
Perform low-level cryptographic operations in next-generation scripts
Use the next-generation utils binding to perform functions such as encoding/decoding
and encryption/decryption, type conversion, and cryptographic operations.
The utils binding isn’t available in legacy scripts.
|
Base64 encode and decode
- String base64.encode(String toEncode)
-
Encodes the specified text using base64.
- String base64.encode(byte[] toEncode)
-
Encodes the specified bytes using base64.
- String base64.decode(String toDecode)
-
Decodes the specified text using base64.
- byte[] base64.decodeToBytes(String toDecode)
-
Decodes the specified text using base64 and returns the result as an array of bytes.
- Example
var encoded = utils.base64.encode("exampletext")
logger.debug("Encoded text: " + encoded); //ZXhhbXBsZXRleHQ=
var decoded = utils.base64.decode(encoded);
logger.debug("Decoded text: " + decoded);Base64Url encode and decode
- String base64url.encode(String toEncode)
-
Encodes the specified text using base64url.
- String base64url.decode(String toDecode)
-
Decodes the specified text using base64url.
- Example
var encodedURL = utils.base64url.encode("http://exampletext=")
logger.debug("Encoded URL: " + encodedURL); //aHR0cDovL2V4YW1wbGV0ZXh0PQ
var decodedURL = utils.base64url.decode(encodedURL);
logger.debug("Decoded URL: " + decodedURL);Generate random values
- String crypto.randomUUID()
-
Returns a type 4 pseudo-random generated UUID.
- <JavaScript array> crypto.getRandomValues(<JavaScript array> array)
-
Returns the specified array filled with the same number of generated random numbers.
- Example
// generate a pseudorandom UUID (version 4)
var uuid = utils.crypto.randomUUID();
logger.debug("UUID: " + uuid); //eef5b4e1-ae86-4c0a-9160-5afee2b5e791
// generate an array of 5 random values
var array = [0,0,0,0,0];
utils.crypto.getRandomValues(array);
array.forEach(function(element){
logger.debug("Random value: " + element);
});Convert types
- String types.bytesToString(byte[] toConvert)
-
Converts a byte array to a string.
- byte[] types.stringToBytes(String toConvert)
-
Converts a string to a byte array.
- Example
var dataBytes = utils.types.stringToBytes("data");
var dataString = utils.types.bytesToString(dataBytes);Generate keys
- Object crypto.subtle.generateKey(String algorithm)
-
Generates a key using the specified algorithm and default values.
- Object crypto.subtle.generateKey(Map<String, Object> algorithm)
-
Generates a key using the parameters provided, depending on the algorithm specified.
- Parameters
| Option | Algorithm | Description |
|---|---|---|
|
All |
Required. The name of the algorithm. Possible values: |
|
|
Optional. Default: |
|
|
Optional. Default: |
|
|
Optional. Possible values: |
- Example
var aesKey = utils.crypto.subtle.generateKey("AES");
// Optionally specify 'length' (default 256)
var aesKeyCustom = utils.crypto.subtle.generateKey(
{
"name": "AES", length: 256
}
);
var rsaKey = utils.crypto.subtle.generateKey("RSA");
// Optionally specify 'modulusLength' (default 2048)
var rsaKeyCustom = utils.crypto.subtle.generateKey(
{
"name": "RSA", modulusLength: 4096
}
);
var hmacKey = utils.crypto.subtle.generateKey("HMAC");
// Optionally specify 'hash' (default 'SHA-256')
var hmacKeyCustom = utils.crypto.subtle.generateKey(
{
"name": "HMAC", "hash": "SHA-256"
}
);
logger.debug("AES key: " + aesKey.length);
logger.debug("RSA keys: " + rsaKey.publicKey.length + " : " + rsaKey.privateKey.length);Encrypt and decrypt
- byte[] crypto.subtle.encrypt(String algorithm, byte[] key, byte[] data)
-
Encrypts the data using the specified key and algorithm (
AESorRSA).
- byte[] crypto.subtle.decrypt(String algorithm, byte[] key, byte[] data)
-
Decrypts the data using the specified key and algorithm (
AESorRSA).
- Example
var data = utils.types.stringToBytes("data");
var aesKey = utils.crypto.subtle.generateKey("AES");
var rsaKey = utils.crypto.subtle.generateKey("RSA");
var encryptedAes = utils.crypto.subtle.encrypt("AES", aesKey, data);
var decryptedAes = utils.crypto.subtle.decrypt("AES", aesKey, encryptedAes);
var encryptedRsa = utils.crypto.subtle.encrypt("RSA", rsaKey.publicKey, data);
var decryptedRsa = utils.crypto.subtle.decrypt("RSA", rsaKey.privateKey, encryptedRsa);
logger.debug("decryptedAes: " + decryptedAes + " decryptedRsa: " + decryptedRsa);Compute digest (hash) values
- String crypto.subtle.digest(String algorithm, byte[] data)
-
Returns the digest of the data using the specified algorithm. The algorithm must be one of
SHA-1,SHA-256,SHA-384,SHA-512. - Example
var data = utils.types.stringToBytes("data");
var digest = utils.crypto.subtle.digest("SHA-256", data);
logger.debug("Digest length: " + digest.length);Sign and verify
- byte[] sign(String algorithm, byte[] key, byte[] data)
-
Signs the data using the specified algorithm and key.
- byte[] sign(Map<String, Object> algorithmOptions, byte[] key, byte[] data)
-
Signs the data using the specified algorithm options and key.
- boolean verify(String algorithm, byte[] key, byte[] data, byte[] signature)
-
Verifies the signature of the data using the specified algorithm and key.
- boolean verify(Map<String, Object> algorithmOptions, byte[] key, byte[] data, byte[] signature)
-
Verifies the signature of the data using the specified key and map of parameters.
- Parameters
| Option | Algorithm | Description |
|---|---|---|
|
All |
Required. The name of the algorithm. Possible values: |
|
|
Optional. Possible values: |
- Example
var data = utils.types.stringToBytes("data");
var rsaKey = utils.crypto.subtle.generateKey("RSA");
var hmacKey = utils.crypto.subtle.generateKey("HMAC");
var signRsa = utils.crypto.subtle.sign("RSA", rsaKey.privateKey, data);
var verifyRsa = utils.crypto.subtle.verify("RSA", rsaKey.publicKey, data, signRsa);
var hmacOpts = {
"name": "HMAC",
"hash": "SHA-512"
}
var signHmac = utils.crypto.subtle.sign(hmacOpts, hmacKey, data);
var verifyHmac = utils.crypto.subtle.verify(hmacOpts, hmacKey, data, signHmac);
logger.debug("RSA key verified: " + verifyRsa);
logger.debug("HMAC key verified: " + verifyHmac);Manage entitlement lifecycle management
Entitlement lifecycle management (LCM) provides a form of delegated administration, allowing application owners, entitlement owners, and end users with the scope permissions to manage entitlements in the applications available to them.
A key capability of Entitlement LCM is metadata management. Users need clear and accurate entitlement information when making requests or assigning permissions. Entitlement LCM enables organizations to maintain up-to-date entitlement attributes, preventing outdated or stale metadata from affecting decision-making.
Entitlement LCM also enforces policies by requiring approvals before entitlement changes take effect. This prevents users from granting excessive permissions without oversight, ensuring that access rights align with organizational policies.
Enable Entitlement LCM
Tenant administrators must enable Entitlement LCM to activate the feature for their end users:
-
In the Advanced Identity Cloud admin console, go to Governance > Requests.
-
On the Requests page, click the Settings tab.
-
In the Governance LCM section, click Activate.
-
In the Governance LCM modal, read what activating this feature entails, and click Next.
-
In the Governance LCM modal, click Entitlement LCM, and then click Activate. The governance LCM is now active on your tenant.

Adds scopes
Scopes provide the permissions to let end users to take action only on applications and entitlements to which they are permitted. Tenant or governance administrators assign these scopes to end users.
For example, when you assign a scope for an application with the Create Entitlements permission,
the end user can create entitlements for the application in that scope.
However, this doesn’t mean they can view entitlements. For that, they must have the View Entitlements permission.
The following rules apply to scope permission:
-
If end users have scope permissions for view entitlements, they can view those entitlements regardless of the application permissions.
-
If end users have modify permissions, they can modify the entitlements they can see.
-
If end users have view grant permissions, they can view the users of the entitlements you can see.
To add scopes:
-
Sign on to the Advanced Identity Cloud admin console as a tenant administrator.
-
In the Advanced Identity Cloud admin console, go to Governance > Scopes.
-
Click New Scopes.
-
On the New Scope page, enter the following in the Details section:
-
Name: Enter the name for the scope.
-
Description: Enter a description for the scope.
-
Click Next.

-
-
On the Applies to page, define which users should be subject to this scope. Decide if you want to grant application or entitlement permissions to the end user.
-
Select if the All or Any condition must be met.
-
Select a property for this scoping rule. For example, select userName.
-
Select an operator for the scoping rule. For example, select contains.
-
Enter an entitlement.
-
If you want to add another rule, click and repeat the steps.
-
Click Next.

-
-
On the Access page, enter the following depending if you are granting applications or entitlement permissions:
-
For application permissions:
-
Select the Applications checkbox.
-
Click All Applications or Applications matching a filter. Click Applications matching a filter.
-
Select if All or Any condition must be met.
-
Select a property for this scoping rule. For example, select name.
-
Select an operator for the scoping rule. For example, select is.
-
Enter an application.
-
If you want to add another rule, click and repeat the steps.
-
Click Create Entitlements.
The View Applications scope permission is also included.
-
Click Save.
The end user now has the permission to create new entitlements for the matching application.

-
-
For entitlement permissions:
-
Select the Entitlements checkbox.
-
If you click Applications matching a filter, click All Entitlements or Entitlements matching a filter.
-
Select if the All or Any condition must be met.
-
Select a property for this scoping rule. For example, select userName.
-
Select an operator for the scoping rule. For example, select is.
-
Enter a user.
-
If you want to add another rule, click and repeat the steps.
-
Click Modify Entitlements.
The View Entitlements scope permission is also included.
-
Click View Grants to allow the end user to view who has the entitlement.
-
Click Save.

-
-
Application tasks
End users with application permissions on entitlements can only work with entitlements specific to the application. They can:
View entitlements in an application
-
In the Advanced Identity Cloud end-user UI, sign on as your test application owner:
veronica.achorn. -
Go to Administer > Entitlements. All entitlements specific to the selected application are displayed.

-
From here, the end user can do:
-
View all entitlements specific to the application.
-
View the details, object properties, and users of a specific entitlement.
-
Create an entitlement.
-
Modify an entitlement.
-
Add a new entitlement to an application
-
In the Advanced Identity Cloud end-user UI, sign on as your test user who has application permissions.
-
Go to Administer > Entitlement. The application’s entitlements are accessible to the end user.
-
On the Entitlements page, click New Entitlement.
-
In the New Entitlement modal:
-
Click Application and click the application available to the test user. You should see only one available option.
-
Click Object Type and select an object type for the new entitlement.
-
Click Next.
-
-
In the Entitlement Details modal:
-
Enter or select the fields required for your entitlement. Fields can differ based on how you configured your glossary items. For example:
-
Description: Enter a general description of the entitlement.
-
Entitlement Owner: Type a user to add as an entitlement owner.
-
Entitlement Type: Enter the type of entitlement.
-
Parent Entitlement: Enter any parent entitlement if any.
-
Requestable: Click to make the entitlement requestable.
-
-
Click Submit.
The new entitlement appears in the list of entitlements specific to the application.
-
Modify entitlement details in an application
-
In the Advanced Identity Cloud end-user UI, sign on as your test user who has application permissions.
-
Go to Administer > Entitlements. The application’s entitlements are accessible to the end user.
-
Click an entitlement.
-
Modify any field including Entitlement Owner and click Save.
A change request is entered in the system and must be approved by the user specified in the workflow. For example: the Modify Entitlement workflow specifies that the entitlement approves any entitlement change requests.

End user tasks
After administrators grant end users the required scope permissions to view and act on any applications and entitlements, the end users can take action on the permitted entitlements.
End user UI
-
In the Advanced Identity Cloud end-user UI, sign on as your test end user:
Abby Dabby. -
Go to Administer > Entitlements. The entitlement is accessible to the end user.

-
From here, the end user can do the following depending on their scope permissions:
-
View the entitlement details.
-
View users who have the entitlement.
-
Modify the entitlement: If the end user makes a change to the entitlement, Identity Governance generates a request that awaits review and approval by the designated approver. Tenant administrators can designate the approver within the Modify Entitlement workflow.
-