Authentication node reference
Basic nodes
Data Store Decision node
The Data Store Decision node checks that the credentials provided during authentication match the ones stored in the configured data store for the realm.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the realm, username, and password properties in the incoming node state.
You can implement the following nodes as inputs to the Data Store Decision node:
Dependencies
The Data Store Decision node is a basic node used in many authentication application types, such as basic, push, OAuth 2.0, and social provider authentication applications.
Outcomes
Returns a boolean outcome:
True-
The credentials match those found in the data store.
False-
The credentials do not match those found in the data store.
Errors
The following Data Store Decision node warnings and errors can appear in the logs:
- Warnings
-
-
"invalid password error"
-
"invalid username error"
-
- Errors
-
-
"Exception in data store decision node"
-
Examples
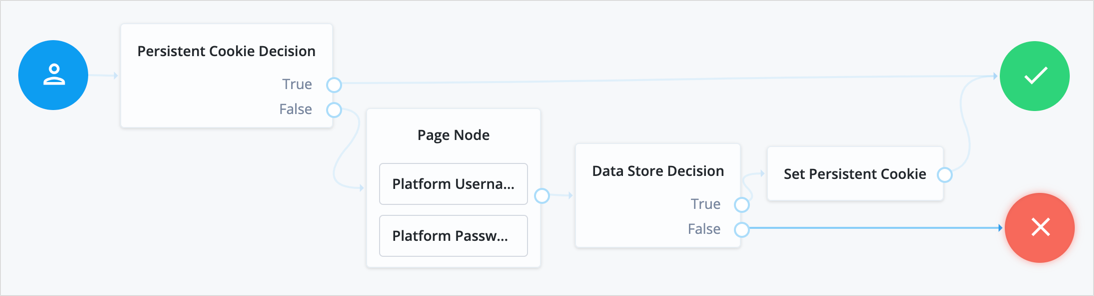
Example 1: Simple username and password collector nodes with Data Store Decision node
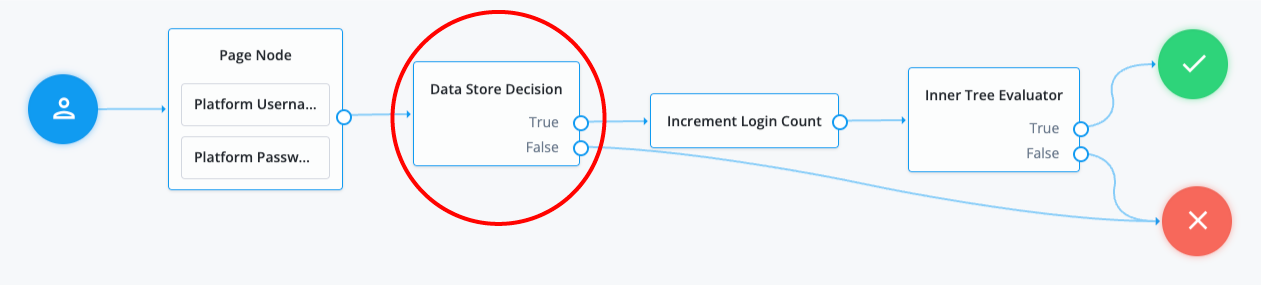
This example illustrates a simple login process. The journey involves a Page node that contains two embedded nodes: Platform Username node and Platform Password node. To enhance user experience, the Page node lets users input their username and password on a single page, instead of splitting them across two different pages.
The Data Store Decision node has two outcomes: True or False.
When the outcome is True, it triggers a Login Count Decision node.
The Increment Login Count node then moves to an Inner Tree Evaluator node, which performs additional login processes.
The False outcome connects directly to a failure node,
indicating a failed state where the username and/or password provided by the user did not match the information stored
in the data store.
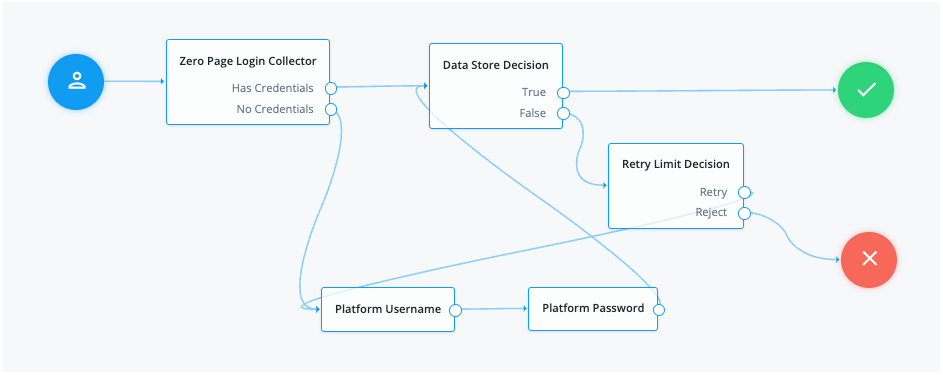
Example 2: Grant the user several attempts to enter their credentials correctly
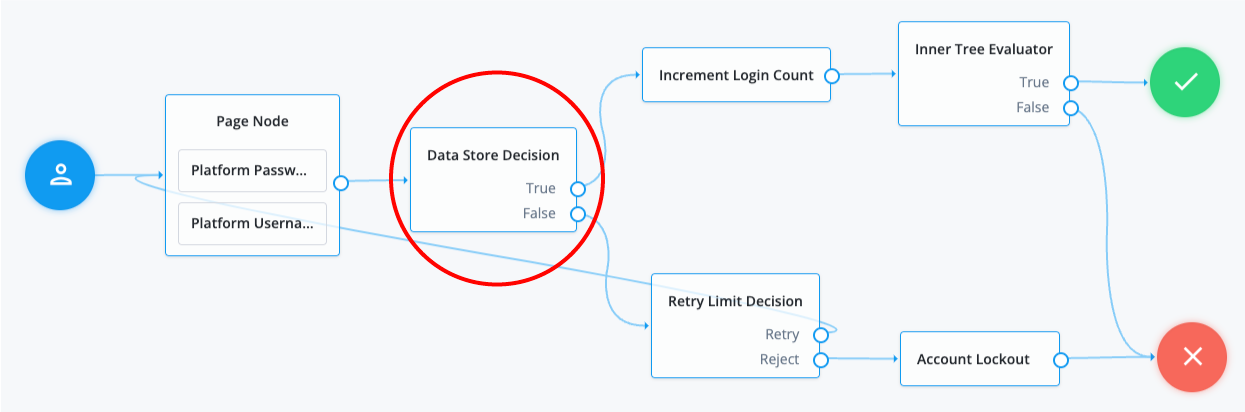
In the following example, when an authentication attempt fails at the Data Store Decision node, you can direct it to a Retry Limit Decision node. The Retry Limit Decision node determines the number of retries allowed and either retries the login attempt or rejects it. If the journey rejects the login attempt after reaching the configured limit, for example three attempts, the operation results in an account lockout.
Additional information
The following are alternate nodes that you can use in your journeys depending on your specific use cases:
-
The LDAP Decision node supports LDAP Behera Password Policies with separate outcomes for accounts that are locked and passwords that have expired.
-
In Advanced Identity Cloud applications, the Identity Store Decision node is an enhanced node with additional outcomes. Use this node if your authentication journey needs more functionality than a simple
TrueorFalseoutcome.
LDAP Decision node
The LDAP Decision node verifies that the provided username and password exist in the specified LDAP user data store. The node also checks whether the associated user account has expired or is locked out.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
The node reads the username and password fields from the node state.
The journey can provide these credentials in a number of ways, for example, with a combination of the Platform Username node and Platform Password node, or by using the Zero Page Login Collector node.
Configuration
| Property | Usage | ||
|---|---|---|---|
Primary LDAP Server (required) |
Specify one or more primary directory servers.
Specify each directory server in the following format: For example, |
||
Secondary LDAP Server |
Specify one or more secondary directory servers.
Specify each directory server in the following format: The journey uses the secondary servers when none of the primary servers are available. For example, |
||
DN to Start User Search (required) |
Specify the DN from which to start the user search.
More specific DNs, such as If multiple entries with the same attribute values exist in the directory server, make sure this property is specific enough to return only one entry. |
||
Bind User DN, Bind User Password |
The credentials used to connect to the LDAP user data store. |
||
Attribute Used to Retrieve User Profile (required) |
The attribute used to retrieve a user profile from the directory server. The user search will have already happened, as specified by the Attributes Used to Search for a User to be Authenticated and User Search Filter properties. |
||
Attributes Used to Search for a User to be Authenticated (required) |
The attributes the node uses to match the credentials provided by the user to an entry in the directory server. For example, a value of Multiple attribute values let the user authenticate with any one of the values.
For example, if you set both
|
||
User Search Filter |
A filter to append to user searches. For example, if your search attribute is |
||
Search Scope |
The extent of the search for users in the directory server:
Default: |
||
LDAP Connection Mode |
Specifies whether to use SSL or StartTLS to connect to the directory server. The node must be able to trust the certificates used. Possible values: Default: |
||
mTLS Enabled |
Enables mTLS (mutual TLS) between AM and the directory server. This setting applies to all configured LDAP servers; that is, AM uses mTLS to authenticate to all LDAP servers configured for this node. When mTLS is enabled, AM ignores the values for Bind User DN and Bind User Password. If you enable this property, you must:
Default: Disabled |
||
mTLS Secret Label Identifier |
Identifier used to create a secret label for mapping to the mTLS certificate in the secret store.
AM uses this identifier to create a specific secret label for this node. The secret label takes the form
For more security, you should rotate certificates periodically. When you rotate a certificate, update the corresponding mapping in the realm secret store configuration to reflect this label. When you rotate a certificate, AM closes any existing connections using the old certificate. A new connection is selected from the connection pool and no server restart is required. |
||
Return User DN to DataStore |
When enabled, the node returns the DN rather than the User ID.
From the DN value, AM uses the RDN to search for the user profile.
For example, if a returned DN value is Default: Enabled |
||
User Creation Attributes |
This list lets you map (external) attribute names from the LDAP directory server to (internal) attribute names used by AM. |
||
Minimum Password Length |
The minimum acceptable password length. Default: |
||
LDAP Behera Password Policy Support |
When enabled, support interoperability with servers that implement the Internet-Draft, Password Policy for LDAP Directories. Default: Enabled |
||
Trust All Server Certificates |
When enabled, the server blindly trusts server certificates, including self-signed test certificates. Default: Disabled |
||
LDAP Connection Heartbeat Interval |
Specifies how often AM should send a heartbeat request to the directory server to ensure that the connection doesn’t remain idle. Some network administrators configure firewalls and load balancers to drop connections that are idle for too long.
Set the units for the interval in the
Default: |
||
LDAP Connection Heartbeat Time Unit |
The time unit for the Default: |
||
LDAP Operations Timeout |
The timeout, in seconds, that AM should wait for a response from the directory server. Default: |
||
Use mixed case for password change messages |
Specifies whether the server returns password change messages in mixed (sentence) case or transforms them to uppercase. By default, the server transforms password reset and password change messages to uppercase. Enable this setting to return messages in sentence case. Default: Disabled |
||
LDAP Affinity Level |
Level of affinity used to balance requests across LDAP servers. Affinity-based load balancing means that each request for the same user entry goes to the same DS server. The DS server used for a specific operation is determined by the DN of the identity involved. List the directory server instances that form part of the affinity deployment in the Primary LDAP Server and Secondary LDAP Server properties. Options are:
Default: |
Outcomes
True-
The provided credentials match those found in the LDAP user data store.
False-
The provided credentials don’t match those found in the LDAP user data store.
Locked-
The profile associated with the provided credentials is locked.
Cancelled-
The user must change their password. When the journey prompts the user to change their password, the user cancels the password change.
Expired-
The profile is found, but the password has expired.
Identity Store Decision node
The Identity Store Decision node attempts to match the provided username and password with the credentials stored in the identity store.
If the credentials exist, the node checks the following:
-
Is the profile locked?
-
Has the provided password expired?
-
Has the user cancelled a password reset?
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
No |
Ping Identity Platform (self-managed) |
No |
Inputs
The node reads the username and password fields from the node state.
The journey can provide these credentials in a number of ways, for example, with a combination of the Platform Username node and Platform Password node, or by using the Zero Page Login Collector node.
Configuration
| Property | Usage |
|---|---|
Minimum Password Length |
For password change requests, the node rejects passwords that are shorter than this value.
If you set this value to Default: |
Username as Universal Identifier |
If you enable this property, the If this property is false, the value of the Default: false |
Use mixed case for password change messages |
Return password change messages in mixed (sentence) case. By default password reset and password change messages are transformed to upper case. Enable this option to return messages in sentence case. Default: Disabled |
Outcomes
True-
The credentials match those found in the identity store.
False-
The credentials don’t match those found in the identity store.
Locked-
The profile associated with the provided credentials is locked.
Cancelled-
The user cancelled a password change request. The example provides a detailed explanation of this outcome.
Expired-
The credentials match those found in the identity store, but the password has expired.
Example
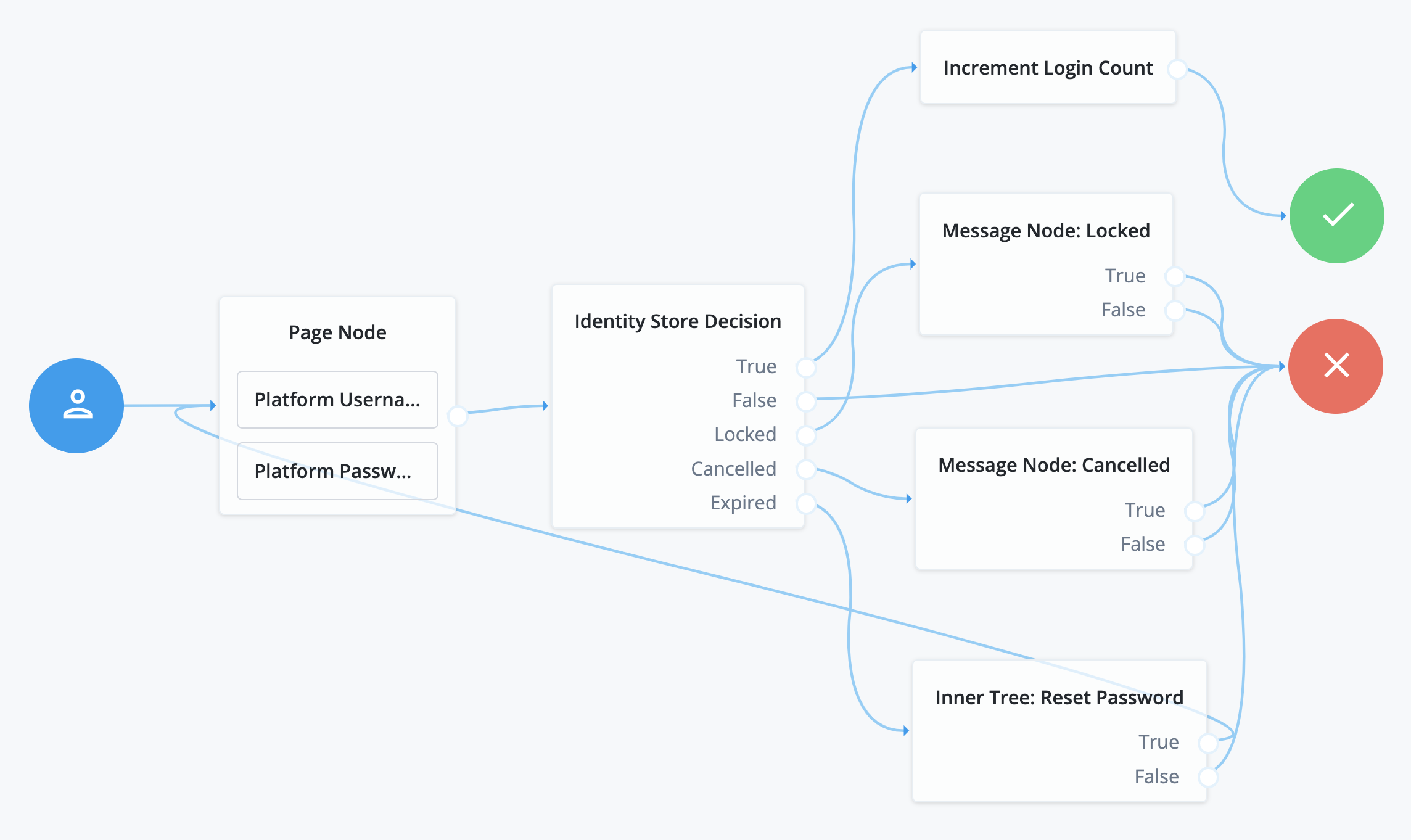
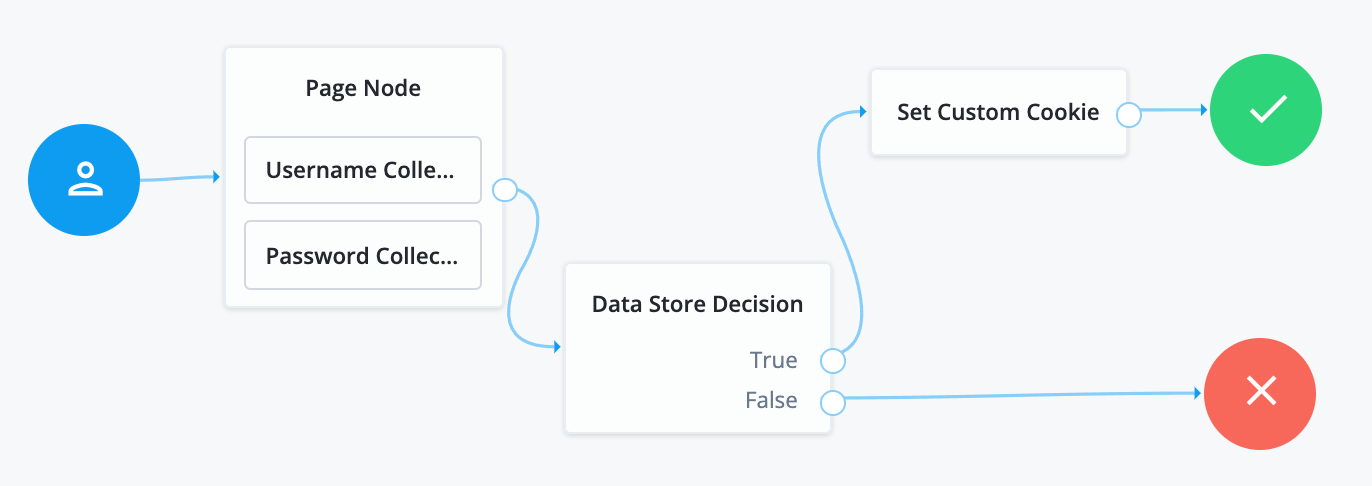
This example illustrates a simple login process.
-
A Page node with the embedded nodes (Platform Username node and Platform Password node) prompts the user for their credentials.
-
The Identity Store Decision node assesses the credentials:
-
If it finds the credentials in the data store and the credentials are valid, the journey follows the
Trueoutcome. An Increment Login Count node increments the login count and the user is authenticated. -
If the credentials don’t exist in the data store, the journey follows the
Falseoutcome and authentication fails. -
If the credentials exist in the data store but the account is locked, the journey follows the
Lockedoutcome. A Message node displays a custom lockout message and authentication fails. -
If the credentials exist in the data store but the user must change their password, the node prompts the user to change their password. If the user cancels this change request, the journey follows the
Cancelledoutcome. A Message node displays a custom message and authentication fails. -
If the credentials exist in the data store but the password has expired, the node follows the
Expiredoutcome. The user is routed to an inner tree journey that contains the password reset logic and then routes the user to the start of the journey to authenticate again.
-
Alternative nodes
-
The Data Store Decision node is a simpler node with only two outcomes,
TrueandFalse. Use this node if the flow only requires these outcomes.
Zero Page Login Collector node
The Zero Page Login Collector node verifies the presence of specific HTTP username and password headers in the incoming authentication request. If the headers exist, the node uses their corresponding values as the provided username and password.
The Zero Page Login Collector node is commonly used to:
-
Connect the
Has Credentialsoutcome connector to the input of a Data Store Decision node. -
Connect the
No Credentialsoutcome connector to the input of a Platform Username node followed by a Platform Password node, and then into the same Data Store Decision node.
The password collected by this node remains in the node state only until the journey reaches the next node that requires user interaction.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
-
HTTP username header
-
HTTP password header
-
An allowlist of referrers if
Allow Without Refererproperty is disabled. When you set theAllow Without Refererproperty tofalse, the request must contain a referrer from the allowlist; otherwise, the journey ends in a failure.
Configuration
Properties
| Property | Usage | ||
|---|---|---|---|
Username Header name |
Enter the name of the header that contains the username value. Default: X-OpenAM-Username |
||
Password Header name |
Enter the name of the header that contains the password value. Default: X-OpenAM-Password |
||
Allow without referer |
If enabled, the node accepts incoming requests that do not contain a If disabled, a Default: |
||
Referer Whitelist |
Specify a list of URLs allowed in the
|
Outcomes
-
Has Credentials -
No Credentials
Evaluation continues along the Has Credentials outcome path
if the specified headers are available in the request,
or the No Credentials path if the specified headers are not present.
Errors
- If more than one header value exists for username and/or password, the node returns the following error message
-
"Expecting only one header value for username and/or password but size is {}."
- If the node can’t decode the header values, the node returns the following error message
-
"Could not decode username or password header."
Multi-factor nodes
Get Authenticator App node
Displays information to obtain an authenticator application from the Apple App Store or the Google Play Store.
Use the following variables to customize the message:
-
{{appleLink}} -
{{appleLabel}} -
{{googleLink}} -
{{googleLabel}}
You can also include HTML elements, for example:
Apple: <a target='_blank' href='{{appleLink}}'>{{appleLabel}}</a>
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Get App Authenticator Message |
Localized title for the node.
The key is the language, such as Default: |
Continue Label |
Localized text to use on the Continue button.
The key is the language, such as |
Apple App Store URL |
Specifies the URL to download your authenticator application from the Apple App Store. The default value points to the ForgeRock Authenticator application for iOS. |
Google Play URL |
Specifies the URL to download your authenticator application from the Google Play Store. The default value points to the ForgeRock Authenticator application for Android. |
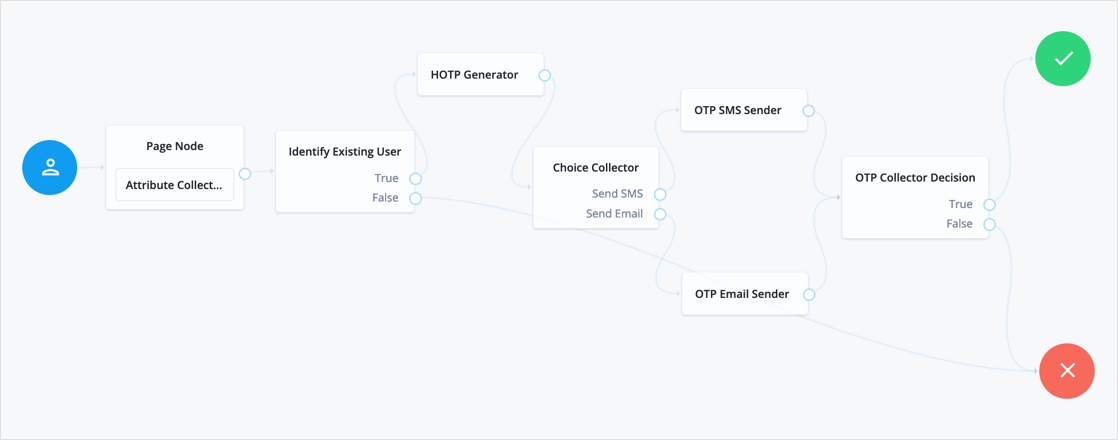
HOTP Generator node
Creates a string of random digits of the specified length for use as a one-time passcode.
Passwords are stored in the oneTimePassword transient node state property.
Use this node with these nodes to add one-time passcode verification as an additional factor:
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
One-time password length |
Specify the number of digits in the one-time passcode. The minimum number of digits is 6, in accordance with the HOTP specification. Default: 8 |
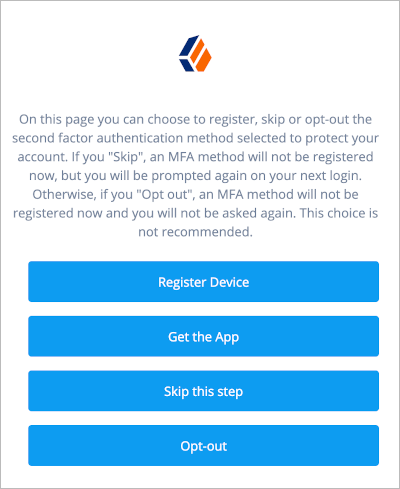
MFA Registration Options node
Lets the user register a multi-factor authentication device or skip the registration process.
The node requires the username of the identity to update and the type of MFA device. For example, you can use a Platform Username node and a Push Sender node earlier in the flow to obtain these.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
Register -
Get App(configurable) -
Skip(configurable) -
Opt-out(configurable)
Evaluation continues along the outcome the user selects.
Properties
| Property | Usage |
|---|---|
Remove 'skip' option |
If checked, users can no longer skip the node and must interact with it. |
Display Get Authenticator App |
If enabled, display the Get the App button. |
Message |
Localized text to use as the title of the screen. The key is the language, such as |
Register Device |
Localized text to use on the Register Device button. The key is the language, such as |
Get Authenticator App |
Localized text to use on the Get Authenticator App button. The key is the language, such as |
Skip this Step |
Localized text to use on the Skip this Step button. The button and the outcome only appear if the Remove 'skip' option is not enabled. The key is the language, such as |
Opt-out |
Localized text to use on the Opt-Out button. The button and the outcome only appear if the Remove 'skip' option is not enabled. Note that this node does not change the user’s profile. Connect the Opt-out outcome to an Opt-out Multi-Factor Authentication node to persist the option in the user’s profile. The key is the language, such as |
Example
Refer to the Push authentication example journey for how to use the MFA Registration Options node in a journey handling push devices.
OATH Device Storage node
The OATH Device Storage node stores devices in the user profile after an OATH Registration node records them in the shared state.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The OATH-related nodes can integrate with the following authenticator apps:
-
The ForgeRock Authenticator app for Android and iOS.
-
Third-party authenticator apps that support the following open standards:
Inputs
This node reads the device profile as the value of the shared state attribute oathDeviceProfile.
Dependencies
Precede this node in the flow with an OATH Registration node with its Store device data in shared state setting enabled.
Errors
This node logs a No device profile found on shared state error message
if it can’t get the device profile from the oathDeviceProfile shared state attribute.
Example
The following journey includes both username-password and one-time passcode authentication:
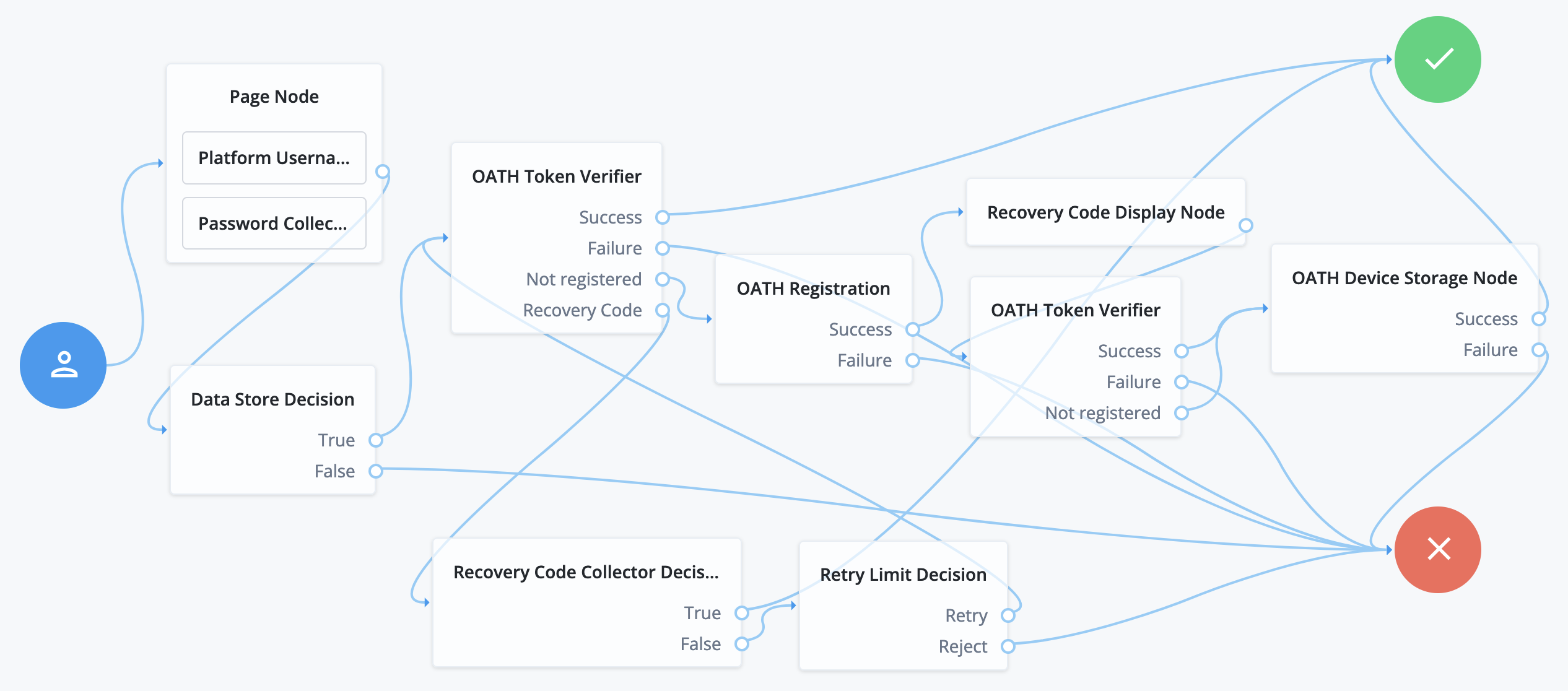
-
The Page node with the Platform Username node and the Platform Password node prompts for the user credentials.
-
The Data Store Decision node confirms the username-password credentials.
-
The first OATH Token Verifier node prompts for a one-time passcode with an option to use a recovery code.
-
The OATH Registration node prompts the user to register a device and includes its profile in the shared state.
-
The Recovery Code Display node shows the recovery codes and prompts the user to keep them safe.
-
The second OATH Token Verifier node prompts for a one-time passcode using the newly registered device.
-
The OATH Device Storage node writes the device profile to the user’s account.
-
The Recovery Code Collector Decision node prompts for a recovery code.
-
The Retry Limit Decision node lets the user retry another code if they enter one incorrectly.
OATH Registration node
The OATH Registration node lets the user register a device for OATH-based multi-factor authentication (MFA).
Based on the node settings, the user device displays a QR code that includes all the details required for registration.
If registration is successful, the node stores the device data, and recovery codes (if enabled),
and sets the skippable attribute to prevent repeat registration at next login.
|
You can use the Combined MFA Registration node to register a device for both push notifications and one-time passcode (OATH) verification in a single step. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The OATH-related nodes can integrate with the following authenticator apps:
-
The ForgeRock Authenticator app for Android and iOS.
-
Third-party authenticator apps that support the following open standards:
Inputs
This node reads the username attribute and optionally the oathDeviceProfile attribute from the shared state.
Dependencies
Confirm the user credentials before letting them register a device. For example, precede this node with the following nodes earlier in the authentication flow:
Properties
| Property | Usage | ||
|---|---|---|---|
Issuer |
Specify an identifier to appear on the user’s device, such as a company name, a website, or a realm. The authenticator application displays the value. Default: |
||
Account Name |
Select the profile attribute to display as the username in the authenticator application. If not specified, or if the specified profile attribute is empty, their username is used. Default: Username |
||
Background Color |
The background color in hex notation that displays behind the issuer’s logo within the authenticator application. Default: |
||
Logo Image URL |
The location of an image to download and display as the issuer’s logo within the authenticator application.
Default: none |
||
Generate Recovery Codes |
If enabled, recovery codes are generated and stored in the successful outcome’s transient state. Use the Recovery Code Display node to display the codes to the user for safekeeping. Default: true |
||
QR code message |
A custom, localized message with instructions to scan the QR code to register the device.
Default: none |
||
One Time Password Length |
The length of the generated OTP in digits. This value must be at least Default: |
||
Minimum Secret Key Length |
Number of hexadecimal characters allowed for the secret key. Default: |
||
OATH Algorithm |
Specify the algorithm the device uses to generate the OTP:
Default: |
||
TOTP Time Step Interval |
The length of time that an OTP is valid in seconds. For example, if the time step interval is 30 seconds, a new OTP is generated every 30 seconds and is valid for 30 seconds only. Default: |
||
TOTP Hash Algorithm |
The HMAC hash algorithm used to generate the OTP codes. PingOne Advanced Identity Cloud supports SHA1, SHA256, and SHA512. Default: |
||
HOTP Checksum Digit |
This adds a digit to the end of the OTP generated to be used as a checksum to verify the OTP was generated correctly. This is in addition to the actual password length. Only set this if the user devices support it. Default: false |
||
HOTP Truncation Offset |
This is an option used by the HOTP algorithm that not all devices support. Leave the default value unless you know user devices use an offset. Default: |
||
Store device data in shared state |
If enabled, the device data isn’t stored in the user profile on successful completion of the node.
Instead, the node adds the device data as a base64-encoded string to the In the shared node state: Decoded value: json Use the OATH Device Storage node to store the device data in the user profile instead. Default: false |
Outputs
If the Store device data in shared state setting is enabled,
this node records the device profile in the oathDeviceProfile shared state attribute.
If the Generate Recovery Codes setting is enabled,
this node records the recovery codes in the oathEnableRecoveryCode shared state attribute.
Errors
This node logs the following error messages:
No username found.-
The node failed to read the username from the shared state.
No device profile found on shared state-
The node failed to read the device profile from the shared state.
Example
The following journey includes both username-password and one-time passcode authentication:
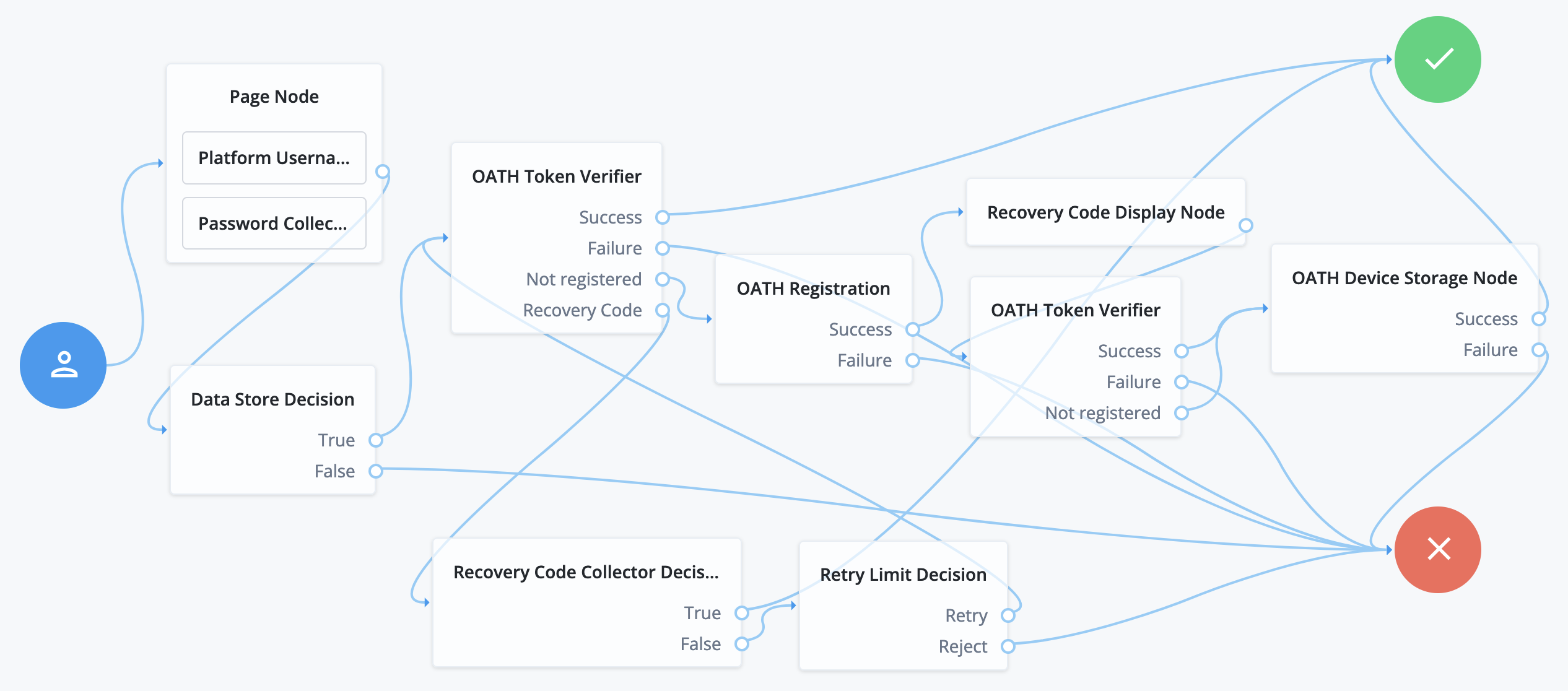
-
The Page node with the Platform Username node and the Platform Password node prompts for the user credentials.
-
The Data Store Decision node confirms the username-password credentials.
-
The first OATH Token Verifier node prompts for a one-time passcode with an option to use a recovery code.
-
The OATH Registration node prompts the user to register a device and includes its profile in the shared state.
-
The Recovery Code Display node shows the recovery codes and prompts the user to keep them safe.
-
The second OATH Token Verifier node prompts for a one-time passcode using the newly registered device.
-
The OATH Device Storage node writes the device profile to the user’s account.
-
The Recovery Code Collector Decision node prompts for a recovery code.
-
The Retry Limit Decision node lets the user retry another code if they enter one incorrectly.
OATH Token Verifier node
The OATH Token Verifier node requests and verifies a one-time passcode (OTP) generated by a device such as a mobile phone.
The default configuration is time-based OTP (TOTP), but the node also supports HMAC (HOTP).
The node requires prior authentication and a device registered with an OATH Registration node.
|
You can use the OATH nodes in conjunction with the ForgeRock Authenticator application to register your device, receive notifications, and generate one-time passwords. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The OATH-related nodes can integrate with the following authenticator apps:
-
The ForgeRock Authenticator app for Android and iOS.
-
Third-party authenticator apps that support the following open standards:
Dependencies
Confirm the user credentials before letting them authenticate with a device. For example, precede this node with the following nodes earlier in the authentication flow:
Configuration
| Property | Usage |
|---|---|
OATH Algorithm |
Specify the algorithm the device uses to generate the OTP:
Default: |
HOTP Window Size |
Specify how much the OTP device and the server counter can be out of sync. For example, if the window size is 100 and the server’s last successful login was at counter value 2, the server accepts an OTP that is generated between counter 3 and 102. Default: |
TOTP Time Step Interval |
The length of time an OTP is valid in seconds. For example, if the time step interval is 30 seconds, a new OTP is generated every 30 seconds and is valid for 30 seconds only. Default: |
TOTP Time Steps |
Specify how many time steps the OTP can be out of sync. This applies to codes generated before or after the current code. For example, with a time step of 1, the server accepts the previous, current, and next codes. Default: |
TOTP Hash Algorithm |
The HMAC hash algorithm used to generate the OTP codes. The ForgeRock Authenticator application supports SHA1, SHA256, and SHA512. Default: |
TOTP Maximum Allowed Clock Drift |
Specify how many time steps the authenticator application can be out of sync with the server before manual resynchronization is required. For example, with TOTP Time Steps of The drift for a user’s device is calculated each time they enter a new code.
If the drift exceeds this value, the outcome is Default: |
Allow recovery codes |
If enabled, lets users provide a recovery code to authenticate. Default: false |
Outcomes
Success-
The user has a registered device and the token code was verified.
Failure-
The user was not authenticated, or the collected token code can’t be verified.
Not registered-
The user account has no registered device profiles.
Recovery Code-
Allow recovery codes is enabled, and the user chose to provide a recovery code.
Errors
If this node cannot read the username from the shared state, it logs an error message: Expected username to be set.
If processing raises an exception, this node logs the detail as an error message.
Example
The following journey includes both username-password and one-time passcode authentication:
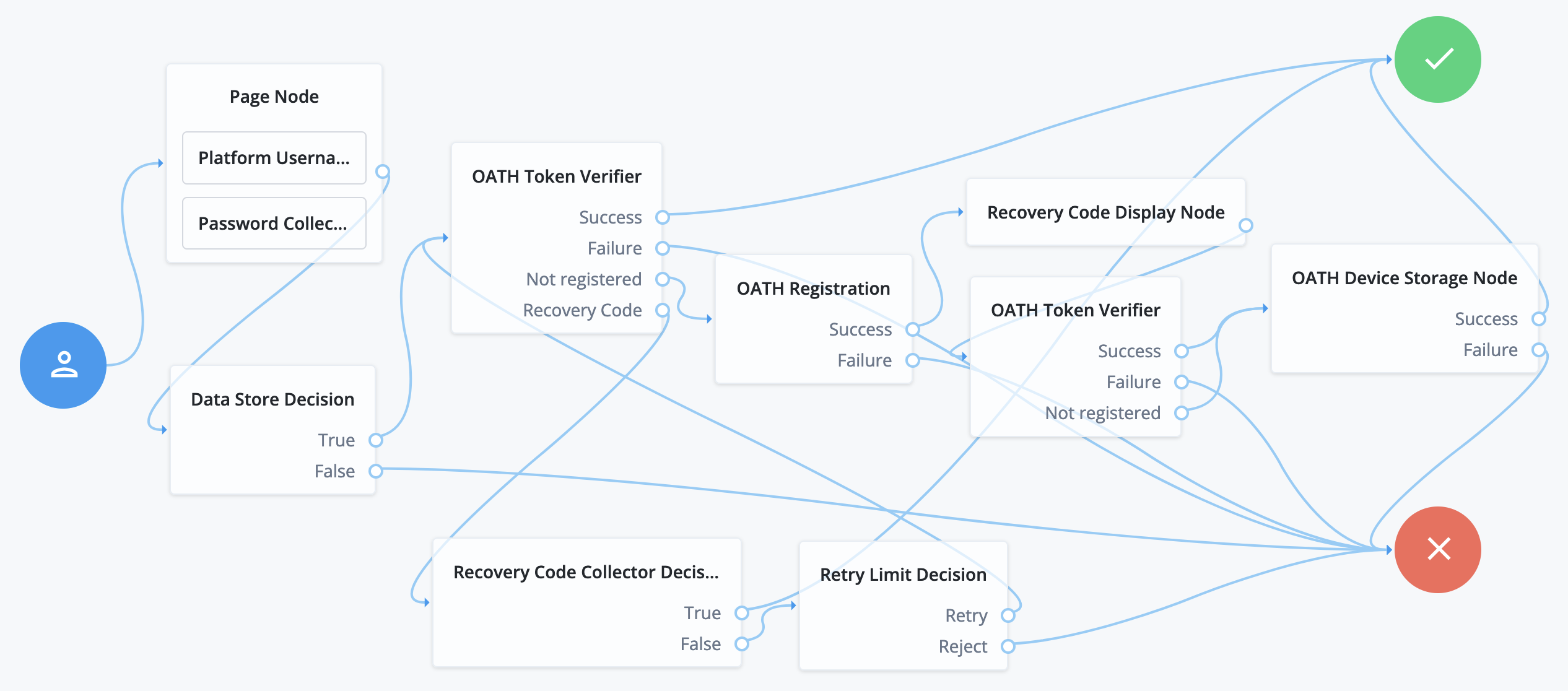
-
The Page node with the Platform Username node and the Platform Password node prompts for the user credentials.
-
The Data Store Decision node confirms the username-password credentials.
-
The first OATH Token Verifier node prompts for a one-time passcode with an option to use a recovery code.
-
The OATH Registration node prompts the user to register a device and includes its profile in the shared state.
-
The Recovery Code Display node shows the recovery codes and prompts the user to keep them safe.
-
The second OATH Token Verifier node prompts for a one-time passcode using the newly registered device.
-
The OATH Device Storage node writes the device profile to the user’s account.
-
The Recovery Code Collector Decision node prompts for a recovery code.
-
The Retry Limit Decision node lets the user retry another code if they enter one incorrectly.
Opt-out Multi-Factor Authentication node
Sets the skippable attribute in the user’s profile, which lets them skip MFA.
The node requires the username of the identity to update, and the type of MFA device. For example, you can use a Platform Username node and a Push Sender node earlier in the flow to obtain these.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
OTP Collector Decision node
Requests and verifies one-time passwords.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
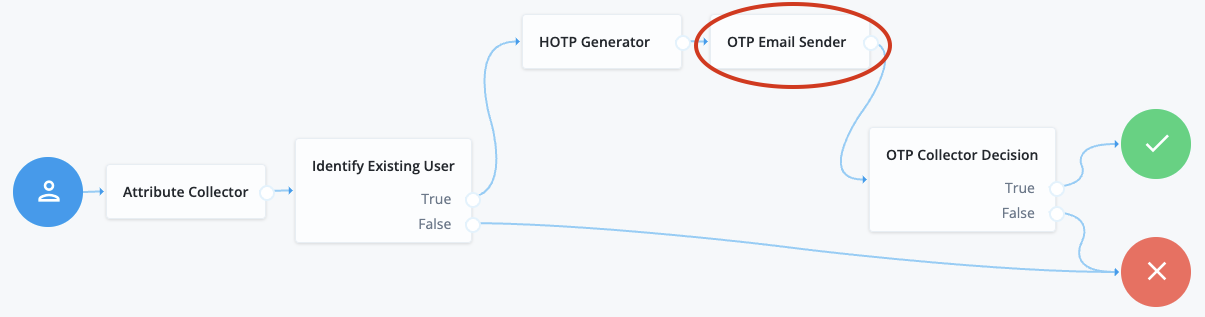
OTP Email Sender node
The OTP Email Sender node sends an email containing a generated one-time passcode (OTP) to the user.
Send mail requests time out after 10 seconds.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the following input from the shared state:
-
The authenticating user’s ID. The node queries the user’s entry for an email address.
Implement an Attribute Collector node node before this node to obtain the user’s ID.
-
The OTP stored in the
oneTimePasswordtransient state property.Implement the HOTP Generator node before this node in the journey to obtain the OTP.
Configuration
| Property | Usage | ||
|---|---|---|---|
Mail Server Host Name (required) |
The hostname of the SMTP email server. |
||
Mail Server Host Port |
The outgoing mail server port. Common ports are 25, 465 for SSL/TLS, or 587 for StartTLS. |
||
Mail Server Authentication Username |
The username PingOne Advanced Identity Cloud uses to connect to the mail server. |
||
Mail Server Authentication Password |
The password PingOne Advanced Identity Cloud uses to connect to the mail server.
|
||
Mail Server Secret Label Identifier |
An identifier used to create a secret label for mapping to a secret in a secret store. PingOne Advanced Identity Cloud uses this identifier to create a specific secret label for this node. The secret label takes the form
If you set a Mail Server Secret Label Identifier and PingOne Advanced Identity Cloud finds a matching secret in a secret store, the Mail Server Authentication Password is ignored. |
||
Email From Address (required) |
The email address from which the OTP will appear to have been sent. |
||
Email Attribute Name |
The attribute in the user profile that contains the email address to which the email with the OTP is sent. Default: |
||
The subject of the email |
Click Add to add a new email subject. Enter the locale, such as |
||
The content of the email |
Click Add to add the content of the email. Enter the locale, such as |
||
Mail Server Secure Connection |
Set the connection method to the mail server. If you set a secure method here, PingOne Advanced Identity Cloud must trust the server certificate of the mail server. The possible values for this property are:
Default: |
||
Gateway Implementation Class |
The class the node uses to send SMS and email messages. Default: |
Errors
The node throws an IdRepoException and an SSOException error if it’s unable to obtain the user’s email address.
Outcomes
Single outcome path.
Implement an OTP Collector Decision node after this node to continue the authentication journey.
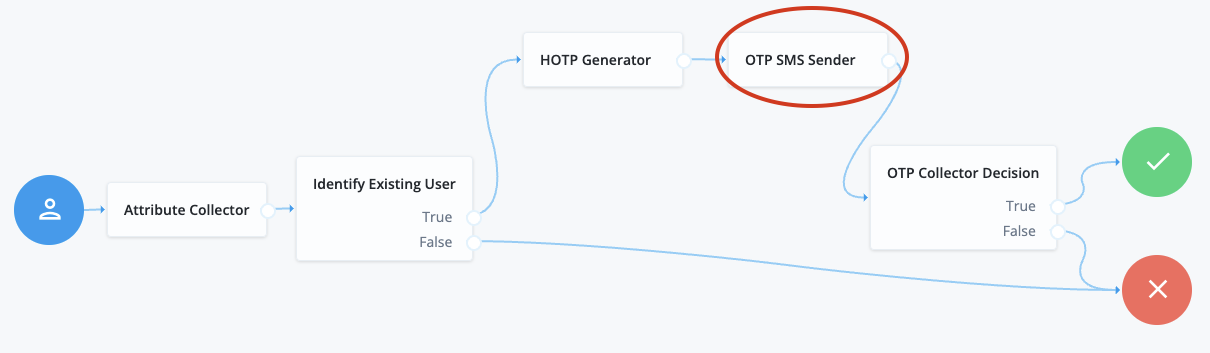
OTP SMS Sender node
The OTP SMS Sender node uses an email-to-SMS gateway provider to send an SMS message containing a generated one-time password (OTP) to the user.
The node sends an email to an address formed by joining the following values together:
-
The user’s telephone number, obtained by querying a specified profile attribute, for example,
telephoneNumber. -
The
@character. -
The email-to-SMS gateway domain, obtained by querying the profile attribute specified by the Mobile Carrier Attribute Name property.
For example, if configured to use the TextMagic email-to-SMS service,
the node might send an email through the specified SMTP server to the address: 18005550187@textmagic.com.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the following input from the shared state:
-
The authenticating user’s ID. The node queries the user’s entry for a telephone number.
Implement an Attribute Collector node node before this node to obtain the user’s ID.
-
The OTP stored in the
oneTimePasswordtransient state property.Implement the HOTP Generator node before this node in the journey to obtain the OTP.
Configuration
| Property | Usage | ||
|---|---|---|---|
Mail Server Host Name (required) |
The hostname of the SMTP email server. |
||
Mail Server Host Port |
The outgoing mail server port. Common ports are 25, 465 for SSL/TLS, or 587 for StartTLS. |
||
Mail Server Authentication Username |
The username PingOne Advanced Identity Cloud uses to connect to the mail server. |
||
Mail Server Authentication Password |
The password PingOne Advanced Identity Cloud uses to connect to the mail server.
|
||
Mail Server Secret Label Identifier |
An identifier used to create a secret label for mapping to a secret in a secret store. PingOne Advanced Identity Cloud uses this identifier to create a specific secret label for this node. The secret label takes the form
If you set a Mail Server Secret Label Identifier and PingOne Advanced Identity Cloud finds a matching secret in a secret store, the Mail Server Authentication Password is ignored. |
||
Email From Address (required) |
The email address from which the OTP will appear to have been sent. |
||
Mobile Phone Number Attribute Name |
The attribute in the user profile that contains the mobile phone number to which the SMS with the OTP is sent. Default: |
||
Mobile Carrier Attribute Name |
The attribute in the user profile that contains the mobile carrier domain for sending SMS messages. By default, an PingOne Advanced Identity Cloud user profile doesn’t have an attribute for the mobile carrier domain. You can customize the user profile by adding a new attribute to it, then populate that attribute with users' SMS messaging domains. All mobile carriers and bulk SMS messaging services have associated SMS messaging domains.
For example, Verizon uses If you leave the Mobile Carrier Attribute Name property empty, PingOne Advanced Identity Cloud defaults to sending SMS messages
using |
||
The subject of the message |
Click Add to add a new message subject. Enter the locale, such as |
||
The content of the message |
Click Add to add the content of the message. Enter the locale, such as |
||
Mail Server Secure Connection |
Set the connection method to the mail server. If you set a secure method here, PingOne Advanced Identity Cloud must trust the server certificate of the mail server. The possible values for this property are:
Default: |
||
Gateway Implementation Class |
The class the node uses to send SMS and email messages. Default: |
Errors
The node throws an IdRepoException and an SSOException error if it’s unable to obtain the user’s telephone number.
Outcomes
Single outcome path.
Implement an OTP Collector Decision node after this node to continue the authentication journey.
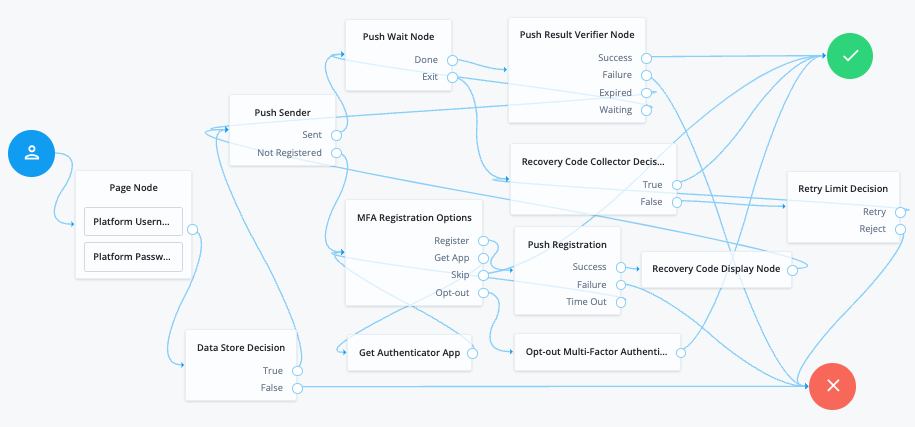
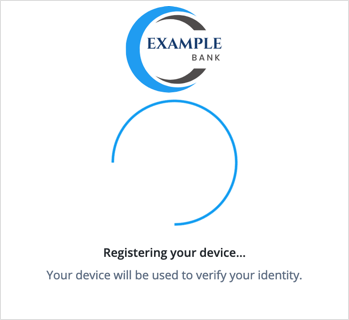
Push Registration node
Provides a way to register a device, such as a mobile phone for multi-factor authentication using push notifications.
Learn more in MFA: Authenticate using push notification.
The node requires the username of the identity to update. For example, by using a Platform Username node.
|
You can use the Combined MFA Registration node to register a device for use with both push notifications and one-time passcode (OATH) verification in a single step. |
You must also configure the Push Notification Service.
For information on provisioning the credentials required by the Push Notification Service, refer to How To Configure Service Credentials (Push Auth, Docker) in Backstage in the Knowledge Base.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The push-related nodes integrate with the ForgeRock Authenticator app for Android and iOS.
Third-party authenticator apps are not compatible with ForgeRock’s push notification functionality.
Outcomes
-
Success -
Failure -
Time Out
If the user successfully registers their authenticator, evaluation continues along the Success outcome path.
If the node does not receive a response from the user’s device within the time specified in the node configuration,
evaluation continues along the Time Out outcome path.
If AM encounters an issue when attempting to register using a device,
evaluation continues along the Failure outcome path.
Properties
| Property | Usage | ||
|---|---|---|---|
Issuer |
Specify an identifier so that the user knows which service their account relates to. The value is displayed by the authenticator application: 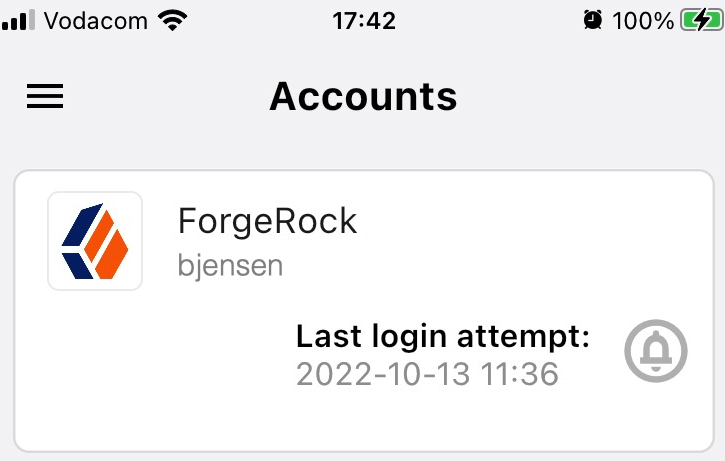
For example, |
||
Account Name |
Specifies the profile attribute to display as the username in the authenticator application. If not specified, or if the specified profile attribute is empty, their username is used. |
||
Registration Response Timeout |
Specify the number of seconds to wait for a response from the authenticator. If the specified time is reached, evaluation continues along the |
||
Background Color |
Specifies the background color, in hex notation, to display behind the issuer’s logo within the ForgeRock Authenticator application. |
||
Logo Image URL |
Specifies the location of an image to download and display as the issuer’s logo in the ForgeRock Authenticator application. |
||
Generate Recovery Codes |
Specify whether push-specific recovery codes should be generated. If enabled, recovery codes are generated and stored in transient state if registration was successful. Use the Recovery Code Display node to display the codes to the user for safe keeping.
|
||
QR code message |
The message with instructions to scan the QR code to register the device. Click Add.
Enter the message locale in the Key field. For example, |
Example
Refer to the Push authentication example journey for how to use the Push Registration node in a journey handling push devices.
Push Result Verifier node
Works with the Push Sender node to validate the user’s response to a previously sent push notification message.
|
If the push message contained any additional information, for example, if it was a registration request,
the values are stored in the |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The push-related nodes integrate with the ForgeRock Authenticator app for Android and iOS.
Third-party authenticator apps are not compatible with ForgeRock’s push notification functionality.
Outcomes
-
Success -
Failure -
Expired -
Waiting
Evaluation continues along the Success outcome path if the push notification was approved by the user.
Evaluation continues along the Failure outcome path if the push notification was rejected by the user.
If no response to the push notification was received
within the Message Timeout value specified in the Push Sender node,
evaluation continues along the Expired outcome path.
If no response to the push notification has been received yet,
evaluation continues along the Waiting outcome path.
Push Sender node
Sends push notification messages to a device for multi-factor authentication.
Configure the AM Push Notification Service for the realm before using this node.
For information on provisioning the credentials used by the service, refer to How To Configure Service Credentials (Push Auth, Docker) in Backstage in the Knowledge Base.
To determine whether the user has a registered device, the flow must have included the username in the shared state, for example, by using a Platform Username node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The push-related nodes integrate with the ForgeRock Authenticator app for Android and iOS.
Third-party authenticator apps are not compatible with ForgeRock’s push notification functionality.
Outcomes
-
Sent -
Not Registered -
Skipped -
Failure
Evaluation continues along the Sent outcome path
if the push notification was successfully sent to the handling service.
If the user doesn’t have a registered device, evaluation continues along the Not Registered outcome path.
If the user chooses to skip push authentication, evaluation continues along the Skipped outcome path.
The node displays the Failure outcome only if you enable the Capture failure configuration option. In this
case, evaluation proceeds along the Failure path if there’s an error during execution of the node.
Properties
| Property | Usage |
|---|---|
Message Timeout |
Specifies the number of milliseconds the push notification message will remain valid. The Push Result Verifier node rejects responses to push messages that have timed out. |
User Message |
Specifies the optional message to send to the user. You can provide the message in multiple languages by specifying the locale in the The locale selected for display is based on the user’s locale settings in their browser. Messages provided in the node override the defaults provided by AM. The following variables can be used in the
Example: |
Remove 'skip' option |
Enable this option in the node to make the push authentication mandatory. When disabled, the user can skip the push authentication requested by the node,
and evaluation continues along the Default: Disabled |
Share Context info |
If enabled, context data such as For example: json The ForgeRock Authenticator displays this additional information to the user to help verify that the request is genuine and initiated by them. 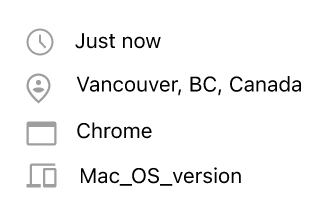
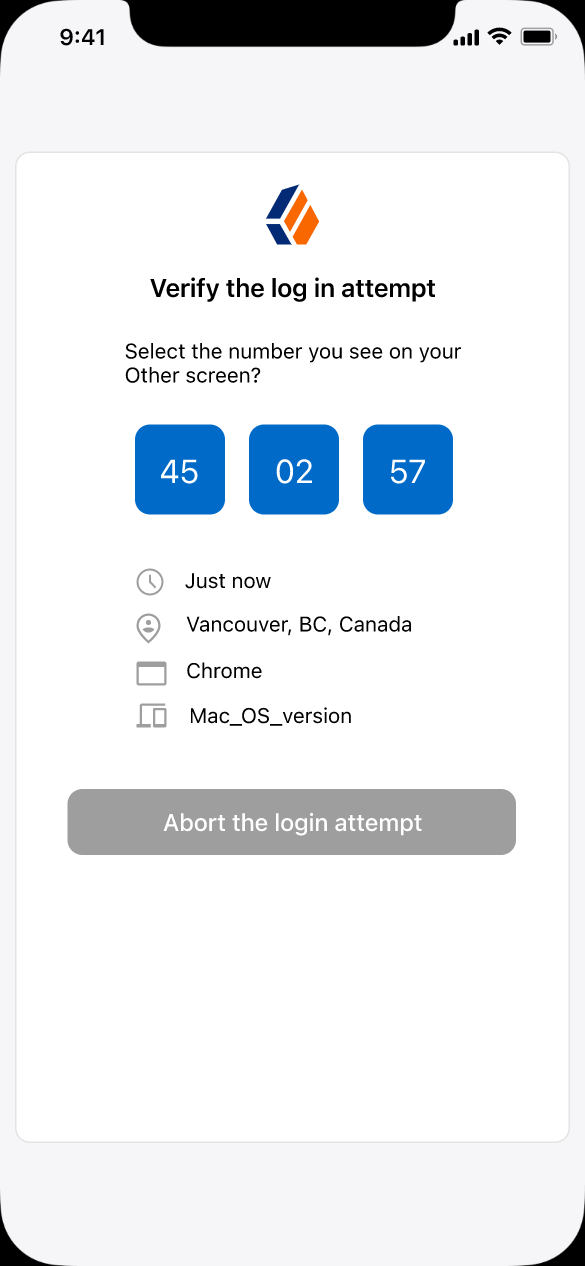
Figure 1. Context information in the ForgeRock Authenticator
For the location attribute to be set, the flow must contain a Device Profile Collector node with Collect Device Location enabled. |
Custom Payload Attributes |
Specify shared state objects to be included in the message payload sent to the client.
The size of the payload must not exceed 3 Kb or a To add a custom attribute, enter the shared state object name in the text field and click Add. Repeat for each object you want to include in the payload. |
Push Type |
Select the type of the push authentication the user must perform on their device to continue the journey. Possible values are:
The actions the user performs vary depending on the selected option. Refer to Respond to push notifications. |
Capture failure (optional) |
If enabled, and the node fails to send the Push Notification, the journey skips the node. The journey stores the reason
for the failure in the Possible failure reasons include |
Example
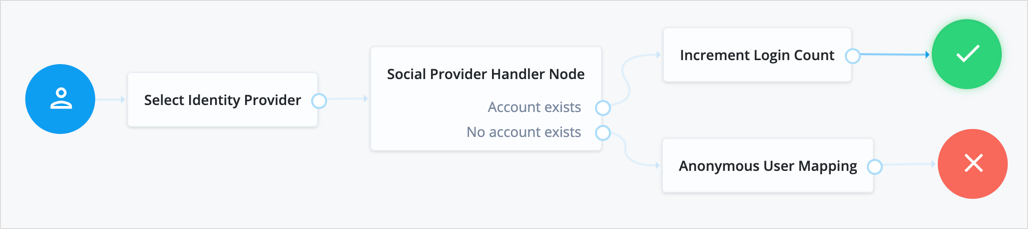
The following example shows one possible implementation of multi-factor push authentication:
Node connections
| Source node | Outcome path | Target node |
|---|---|---|
Page Node containing: Platform Username, Platform Password |
→ |
Data Store Decision |
Data Store Decision |
True |
Push Sender |
False |
Failure |
|
Push Sender |
Sent |
Push Wait |
Not Registered |
MFA Registration Options |
|
Push Wait |
Done |
Push Result Verifier |
Exit |
Recovery Code Collector Decision |
|
Push Result Verifier |
Success |
Success |
Failure |
Failure |
|
Expired |
Push Sender |
|
Waiting |
Push Wait |
|
MFA Registration Options |
Register |
Push Registration |
Get App |
Get Authenticator App |
|
Skip |
Success |
|
Opt-out |
Opt-out Multi-Factor Authentication |
|
Recovery Code Collector Decision |
True |
Success |
False |
Retry Limit Decision |
|
Push Registration |
Success |
Recovery Code Display Node |
Failure |
Failure |
|
Time Out |
MFA Registration Options |
|
Get Authenticator App |
→ |
MFA Registration Options |
Opt-out Multi-Factor Authentication |
→ |
Success |
Retry Limit Decision |
Retry |
Recovery Code Collector Decision |
Reject |
Failure |
|
Recovery Code Display Node |
→ |
Push Sender |
After verifying the user’s credentials, evaluation continues to the Push Sender node.
If the user has a registered device:
-
AM sends a push to their registered device.
-
The Push Wait node pauses authentication for 5 seconds, during which time the user can respond to the push notification on their device; for example, by using the ForgeRock Authenticator application.
-
If the user responds positively, they are authenticated successfully and logged in.
-
If the user responds negatively, they are not authenticated successfully and do not receive a session.
-
If the push notification expires, AM sends a new push notification.
Use a Retry Limit Decision node to constrain the number of times a new code is sent. -
If the user has not yet responded, the flow loops back a step and the Push Wait node pauses authentication for another 5 seconds.
If the user exits the Push Wait node, they can enter a recovery code in order to authenticate.
For this situation, configure the Exit Message property in the Push Wait node with a message, such as
Lost phone? Use a recovery code. -
A Retry Limit Decision node allows three attempts at entering a recovery code before failing the authentication.
If the user does not have a registered device:
-
The MFA Registration Options node presents the user with the following options:
- Register Device
-
The flow continues to the Push Registration node, which displays the QR code that should be scanned with a suitable authenticator application.
- Get the App
-
The flow continues to the Get Authenticator App node, which displays the links needed to obtain a suitable application, such as the ForgeRock Authenticator.
- Skip this step
-
Displayed only if the node configuration lets the user skip. In this example, skipping is linked to the
Successoutcome. Alternatively, an Inner Tree Evaluator node could have been used for authentication. - Opt-out
-
Displayed only if the node configuration allows the user to skip or opt out. Evaluation continues to the Opt-out Multi-Factor Authentication node, which updates the user’s profile to skip MFA with push in the future. In this example, after updating the profile the flow continues to the Success node.
-
The user registers the device with the Push Registration node.
After registration, the recovery codes are displayed to the user for safekeeping, and evaluation continues with the Push Sender node to start push notification.
|
To manage push devices, the user must log in using either the device or a recovery code. Learn more in Manage devices for MFA. |
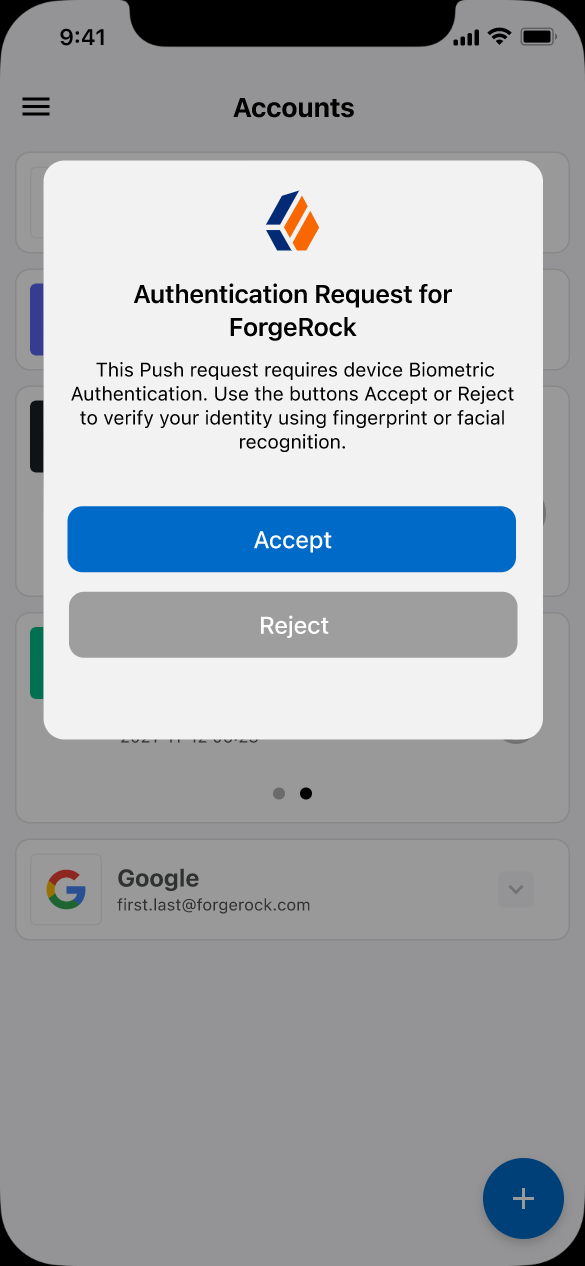
Respond to push notifications
The default Push Type setting is Tap to Accept. This requires the user to tap to either Accept or Reject in the ForgeRock Authenticator.
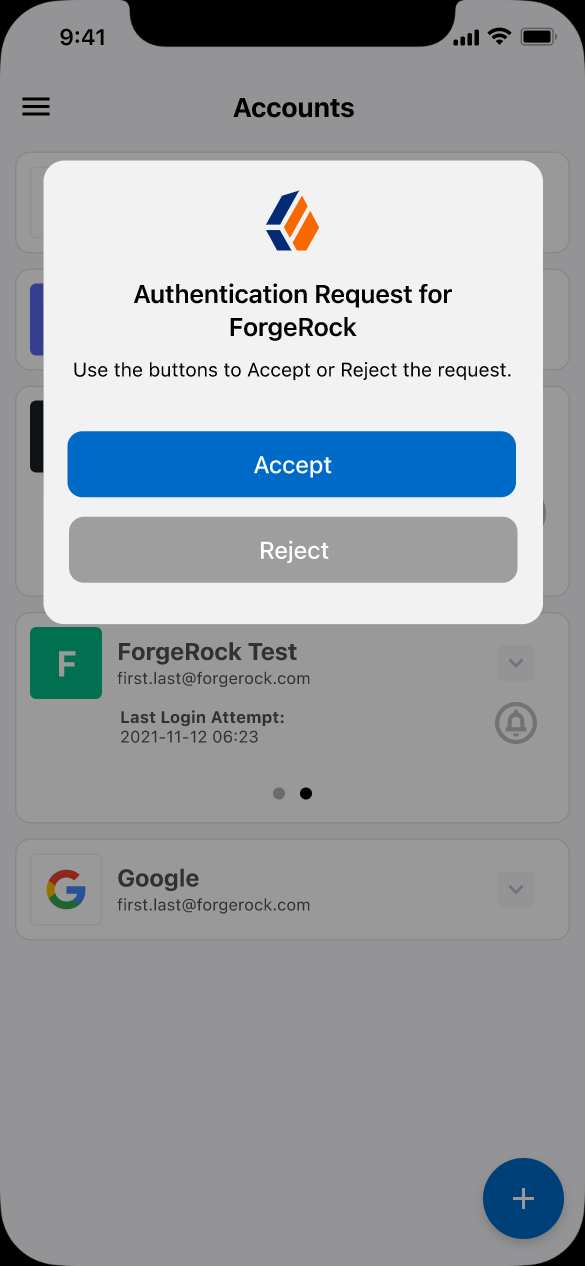
Research shows that users might accept a push authentication without fully checking if it is legitimate. To reduce the chances of a user accepting a malicious push authentication attempt, you can configure two additional push types:
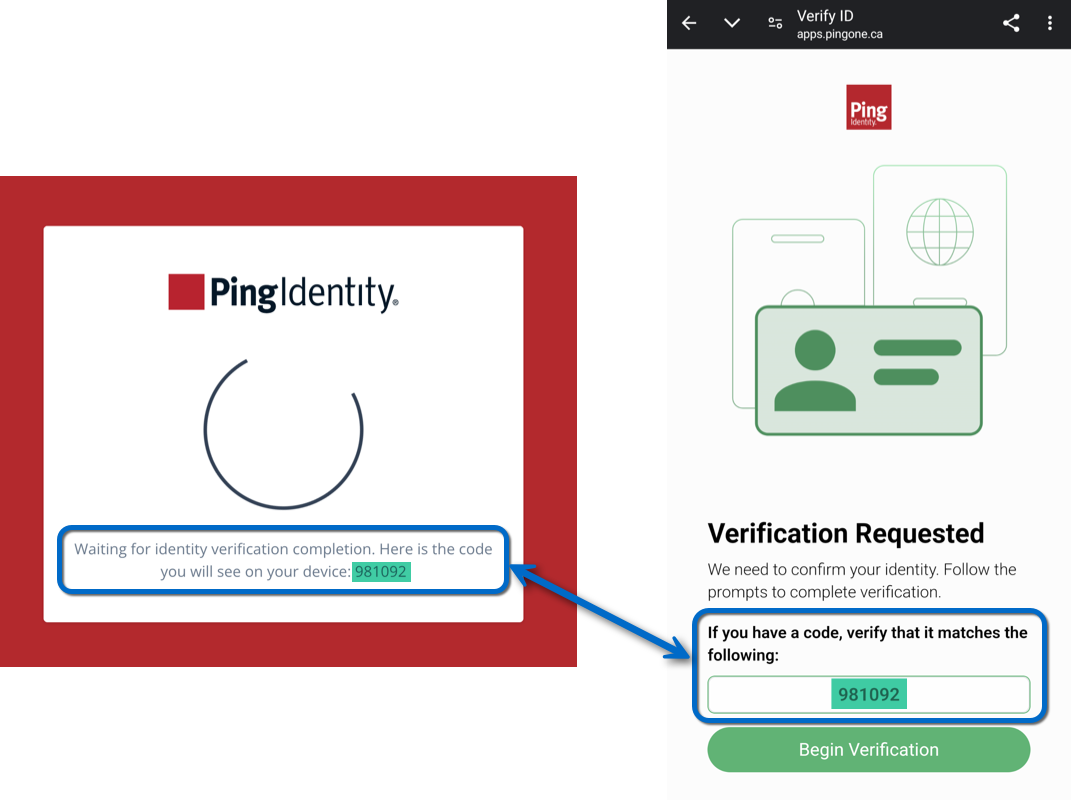
Display Challenge Code-
Requires the user to select one of three numbers displayed on their device. This selected number must match the code displayed in the browser for the request to be verified.
Use Biometrics to Accept-
Requires the user’s biometric authentication to process the notification, after tapping
AcceptorReject.
Push Wait node
Pauses the authentication for the specified number of seconds during the processing of a push authentication request.
When push authentication involves a number selection challenge,
where the push type of the Push Sender node is set to Display Challenge Code,
the node displays the code challenge for the user to complete.
Connect this node to a Push Result Verifier node to check the result of the code challenge.
Both nodes' waiting times and the messages are configurable.
The message displayed on the exit button can be configured using the Exit Message property.
To provide localized versions of the waiting, push challenge, and exit messages
in multiple languages, configure the message properties
to specify the locale in the KEY field (for example, en-US) and the message in the VALUE field.
The locale selected for display is based on the user’s locale settings in their browser.
Messages provided in the node override the defaults provided by AM.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Authenticators
The push-related nodes integrate with the ForgeRock Authenticator app for Android and iOS.
Third-party authenticator apps are not compatible with ForgeRock’s push notification functionality.
Outcomes
-
Done -
Exit
Evaluation continues along the Done outcome path after the wait time has passed.
Evaluation continues along the Exit outcome path if the user clicks the exit button.
Properties
| Property | Usage |
|---|---|
Seconds To Wait |
Specify the number of seconds to pause authentication. Default: |
Waiting Message |
Customize the message to display to the user. To include the remaining seconds in the message,
use the Click Add to enter a KEY and VALUE for a localized message and + to save. Repeat for each supported language. Default: |
Push Challenge Message |
Customize the message containing the challenge code. To include the number challenge,
use the Click Add to enter a KEY and VALUE for a localized message and + to save. Repeat for each supported language. Default: |
Exit Message |
Customize the message to display to the user when they choose to exit the node before the wait period has elapsed. The message is displayed as a link. Click Add to enter a KEY and VALUE for a localized message and + to save. Repeat for each supported language. Default: |
Example
Refer to the Push authentication example journey for how to use the Push Wait node in a journey handling push devices.
Recovery Code Collector Decision node
Lets users authenticate with a recovery code provided when registering a device for multi-factor authentication.
Use this node for a flow that includes push notifications or one-time passwords. When the user loses their registered device, they can use a recovery code as an alternative method for authentication. For more information on viewing the recovery codes when registering a device, refer to Register the ForgeRock Authenticator for multi-factor authentication.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
True -
False
Evaluation continues along the True outcome path if the provided recovery code matches one belonging to the user.
To determine whether the provided code belongs to the user, the shared state must include the username.
You can obtain this using a
Platform Username node.
If the recovery code does not match, or a username has not been acquired,
evaluation continues along the False outcome path.
Recovery Code Display node
Retrieves generated recovery codes from the transient state and presents them to the user, for safe-keeping. The codes can be used to authenticate if a registered device is lost or stolen.
Use this node with the WebAuthn Registration node, the OATH Registration node or the Push Registration node.
Generated recovery codes are inserted into transient state
when evaluation continues along the Success outcome path of the MFA nodes configured to generate recovery codes.
Connect this node to the Success outcome path to display the codes.
If no recovery codes are available in transient state, evaluation continues along the only outcome path, and nothing is displayed to the user.
|
Generated recovery codes cannot be retrieved from the user’s profile—they are one-way encrypted. This node is the one and only opportunity to view and save the recovery codes. |
WebAuthn Authentication node
The WebAuthn Authentication node lets users on supported clients authenticate using a registered FIDO device.
What are the differences between WebAuthn and device binding/signing?
There are many similarities between WebAuthn and device binding and JWS verification. We provide authentication nodes to implement both technologies in your journeys.
Both can be used for usernameless and passwordless authentication, they both use public key cryptography, and both can be used as part of a multi-factor authentication journey.
One major difference is that with device binding, the private key never leaves the device.
With WebAuthn, there is a possibility that the private key is synchronized across client devices because of Passkey support, which may be undesirable for your organization.
For details of the differences, refer to the following table:
| Feature | WebAuthn / FIDO | Device Binding / JWS Verifier | Details |
|---|---|---|---|
Industry-standards based |
✅ |
❌ |
You can refer to the WebAuthn W3C specification. Device binding and JWS verification are proprietary implementations. |
Public key cryptography |
✅ |
✅ |
Both methods use Public key cryptography. |
Usernameless support |
✅ |
✅ |
After registration, the username can be stored in the device and obtained during authentication without the user having to enter their credentials. |
Keys are bound to the device |
❌ |
✅ |
With WebAuthn, if Passkeys are used, they can be shared across devices. With device binding, the private keys do not leave the device. |
Sign custom data |
❌ |
✅ |
With device binding, you can:
|
Format of signed data |
|||
Integration |
❌ |
✅ |
With device binding, after verification, the signed JWT is available in:
This enables the data within to be used for integration into your processes and business logic. |
Platform support |
✅ Android ✅ iOS ✅ Web browsers |
✅ Android ✅ iOS ❌ Web browsers |
As it is challenging to store secure data in a browser as a client app, device binding is not supported in web browsers. |
Authenticator support |
Determined by the platform. Configuration limited to:
|
Determined by the authentication node. Full configuration options:
|
With device binding, you can specify what authentication action the user must perform to get access to the private keys. This provides greater flexibility in your security implementation and can reduce authentication friction for your users. |
Key storage |
Web browsers and iOS synchronize to the cloud. Android has the option to synchronize to the cloud. |
|
Both technologies store the private keys securely on the client. WebAuthn supports synchronizing the private keys to the cloud for use on other devices. This can reduce authentication friction for your users but may also increase the risk of a breach. |
Managing device keys |
Managed by the device OS. Apps cannot delete local client keys programmatically and do not have a reference to the remote server key for deletion. |
Managed by the Ping SDKs. Provides an interface to delete local client and remote server keys. |
The ability to programmatically delete both client and server keys can greatly simplify the process of registering a new device if an old device is lost or stolen. |
Passkey support |
✅ |
❌ |
WebAuthn supports synchronizing the private keys to the cloud for use on other devices. Device binding keeps the private key locked in the device. |
App integrity verification |
|
Not provided by the device binding or verification nodes. It can be added as part of the journey by using app integrity nodes. |
App integrity verification helps ensure your users are only using a supported app rather than a third-party or potentially malicious version. |
Key attestation |
|
|
Key attestation verifies that the private key is valid and correct, is not forged, and was not created in an insecure manner. |
Complexity |
Medium |
Low |
WebAuthn requires a bit more configuration, for example, creating and uploading the Device binding only requires the journey and the SDK built into your app. |
| To authenticate using WebAuthn on an Android or iOS device without an external keystore, screen lock must be enabled. Find more information in the respective device documentation for Android and iOS. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
-
This node requires a
usernamein the incoming node state to assess whether the user has a registered device.Implement the Platform Username node as an input to the WebAuthn Authentication node.
-
Optionally, this node can read the contents of the
webAuthnExtensionsshared state property as input.You can populate the
webAuthnExtensionsproperty with any JSON object you choose using a script or in a node that occurs earlier in the journey. If this property is populated, its contents are placed in theextensionsentry passed to the browser or authenticator. If this property is empty, an empty JSON object is passed to the browser or authenticator.You can find more information on WebAuthn extensions in WebAuthn Extensions.
Dependencies
For successful authentication, this node depends on:
-
A client that supports web authentication
-
A registered FIDO device
Configuration
| Property | Usage |
|---|---|
Relying party identifier |
The domain used as the relying party identifier during web authentication. This is the domain against which to register the device. If you leave this field blank, it defaults to
the domain name of your tenant, for example, |
Origin domains |
A list of fully qualified URLs to accept as the origin of the incoming request. If this field is empty, the accepted origin is the incoming request origin. |
User verification requirement |
The required user verification level. The available options are:
|
Allow recovery codes |
If you select this option, PingOne Advanced Identity Cloud lets the user enter a recovery code instead of performing an authentication gesture. Enabling this options adds a |
Timeout |
The number of seconds to wait for a valid WebAuthn authenticator to be registered before failing. If the specified timeout is reached, evaluation continues along the |
Username from device |
Specifies whether PingOne Advanced Identity Cloud should get the username from the device. If you enable this option and the device is unable to store or provide usernames,
the node fails and evaluation continues along the You can find information on using this property for usernameless authentication with ForgeRock Go in Configure usernameless authentication with ForgeRock Go. |
Return challenge as JavaScript |
Choose how the node should return its challenge for consumption by your front-end user interface:
|
Detect sign count mismatch |
If you enable this option, the node compares the authenticator’s sign count (signature counter) with the sign count stored in the user’s profile. If the authenticator sign count is less than or equal to the stored value, evaluation continues to the Sign Count Mismatch outcome. |
Outcomes
Unsupported-
If the user’s client doesn’t support web authentication, evaluation continues along the
Unsupportedoutcome path. For example, clients connected over the HTTP protocol rather than HTTPS don’t support WebAuthn; however, HTTPS may not be required when testing locally onhttp://localhost. Learn more in Is origin potentially trustworthy?. No Device Registered-
If the user doesn’t have a registered device, evaluation continues along the
No Device Registeredoutcome path. Success-
If the user successfully authenticates with a device of the type determined by the User verification requirement property, evaluation continues along the
Successoutcome path. Failure-
If the node encounters an issue when attempting to authenticate the user with the device, evaluation continues along the
Failureoutcome path; for example, if the node can’t verify that the response from the authenticator was appropriate for the specific instance of the authentication journey. Client Error-
If the user’s client encounters an issue when attempting to authenticate using the device, for example, if the timeout was reached, evaluation continues along the
Client Erroroutcome path.The journey takes this path whenever the client throws a
DOMException, as required by the Web Authentication: An API for accessing Public Key Credentials Level 1 specification. Recovery Code-
If Allow recovery code is enabled, the node gives the user an option to enter a recovery code rather than authenticate using a device. If the user enters a recovery code, evaluation continues along the
Recovery Codeoutcome path.This outcome path must lead to a Recovery Code Collector Decision node to let PingOne Advanced Identity Cloud accept and verify the recovery code.
Sign Count Mismatch-
If Detect sign count mismatch is enabled and the authenticator sign count is less than or equal to the value stored in the user’s profile, evaluation continues to the Sign Count Mismatch outcome.
This outcome can help to detect cloned or malfunctioning authenticators. A sign count mismatch doesn’t necessarily indicate that the operation was performed by a cloned authenticator. Address this situation appropriately for your deployment, for example, by using a scripted decision node.
The node itself is considered to have succeeded even if evaluation leads to this outcome. Therefore, if it suits your deployment, you can design your journey to continue through this outcome.
Outputs
-
If a client error occurs, the node adds the error type and description to a property named
WebAuthenticationDOMExceptionin the shared state. Other nodes can read this property later in the journey, if required. -
PingAM On successful authentication, the node adds the UUID of the device (
webauthnDeviceUuid) and the name of the device (webauthnDeviceName) to the shared state.This lets you track the use of biometric authentication and the device used to authenticate.
-
PingAM On successful authentication, the node adds a
webauthnAssertionInfoobject to the transient state.The
webauthnAssertionInfoobject includes the following information:{ "authenticatorAttachment": "platform", "flags": { "UP": true, "UV": true, "ED": false, "AT": false, "BE": true, "BS": true } }jsonThe
authenticatorAttachmentfield is only populated when the UI or client application supports sending it This field lets the journey identify whether the device used to authenticate was a roaming (cross-platform) device or a client-bound (platform) device. Learn more in Authenticator Attachment Modality in the WebAuthn specification.The
flagsprovide additional information about the authenticator. Learn more about these flags in Authenticator Data in the WebAuthn specification.-
With the exception of the
webauthnAssertionInfoobject, the contents of the transient state for this node aren’t public. Don’t rely on them in your scripts.
-
Example
This example shows one possible implementation of the flow for authenticating with WebAuthn devices:
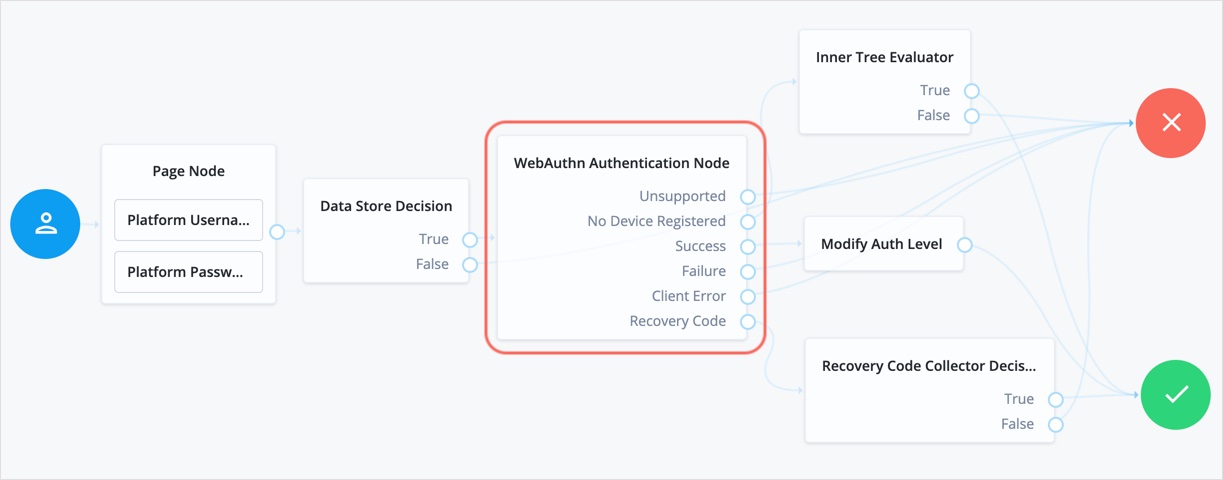
After verifying the users credentials against the configured data store, evaluation continues to the WebAuthn Authentication node.
If the user’s client doesn’t support WebAuthn, authentication fails and the user doesn’t get a session.
A more user-friendly approach would be to set a success URL
to redirect the user to a page explaining the benefits of multi-factor authentication,
and then proceeding to the Success node.
If there are no registered WebAuthn devices present in the user’s profile, the failure URL is set, pointing to a flow that lets the user register a device. This stage could also be an Inner Tree Evaluator node.
If the user’s client supports WebAuthn, and the connection is secured with TLS, the user is prompted to complete an authorization gesture, for example, scanning a fingerprint, or entering a PIN:
The user’s browser may present a consent pop-up to allow access to the authenticators available on the client. When consent has been granted, the browser activates the relevant authenticators, ready for authentication.
|
The relying party details configured in the node are often included in the consent message to help the user verify the entity requesting access. |
The authenticators the client activates for authentication depend on the value of the properties in the node.
For example, if the User verification requirement property is set to REQUIRED,
the client SHOULD only activate authenticators that verify the identity of the user.
For extra protection, PingOne Advanced Identity Cloud WILL verify that the response from an authenticator
matches the criteria configured for the node, and will reject an authentication attempt
by an inappropriate authenticator type by routing it to the Failure outcome.
When the user completes an authorization gesture, for example,
by scanning a fingerprint or entering a PIN, evaluation continues along the Success outcome path.
In this example,
their authentication level is increased by ten to signify the stronger authentication that has occurred,
and the user is taken to their profile page.
If the user clicks the Use Recovery Code button, evaluation continues
to the Recovery Code Collector Decision node, ready to accept the recovery code.
If verified, the user is taken to their profile page.
Any problems encountered during authentication lead to the Failure outcome,
including a timeout, or to the Client Error outcome, resulting in an authentication failure.
WebAuthn Device Storage node
Writes information about FIDO2 devices to a user’s profile. The user can subsequently authenticate using the device.
Use this node to store the device data the WebAuthn Registration node places into the transient node state when its Store device data in transient state property is enabled.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
Success -
Failure -
Exceed Device Limit
If AM encounters an issue when attempting to save the device data to the user’s profile;
for example, the user was not identified earlier, then evaluation continues along the Failure outcome path.
If the Maximum Saved Devices property is set to an integer greater than zero, and registering a new device would take the number of devices above the specified threshold, then evaluation continues down the Exceed Device Limit outcome path. In this case, you may need to instruct your users to log in with an existing device in order to remove one or more of their registered devices.
If the node successfully stores the device data to the user’s profile,
evaluation continues along the Success outcome path.
Properties
| Property | Usage | ||
|---|---|---|---|
Generate recovery codes |
Specify whether WebAuthn device recovery codes should be generated. If enabled, recovery codes are generated and stored in the transient node state, and stored alongside the device profile. Use the Recovery Code Display node to display the codes to the user for safe keeping.
|
||
Maximum Saved Devices |
Specify the maximum number of WebAuthn devices to save in a user’s profile. Set this property to When this property is greater than zero, the |
WebAuthn Registration node
The WebAuthn Registration node lets users of supported clients register FIDO2 devices for use during authentication.
What are the differences between WebAuthn and device binding/signing?
There are many similarities between WebAuthn and device binding and JWS verification. We provide authentication nodes to implement both technologies in your journeys.
Both can be used for usernameless and passwordless authentication, they both use public key cryptography, and both can be used as part of a multi-factor authentication journey.
One major difference is that with device binding, the private key never leaves the device.
With WebAuthn, there is a possibility that the private key is synchronized across client devices because of Passkey support, which may be undesirable for your organization.
For details of the differences, refer to the following table:
| Feature | WebAuthn / FIDO | Device Binding / JWS Verifier | Details |
|---|---|---|---|
Industry-standards based |
✅ |
❌ |
You can refer to the WebAuthn W3C specification. Device binding and JWS verification are proprietary implementations. |
Public key cryptography |
✅ |
✅ |
Both methods use Public key cryptography. |
Usernameless support |
✅ |
✅ |
After registration, the username can be stored in the device and obtained during authentication without the user having to enter their credentials. |
Keys are bound to the device |
❌ |
✅ |
With WebAuthn, if Passkeys are used, they can be shared across devices. With device binding, the private keys do not leave the device. |
Sign custom data |
❌ |
✅ |
With device binding, you can:
|
Format of signed data |
|||
Integration |
❌ |
✅ |
With device binding, after verification, the signed JWT is available in:
This enables the data within to be used for integration into your processes and business logic. |
Platform support |
✅ Android ✅ iOS ✅ Web browsers |
✅ Android ✅ iOS ❌ Web browsers |
As it is challenging to store secure data in a browser as a client app, device binding is not supported in web browsers. |
Authenticator support |
Determined by the platform. Configuration limited to:
|
Determined by the authentication node. Full configuration options:
|
With device binding, you can specify what authentication action the user must perform to get access to the private keys. This provides greater flexibility in your security implementation and can reduce authentication friction for your users. |
Key storage |
Web browsers and iOS synchronize to the cloud. Android has the option to synchronize to the cloud. |
|
Both technologies store the private keys securely on the client. WebAuthn supports synchronizing the private keys to the cloud for use on other devices. This can reduce authentication friction for your users but may also increase the risk of a breach. |
Managing device keys |
Managed by the device OS. Apps cannot delete local client keys programmatically and do not have a reference to the remote server key for deletion. |
Managed by the Ping SDKs. Provides an interface to delete local client and remote server keys. |
The ability to programmatically delete both client and server keys can greatly simplify the process of registering a new device if an old device is lost or stolen. |
Passkey support |
✅ |
❌ |
WebAuthn supports synchronizing the private keys to the cloud for use on other devices. Device binding keeps the private key locked in the device. |
App integrity verification |
|
Not provided by the device binding or verification nodes. It can be added as part of the journey by using app integrity nodes. |
App integrity verification helps ensure your users are only using a supported app rather than a third-party or potentially malicious version. |
Key attestation |
|
|
Key attestation verifies that the private key is valid and correct, is not forged, and was not created in an insecure manner. |
Complexity |
Medium |
Low |
WebAuthn requires a bit more configuration, for example, creating and uploading the Device binding only requires the journey and the SDK built into your app. |
PingOne Advanced Identity Cloud interacts with FIDO2/WebAuthn capable browsers, such as Chrome, Firefox and Microsoft Edge.
These browsers interact with the following:
-
Client to Authenticator Protocol 2 (CTAP2) authenticators, including Universal 2nd Factor (U2F) and FIDO2 Security Keys
-
Platforms such as Windows Hello and Apple Touch ID
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
-
This node requires the
usernameandpasswordproperties in the incoming node state.+ Implement the Platform Username node and Platform Password node before this node in the journey.
-
Optionally, this node can read the contents of the
webAuthnExtensionsshared state property as input.You can populate the
webAuthnExtensionsproperty with any JSON object you choose using a script or in a node that occurs earlier in the journey. If this property is populated, its contents are placed in theextensionsentry passed to the browser or authenticator. If this property is empty, an empty JSON object is passed to the browser or authenticator.You can find more information on WebAuthn extensions in WebAuthn Extensions.
Dependencies
You must configure the WebAuthn Profile Encryption service to use this node.
Configuration
| Property | Usage | ||
|---|---|---|---|
Relying party |
The name of the relying party entity that registers and authenticates users by using WebAuthn. This could be the name of the organization, realm, and so on. For example, |
||
Relying party identifier |
The domain used as the
relying party identifier during WebAuthn.
If not specified, AM uses the domain name of the instance, such as Specify an alternative domain if your AM instances are behind a load balancer. |
||
Origin domains |
A set of fully-qualified URLs of accepted origins, for example |
||
User verification requirement |
The required level of user verification. The available options are:
Default: |
||
Preferred mode of attestation |
Indicates whether the authenticator must provide attestation statements. The available options are:
PingOne Advanced Identity Cloud supports the following attestation formats:
|
||
Accepted signing algorithms |
The algorithms authenticators can use to sign their assertions. |
||
Authentication attachment |
If specified, PingOne Advanced Identity Cloud filters out authenticators that don’t match the attachment type. There are two attachment types:
Available options for this property are:
|
||
Trust Store alias |
The alias of the realm trust store holding the secrets necessary to validate a supplied attestation certificate.
The alias can only contain the characters This value is appended to the string |
||
Enforce revocation check |
Whether to enforce the checking of revocation entries from certificates. If you enable this setting, any attestation certificate’s trust chain must have a CRL or OCSP entry that PingOne Advanced Identity Cloud can verify. If you disable this setting, PingOne Advanced Identity Cloud doesn’t check presented certificates for revocation.
|
||
Timeout |
The number of seconds to wait for a response from an authenticator. If the specified time is reached, evaluation continues along the |
||
Limit registrations |
Indicates whether the same authenticator can be registered multiple times. If you enable this property, the client won’t activate an authenticator that’s already registered for registration. |
||
Generate recovery codes |
Indicates whether PingOne Advanced Identity Cloud generates WebAuthn-specific recovery codes. If enabled, PingOne Advanced Identity Cloud generates recovery codes and stores them in the transient state if registration is successful. Use the Recovery Code Display node to display the codes to the user for safe-keeping. Don’t enable this property if you’ve enabled the Store device data in transient state property (and aren’t saving the device data to the user’s profile immediately). Enable the Generate recovery codes property in the WebAuthn Device Storage node instead.
|
||
Store data in transient state |
If you enable this property, the node stores the following data in transient state:
|
||
Store device data in transient state |
If you enable this property, information about the device required for WebAuthn is stored in transient state instead of saved immediately to the user’s profile. Enable this option under the following conditions:
If you enable this option, use the WebAuthn Device Storage node to write the device data to the user’s profile. If this option is disabled, device data is written automatically to the user’s profile when registration is successful. |
||
Username to device |
This option specifies that the device should store the user’s username. If you enable this option, devices that don’t support storing and providing the username won’t be able to use this node. If the device can’t store or provide usernames, the node fails and the journey follows the Failure outcome. You can find information on using this property for usernameless authentication with ForgeRock Go in Configure usernameless authentication with ForgeRock Go. |
||
Shared state attribute for display name |
The share state property that contains a display name for the user. For example, their full name, or email address. When Username to device is enabled, PingOne Advanced Identity Cloud writes the value stored in this property to devices in addition to the username. This helps the user select between the accounts they may have on their devices. If you don’t set this property, or if the variable isn’t found in shared state, the username is used. You can find information on using this property for usernameless authentication with ForgeRock Go in Configure usernameless authentication with ForgeRock Go. |
||
Return challenge as JavaScript |
Choose how the node should return its challenge for consumption by your front-end user interface:
|
||
Maximum Saved Devices |
The maximum number of WebAuthn devices that can be stored in the user’s profile. Set this property to When this property is greater than zero, the
|
||
Validate FIDO-U2F attestation AAGUID |
If enabled, the node validates the Authenticator Attestation Global Unique Identifier (AAGUID) for any FIDO-U2F attestation type. The AAGUID must be 16 bytes, initialized with all zeros. |
||
FIDO Certification Level |
The minimum FIDO certification level that the device’s certification status must satisfy during a registration flow. If this setting is Other options include:
|
Outputs
-
The node passes the contents of the
webAuthnExtensionsproperty to the browser or authenticator. -
If a timeout is reached, or any other client error occurs, the error type and description are added to the
WebAuthenticationDOMExceptionshared state property. -
If Shared state attribute for display name is set, the node writes the username or display name to shared state as a value of the specified property.
-
If Store data in transient state is set, the node writes the following data to transient state on successful registration:
-
Information provided by the device is stored in the
webauthnDataproperty. -
The attestation type achieved is stored in the
webauthnAttestationTypeproperty. -
PingAM Additional attestation information is stored in the
webauthnAttestationInfoobject.The
webauthnAttestationInfoobject includes the following information:{ "authenticatorAttachment": "platform", "flags": { "UP": true, "UV": true, "ED": false, "AT": false, "BE": true, "BS": true } }jsonThe
authenticatorAttachmentfield is added only if Return challenge as JavaScript is enabled. This field lets the journey identify whether the end user registered a roaming (cross-platform) device or a client-bound (platform) device. Learn more in Authenticator Attachment Modality in the WebAuthn specification.The
flagsprovide additional information about the authenticator. Learn more about these flags in Authenticator Data in the WebAuthn specification.
-
Outcomes
- Unsupported
-
If the user’s client doesn’t support WebAuthn, evaluation continues along the
Unsupportedoutcome path. For example, clients connected over the HTTP protocol rather than HTTPS don’t support WebAuthn. - Success
-
If the user successfully registers an authenticator of the correct type as determined by the node’s properties, evaluation continues along the
Successoutcome path. - Failure
-
If PingOne Advanced Identity Cloud encounters an issue when attempting to register a user’s device, evaluation continues along the
Failureoutcome path. For example, if PingOne Advanced Identity Cloud can’t verify that the response from the authenticator was appropriate for the specific instance of the authentication ceremony. - Client Error
-
If the user’s client encounters an issue when attempting to register using a device, for example, if the timeout was reached, evaluation continues along the
Client Erroroutcome path. The node follows this outcome whenever the client throws aDOMException, as required by the WebAuthn specification.If a client error occurs, the error type and description are added to the
WebAuthenticationDOMExceptionshared state property. If required, this property can be read by nodes later in the journey. - Exceed Device Limit
-
If the Maximum Saved Devices property is an integer greater than zero, and registering a new device would take the number of devices above the specified threshold, evaluation continues down the
Exceed Device Limitoutcome path. In this case, you might need to instruct users to log in with an existing device to remove one or more of their registered devices.
Example
The following sample journey registers WebAuthn devices:
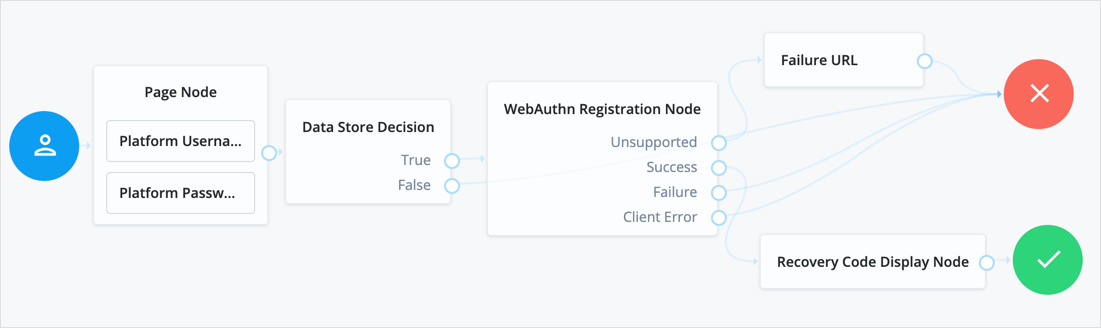
If the user’s client doesn’t support WebAuthn, the failure URL is altered, for example to redirect the user to a page explaining which clients and operating systems support WebAuthn.
If the user’s client does support WebAuthn, and the connection is secured with TLS, AM prompts the user to register an authenticator:
The user’s browser may present a consent pop-up to allow access to the authenticators available on the client. When consent has been granted, the browser activates the relevant authenticators, ready for registration.
|
The relying party details configured in the node are often included in the consent message to help the user verify the entity requesting access. |
The authenticators the client activates for registration depend on the value of the properties in the node.
For example, if the User verification requirement property is set to REQUIRED,
the client would not activate a USB hardware security key for registration.
When the user completes an authorization gesture, for example,
by scanning a fingerprint or entering a PIN,
the evaluation continues along the Success outcome path, and in this example will be taken to their profile page.
The registered authenticator appears on the user’s dashboard page, with the label New Security Key. To rename the authenticator, click its vertical ellipsis context icon, , and click Rename.
Any problems encountered during the registration, including a timeout,
results in the evaluation continuing to the Failure outcome.
Risk management nodes
Account Active Decision node
The Account Active Decision node determines whether the current account is both active and unlocked, and lets the journey make a decision, based on that check.
An account is considered locked under these conditions:
-
The status is inactive.
-
The status is active and a duration lockout is set on the account.
An account is considered unlocked under this condition:
-
The status is active and no duration lockout is set on the account.
The node determines whether the account has been locked through both persistent (physical) lockout and duration lockout. Learn more in Account lockout.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
The node reads the user’s identity from the shared state. Implement a Platform Username node before this node in the journey.
Outcomes
-
TrueThe journey follows this outcome path if the account is assessed to be
activeandunlocked. -
FalseThe journey follows this outcome path if the account is assessed to be
inactiveorlocked.
Errors
If the node cannot read the identity of the account, it throws the following exception:
Failed to get the identity object
Examples
In this simple login journey, authentication fails if the account is assessed to be inactive or locked.
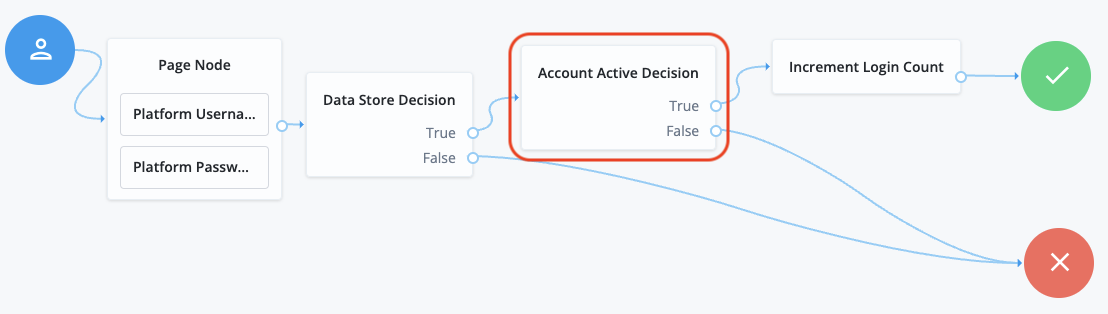
This example uses the following nodes:
-
The Page node prompts the user to input their username and password:
-
The Platform Username node collects the username and stores it in the shared state.
-
The Platform Password node collects the password and stores it in the shared state.
-
-
The Data Store Decision node uses the username and password to determine whether the account exists.
-
The Account Active Decision node determines whether the account is active and unlocked.
-
If the account is active and unlocked, the Increment Login Count node increments the login count and authentication succeeds.
-
If the account is inactive or locked, the authentication fails.
Account Lockout node
The Account Lockout node locks or unlocks the authenticating user’s account profile.
The node also determines whether the account has been locked through both persistent (physical) lockout and duration lockout. Learn more in Account lockout.
| You can also use the Account Active Decision node to check whether the account is locked at any point in the journey. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the username property in the incoming node state.
It uses this information to access the account status in the user profile.
It also requires the realm property, which PingOne Advanced Identity Cloud sets by default.
Configuration
| Property | Usage |
|---|---|
Lock Action |
Choose whether to |
Outcomes
Single outcome path; the node updates the account status according to the configured Lock Action:
LOCK-
The account is inactive and the user cannot authenticate.
UNLOCK-
The account is active and the user can authenticate.
Errors
If this node fails to set the account status, it logs a failed to set the user status inactive warning.
This node can also throw exceptions with the following messages:
| Message | Notes |
|---|---|
|
Failed to read the |
|
Failed to read the |
|
Failed to find the account profile with this |
|
Failed to update the account status; applies when locking and unlocking the account |
Example
The following simple example uses this node with the Retry Limit Decision node to lock an account after the set number of invalid attempts:
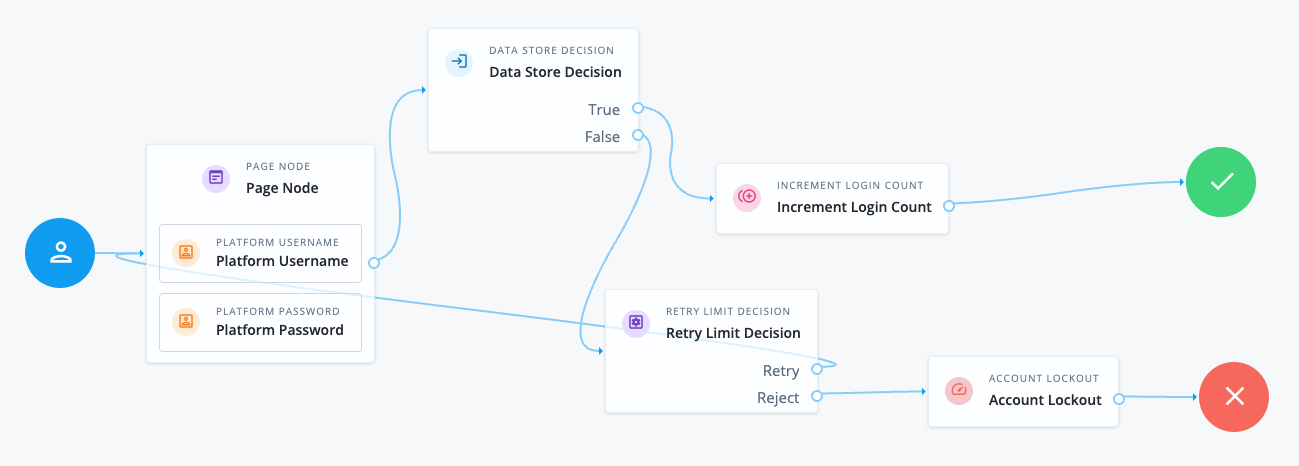
The Retry Limit Decision node Retry limit (default: 3) defines the number of failed attempts before lockout.
Before using a journey like this in deployment, adapt it to reset the retry count on successful authentication.
Auth Level Decision node
Compares the current authentication level value against a configured value.
CAPTCHA node
The CAPTCHA node adds CAPTCHA support by verifying the response token received from the CAPTCHA provider and creating a callback for the UI to interact with.
By default, the node is configured for Google’s reCAPTCHA v2.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
|
This node only supports reCAPTCHA v2 and v3, and hCaptcha. For Google reCAPTCHA Enterprise support, use the reCAPTCHA Enterprise node. |
Dependencies
You need to sign up for access to the reCAPTCHA API to get the API key pair required for configuring the node.
Configuration
| Property | Usage | ||
|---|---|---|---|
CAPTCHA Site Key (required) |
The CAPTCHA site key supplied by the CAPTCHA provider when you sign up for access to the API. |
||
CAPTCHA Secret Key |
The CAPTCHA secret key supplied by the CAPTCHA provider when you sign up for access to the API.
|
||
CAPTCHA Secret Label Identifier |
An identifier used to create a secret label for mapping to a secret in a secret store. PingOne Advanced Identity Cloud uses this identifier to create a specific secret label for this node.
The secret label takes the form The identifier can only contain alphanumeric characters If you set a CAPTCHA Secret Label Identifier and PingOne Advanced Identity Cloud finds a matching secret in a secret store, the CAPTCHA Secret Key is ignored. |
||
CAPTCHA Verification URL |
The URL used to verify the CAPTCHA submission. Use |
||
CAPTCHA API URL (required) |
The URL of the JavaScript that loads the CAPTCHA widget. Use |
||
Class of CAPTCHA HTML Element |
The class of the HTML element required by the CAPTCHA widget. Use |
||
ReCaptcha V3 node |
If you’re using Google reCAPTCHA, specify whether it’s v2 or v3. Turn on for v3. |
||
Score Threshold |
If you’re using Google reCAPTCHA v3, enter a score threshold. The CAPTCHA provider returns a score for each user request, based on observed interaction with your site. CAPTCHA "learns" by observing real site traffic, so scores in a staging environment or in a production deployment that has just been implemented might not be very accurate. A score of 1.0 is likely a good user interaction, while 0.0 is likely to be a bot. The threshold you set here determines whether to allow or deny access, based on the score returned by the CAPTCHA provider. Start with a threshold of 0.5. Learn more about score thresholds in the Google documentation. |
||
Disable submission until verified |
If selected, form submission is disabled until CAPTCHA verification succeeds. Default: Enabled |
Outcomes
True-
The CAPTCHA response was successfully verified.
False-
The CAPTCHA response wasn’t verified or failed verification.
Errors
This node can throw exceptions with the following messages:
-
CAPTCHA response required for verification -
Unable to verify CAPTCHA response -
Unable to retrieve state from token response -
No secret key found
Example
The following journey uses a Page node and a Data Store Decision node to collect and verify the credentials and a CAPTCHA response:
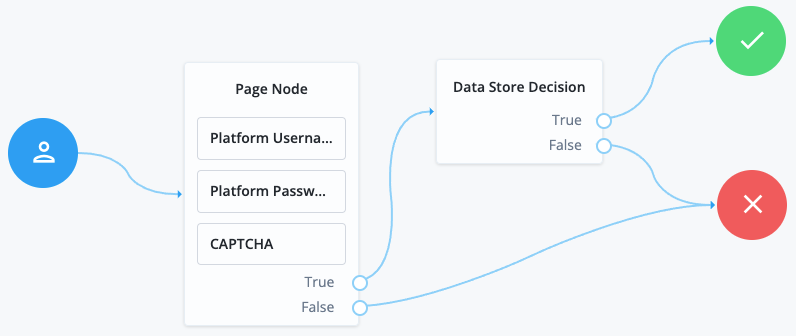
This example uses the following nodes:
-
The Page node prompts the user to input their username and password:
-
The Platform Username node collects the username and stores it in the shared state.
-
The Platform Password node collects the password and stores it in the shared state.
-
The CAPTCHA node collects and verifies the CAPTCHA response.
-
-
The Data Store Decision node uses the username and password to determine whether authentication is successful.
reCAPTCHA Enterprise node
The reCAPTCHA Enterprise node adds Google reCAPTCHA Enterprise support to your journeys.
Google reCAPTCHA Enterprise offers improvements over previous versions, including more granular scores, reason codes for events deemed higher risk, Web Application Firewall (WAF) support, and native support for Android and iOS.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
-
Only the Ping SDKs support the reCAPTCHA Enterprise functionality this node provides.
The following user interfaces do not support this node:
-
Advanced Identity Cloud hosted pages
-
PingAM User UI
-
-
This node only supports Google reCAPTCHA Enterprise.
For reCAPTCHA v2 and v3 support, and hCaptcha support, use the CAPTCHA node.
Inputs
This node reads an optional CaptchaEnterpriseNode.PAYLOAD variable from shared state.
Use this variable to customize the payload the node sends to the Google reCAPTCHA Enterprise server for assessment.
You can set the value by using a Set State node, or by using a Scripted Decision node, using a script similar to the following:
var username = nodeState.get("username");
var customPayload =
JSON.parse(`{"userInfo": {"accountId": "${username}"}}`);
sharedState.put("CaptchaEnterpriseNode.PAYLOAD", customPayload);
outcome = "true";To learn more about the payload, refer to Project Assessments - Event in the Google Developer documentation.
Dependencies
You need to sign up for access to the reCAPTCHA API to get the API key pair required to configure the node.
Configuration
| Property | Usage |
|---|---|
Google Cloud project ID |
The ID of the project that has Google reCAPTCHA enabled. You can get the ID of your project in the Google Cloud console. For example, |
reCAPTCHA Site Key (required) |
The ID of the reCAPTCHA key you created in the Google Cloud console. The key can be for any platform type, Sometimes referred to as a key ID in the Google Cloud console and documentation. |
reCAPTCHA API key secret identifier |
An identifier used to create a secret label for mapping to your Google reCAPTCHA API key in a secret store. Get or create your API key from the Google Cloud Console under APIs and Services > Credentials. The secret label takes the form The identifier can only contain alphanumeric characters |
Score Threshold |
The score threshold for determining if a user is likely to be a real person. reCAPTCHA scores are between If the returned score is equal to or greater than the threshold the journey continues along the To learn more, refer to Interpret scores in the Google documentation. |
Store reCAPTCHA assessment JSON |
Stores the assessment response JSON for future reference within the journey. The node stores the JSON response in the |
Store reCAPTCHA error messages |
Stores the error messages for future reference within the journey. The node stores the error messages in the The error consists of an error code and description of the error. View the possible error codes
|
reCAPTCHA CSS class |
A CSS class to apply to the HTML elements reCAPTCHA adds to JavaScript apps. The default is |
reCAPTCHA Verification URL |
The URL to send the reCAPTCHA to for verification. Only change this if Google updates the URL used for reCAPTCHA verifications. The default is |
JavaScript reCAPTCHA API URL |
The URL of the JavaScript file containing the reCAPTCHA API. Only change this if Google releases a new version of the JavaScript reCAPTCHA API. The default is |
Outputs
If you enable the Store reCAPTCHA assessment JSON property, the node outputs the reCAPTCHA assessment response JSON in a state variable named CaptchaEnterpriseNode.ASSESSMENT_RESULT.
If you enable the Store reCAPTCHA error messages property, the node outputs the error response JSON in a state variable named CaptchaEnterpriseNode.FAILURE.
Outcomes
True-
The reCAPTCHA response was successfully verified.
False-
The reCAPTCHA response wasn’t verified or failed verification.
Example
The following journey uses a Page node and a Data Store Decision node to collect and verify the credentials and a CAPTCHA response:
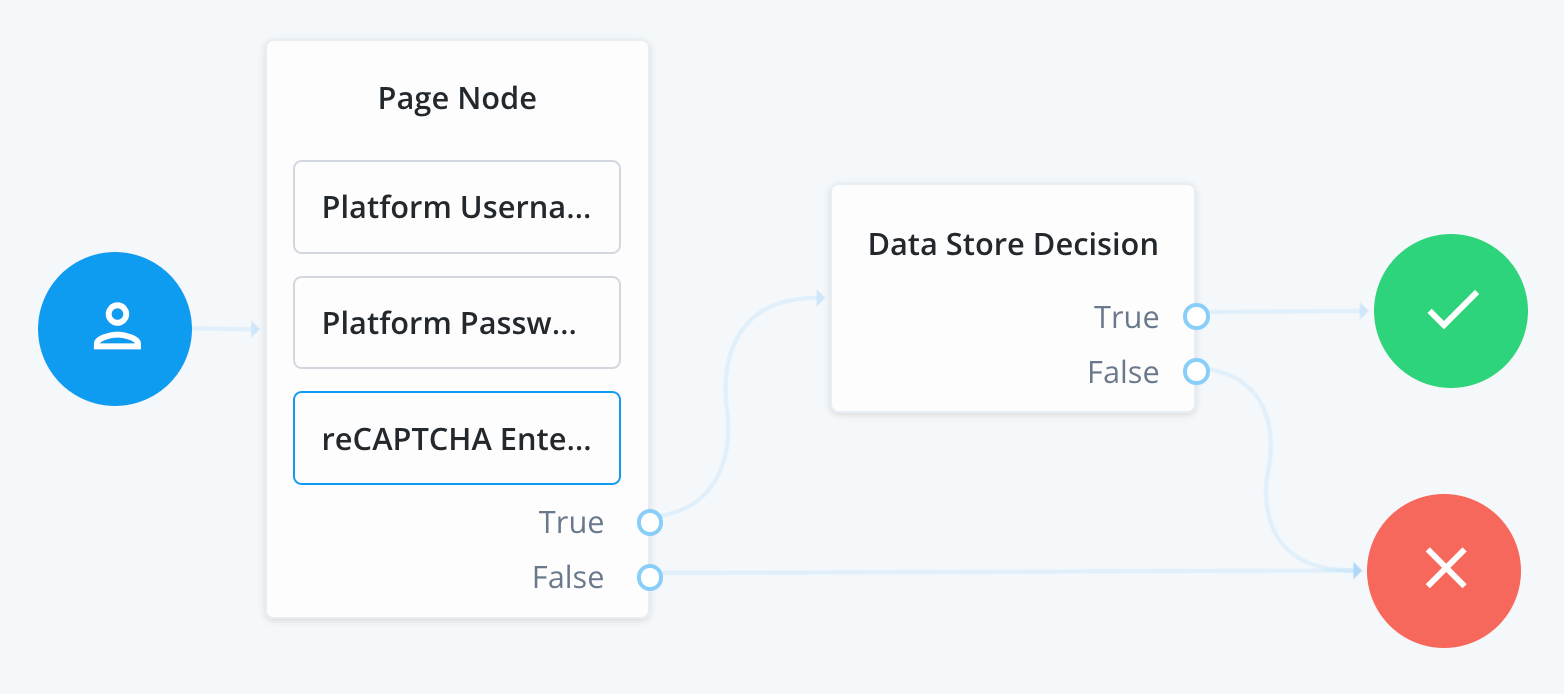
This example uses the following nodes:
-
The Page node prompts the user to input their username and password:
-
The Platform Username node collects the username and stores it in the shared state.
-
The Platform Password node collects the password and stores it in the shared state.
-
The reCAPTCHA Enterprise node collects and verifies the reCAPTCHA Enterprise response.
-
-
The Data Store Decision node uses the username and password to determine successful authentication.
Legacy CAPTCHA node
Verifies the response token received from the CAPTCHA verifier, and creates a CAPTCHA callback for the UI to interact with. Default values are for Google ReCAPTCHA.
| This node has been superseded by the CAPTCHA node. Use that node instead. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
CAPTCHA Site Key (required) |
The CAPTCHA site key supplied by the CAPTCHA provider when you sign up for access to the API. |
CAPTCHA Secret Key (required) |
The CAPTCHA secret key supplied by the CAPTCHA provider when you sign up for access to the API. |
CAPTCHA Verification URL (required) |
The URL used to verify the CAPTCHA submission. Use |
CAPTCHA API URL (required) |
The URL of the JavaScript that loads the CAPTCHA widget. Use |
Class of CAPTCHA HTML Element |
The class of the HTML element required by the CAPTCHA widget. Use |
Behavioral nodes
Increment Login Count node
The Increment Login Count node increments the successful login count property of a managed object.
Use the Login Count Decision node to change the flow of the journey based on the count.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node’s Identity Attribute specifies the property it requires in the incoming node state. It uses this property to access the managed object.
Configuration
| Property | Usage |
|---|---|
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Errors
If this node fails to access the managed object, it throws an exception with a No object to increment message.
If this node fails to increment the login count, it logs an Unable to increment login count warning message.
Example
The following journey uses the Increment Login Count node to update the login count on successful authentication:
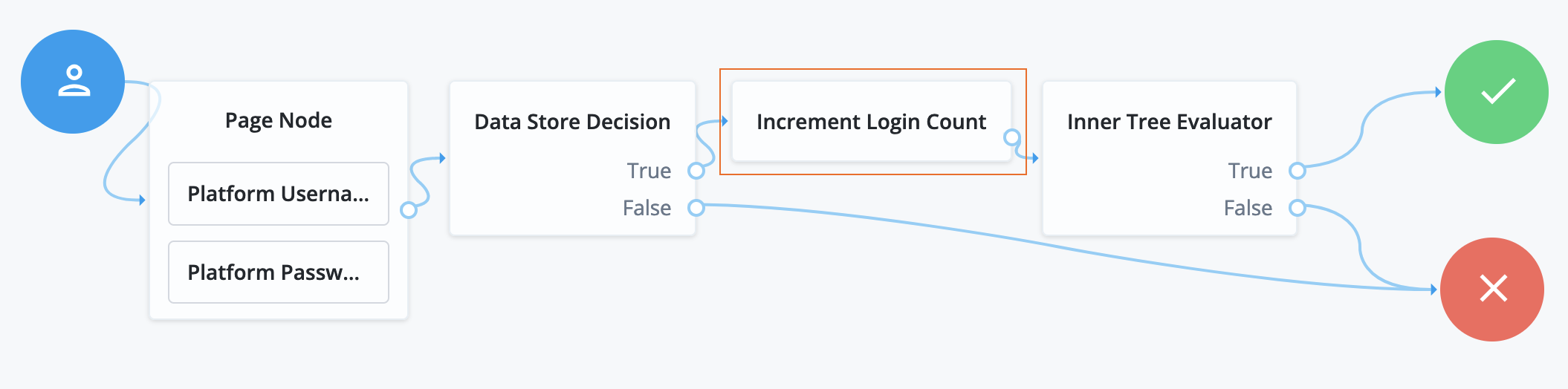
-
The Platform Username node injects the
userNameinto the shared node state. -
The Data Store Decision node determines whether authentication is successful.
-
The Increment Login Count node (outlined in the image) updates the login count.
-
The Inner Tree Evaluator node invokes the following nested journey for progressive profiling:
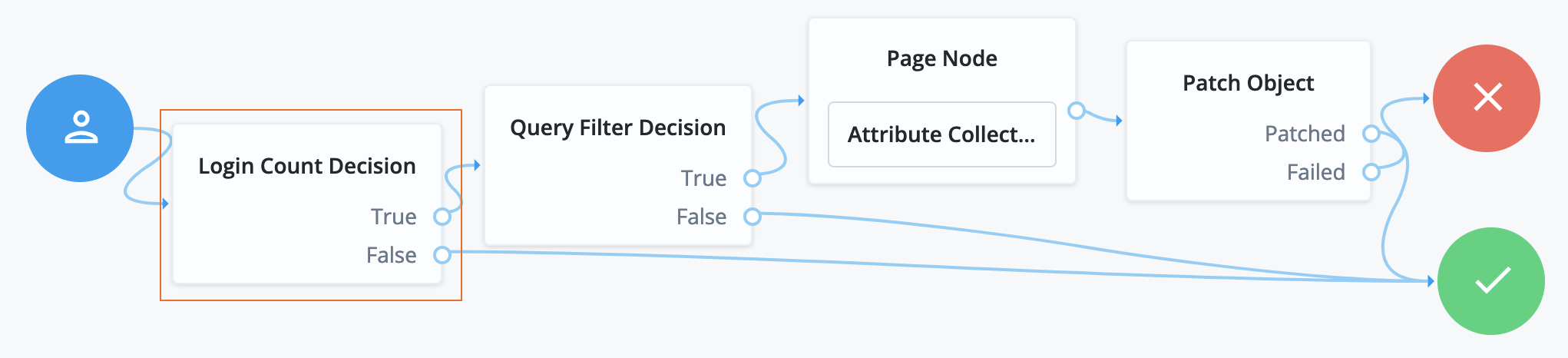
-
The Login Count Decision node triggers the rest of the journey depending on the login count and its settings.
-
The Query Filter Decision node determines whether managed object profile fields are still missing.
-
The Page node requests additional input for the profile.
-
The Patch Object node stores the additional input in the managed object profile.
Login Count Decision node
The Login Count Decision node triggers an action when a user’s successful login count property reaches a specified number.
Use the Increment Login Count node to set the login count on successful authentication.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node’s Identity Attribute specifies the property it requires in the incoming node state. It uses this property to access the managed object.
Configuration
| Property | Usage |
|---|---|
Interval |
Trigger the
Default: |
Amount |
The login count to trigger a Default: 25 |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Outcomes
True-
The login count reached Amount, and the Interval setting triggered this outome.
False-
All other cases.
Errors
This node can throw exceptions with the following messages:
| Message | Notes |
|---|---|
|
Failed to read the specified Identity Attribute in the shared node state |
|
Failed to find the managed object using the Identity Attribute value from the shared node state |
|
Failed to read the managed object’s login count |
Example
The following journey uses the Increment Login Count node to update the login count on successful authentication:
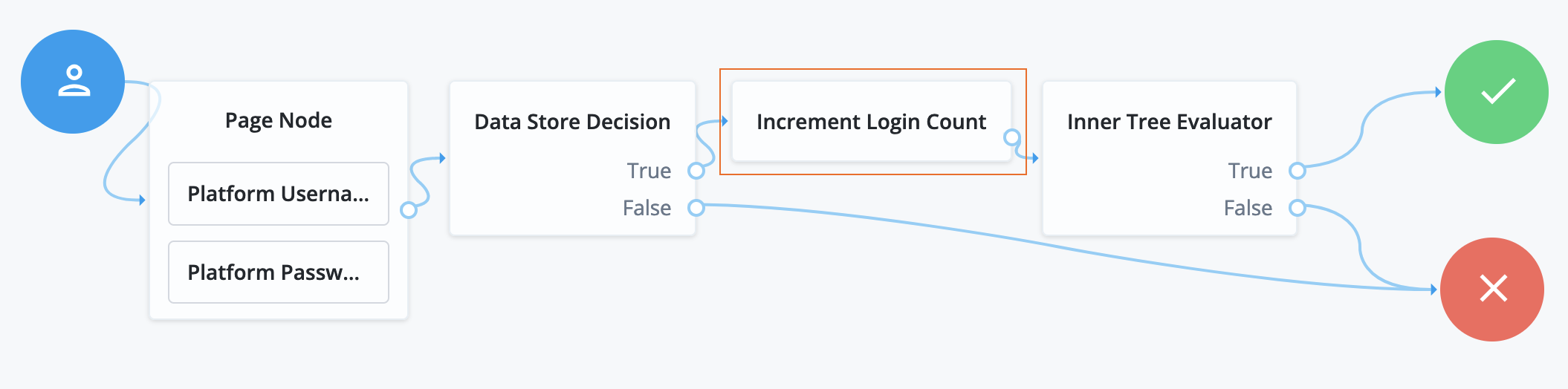
-
The Platform Username node injects the
userNameinto the shared node state. -
The Data Store Decision node determines whether authentication is successful.
-
The Increment Login Count node (outlined in the image) updates the login count.
-
The Inner Tree Evaluator node invokes the following nested journey for progressive profiling:
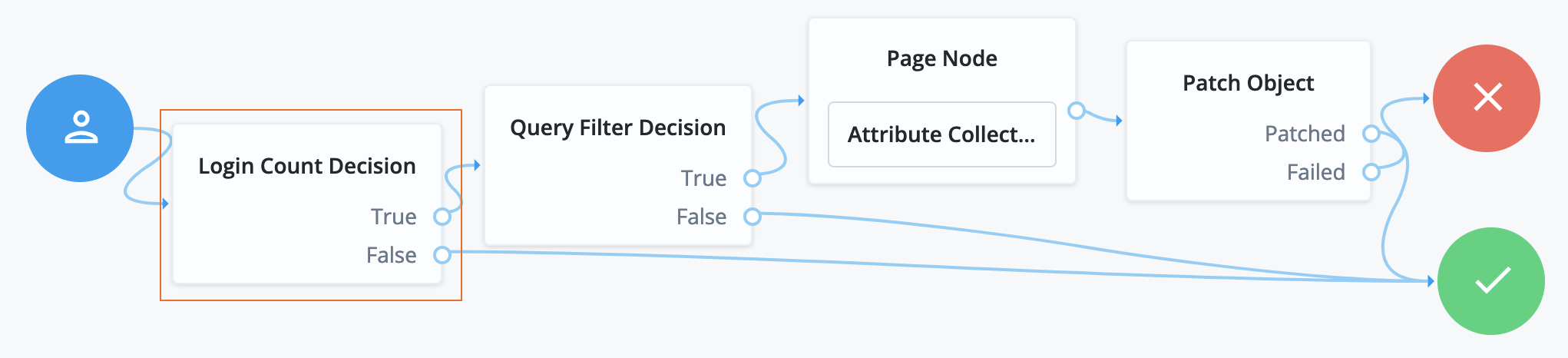
-
The Login Count Decision node triggers the rest of the journey depending on the login count and its settings.
-
The Query Filter Decision node determines whether managed object profile fields are still missing.
-
The Page node requests additional input for the profile.
-
The Patch Object node stores the additional input in the managed object profile.
Contextual nodes
Certificate Collector node
The Certificate Collector node collects an X.509 digital certificate from the request. The journey can use the collected certificate as authentication credentials for a user or OAuth 2.0 client.
PingAM accepts certificates in PEM and DER format.
Advanced Identity Cloud accepts certificates in DER format.
| You can’t use this node in isolation because it only collects the certificate from the request. It doesn’t extract or validate the certificate’s content. Use a Certificate Validation node to validate the certificate and a Certificate User Extractor node to extract the user details from the certificate. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the certificate from the request payload or in a request header. It doesn’t read anything from the shared state.
Configuration
| Property | Usage |
|---|---|
Certificate Collection Method |
How the node should collect the certificate from the request. Possible values are:
Default: |
HTTP Header Name for the Client Certificate |
The name of the HTTP header that contains the certificate.
If you set the Certificate Collection Method to Default: No value |
Trusted Remote Hosts |
A list of IP addresses trusted to supply certificates on behalf of the authenticating client, such as load balancers doing TLS termination. If you don’t set a value here, PingOne Advanced Identity Cloud rejects certificates supplied by remote hosts.
If you set a value of Default: No value |
Outcomes
Collected-
The node was able to collect the certificate.
Not Collected-
The node was unable to collect the certificate.
Outputs
The node outputs the X509 certificate to the transient state to be consumed by the Certificate Validation node.
Errors
-
If no certificate is provided in the configured location (either header or request), the node logs the following error:
Certificate was not successfully collected based on node configuration and client request -
If there’s a problem with the certificate provided in the header or in the request, the node logs the following error:
CertificateFromParameter decode failed, possibly invalid Base64 input
Example
This example shows an authentication journey using a certificate as credentials.
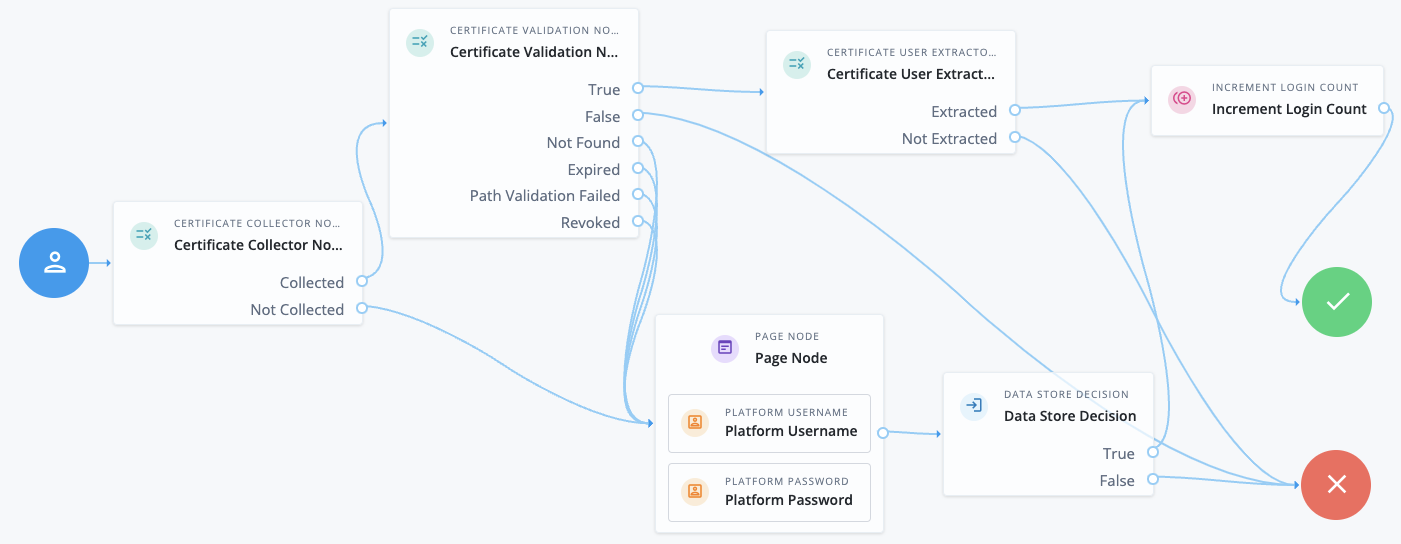
-
The Certificate Collector node attempts to collect the certificate from the request body or the header.
-
If the node can collect the certificate, the journey proceeds to the Certificate Validation node.
-
If the node can’t collect the certificate, the journey proceeds to a Page node containing a Platform Username node and a Platform Password node to let the user authenticate with username/password credentials.
-
-
The Certificate Validation node attempts to validate the certificate based on the configuration of that node.
-
If the certificate can be validated, the journey proceeds to the Certificate User Extractor node.
-
If the certificate is invalid, the journey proceeds to the Failure node.
-
In all other cases, the journey proceeds to a Page node containing a Platform Username node and a Platform Password node to let the user authenticate with username/password credentials.
-
-
The Certificate User Extractor node extracts the user ID from the certificate and attempts to find a match in the identity store.
-
If the username can be extracted and a matching user is found in the identity store, the journey increments the login count and authenticates the user.
-
If the username can’t be extracted or no matching user is found in the identity store, the journey proceeds to the Failure node.
-
Certificate User Extractor node
The Certificate User Extractor node extracts an identifier from the certificate collected by the Certificate Collector node and searches for that identifier in the identity store. The purpose of this node is to match the collected certificate with a user in the identity store.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the value of the X509Certificate property from the transient state.
Implement the Certificate Collector node as input to this node to obtain the X509Certificate.
Configuration
| Property | Usage |
|---|---|
Certificate Field Used to Access User Profile |
Specifies the field in the certificate that AM uses to search for the user in the identity store. Possible values are:
If you select Select Default: |
Other Certificate Field Used to Access User Profile |
Specifies a custom certificate field to use as the base of the user search. |
SubjectAltNameExt Value Type to Access User Profile |
Specifies how to look up the user profile:
Default: |
Outcomes
Extracted-
The node extracted the user ID from the certificate and found a match in the identity store.
Not Extracted-
The node couldn’t extract the user ID from the certificate or couldn’t match the ID to an identity in the identity store.
Outputs
If the node can extract a value from the certificate, that value is stored in the username key in the shared node state.
Errors
If the node can’t extract the user ID from the certificate, it logs the following error:
Unable to parse user token ID from Certificate
Example
This example shows an authentication journey using a certificate as credentials.
-
The Certificate Collector node attempts to collect the certificate from the request body or the header.
-
If the node can collect the certificate, the journey proceeds to the Certificate Validation node.
-
If the node can’t collect the certificate, the journey proceeds to a Page node containing a Platform Username node and a Platform Password node to let the user authenticate with username/password credentials.
-
-
The Certificate Validation node attempts to validate the certificate based on the configuration of that node.
-
If the certificate can be validated, the journey proceeds to the Certificate User Extractor node.
-
If the certificate is invalid, the journey proceeds to the Failure node.
-
In all other cases, the journey proceeds to a Page node containing a Platform Username node and a Platform Password node to let the user authenticate with username/password credentials.
-
-
The Certificate User Extractor node extracts the user ID from the certificate and attempts to find a match in the identity store.
-
If the username can be extracted and a matching user is found in the identity store, the journey increments the login count and authenticates the user.
-
If the username can’t be extracted or no matching user is found in the identity store, the journey proceeds to the Failure node.
-
Certificate Validation node
The Certificate Validation node validates a digital X.509 certificate collected by the Certificate Collector node.
|
Certificate validation rules
|
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires an X509Certificate property in the incoming node state.
Implement the Certificate Collector node as input to the Certificate Validation node.
Configuration
| Property | Usage |
|---|---|
Match Certificate in LDAP |
When enabled, PingOne Advanced Identity Cloud matches the collected certificate with a certificate stored in the identity store. Set the Subject DN Attribute Used to Search LDAP for Certificates to specify which LDAP property to search for certificate information. Default: Disabled |
Check Certificate Expiration |
When enabled, PingOne Advanced Identity Cloud checks if the collected certificate has expired. Default: Disabled |
Subject DN Attribute Used to Search LDAP for Certificates |
The attribute PingOne Advanced Identity Cloud uses to search the identity store for the certificate. The search filter is based on this attribute and the value of the Subject DN as it appears in the certificate. Default: |
Match Certificate to CRL |
When enabled, PingOne Advanced Identity Cloud checks if the collected certificate has been revoked according to a Certificate Revocation List (CRL) in the identity store. Define related CRL properties later in the node configuration. Default: Disabled. |
Issuer DN Attribute(s) Used to Search LDAP for CRLs |
The name of the attribute or attributes in the issuer certificate that PingOne Advanced Identity Cloud uses to locate the CRL in the identity store.
Default: |
HTTP Parameters for CRL Update |
Parameters PingOne Advanced Identity Cloud includes in any HTTP CRL call to the CA that issued the certificate. If the client or CA certificate includes the Add the parameters as key-value pairs in a comma-separated list (,).
For example, |
Cache CRLs in Memory |
When enabled, PingOne Advanced Identity Cloud caches CRLs in memory. If this option is enabled, Update CA CRLs from CRLDistributionPoint must also be enabled. Default: Enabled |
Update CA CRLs from CRLDistributionPoint |
When enabled, AM fetches new CA CRLs from the CRL Distribution Point and updates them in the identity store.
If the CA certificate includes either the Default: Enabled |
OCSP Validation |
When enabled, PingOne Advanced Identity Cloud checks the validity of certificates using the Online Certificate Status Protocol (OCSP). PingAM If you enable this option, the AM instance must be able to connect to the internet. You must also configure OCSP for AM under Configure > Server Defaults > Security > Online Certificate Status Protocol Check. Default: Disabled |
Certificate Identity Store |
PingAM Select the identity store (configured for the realm) that AM must search for certificates. If you select an identity store here, AM uses the connection details defined for that identity store and ignores all the server settings below this field. Advanced Identity Cloud Select the default identity store ( |
PingAM LDAP Server Where Certificates are Stored |
The LDAP server that holds certificates.
Enter the server details in the format To associate multiple AM servers in a site with corresponding LDAP servers, use the format |
PingAM LDAP Search Start or Base DN |
Valid base DN for the LDAP search, such as |
PingAM LDAP Server Authentication User and LDAP Server Authentication Password |
The credentials used to connect to the LDAP directory that holds the certificates. If you enable mTLS, the node ignores these credentials. Default Authentication User: |
PingAM mTLS Enabled |
Enables mTLS (mutual TLS) between AM and the directory server. When mTLS is enabled, the node ignores the values for LDAP Server Authentication User and LDAP Server Authentication Password. If you enable this property, you must:
Default: Disabled |
PingAM mTLS Secret Label Identifier |
An identifier used to create a secret label for mapping to the mTLS certificate in the secret store.
AM uses this identifier to create a specific secret label for this node.
The secret label takes the form For greater security, you should rotate certificates periodically. When you rotate a certificate, update the corresponding mapping in the realm secret store configuration to reflect this identifier. When you rotate a certificate, AM closes any existing connections using the old certificate. A new connection is selected from the connection pool and no server restart is required. |
PingAM Use SSL/TLS for LDAP Access |
When enabled, AM uses SSL/TLS to access the LDAP directory. Make sure that AM trusts the certificate from the LDAP server when enabling this option. Default: Disabled |
Outcomes
True-
The node could validate the certificate.
When the outcome is
True, add a Certificate User Extractor node to extract the values of the certificate. False-
The node couldn’t validate the certificate. The journey follows this path when the node can’t validate the certificate and no more specific outcome is available.
Not found-
The Match Certificate in LDAP property is enabled, but the certificate wasn’t found in the LDAP store.
Expired-
The Check Certificate Expiration property is enabled, and the certificate has expired.
Path Validation Failed-
The Match Certificate to CRL property is enabled, and the certificate path is invalid.
Revoked-
The OCSP Validation property is enabled, and the certificate has been revoked.
Example
This example shows an authentication journey using a certificate as credentials.
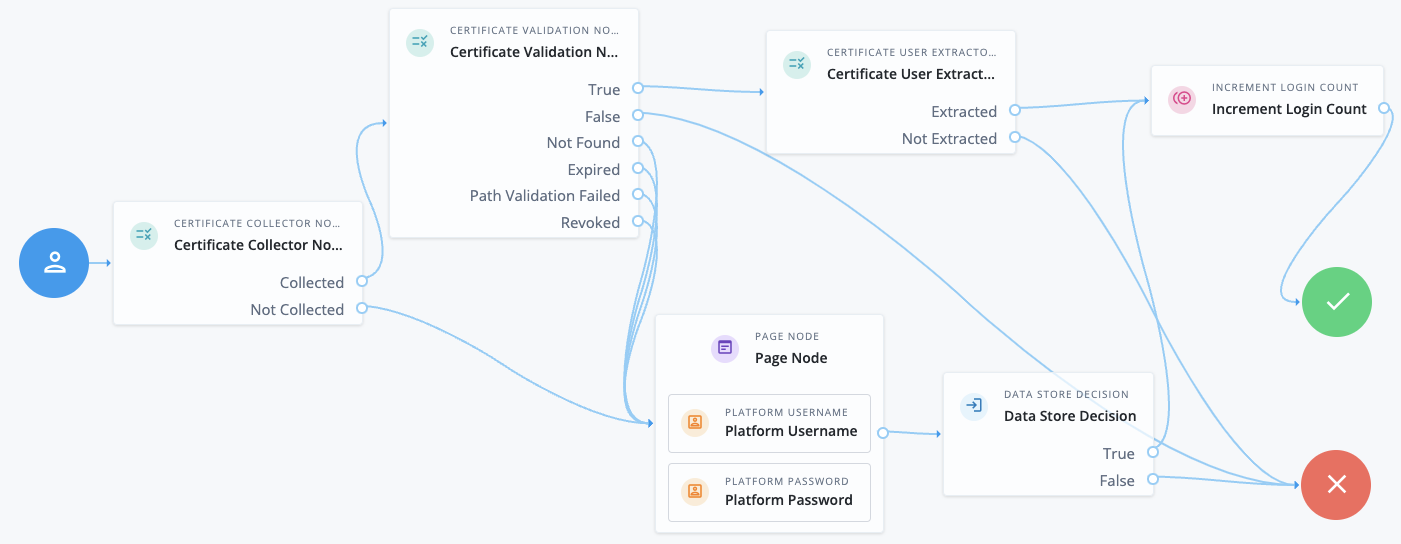
-
The Certificate Collector node attempts to collect the certificate from the request body or the header.
-
If the node can collect the certificate, the journey proceeds to the Certificate Validation node.
-
If the node can’t collect the certificate, the journey proceeds to a Page node containing a Platform Username node and a Platform Password node to let the user authenticate with username/password credentials.
-
-
The Certificate Validation node attempts to validate the certificate based on the configuration of that node.
-
If the certificate can be validated, the journey proceeds to the Certificate User Extractor node.
-
If the certificate is invalid, the journey proceeds to the Failure node.
-
In all other cases, the journey proceeds to a Page node containing a Platform Username node and a Platform Password node to let the user authenticate with username/password credentials.
-
-
The Certificate User Extractor node extracts the user ID from the certificate and attempts to find a match in the identity store.
-
If the username can be extracted and a matching user is found in the identity store, the journey increments the login count and authenticates the user.
-
If the username can’t be extracted or no matching user is found in the identity store, the journey proceeds to the Failure node.
-
Cookie Presence Decision node
Checks that a named cookie is present in the incoming authentication request.
This node does not check the value of the named cookie, only that it exists.
Device Geofencing node
Compares any collected device location metadata with the trusted locations configured in the authentication node.
Use this node with the Device Profile Collector node to determine if the authenticating user’s device is located within range of configured, trusted locations.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
Inside -
Outside
Evaluation continues along the Inside path if the collected location
is within the specified range of a configured trusted location;
otherwise, evaluation continues along the Outside path.
Properties
| Property | Usage |
|---|---|
Trusted Locations (required) |
Specify the latitude and longitude of at least one trusted location.
Separate the values with a comma. For example, |
Geofence Radius (km) |
Specifies the maximum distance, in kilometers, that a device can be from a configured trusted location. The distance is calculated point-to-point. |
Device Location Match node
Compares any collected device location metadata with that stored in the user’s profile.
Use this node with the Device Profile Collector node to determine if the authenticating user’s device is located within range of somewhere they have authenticated from, and saved, previously.
You must establish the identity of the user before attempting to match locations.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
True -
False -
Unknown Device
Evaluation continues along the True path if the collected location
is within the specified range of saved location data;
otherwise, evaluation continues along the False path.
If the user has no saved device profiles or the identity of the user has not been established,
evaluation continues along the Unknown Device path.
Device Match node
The Device Match node compares collected device metadata with that stored in the user’s profile.
Use this node with the Device Profile Collector node to check whether the user is authenticating with a previously saved, trusted device.
The Device Match node supports the following methods of comparison:
-
Built-in matching
The node handles the comparison and matching. You configure the acceptable variance and the maximum age for device profiles.
-
Custom matching
Create scripts to compare captured device data against trusted device profiles.
PingOne Advanced Identity Cloud includes a customizable template script. In the Advanced Identity Cloud admin console, go to Scripts > Auth Scripts, and click Device Profile Match Template - Decision Node Script.
For a comprehensive sample script with instructions for its use and a development toolkit, go to the GitHub sample repository.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the username from the shared state to look up saved device profiles in the user’s account.
Implement a
Platform Username node
earlier in the journey to obtain the username.
This node also reads collected device metadata from the shared state. Implement a Device Profile Collector node earlier in the journey to collect metadata for the current device.
If Use Custom Matching Script is enabled, the inputs depend on the script.
Uniquely identify devices
The Device Match node looks up a user’s stored device profiles using a device identifier as a key.
The client device generates a device identifier as part of the device profile that it returns to the Device Profile Collector node in the JSON payload.
For example:
{
"identifier": "d50cdb5ce8d055a3-86bd35e1b975a14d76b40940112c2380264c8efd",
....
}When can identifiers change?
If the identifier changes, the Device Match node can’t match any stored device profiles.
If this happens, your journey must collect and store a new device profile that contains the new identifier.
This section explains what can cause an identifier to change on each platform.
-
Android
-
iOS
-
JavaScript
In Android, the instance ID is deleted or changes if any of the following occurs:
-
An app is restored on a new device.
-
The user uninstalls and reinstalls the app.
-
The user clears app data.
On iOS, the device ID is stored in the Keychain. This means the ID persists when the app is removed.
However, the device ID is deleted or changes if any of the following occurs:
-
The user wipes or factory resets the phone.
-
The user migrates to a new phone.
-
The keychain is programmatically deleted from the phone.
-
The device ID is programmatically deleted from the Keychain.
-
The keychain identifier in the
forgerock_keychain_access_groupconfiguration property changes.
In JavaScript, the device ID is deleted or changes if any of the following occurs:
-
The browser window creates the device ID while in "private" or "incognito" mode. Closing the browser removes the ID.
-
The browser removes the ID when cleaning up old data to accommodate new data.
-
The browser is uninstalled and reinstalled. The ID is removed.
-
The user removes the device ID by clearing the browser data.
Configuration
| Property | Usage |
|---|---|
Acceptable Variance |
The maximum number of acceptable device attribute differences for a match. Default: |
Expiration |
The maximum age in days a saved profile is valid for comparison. The node ignores older device profiles saved to the user’s account when comparing device profiles with the collected metadata. Default: |
Use Custom Matching Script |
Enable this option to use a custom script instead of built-in matching to compare the collected metadata with saved device profiles. When enabled, the node ignores the Acceptable Variance and Expiration settings. The script type must be
Default: false |
Custom Matching Script |
Select the custom script to use when Use Custom Matching Script is enabled. Only scripts of type
Default: |
Outputs
This node does not change the shared state on its own.
If the node uses a Custom Matching Script, the output is determined by the script.
Outcomes
True-
The collected device metadata matches a saved profile within the configured variance.
False-
The collected device metadata doesn’t match a saved profile, or another error occurred.
Unknown Device-
The journey follows this outcome path in the following situations:
-
The user has no saved trusted device profiles.
-
The user identity hasn’t yet been established.
-
The acceptable device variance matches, but the device ID no longer matches.
-
Errors
This node logs the following warning messages:
script outcome error-
The script failed to set the
outcomefield to a string. error evaluating the script-
The script failed to complete. Refer to the logs for details.
Example
The following journey authenticates the user and checks whether the current device is trusted. If the device isn’t trusted yet, the journey requires an additional authentication factor and lets the user opt to trust the device:
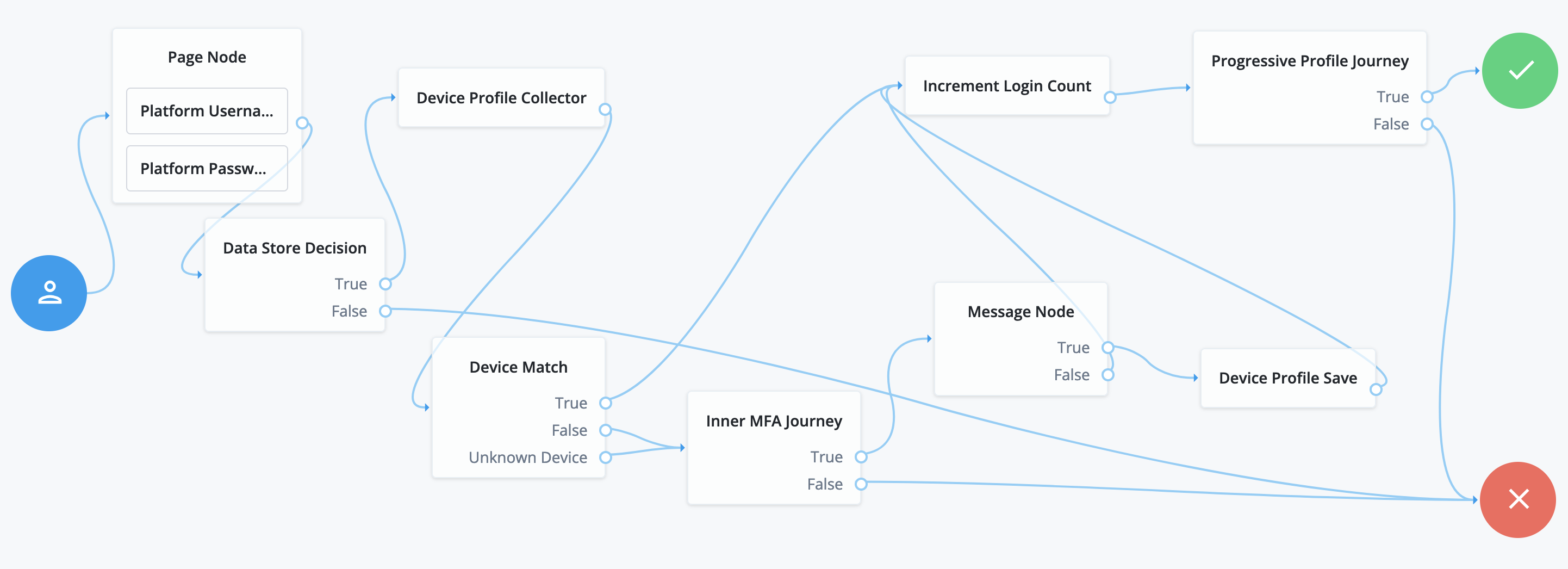
-
The Page node with the Platform Username node and Platform Password node prompt the user for their credentials.
-
The Data Store Decision node confirms the user’s credentials.
-
The Device Profile Collector node collects metadata about the current device.
-
The Device Match node compares saved device profiles with the current device.
-
The Inner MFA Journey, an Inner Tree Evaluator node, requires an additional authentication factor.
-
The Message node prompts the user with an option to trust the current device.
-
The Device Profile Save node saves the current device profile.
-
The Increment Login Count node updates the number of successful authentications.
-
The Progressive Profile Journey, an Inner Tree Evaluator node, invokes a journey to collect additional profile data.
Device Profile Collector node
Gathers metadata about the device used to authenticate.
The node sends a DeviceProfileCallback callback.
Learn more in
Interactive callbacks.
When used with the Ping SDKs, the node can collect the following:
- Device Metadata
-
Information such as the platform, versions, device name, hardware information, and the brand of the device being used.
The captured data is in JSON format, and stored in the authentication shared state in a variable named
forgeRock.device.profile. - Device Location
-
Provides the last known latitude and longitude of the device’s location.
The captured data is in JSON format, and stored in the authentication shared state in a variable named
forgeRock.device.location.The collection of geographical information requires end-user approval. A browser function drives this process. A pop-up displays, prompting for access to share the geographical location. The browser connection must be secure.
|
It is up to you what information you collect from users and devices. Always use data responsibly and provide your users with appropriate control over data they share with you. You are responsible for complying with any regulations or data protection laws. |
In addition to the collected metadata, an identifier string in the JSON uniquely identifies the device.
Use this node with the Device Profile Save node to create a trusted profile from the collected data. You can use the trusted device profile in subsequent authentication attempts; for example, with the Device Match node and Device Location Match node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Maximum Profile Size (KB) |
Specifies the maximum accepted size, in kilobytes, of a device profile. If the collected profile data exceeds this size, authentication fails. Default: |
Collect Device Metadata |
Specifies whether device metadata is requested. |
Collect Device Location |
Specifies whether device location is requested. |
Message |
Specifies an optional message to display to the user while the node collects the requested data. You can provide the message in multiple languages by specifying the locale in the The locale selected for display is based on the user’s locale settings in their browser. Messages provided in the node override the defaults provided by AM. |
Device Profile Save node
Persists collected device data to a user’s profile in the identity store.
Use this node with the Device Profile Collector node to reuse the collected data in future authentications; for example, with the Device Match node and Device Location Match node.
You must establish the identity of the user before attempting to save to their profile.
A user profile can contain multiple device profiles. Use the Maximum Saved Profiles property to configure the maximum number of device profiles to persist per user. Saving a device profile with the same identifier as an existing entry overwrites the original record, and does not increment the device profile count.
The end user UI displays saved device profiles to end users.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Device Name Variable |
Specifies the name of a variable in the shared node state that contains an alias label for the device profile. |
Maximum Saved Profiles |
Specify the maximum number of device profiles to save in a user’s profile. When the maximum is reached, saving a new profile replaces the least-recently used profile. |
Save Device Metadata |
Specifies whether device metadata is saved to the user’s profile. |
Save Device Location |
Specifies whether device location metadata is saved to the user’s profile. |
Device Tampering Verification node
Specifies a threshold for deciding if the device has been tampered with; for example, if it has been rooted or jailbroken.
The device scores between zero and one,
based on the likelihood that is has been tampered with or may pose a security risk.
For example, an emulator scores the maximum of 1.
Use this node with the Device Profile Collector node to retrieve the tampering score from the device.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
Not Tampered -
Tampered
Evaluation continues along the Not Tampered path if the device scores less than or equal to the configured threshold;
otherwise, evaluation continues along the Tampered path.
Properties
| Property | Usage |
|---|---|
Score Threshold |
Specifies the score threshold for determining if a device has been tampered with.
Enter a decimal fraction, between The higher the score returned from the device, the more likely the device is jailbroken, rooted, or is a potential security risk. Emulators score the maximum; |
Persistent Cookie Decision node
The Persistent Cookie Decision node checks for the existence of a specified persistent cookie (default: session-jwt).
If the cookie is present, the node verifies the signature of the JWT stored in the cookie with the configured signing key.
If the configured signing key isn’t valid, PingOne Advanced Identity Cloud checks the signature against all valid signing keys mapped to the configured secret label.
If the signature is valid, the node decrypts the payload of the JWT using the key pair defined
in the active secret mapped to the am.authentication.nodes.persistentcookie.encryption secret label.
If there isn’t a valid secret label mapping in a secret store, PingOne Advanced Identity Cloud uses the key pair specified in Native Consoles > Access Management > Realms > Realm Name > Authentication > Settings > Security > Persistent Cookie Encryption Certificate Alias.
The decrypted JSON payload includes information, such as the UID of the identity and the client IP address. Enable Enforce Client IP to verify that the current IP address and the client IP address in the cookie are the same.
|
This node recreates the specified persistent cookie,
updating the value for the idle time property and the JWT Therefore, the node has cookie creation properties similar to the Set Persistent Cookie node. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the realm property, which PingOne Advanced Identity Cloud sets by default.
Dependencies
To authenticate successfully, the tree must have set a persistent cookie using a node such as the Set Persistent Cookie node.
Configuration
| Property | Usage | ||
|---|---|---|---|
Idle Timeout |
The maximum idle time allowed before the persistent cookie is invalidated, in hours. If no requests are received and the time is exceeded, the cookie is no longer valid. |
||
Enforce Client IP |
When enabled, ensures that the persistent cookie is only used from the same client IP to which the cookie was issued. |
||
Use Secure Cookie |
When enabled, adds the If the |
||
Use HTTP Only Cookie |
When enabled, adds the When the |
||
HMAC Signing Key |
The key to use for HMAC signing of the persistent cookie.
Values must be base64-encoded and at least 256 bits (32 bytes) long. To generate an HMAC signing key, run one of the following commands: bash or bash |
||
HMAC Signing Key Secret Label Identifier |
An identifier used to create a secret label for mapping to a secret in a secret store. PingOne Advanced Identity Cloud uses this identifier to create a specific secret label for the signing key for this node.
The secret label takes the form
If you set an HMAC Signing Key Secret Label Identifier and PingOne Advanced Identity Cloud finds a matching secret in a secret store, the HMAC Signing Key is ignored. If HMAC Signing Key is empty, PingOne Advanced Identity Cloud uses the value configured for
For greater security, you should rotate signing keys periodically by adding new secret versions to the ESV.
|
||
Persistent cookie name |
The name of the persistent cookie to check. |
Outputs
The node copies shared state into the outgoing node state. It records the user identity and stores the cookie name as a session property.
The node adds the UpdatePersistentCookieTreeHook, which runs when the tree completes.
Outcomes
-
True -
False
Evaluation continues along the True outcome path
if the persistent cookie is present and all the verification checks are satisfied;
otherwise, evaluation continues along the False outcome path.
Errors
The node logs the following warning messages:
-
Attempt to verify JWT failed, attempting other valid keys -
Failed to parse universal id username from claim openam.usr
The node logs the following error messages:
-
Claims context not found -
Failed to find signing key with associated keyID -
jwt reconstruction error -
Authentication failed. Jwt claim Realm does not match -
Authentication failed. Cannot read the user from null claims -
Authentication failed. Cannot read the user from empty claims -
Failed to parse universal Id from claim: openam.usr -
Authentication failed. Client IP is different
Set Custom Cookie node
The Set Custom Cookie node lets you store a custom cookie on the client in addition to the session cookie.
The node uses the specified properties to create a cookie with a custom name and value. It can also set attributes, such as the cookie path, domain, expiry, and security flags.
Use this node with the Configuration Provider node to extend custom capabilities.
For example, create a Config Provider script to set custom static values or access values from the shared node state.
Include all the attributes in the configuration provider script’s config map.
The following example sets the attributes of the custom cookie to static values:
config = {
"name": "testname",
"value": "testvalue",
"maxAge": "60",
"domain": "am.example.com",
"path": "/",
"useSecureCookie": false,
"useHttpOnlyCookie": false,
"sameSite": "LAX"
};Reference the script when you create a Configuration Provider node, and set the Node Type to Set Custom Cookie:
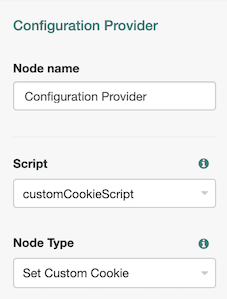
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the user data from the shared node state.
It requires a predecessor node that gathers the user data.
Configuration
| Property | Usage |
|---|---|
Custom Cookie Name (required) |
The name of the custom cookie. The cookie name can contain any US-ASCII characters except for:
space, tab, control, or a separator character ( |
Custom Cookie Value (required) |
The value of the custom cookie. |
Max Age |
The length of time the custom cookie remains valid, in seconds. If that time is exceeded, the cookie is no longer valid. AM sets the If omitted, the cookie expires at the end of the current session. The precise implementation of this is determined by the specific browser. Refer to RFC 6265 for details. |
Custom Cookie Domain |
The domain the custom cookie will be sent to.
If you specify a value here, AM sets a domain cookie.
For example, if you set this property to If you don’t set a value here, AM sets a host level cookie on the FQDN on which the client accessed AM.
For example, if the client accesses AM at |
Custom Cookie Path |
The path of the custom cookie. |
Use Secure Cookie |
When enabled, adds the If you include the |
Use HTTP Only Cookie |
When enabled, adds the If you include the |
Custom Cookie SameSite attribute |
Sets the The default value is |
Set Persistent Cookie node
Creates the specified persistent cookie, the default being session-jwt.
The cookie contains a JWT with a JSON payload including information such as the UID of the identity, and the client IP address.
The node encrypts the payload of the JWT using the key pair defined
in the active secret mapped to the am.authentication.nodes.persistentcookie.encryption secret label.
If there isn’t a valid secret label mapping in a secret store, PingOne Advanced Identity Cloud uses the key pair specified in Native Consoles > Access Management > Realms > Realm Name > Authentication > Settings > Security > Persistent Cookie Encryption Certificate Alias.
The node signs the cookie with the HMAC signing key defined in the node properties or the secret store with the mapped secret label. Configure nodes that read the persistent cookie such as the Persistent Cookie Decision node with the same HMAC signing key.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
When the authentication tree completes successfully, the CreatePersistentCookieTreeHook treehook
for this node uses session properties to create the persistent cookie.
Configuration
| Property | Usage | ||
|---|---|---|---|
Idle Timeout |
The maximum amount of idle time allowed before the persistent cookie is invalidated, in hours. If no requests are received before the timeout, the cookie is no longer valid. |
||
Max life |
The length of time the persistent cookie remains valid, in hours. After this time has passed, the cookie is no longer valid. |
||
Use Secure Cookie |
When enabled, adds the If the |
||
Use HTTP Only Cookie |
When enabled, adds the When the |
||
HMAC Signing Key |
A key to use for HMAC signing of the persistent cookie.
Values must be base64-encoded and at least 256 bits (32 bytes) long. To generate an HMAC signing key, run one of the following commands: bash or bash |
||
HMAC Signing Key Secret Label Identifier |
An identifier used to create a secret label for mapping to a secret in a secret store. PingOne Advanced Identity Cloud uses this identifier to create a specific secret label for the signing key for this node.
The secret label takes the form
If you set an HMAC Signing Key Secret Label Identifier and PingOne Advanced Identity Cloud finds a matching secret in a secret store, the HMAC Signing Key is ignored. If HMAC Signing Key is empty, PingOne Advanced Identity Cloud uses the value configured for
For greater security, you should rotate signing keys periodically by adding new secret versions to the ESV.
|
||
Persistent Cookie Name |
The name used for the persistent cookie. |
Outputs
The node stores the cookie name in the session properties.
The node adds the CreatePersistentCookieTreeHook treehook, which runs when the tree completes.
Errors
The node logs the following warning messages:
-
Unable to create signing key from provided configuration.
The node logs the following error messages:
-
Tree hook creation exception -
No signing keys available to sign JWT -
Error creating jwt string
Example
Refer to the Persistent Cookie Decision node example.
Federation nodes
SAML2 Authentication node
The SAML2 Authentication node integrates SAML 2.0 single sign-on into an authentication flow.
Use this node when deploying SAML 2.0 SSO in integrated mode (SP-initiated SSO only). This node doesn’t support single logout (SLO).
Implement the Write Federation Information node after this node in the journey to link the remote account to a local account.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Dependencies
This node requires the following configuration in PingOne Advanced Identity Cloud:
-
A remote identity provider (IdP) and a hosted service provider (SP) in a circle of trust in the same realm where you’re configuring the journey.
-
You must configure the service provider for integrated mode.
PingAM Configure AM for integrated mode.
Advanced Identity Cloud Configure Advanced Identity Cloud for integrated mode.
Configuration
| Property | Usage |
|---|---|
IdP Entity ID |
The name of the remote IdP. |
SP MetaAlias |
The local alias for the SP in the format |
Allow IdP to Create NameID |
Enable this option if you want the IdP to create a new identifier for the authenticating user if none exists. Learn more in AllowCreate in the SAML Version 2.0 specification. Default: |
Comparison Type |
The comparison method to evaluate authentication context classes or statements. This value overrides the value in the SP configuration: PingAM Under Realms > Realm Name > Applications > Federation > Entity Providers > Service Provider Name > Assertion Content > Authentication Context > Comparison Type. Advanced Identity Cloud Under Native Consoles > Access Management > Realms > Realm Name > Applications > Federation > Entity Providers > Service Provider Name > Assertion Content > Authentication Context > Comparison Type. Valid comparison methods are Learn more about comparison methods in Default: |
Authentication Context Class Reference |
(Optional) Set one or more URIs for authentication context classes to be included in the SAML request. Authentication context classes are unique identifiers for an authentication mechanism. The SAML 2.0 protocol supports a standard set of authentication context classes, defined in Authentication Context for the OASIS Security Assertion Markup Language (SAML) V2.0. You can specify your own authentication context classes in addition to the standard ones. Any authentication context class you specify here must be supported for the SP. To add authentication context classes to the SP:
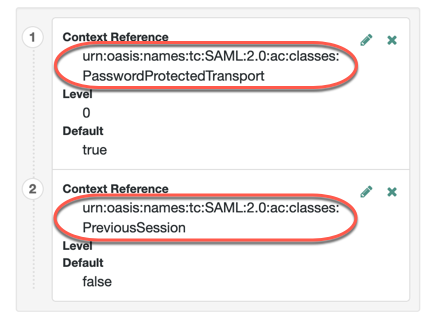
Use the | character to separate multiple authentication context classes, for example: urn:oasis:names:tc:SAML:2.0:ac:classes:Password|urn:oasis:names:tc:SAML:2.0:ac:classes:TimesyncToken |
Authentication Context Declaration Reference |
(Optional) One or more URIs that identify authentication context declarations. Use the | character to separate multiple URIs. Learn more in the section on the |
Request Binding |
The format of the authentication request that the SP sends to the IdP. Valid values are Default: |
Response Binding |
The format of the response that the IdP sends to the SP. Valid values are Default: |
Force IdP Authentication |
Indicate whether the IdP should force authentication or if it can reuse existing security contexts. Default: Disabled |
Passive Authentication |
Indicate whether the IdP should use passive authentication. When this setting is enabled, the IdP can only use authentication methods that don’t require user interaction, such as authenticating with an X.509 certificate. Default: Disabled |
NameID Format |
The SAML name ID format that’s requested in the SAML authentication request. Valid values are: urn:oasis:names:tc:SAML:2.0:nameid-format:persistent urn:oasis:names:tc:SAML:2.0:nameid-format:transient urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified Default: |
Outputs
This node updates the shared state with the SAML 2.0 assertion data as follows:
-
It adds a
userInfokey with two child keys:attributesanduserNames. -
The
attributesobject contains a map of SAML 2.0 attributes, each of which is stored as an array. -
The
attributesobject also stores the SAML 2.0 identity attributessun-fm-saml2-nameid-infoandsun-fm-saml2-nameid-infokey.These attributes are required by the Write Federation Information node.
-
The
userNamesobject contains the user’s UUID.
Example node state after node processing
{
"realm" : "/",
"authLevel" : 0,
"username" : "22fe07c3-ac8b-4e84-9016-b55f1c009924",
"userInfo" : {
"attributes" : {
"uid" : [ "bjensen" ],
"mail" : [ "bjensen@example.com" ],
"sun-fm-saml2-nameid-info" : [ "serviceprovider2|identityprovider1|sAdI2i7LT2YL0rbJC/QqsRt5SABV|identityprovider1|urn:oasis:names:tc:SAML:2.0:nameid-format:persistent|null|serviceprovider2|SPRole|false" ],
"sun-fm-saml2-nameid-infokey" : [ "serviceprovider2|identityprovider1|sAdI2i7LT2YL0rbJC/QqsRt5SABV" ]
},
"userNames" : {
"username" : [ "22fe07c3-ac8b-4e84-9016-b55f1c009924" ],
"uid" : [ "22fe07c3-ac8b-4e84-9016-b55f1c009924" ]
}
},
"emailAddress" : "bjensen@example.com"
}|
You can use a script to read the SAML 2.0 attributes, for example: javascript |
The updated shared state depends on the node outcome:
-
If the outcome is
Account exists, the shared state is updated withnodeState.userNamesas follows:userNames={username=[bjensen], uid=[bjensen]}}javascript -
If the outcome is
No account exists, the shared state is updated withnodeState.userNamesas follows:userNames={username=[null], uid=[null]}}javascript -
If the
mailattribute exists in theattributesmap, the shared state is updated withnodeState.emailAddress. -
If the
RelayStateattribute exists in theattributesmap, the shared state is updated withnodeState.successUrl. -
The
usernameis added to the shared state, regardless of outcome.
The node also sets the following session properties:
-
SessionIndex: the session index -
NameID: the NameID of the Assertion XML -
isTransient: if the NameId isurn:oasis:names:tc:SAML:2.0:nameid-format:transient -
cacheKey: for internal use only
Outcomes
Account exists-
The node found a user account that matches the federated account.
No account exists-
Any other case.
Errors
This node can log the following errors:
| Message | Notes |
|---|---|
|
The node was unable to find the remote IdP descriptor. |
|
The node was unable to find the SP descriptor. |
|
The node was unable to retrieve the SAML 2.0 state from the second-factor authentication. |
|
The node was unable to read the SAML 2.0 response data. |
|
The node was unable to remove the SAML 2.0 response data. |
|
The |
Example
Read the following sections for examples that show this node in a SAML 2.0 authentication journey:
PingAM SSO and SLO in integrated mode.
Advanced Identity Cloud Configure Advanced Identity Cloud for integrated mode.
Legacy Social Provider Handler node
This node takes a provider selection from the Select Identity Provider node and attempts to authenticate the user. The node collects relevant profile information from the provider, transforms the profile information into the appropriate attributes and returns the user to the journey.
This node is deprecated and therefore marked as legacy. A new Social Provider Handler node with additional outcomes will be available in an upcoming release.
Implement this node with the Select Identity Provider node to use the Social Identity Provider Service.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
Account exists-
Social authentication succeeded, and a matching PingOne Advanced Identity Cloud account exists.
No account exists-
Social authentication succeeded, but no matching PingOne Advanced Identity Cloud account exists.
Properties
| Property | Usage |
|---|---|
Transformation Script (required) |
This script is used after the configured provider’s normalization script has mapped the social identity provider’s attributes to a profile format compatible with AM. The transformation script then transforms a normalized social profile to a managed object. Select To view the scripts and bindings, refer to normalized-profile-to-managed-user.js. Normalization scripts ( |
Username Attribute |
The attribute in the underlying identity service that contains the username for this object. |
Client Type |
Specify the client type you are using to authenticate to the provider. Use the default, Select |
Store Tokens |
When In some cases, the social provider requires these tokens, for example, to revoke user authorization. If you choose to store tokens, you can configure a Scripted Decision node later in the journey to handle your social provider use case. Default: |
Social Provider Handler node
The Social Provider Handler node attempts to authenticate a user with an identity provider they select in the Select Identity Provider node. The Social Provider Handler node collects relevant profile information from the provider, transforms the profile information into the appropriate attributes, and returns the user to the journey.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the user’s selected social identity provider from shared state.
Implement the Select Identity Provider node before this node to capture the social provider name.
Dependencies
-
The Social Identity Provider service must be configured with the details of at least one social identity provider.
-
The user must have selected a social identity provider in a previous node in the journey.
Configuration
| Property | Usage | ||
|---|---|---|---|
Transformation Script (required) |
The normalization script of each provider maps that provider’s attributes to a profile format PingOne Advanced Identity Cloud can use. The transformation script then transforms the normalized social profile to a managed object. Select Review the sample script (normalized-profile-to-managed-user.js) for a list of bindings.
|
||
Username Attribute |
The attribute in the underlying identity service that contains the username for this object. |
||
Client Type |
The client type you’re using to authenticate to the provider. Select one of the following:
|
||
Store Tokens |
When In some cases, the social provider requires these tokens, for example, to revoke user authorization. If you choose to store tokens, you can configure a Scripted Decision node later in the journey to handle your social provider use case. Default: |
Outputs
-
If no profile information is returned from the social provider, the journey follows the
Social auth interruptedoutcome. -
If the node retrieves profile information from the social identity provider, it transforms a normalized version of the profile and stores it in
objectAttributesin transient state. -
To link existing users, the
aliasListis updated and saved toobjectAttributesin transient state. -
The node stores the social identity subject as the
usernameboth directly in shared state and in itsobjectAttributes. -
The node also updates
socialOAuthDatain transient state with all existing node state, social provider data, and associated tokens.
| Make sure you copy required transient data to shared state because all transient data is removed if the node is followed by an interactive page later in the journey. |
Outcomes
Account exists-
Social authentication succeeded, and a matching Ping Identity account exists.
No account exists-
Social authentication succeeded, but no matching Ping Identity account exists.
To ensure existing users are dynamically linked, connect the
No account existsoutcome to an Identify Existing User node followed by a Patch Object node to create the link as demonstrated in Example 2: Social Provider Handler node with dynamic linking. Social auth interrupted-
The user interrupted the social authentication journey after the node requested profile information from the social identity provider. This can happen in the following situations:
-
The user clicks the Back button in their browser from the social identity provider’s login page
-
The user clicks the Cancel button on the social identity provider’s login page
-
The user re-enters the journey URL in the same browser window
In this case, the node routes the user back to the Select Identity Provider node to select a social identity provider again.
-
Examples
Example 1: Social Provider Handler node in a social authentication journey
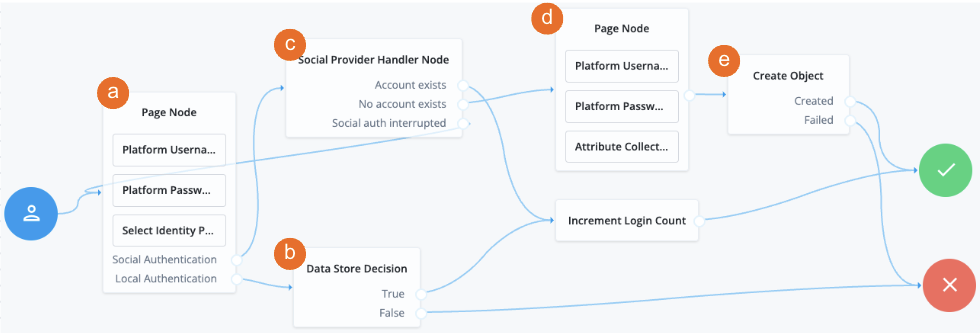
a The Page node containing the Select Identity Provider node prompts the user to select a social identity provider or to authenticate with a username and password.
b If the user selects local authentication, the Data Store Decision node takes care of the authentication.
c If the user selects social authentication, the Social Provider Handler node does the following:
-
Routes the user to the selected social provider to authenticate there
-
Retrieves the user’s profile information, and transforms it into a format that PingOne Advanced Identity Cloud can use
-
Assesses whether the user has an existing identity in PingOne Advanced Identity Cloud
-
If the user has an existing identity, authenticates that identity
-
If the user doesn’t have an identity, routes the user to another page node
-
If the user interrupts the social authentication, routes the user back to the Select Identity Provider node
-
d The nodes on the page node request the information required to register a new identity.
e The Create Object node creates the new identity in PingOne Advanced Identity Cloud.
Example 2: Social Provider Handler node with dynamic linking
This example shows a social authentication journey with dynamic account linking.
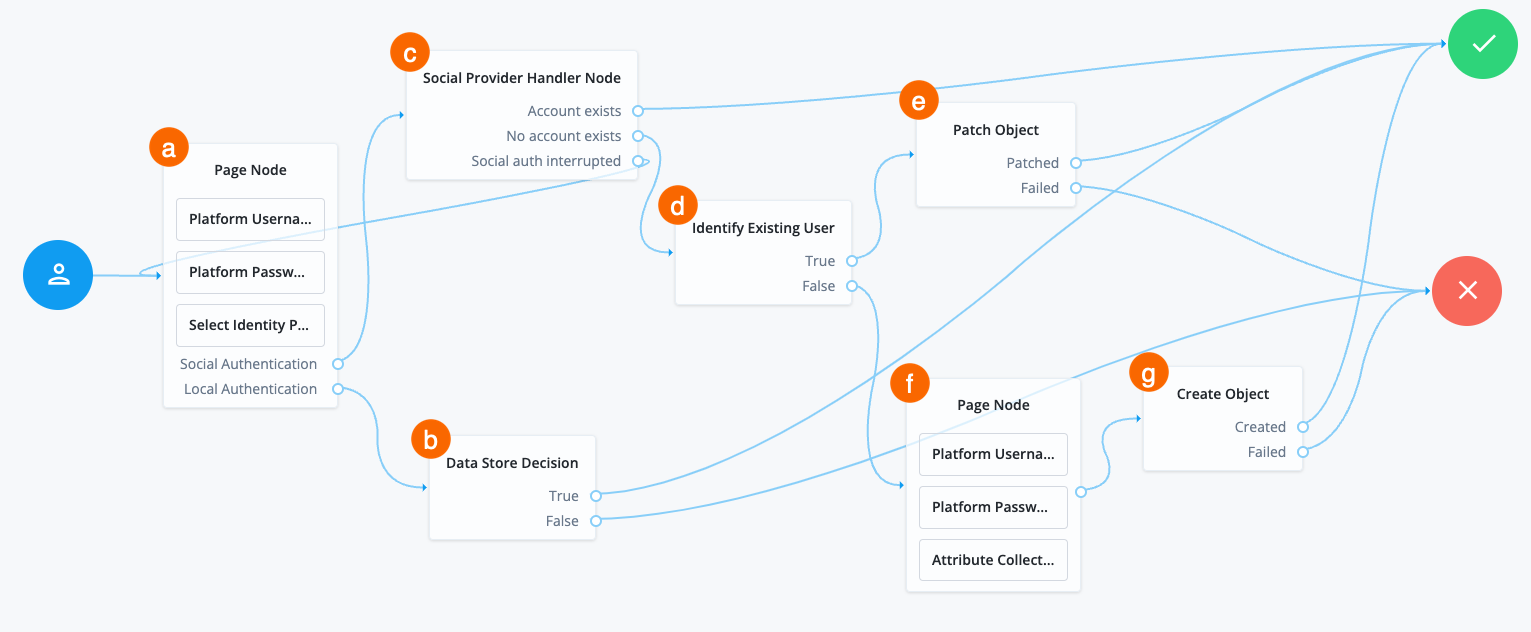
a A Page node contains the Select Identity Provider node node that prompts the user to select a social identity provider or to authenticate with a username and password.
b If the user selects local authentication, the Data Store Decision node takes care of the authentication.
c If the user selects social authentication, the Social Provider Handler node does the following:
-
Routes the user to the selected social provider to authenticate there
-
Retrieves the user’s profile information, and transforms it into a format that PingOne Advanced Identity Cloud can use
-
Assesses whether the user has an existing identity in PingOne Advanced Identity Cloud
-
If the user has an existing identity, authenticates that identity
-
If the user doesn’t have an identity, routes the user to the Identify Existing User node
-
If the user interrupts the social authentication, routes the user back to the Select Identity Provider node
-
d The Identify Existing User node checks if the user exists in PingOne Advanced Identity Cloud using the Identity Attribute specified and does the following:
-
If the user exists, routes the user to the Patch Object node
-
If the user doesn’t exist, routes the user to another page node
e The Patch Object node updates the existing user to create the link.
f The nodes on the page node request the information required to register a new identity.
g The Create Object node creates the new identity in PingOne Advanced Identity Cloud.
Write Federation Information node
Creates a persistent link between a remote IdP account and a local account in the SP, if none exists yet. If a transient link exists, it is persisted. Existing account links with different IdPs are not lost.
Use this node with the SAML2 Authentication node, and ensure that the NameID Format is persistent.
Identity management nodes
Accept Terms and Conditions node
The Accept Terms and Conditions node prompts the user to accept the currently active terms and conditions.
You set terms and conditions in the Ping Identity Platform admin UI. Learn more in Terms and conditions.
Use this node for registration, or combined with the Terms and Conditions Decision node for progressive profiling or log in.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Dependencies
This node depends on the underlying identity service for the active terms and conditions.
Outputs
The node writes a termsAccepted object to the shared node state.
The object contains these fields:
-
acceptDate: A timestamp string indicating when the user accepted the terms. -
termsVersion: A string indicating the version of the accepted terms.
Example
For progressive profiling, include this node after a Terms and Conditions Decision node. If the user has not accepted the latest version of the terms and conditions, evaluation takes them to a page that requires them to accept the current terms and conditions.
The Patch Object node stores the acceptance response in the underlying identity service if the user accepts:
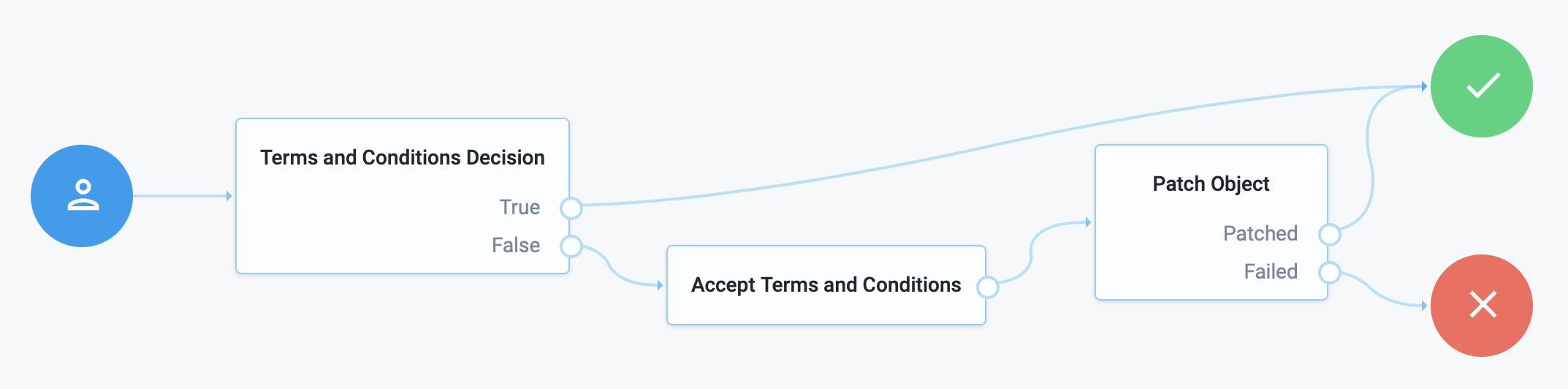
Attribute Collector node
The Attribute Collector node collects the values of attributes for use later in the flow; for example, to populate a new account during registration.
This node supports three types of attributes:
string
boolean
number
To request a value, the attribute must be present in the identity schema of the current identity object.
The node lets you configure whether the attributes are required to continue and whether to use a policy filter of the underlying identity service to validate them.
Use the node alone or within a Page node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
For validation, this node reads the Identity Attribute (default: userName) from the shared node state.
It uses the value to look up the identity object.
It prompts the user for the attributes to collect.
Dependencies
This node depends on the underlying identity service to store the user profile and perform validation.
Configuration
| Property | Usage |
|---|---|
Attributes to Collect |
A list of the attributes to collect based on those in the identity schema for the current identity object. Default: none |
All Attributes Required |
When enabled, all attributes collected in this node are required in order to continue. Default: false |
Validate Input |
When enabled, validate the content against any policies specified in the identity schema for each collected attribute. Learn more in Use policies to validate data. If you enable this property, the collected identity attributes must be User Editable. To make an attribute user-editable in the IDM admin console:
For details, refer to Property Configuration Properties. Default: false |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Outcomes
Single outcome path; on success, downstream nodes can read the attributes from the shared node state.
Examples
Add date and datetime fields to a journey
The Attribute Collector node lets you add properties (attributes) that follow a date or datetime (date and time of day). The format of the date comes from the locale set in your browser.
The following table displays the differences between date and datetime:
| Display format | Managed object field format | Notes | ||
|---|---|---|---|---|
Date only |
String format For example, |
The format of the date comes from the locale set in your browser. For example,
if the locale is English,
then the format presented to the end user is |
||
Date and time |
String format (date and time of day) For example, |
The format of the date comes from the locale set in your browser. For example,
if the locale is English (United States),
then the format presented to the end user is
|
|
While the rendering of the date to the end user changes depending on the locale
set in the browser,
Advanced Identity Cloud
stores the date value in UTC format as |
To render the date or datetime UI element to an end user with the Attribute Collector node, you must:
-
Specify the property to use as date or datetime:
-
General purpose extension attributes — Recommended. Use OOTB indexed attributes:
-
Use the
Dateindexed properties, such asfrIndexedDatefor datetime only. Don’t use it as a date property. -
Use
Stringdata types.
-
-
Create your own custom attributes — Create custom attributes, prefixed with
custom_.
-
-
Apply formatting and policies to the property in the IDM admin console for
DateorDatetime.
Apply formatting and policies
-
In the Advanced Identity Cloud admin console, go to Configure > Managed Objects > Select object, for example, Alpha_user.
-
Select the property to use.
-
To select the format of the attribute, on the Details tab, click the Format field, and select one of the following:
-
For date property —
Date -
For datetime property —
Datetime
-
-
Click Save.
-
On the Validation tab, click + Add Policy.
-
In the Policy Id field, enter one of the following:
-
For date property —
valid-formatted-date -
For datetime property —
valid-datetimeFor more information on applying policies to properties, refer to Apply policies to managed objects.
-
-
Click Add.
-
In your journey, in the Attribute Collector node, add the property name to the Attributes to Collect field; in this case, the following properties are used:
-
For date property —
frIndexedString1 -
For datetime property —
frIndexedDate1
-
For an in-depth use case, add the date or datetime property to an Attribute Collector node in a registration flow. Learn more in User self-registration.
The following video shows an example of a journey collecting the datetime from an end user using the Attribute Collector node:
Attribute Present Decision node
The Attribute Present Decision node checks whether an attribute is present on an object, including private attributes. There is no need to specify the value of the attribute.
Use this node during an update password flow to check whether the local account has a password, for example.
This node is similar to the Attribute Value Decision node when that node is set to use the PRESENT operator,
except it can’t return the value of the attribute, but can work with private attributes.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the Identity Attribute from the shared node state.
If it can’t read the Identity Attribute, it reads the userName from the shared node state.
It uses the value to look up the identity object.
Configuration
| Property | Usage | ||
|---|---|---|---|
Present Attribute |
The attribute whose presence you want to verify in the
the underlying identity service
object.
This can be an otherwise private attribute, such as
Default: |
||
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Example
This journey to update a password uses the Attribute Present Decision node to check whether the account has a password:
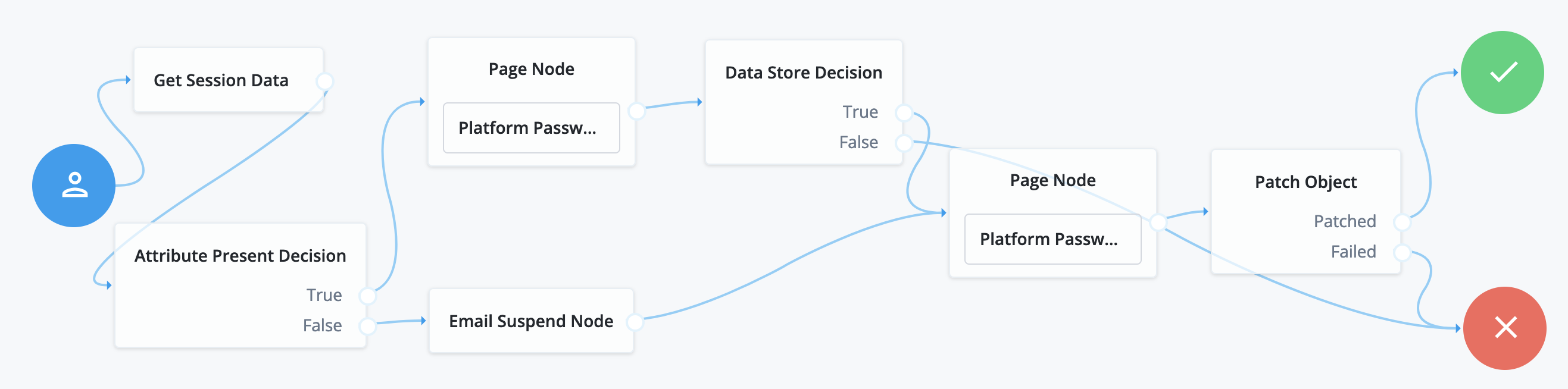
The user has already authenticated before beginning this journey:
-
The Get Session Data node stores the
userNamefrom the session. -
The Attribute Present Decision node checks whether the user object has a password attribute.
-
If so, the first Page node with the Platform Password node prompts the user for the current password.
-
Otherwise, the Email Suspend node sends an email to the user and suspends the flow until the user follows the link in the message.
-
The Data Store Decision node confirms the username-password credentials.
-
The second Page node with the Platform Password node prompts the user for the new password.
-
The Patch Object node updates the user object with the new password.
Attribute Value Decision node
Verifies that the specified attribute satisfies a specific condition.
Use this node to check whether an attribute’s expected value is equal to a collected attribute value, or to validate that the specified attribute was collected.
Examples:
-
To validate that a user provided the country attribute during registration, set the comparison operation to
PRESENT, and the comparison attribute tocountry. -
To validate that the country attribute is set to the United States, set the comparison operation to
EQUALS, the comparison attribute tocountry, and the comparison value toUnited States.
Use Attribute Present Decision node instead
when you need to check for the presence of a private attribute, such as password.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Comparison Operation |
The operation to perform on the object attribute:
|
Comparison Attribute |
The object attribute to compare. |
Comparison Value |
When Comparison Operation is |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. |
Consent Collector node
Prompts the user for consent to share their profile data.
A consent notice is listed for each identity mapping that has consent enabled. If an identity mapping is not created, or the mappings do not have privacy and consent enabled, PingOne Advanced Identity Cloud does not show a consent message to the user.
This node is primarily used in progressive profile and registration flows.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
All Mappings Required |
If enabled, all mappings listed by this node require consent in order to move forward. |
Privacy & Consent Message |
Localized message providing the privacy and consent notice.
The key is the language, such as |
Create Object node
The Create Object node lets you create a new object in the underlying identity service based on information collected during authentication, such as user registration.
Any managed object attributes that are marked as required in the underlying identity service must be collected during authentication in order to create the new object.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Configuration
| Property | Usage | ||
|---|---|---|---|
Identity Resource |
The type of managed identity resource object that this node creates. It must match the identity resource type for the current flow.
Default: |
Errors
This node can log the following warning messages:
| Message | Notes |
|---|---|
Failed to create object |
The preceding nodes don’t provide all the fields required to create the object. |
Failed to retrieve object’s schema |
The node failed to get the list of required attributes from the Identity Resource schema. |
Example
The following example uses this node with the Increment Login Count node to create a new user object.
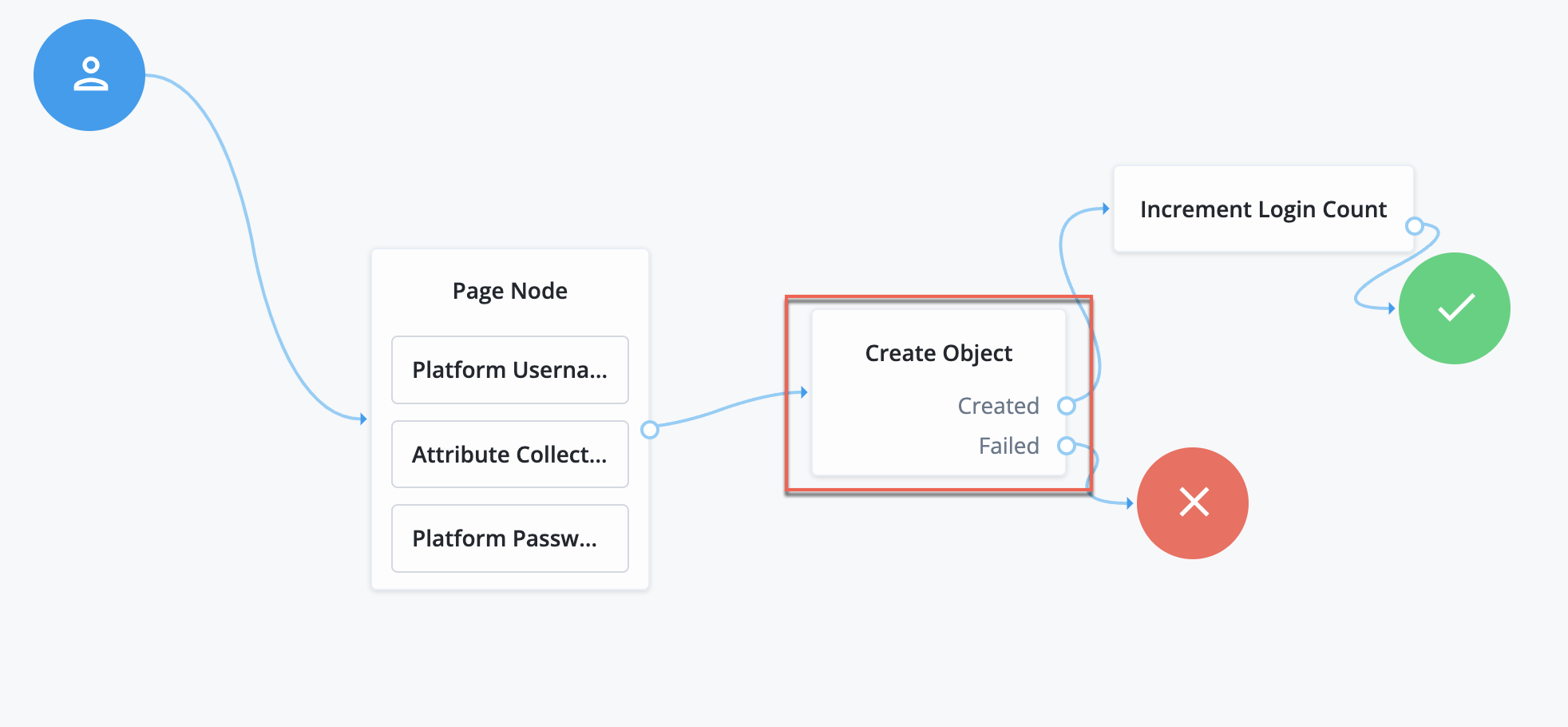
-
The Page node includes various nodes that collect attributes and store them in the shared node state.
-
The Create Object node uses these attributes to create the new user.
-
The Increment Login Count node resets the retry count on successful authentication of the new user.
Display Username node
Fetches a username based on a different identifying attribute, such as an email address, then displays it.
To email the username to the user instead, use the Identify Existing User node combined with a Email Suspend node or Email Template node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
User Name |
The attribute used to identify the username in a managed identity object. |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. When this node serves to recover a username, the identity attribute should be some other attribute that is unique to a user object, such as the email address. The node raises an exception when more than one value exists for this attribute. Make sure the value of whatever attribute you select is unique for each user. |
Identify Existing User node
The Identify Existing User node verifies if a user exists based on an identifying attribute, such as an email address, then makes the value of a specified attribute available in the shared node state.
Use this node in a forgotten password flow to fetch a username to email to the user. To display the username on the screen, use the Display Username node instead.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the Identity Attribute (default: mail) from the shared node state.
If the Identity Attribute is not available, it reads the userName from the shared node state.
Configuration
| Property | Usage |
|---|---|
Identifier |
The attribute to collect from a managed identity object. Default: |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. When this node serves to recover a username, the identity attribute should be some other attribute that is unique to a user object, such as the email address. Default: |
Outputs
The node writes the Identifier and the user account _id to the shared node state.
If the Identifier differs from userName, this node also writes the userName to the shared node state.
Outcomes
True-
The node successfully identified the user and updated the shared node state.
False-
Any other case.
Example
The following example shows a flow to reset a forgotten password:
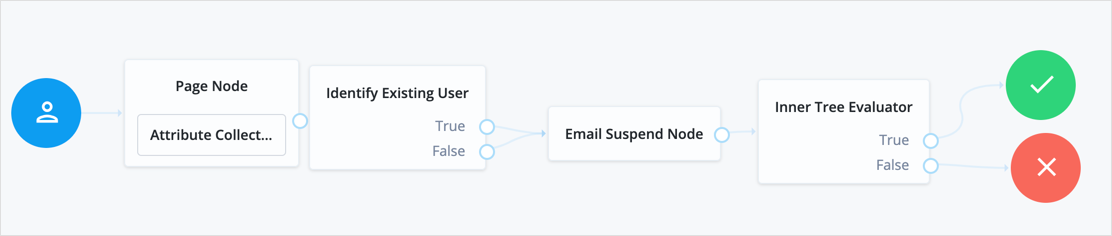
-
The user enters their email in the Attribute Collector node of the Page node.
-
The Identify Existing User node uses the email address to look up the username of the user’s account. If it finds the user account, it adds the username to the shared node state.
-
The Email Suspend node emails the user and suspends authentication.
-
Once authentication resumes, the Inner Tree Evaluator node sends the user to a different flow to reset their password.
KBA Decision node
Checks whether the user account has the required minimum number of KBA questions.
To set the number of KBA questions, edit Configure > Security Questions > Questions > Number in the IDM admin console.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
KBA Definition node
The KBA Definition node collects knowledge-based authentication (KBA) questions and answers.
Use this node when creating or updating a user with KBA enabled. Learn more in Security questions.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Configuration
| Property | Usage |
|---|---|
Purpose Message |
A localized message describing the purpose of the data requested from the user. Default: none |
Allow User-Defined Questions |
When enabled, users can create their own KBA questions. Disable this setting to restrict users to select from predefined questions only. Default: Enabled |
Questions |
Create or modify custom localized questions that the user can choose from when defining security questions. To add a localized security question:
To edit an existing security question, click the edit icon , make your changes, and click Save. Default: |
Errors
This node logs a Failed to retrieve kba configuration warning message when it can’t read the configuration.
Example
The following registration journey prompts for questions and answers when creating an account:
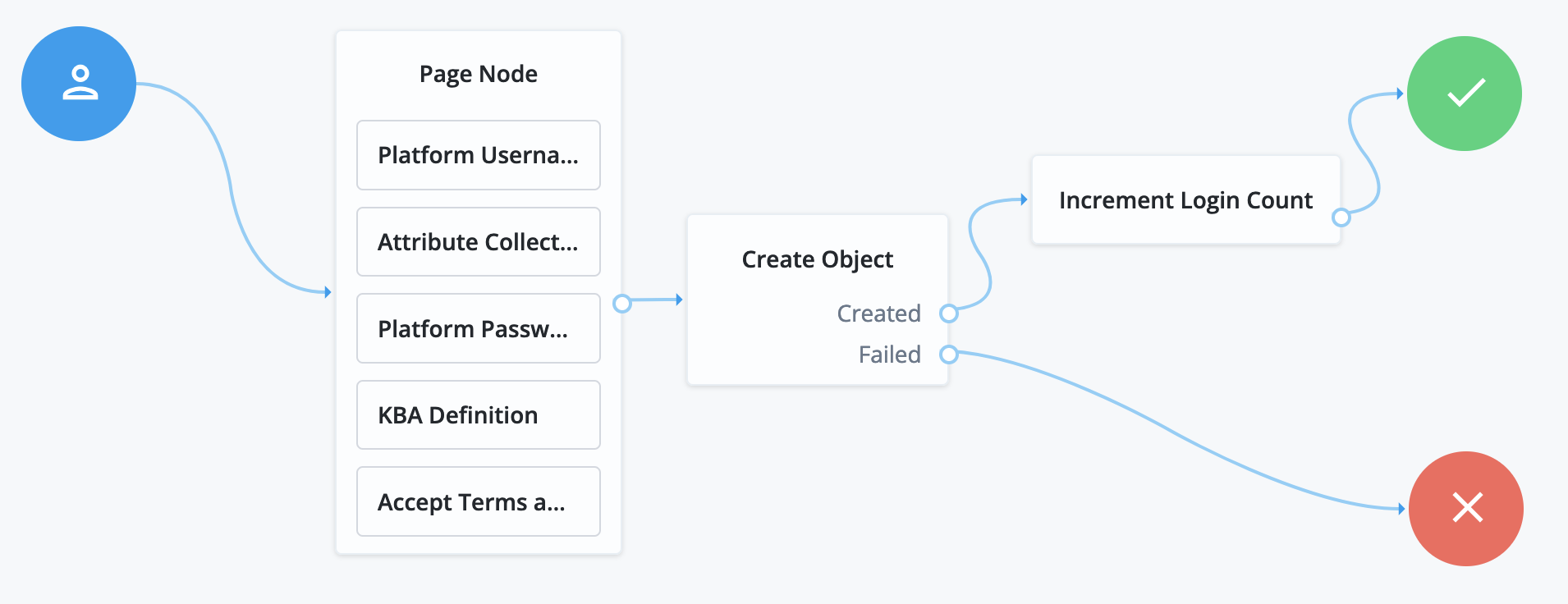
-
The Page node collects registration information:
-
The Platform Username node prompts for and collects a username for the new account.
-
The Attribute Collector node prompts for a given name, a surname, an email address, and profile preferences.
-
The Platform Password node prompts for and collects a password.
-
The KBA Definition node collects questions and answers.
-
The Accept Terms and Conditions node prompts the user to accept the active terms and conditions.
-
-
The Create Object node stores the collected information in the new account object.
-
The Increment Login Count node updates the number of successful authentications.
KBA Verification node
Presents KBA questions to the user, collects answers to those questions, and verifies the input against the user’s stored answers.
Use this node for additional authentication when resetting a forgotten password or username.
To set the number of KBA questions, edit Configure > Security Questions > Questions > Number in the IDM admin console.
Pass-through Authentication node
Authenticates an identity through a connector to a third-party service.
This lets you migrate user profiles without forcing users to reset their passwords, or retain a third-party service indefinitely as the canonical store for authentication credentials.
Before you use the node:
-
Configure the connector to the third-party service.
For details, refer to Sync identities.
-
If you plan to collect credentials in the identity repository for users, synchronize accounts from the third-party service.
For details, refer to Sync identities.
Use this node after collecting the authentication credentials. For example, use the Platform Username node and the Platform Password node to collect the username and password.
Pass the credentials to this node to authenticate the identity against the service.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Connectors that support pass-through authentication
The following connectors support pass-through authentication using the AuthenticateOp interface by default:
All Scripted Groovy-based connectors are capable of pass-through authentication if the AuthenticateScript.groovy script is implemented, but the only default implementation is the ScriptedSQL connector. Learn more in Authenticate script and Authenticate operation.
|
Properties
| Property | Usage |
|---|---|
System Endpoint |
Required. Name of the connector to the third-party service that performs authentication. |
Object Type |
The ICF object type for the object being authenticated. Default: |
Identity Attribute |
The username attribute for authentication. Default: |
Password Attribute |
The password attribute for authentication. Default: |
Example
Before trying this example, synchronize accounts from the third-party service. The example shows a login flow that tries pass-through authentication when local authentication fails, and stores the user password when authentication with the third-party service succeeds.
In this example, the user enters their credentials with the Platform Username node and Platform Password node. The Data Store Decision node authenticates against the platform directory service. On failure, authentication passes through to the third-party service. If authentication with the third-party service is successful, the Identify Existing User node and Required Attributes Present node check for a valid user profile. The Patch Object node updates the user’s profile with the successful password:
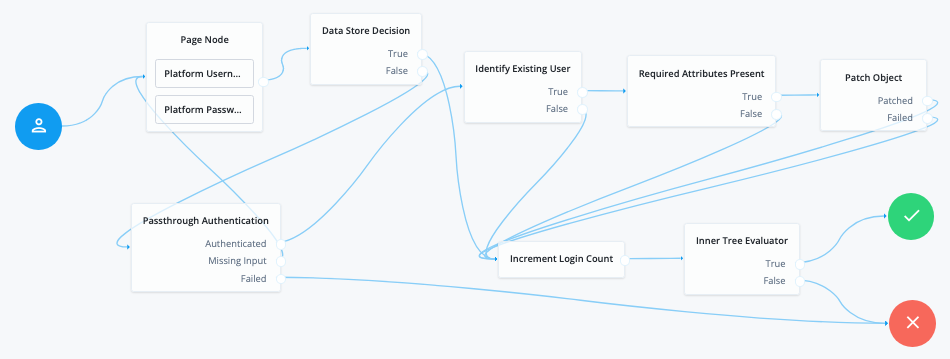
Node connections
| Source node | Outcome path | Target node |
|---|---|---|
Page Node containing:
|
→ |
Data Store Decision |
Data Store Decision |
True |
Increment Login Count |
False |
Pass-through Authentication |
|
Pass-through Authentication |
Authenticated |
Identify Existing User |
Missing Input |
Page Node |
|
Failed |
Failure |
|
Identify Existing User |
True |
Required Attributes Present |
False |
Increment Login Count |
|
Required Attributes Present |
True |
Patch Object |
False |
Increment Login Count |
|
Patch Object |
Patched |
Increment Login Count |
Failed |
Increment Login Count |
|
Increment Login Count |
→ |
Inner Tree Evaluator |
Inner Tree Evaluator |
True |
Success |
False |
Failure |
Patch Object node
The Patch Object node updates the attributes of an existing managed identity object.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the Identity Attribute and the managed object fields to patch from the shared node state.
If it can’t read the Identity Attribute, it reads the userName from the shared node state.
Dependencies
This node depends on the underlying identity service to find and patch the managed object.
Configuration
| Property | Usage | ||
|---|---|---|---|
Patch as Object |
If enabled, update the object as its subject—for example, update a managed user object as the user; otherwise, update the object as the client application. Enable this property to patch fields of the current, authenticated user’s account the client application can’t update. Default: false |
||
Ignored Fields |
Omit the specified shared state fields from the patch. If no fields are specified, the node attempts to update all the shared state fields as part of the patch. Default: none |
||
Identity Resource |
The type of managed identity resource object this node patches. This must match the identity resource type for the current flow.
Default: |
||
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Errors
This node logs the following warning messages when an update fails:
-
Failed to create object -
Failed to patch object
Review the logs for additional messages describing the problem.
Example
This journey uses the Patch Object node to update a user’s password:
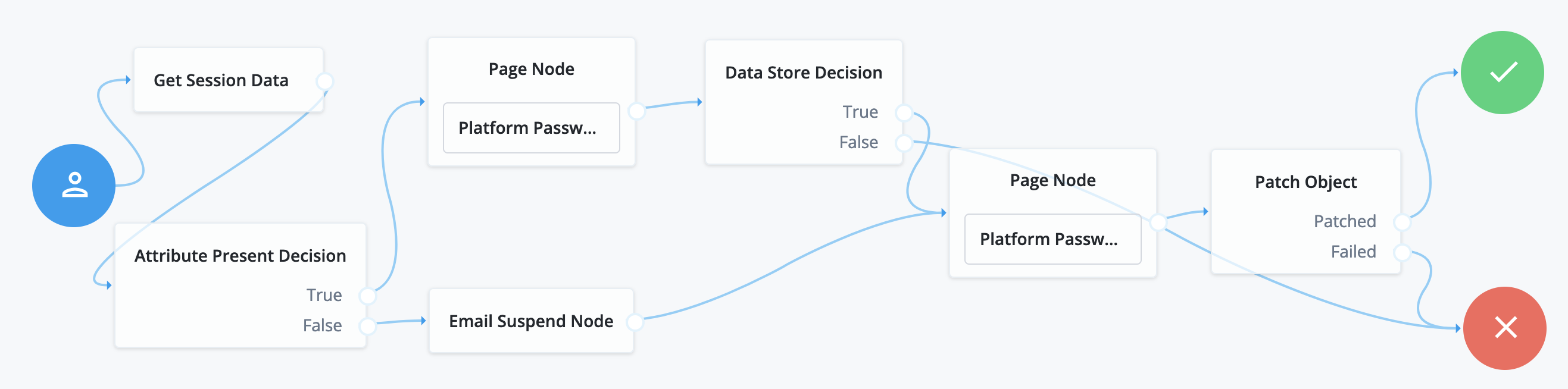
The user has already authenticated before beginning this journey:
-
The Get Session Data node stores the
userNamefrom the session. -
The Attribute Present Decision node checks whether the user object has a password attribute.
-
If so, the first Page node with the Platform Password node prompts the user for the current password.
-
Otherwise, the Email Suspend node sends an email to the user and suspends the flow until the user follows the link in the message.
-
The Data Store Decision node confirms the username-password credentials.
-
The second Page node with the Platform Password node prompts the user for the new password.
-
The Patch Object node updates the user object with the new password.
PingOne Create User node
The PingOne Create User node can create new users in the PingOne platform.
You can configure the node to create a user including their profile data or to create an anonymized user.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the username field from the shared node state to access the user’s identity profile.
Implement a Platform Username node before this node in the journey.
You should also verify the user’s identity by using an Identity Store Decision node.
Dependencies
This node requires a PingOne Worker Service configuration so that it can authenticate to your PingOne instance.
You can find information on the properties used by the service in PingOne Worker service.
Configuration
| Property | Usage | ||
|---|---|---|---|
PingOne Worker Service ID |
The ID of the PingOne worker service for connecting to PingOne. |
||
Population ID |
The ID of the population in PingOne to check for users or provision new ones. If not specified, the node uses the environment’s default population ID. |
||
Anonymized user |
When enabled, the node creates a user in PingOne with only a unique identifier and a language attribute. It does not add any other profile attributes, helping prevent any personally identifiable information (PII) from being shared. |
||
AM Identity Attribute |
The attribute from the user’s PingOne Advanced Identity Cloud profile that the node uses as the username for the account created in PingOne.
Default: |
||
Capture failure |
Capture the details in shared state if a failure occurs. The node stores the details in a variable named Default: Example: json |
Outputs
The node is non-interactive and does not send a callback to the client.
If the node was able to create a new user in PingOne it stores the PingOne user identifier in a state variable named pingOneUserId. For example a648aaac-ch15-b357-457b-8d2e714180ff.
If you select Capture failure, the node stores any error response in a shared state variable named pingOneCreateUserFailureReason.
Outcomes
True
The node created an account in PingOne.
False
The node did not create an account in PingOne.
The journey also uses this outcome if any error occurs. Enable Capture Failure to store the details in node state.
Example
The following example journey leverages PingOne Verify to perform user identity verification.
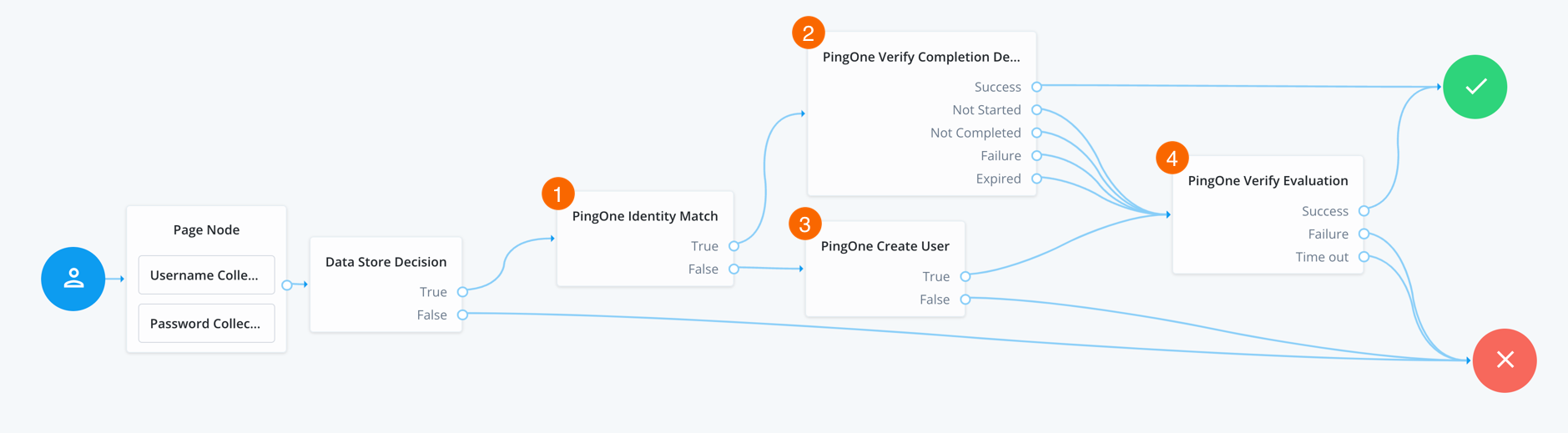
-
The user enters their credentials, which the Data Store Decision node then verifies against the identity store.
-
1 The PingOne Identity Match node checks PingOne for a matching user.
-
2 If a user is found, the PingOne Verify Completion Decision node checks the user’s most recent verification transaction to determine the status:
- Success
-
The user successfully completed the most recent PingOne Verify transaction, so continue directly to the Success node, completing the authentication journey.
- Not Completed
-
The user has an existing PingOne Verify transaction in progress, so continue the journey to resume the existing verification transaction.
The node adds the user’s existing transaction ID to the shared node state in a variable named
pingOneVerifyTransactionId. - Not Started / Failure / Expired
-
The user either does not have an existing transaction (
Not Started), or did not successfully complete the most recent PingOne Verify transaction, or it expired, so continue the journey to start a new verification transaction.
-
3 If a user is not found, the PingOne Create User node creates a new user in PingOne.
-
4 The PingOne Verify Evaluation node starts a new PingOne Verify evaluation, or continues an existing one if
pingOneVerifyTransactionIdis present in the shared node state, and either completes or fails the journey based on the result.
PingOne Delete User node
The PingOne Delete User node can delete users from the PingOne platform.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the pingOneUserId variable from node state. The variable must contain the identifier of the user to delete from PingOne. For example, a648aaac-ch15-b357-457b-8d2e714180ff.
Use either of the following nodes to populate the pingOneUserId variable in shared state:
Dependencies
This node requires a PingOne Worker Service configuration so that it can authenticate to your PingOne instance.
You can find information on the properties used by the service in PingOne Worker service.
Configuration
| Property | Usage |
|---|---|
PingOne Worker Service ID |
The ID of the PingOne worker service for connecting to PingOne. |
Capture failure |
Capture the details in shared state if a failure occurs. The node stores the details in a variable named Default: Example: json |
PingOne Identity Match node
The PingOne Identity Match node checks that users that exist in the ForgeRock platform also exist in the PingOne platform.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the username field from the shared node state to access the user’s identity profile.
Implement a Platform Username node before this node in the journey.
You should also verify the user’s identity by using an Identity Store Decision node.
Dependencies
This node requires a PingOne Worker Service configuration so that it can authenticate to your PingOne instance.
You can find information on the properties used by the service in PingOne Worker service.
Configuration
| Property | Usage |
|---|---|
PingOne Worker Service ID |
The ID of the PingOne worker service for connecting to PingOne. |
Population ID |
The ID of the population in PingOne to check for users or provision new ones. If not specified, the node uses the environment’s default population ID. |
AM Identity Attribute |
The attribute from the user’s ForgeRock profile that the node uses to match their account in PingOne. Default: |
Ping Identity Attribute |
The attribute from the user’s PingOne profile that the node uses to search for a matching account. If there are multiple entries with the same attribute value in the PingOne directory server, ensure that this property is specific enough to retrieve only one entry. Default: |
Capture failure |
Capture the details in shared state if a failure occurs. The node stores the details in a variable named Default: Example: json |
Outputs
The node is non-interactive and does not send a callback to the client.
If the node was able to find a unique match in PingOne it stores the PingOne user identifier in a state variable named pingOneUserId. For example a648aaac-ch15-b357-457b-8d2e714180ff.
If you select Capture failure, the node stores any error response in a shared state variable named pingOneIdentityMatchFailureReason.
Outcomes
True
The node found a unique matching account in PingOne.
False
The node did not find a unique match in PingOne.
Example
The following example journey leverages PingOne Verify to perform user identity verification.
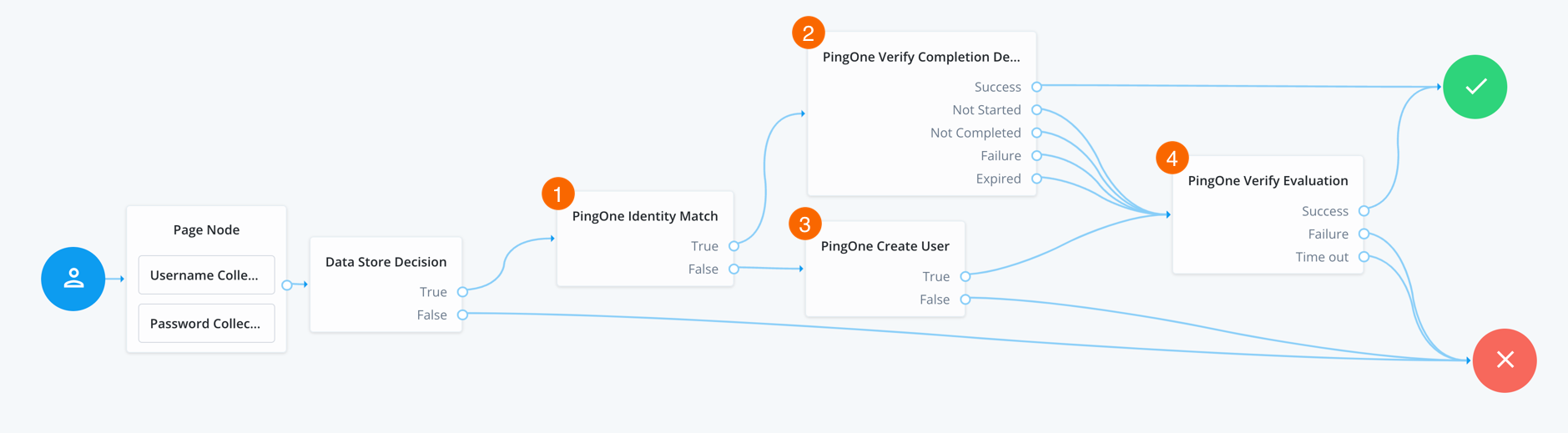
-
The user enters their credentials, which the Data Store Decision node then verifies against the identity store.
-
1 The PingOne Identity Match node checks PingOne for a matching user.
-
2 If a user is found, the PingOne Verify Completion Decision node checks the user’s most recent verification transaction to determine the status:
- Success
-
The user successfully completed the most recent PingOne Verify transaction, so continue directly to the Success node, completing the authentication journey.
- Not Completed
-
The user has an existing PingOne Verify transaction in progress, so continue the journey to resume the existing verification transaction.
The node adds the user’s existing transaction ID to the shared node state in a variable named
pingOneVerifyTransactionId. - Not Started / Failure / Expired
-
The user either does not have an existing transaction (
Not Started), or did not successfully complete the most recent PingOne Verify transaction, or it expired, so continue the journey to start a new verification transaction.
-
3 If a user is not found, the PingOne Create User node creates a new user in PingOne.
-
4 The PingOne Verify Evaluation node starts a new PingOne Verify evaluation, or continues an existing one if
pingOneVerifyTransactionIdis present in the shared node state, and either completes or fails the journey based on the result.
PingOne Verify Completion Decision node
The PingOne Verify Evaluation node determines the completion status of the most recent identity verification transaction for a PingOne user.
The node checks the previous identity verification transaction for the user and returns an outcome based on the verification status.
You can use this node to prevent users from repeatedly having to verify their identity by checking their most recent verification transaction. You can also determine if a transaction is already in progress, to prevent multiple ongoing transactions.
For further customization of behavior, use a PingOne Verify Completion Decision script to evaluate the verification transactions started for the specified PingOne user, and the associated metadata. The script can then add additional context to the journey, or perform additional business logic, dependent on the verification metadata.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires that the user has an account in the PingOne environment. It requires that the journey stores the PingOne user ID for the account in the shared state variable named pingOneUserId.
Use a PingOne Identity Match node to populate the shared state with the user’s PingOne ID.
The shared state data must also include all required Script Inputs properties.
You can restrict available inputs using the Script Inputs field when configuring the node.
Dependencies
This node requires a PingOne Worker Service configuration so that it can connect to your PingOne instance and send it the necessary data to perform PingOne Verify evaluations as part of the journey.
You can find information on the properties used by the service in PingOne Worker service.
Configuration
| Property | Usage |
|---|---|
PingOne Worker service ID |
The ID of the PingOne worker service for connecting to PingOne. |
Use a script to process Verify transactions |
When enabled, use a PingOne Verify Completion Decision script to process verification transaction data relating to the user. Example verification transaction datajson For more information on verification transaction data, refer to Read All Verify Transactions. |
Manage Verify transactions script |
The name of the script to process the JSON containing verification transactions relating to the user. The script must be of type PingOne Verify Completion Decision. Refer to Example scripts. |
Script Inputs |
Optionally, list the shared state data properties required by the script. Declare each required property, enter Default: |
Capture failure |
Capture the details in shared state if a failure occurs. The node stores the details in a variable named Default: Example: json |
Outputs
The node is non-interactive and doesn’t send a callback to the client.
If the node discovers that the user’s most recent Verify transaction isn’t yet complete,
it adds the ID of the transaction to the shared state, in a variable named pingOneVerifyTransactionId.
The PingOne Verify Evaluation node can use this value to continue the existing Verify evaluation,
rather than start a brand new one.
If you select Capture failure, the node stores any error response in a shared state variable named pingOneVerifyCompletionFailureReason.
If you enable the Use a script to process Verify transactions property, the script you specify can add values to the shared state, as required.
Outcomes
Success-
The user successfully completed their most recent PingOne Verify evaluation.
Failure-
The user did not successfully complete their most recent PingOne Verify evaluation, or an error occurred.
Expired-
The user’s most recent PingOne Verify evaluation timed out. Usually this happens when a user starts a verification transaction, but does not complete it within the time limit.
Not Started-
The user’s most recent PingOne Verify evaluation has not yet started.
Not Completed-
The user’s most recent PingOne Verify evaluation has started, but not yet completed.
Examples
Example journey
The following example journey leverages PingOne Verify to perform user identity verification.
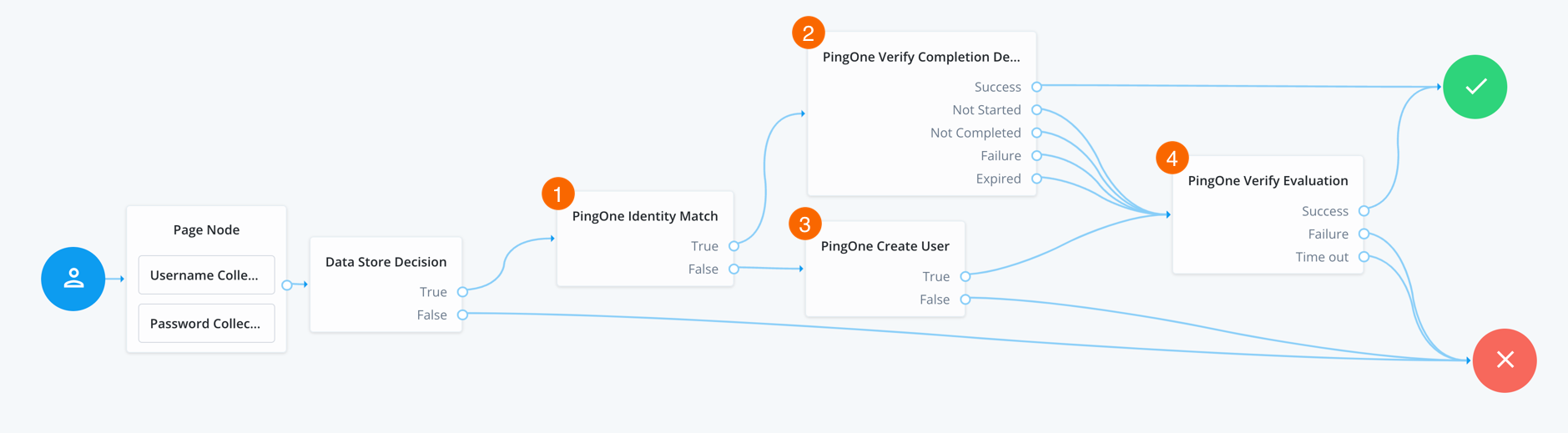
-
The user enters their credentials, which the Data Store Decision node then verifies against the identity store.
-
1 The PingOne Identity Match node checks PingOne for a matching user.
-
2 If a user is found, the PingOne Verify Completion Decision node checks the user’s most recent verification transaction to determine the status:
- Success
-
The user successfully completed the most recent PingOne Verify transaction, so continue directly to the Success node, completing the authentication journey.
- Not Completed
-
The user has an existing PingOne Verify transaction in progress, so continue the journey to resume the existing verification transaction.
The node adds the user’s existing transaction ID to the shared node state in a variable named
pingOneVerifyTransactionId. - Not Started / Failure / Expired
-
The user either does not have an existing transaction (
Not Started), or did not successfully complete the most recent PingOne Verify transaction, or it expired, so continue the journey to start a new verification transaction.
-
3 If a user is not found, the PingOne Create User node creates a new user in PingOne.
-
4 The PingOne Verify Evaluation node starts a new PingOne Verify evaluation, or continues an existing one if
pingOneVerifyTransactionIdis present in the shared node state, and either completes or fails the journey based on the result.
Example scripts
These example scripts demonstrate some use cases for the PingOne Verify Completion Decision node. They use the verifyTransactionsHelper next-generation script binding, which gives access to the data used during a PingOne Verify transaction.
To learn more about the binding, refer to Access PingOne Verify transactions and manage associated use.
- Example 1
-
Check the status of the user’s most recent PingOne Verify transaction and that the ID used was a driving license.
Show example script
/** ****************************************************************** * * The following script checks the status of the user's most recent * identity check, and ensures the ID used was a driver's license. * * Global node variables accessible within this scope: * 1. `nodeState` provides access to auth tree state attributes * 2. `verifyTransactionsHelper` provides access to verify transactions * 3. `outcome` variable maps to auth tree node outcomes; values are * 'successOutcome', 'notStartedOutcome', 'notCompletedOutcome', * 'expiredOutcome', or 'failureOutcome'. * ******************************************************************/ // Retrieve the user's latest verified transaction. var result = verifyTransactionsHelper.getLastVerifyTransaction(); if (result != null) { var lastTransaction = JSON.parse(result); if (lastTransaction.hasOwnProperty("transactionStatus")) { // Get the status of the transaction. var status = lastTransaction.transactionStatus.status; // Determine the document type and verify if it is a Driver's License. var verifiedDocuments = lastTransaction.verifiedDocuments; if (status == "SUCCESS" && verifiedDocuments.includes("driver_license")) { outcome = "successOutcome"; } else { outcome = "failureOutcome"; } } else { outcome = "notStartedOutcome"; } }javascript
- Example 2
-
Check the ID used in the user’s most recent PingOne Verify transaction and that their age is 18 or over.
This data is available for a short timeframe after the verification.
Usually 30 minutes after PingOne Verify reaches its verification decision.
Show example script
/** ****************************************************************** * * The following script checks the ID used in the user's most recent * identity check, and that their age is 18 or over. * * Note: * This data is available for a short timeframe after the verification. * Usually 30 minutes after a verification decision is reached. * * Global node variables accessible within this scope: * 1. `nodeState` provides access to auth tree state attributes * 2. `verifyTransactionsHelper` provides access to verify transactions * 3. `outcome` variable maps to auth tree node outcomes; values are * 'successOutcome', 'notStartedOutcome', 'notCompletedOutcome', * 'expiredOutcome', or 'failureOutcome'. * ******************************************************************/ // Retrieve the user's latest verified transaction. var result = verifyTransactionsHelper.getLastVerifyTransaction(); if (result != null) { var lastTransaction = JSON.parse(result); if (lastTransaction.hasOwnProperty("id")) { // Obtain the ID of the last transaction. var lastTransactionId = lastTransaction.id; // Get the verified data for the Government ID provided by the user. var verifiedDataResult = verifyTransactionsHelper.getVerifiedDataByType(lastTransactionId, "GOVERNMENT_ID"); // Determine the age of the user. if (verifiedDataResult != null) { var verifiedData = JSON.parse(verifiedDataResult); var dateString = verifiedData._embedded.verifiedData[0].data.birthDate; if (dateString != null && dateString.trim() != "") { var birthDate = new Date(dateString + "T00:00:01"); var currentDate = new Date().getTime(); var difference = currentDate - birthDate; var currentAge = Math.floor(difference / (1000 * 60 * 60 * 24 * 365.25)); if (currentAge >= 18) { outcome = "successOutcome"; } else { outcome = "failureOutcome"; } } else { outcome = "failureOutcome"; } } else { outcome = "notCompletedOutcome"; } } else { outcome = "notStartedOutcome"; } } else { outcome = "notStartedOutcome"; }javascript
- Example 3
-
Check the user’s most recent PingOne Verify transaction to obtain the expiration date for the Government ID provided.
The node stores this information in a variable named
governmentIdExpireDatein the shared state, but you could also store it in a user attribute to determine when to perform the next identity verification.This data is available for a short timeframe after the verification.
Usually 30 minutes after PingOne Verify reaches its verification decision.
Show example script
/** ****************************************************************** * * The following script checks the user's most recent Verify transaction * to obtain the expiration date for the Government ID provided. * * This information is stored in a variable named `governmentIdExpireDate` * in the shared state, but could also be stored as a user attribute * to determine when to perform the next identity verification. * * Note: * This data is available for a short timeframe after the verification. * Usually 30 minutes after a verification decision is reached. * * Global node variables accessible within this scope: * 1. `nodeState` provides access to auth tree state attributes * 2. `verifyTransactionsHelper` provides access to verify transactions * 3. `outcome` variable maps to auth tree node outcomes; values are * 'successOutcome', 'notStartedOutcome', 'notCompletedOutcome', * 'expiredOutcome', or 'failureOutcome'. * ******************************************************************/ // Retrieve the user's latest verified transaction. var result = verifyTransactionsHelper.getLastVerifyTransaction(); if (result != null) { var lastTransaction = JSON.parse(result); if (lastTransaction.hasOwnProperty("id")) { // Obtain the ID of the last transaction. var lastTransactionId = lastTransaction.id; // Get the verified data for the Government ID provided by the user. var verifiedDataResult = verifyTransactionsHelper.getVerifiedDataByType(lastTransactionId, "GOVERNMENT_ID"); // Get the expire date and set on shared state. if (verifiedDataResult != null) { var verifiedData = JSON.parse(verifiedDataResult); var expireDate = verifiedData._embedded.verifiedData[0].data.expirationDate; if (expireDate != null && expireDate.trim() != "") { nodeState.putShared("governmentIdExpireDate", expireDate); outcome = "successOutcome"; } else { outcome = "failureOutcome"; } } else { outcome = "notCompletedOutcome"; } } else { outcome = "notStartedOutcome"; } } else { outcome = "notStartedOutcome"; }javascript
- Example 4
-
Check that the user has at least one successful identity verification in the past 365 days.
Show example script
/** ****************************************************************** * * The following script checks that the user has at least one successful * identity verification in the past 365 days. * * Global node variables accessible within this scope: * 1. `nodeState` provides access to auth tree state attributes * 2. `verifyTransactionsHelper` provides access to verify transactions * 3. `outcome` variable maps to auth tree node outcomes; values are * 'successOutcome', 'notStartedOutcome', 'notCompletedOutcome', * 'expiredOutcome', or 'failureOutcome'. * ******************************************************************/ // Retrieve all transactions for the user var result = verifyTransactionsHelper.getAllVerifyTransactions(); if (result != null) { var allTransactions = JSON.parse(result); if (allTransactions != null) { // Loop through the transactions to find a successful verification within the last 12 months. var verifyTransactions = allTransactions._embedded.verifyTransactions; var found = false; for (var i = 0; i < verifyTransactions.length; i++) { var transaction = verifyTransactions[i]; // Get the status of the transaction. var status = transaction.transactionStatus.status; // If status is success, verify if it is still valid if (status == "SUCCESS") { found = true; // Calculate the number of days var dateString = transaction.createdAt; var createdDate = new Date(dateString); var currentDate = new Date().getTime(); var difference = Math.abs(createdDate - currentDate); var numDaysBetween = difference / (1000 * 60 * 60 * 24); if (numDaysBetween <= 365) { outcome = "successOutcome"; break; } else { outcome = "expiredOutcome"; } } } // No successful transaction found if (found == false) { outcome = "failureOutcome"; } } else { outcome = "notStartedOutcome"; } } else { outcome = "notStartedOutcome"; }javascript
- Example 5
-
Check the user’s most recent PingOne Verify transaction to review the biographic match results.
The script uses the Failure outcome if the match confidence for any attribute is anything other than
HIGH.Show example script
/** ****************************************************************** * * The following script checks the user's last identity verification to * review the "Biographic Match" results. * * The script uses the failure outcome if the match confidence for any * attribute is below `HIGH`. * * Global node variables accessible within this scope: * 1. `nodeState` provides access to auth tree state attributes * 2. `verifyTransactionsHelper` provides access to verify transactions * 3. `outcome` variable maps to auth tree node outcomes; values are * 'successOutcome', 'notStartedOutcome', 'notCompletedOutcome', * 'expiredOutcome', or 'failureOutcome'. * ******************************************************************/ // Retrieve the user's latest verified transaction. var result = verifyTransactionsHelper.getLastVerifyTransaction(); if (result != null) { var lastTransaction = JSON.parse(result); if (lastTransaction.hasOwnProperty("id")) { // Obtain the ID of the last transaction. var lastTransactionId = lastTransaction.id; // Get all the metadata. var allMetadataResult = verifyTransactionsHelper.getAllMetadata(lastTransactionId); // Loop through the metadata to find the biographic match results. var biographicMatchResults; if (allMetadataResult != null) { var allMetadataJson = JSON.parse(allMetadataResult); var allMetadata = allMetadataJson._embedded.metaData; for (var i = 0; i < allMetadata.length; i++) { var metadata = allMetadata[i]; var type = metadata.type; var status = metadata.status; if (type == "BIOGRAPHIC_MATCH" && status == "SUCCESS") { biographicMatchResults = metadata.data.biographic_match_results; break; } } } else { outcome = "failureOutcome"; } // Validate the biographic match results if (biographicMatchResults != null && biographicMatchResults.length > 0) { var success = true; for (var j = 0; j < biographicMatchResults.length; j++) { var match = biographicMatchResults[j].match; if (match != "HIGH") { success = false; break; } } if (success) { outcome = "successOutcome"; } else { outcome = "failureOutcome"; } } else { outcome = "failureOutcome"; } } else { outcome = "notStartedOutcome"; } } else { outcome = "notStartedOutcome"; }javascript
PingOne Verify Evaluation node
The PingOne Verify Evaluation node leverages the PingOne Verify Service to initiate a new or continue an existing verification transaction.
It offers a range of delivery methods, such as a QR code, email, or SMS to start the identity verification process.
You can customize the verification types users can perform in the PingOne Verification Policy.
Learn more in Verify policies.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires that the user has an account in the PingOne environment. It requires that the journey stored the PingOne user ID for the account in a shared state variable named pingOneUserId.
Use a PingOne Identity Match node to populate the shared state with the user’s PingOne ID.
If there’s a transaction ID in the shared state variable named pingOneVerifyTransactionId, this node continues that evaluation, rather than starting a new one.
Use a PingOne Verify Completion Decision node to determine the status of any previous transactions and populate the shared state with an in-progress transaction ID.
Dependencies
This node requires a PingOne Worker Service configuration so that it can connect to your PingOne instance and send it the necessary data to perform PingOne Verify evaluations as part of the journey.
You can find information on the properties used by the service in PingOne Worker service.
Configuration
| Property | Usage | ||
|---|---|---|---|
PingOne Worker Service ID |
The ID of the PingOne worker service for connecting to PingOne. |
||
Verify Policy ID |
The ID of the policy to use for the PingOne Verify evaluation. If not specified, the node uses the environment’s default Verify policy. |
||
Verify URL delivery method |
How the user will receive the URL they need to start a PingOne Verify evaluation. Choose from:
On completion, redirect the user back to PingOne Advanced Identity Cloud to continue the authentication journey. Default: |
||
Allow user to choose the URL delivery method |
When enabled, the node prompts the user to choose the URL delivery method. |
||
Delivery method message |
Add the text per locale to display when prompting the user to choose their delivery method:
To edit an entry, click its pencil icon (). To remove an entry, click its delete icon (). |
||
QR code message |
Add the text per locale to display when you select QR code as the delivery method:
To edit an entry, click its pencil icon (). To remove an entry, click its delete icon (). |
||
Redirect message |
Add the text per locale to display when you select Redirect as the delivery method, and the node redirects the user back to PingOne Advanced Identity Cloud to continue the journey:
To edit an entry, click its pencil icon (). To remove an entry, click its delete icon (). |
||
Waiting message |
Add the text per locale to display while waiting for the user to respond to the Verify transaction, when using the SMS or Email delivery methods:
To edit an entry, click its pencil icon (). To remove an entry, click its delete icon (). |
||
Biographic Matching |
Require that the specified data obtained from the user’s identity documents match the paired attribute in the user’s profile. To create a pairing:
To edit an entry, click its pencil icon (). To remove an entry, click its delete icon (). |
||
Store Verification Metadata |
When enabled, store the verification metadata returned from PingOne Verify in shared state under a key named Example verification metadatajson
Default: Disabled |
||
Store Verified Data |
When enabled, store a list of the verified data submitted by the user in shared state under a key named Example verified datajson
Default: Disabled |
||
Capture failure |
Capture the details in shared state if a failure occurs. The node stores the details in a variable named Default: Example: json |
1 Specify a
locale that Java supports, such as en-gb. Otherwise, the node throws a configuration exception with an Invalid locale provided message.
Outputs
-
If Allow user to choose the URL delivery method is selected, the node sends the following callbacks:
TextOutputCallback-
Contains the Delivery method message.
ConfirmationCallback-
Contains the options available to the client application.
-
When using the
QR CodeURL delivery method, the node sends the following callbacks:TextOutputCallback-
Contains the QR Code message.
ScriptTextOutputCallback-
Contains JavaScript script to run to display the QR code.
HiddenValueCallback-
Contains the actual URL to start the verification. The client might display this to users on a mobile device that cannot scan a QR code, or to render their own QR code, for example.
PollingWaitCallback-
Waits for the user to complete the verification, and the Waiting message.
-
When using the
EmailorSMSURL delivery method, the node sends the following callbacks:PollingWaitCallback-
Waits for the user to complete the verification, and contains the Waiting message.
-
When using the
Redirectdelivery method, the node sends the following callbacks:RedirectCallback-
Contains the URI to redirect the user to for identity verification, using the PingOne Verify web application.
-
If you select Store Verification Metadata, the node outputs the verification metadata JSON in a state variable named
pingOneVerifyMetadata.To learn more about verification metadata, refer to Read All Verification Metadata.
-
If you select Store Verified Data, the node outputs the verified information gathered from the user’s ID in a state variable named
pingOneVerifyVerifiedData.To learn more about verified data, refer to Read One User Verified Data.
-
If you select Capture failure, the node stores any error response in a shared state variable named
pingOneVerifyEvaluationFailureReason.
Outcomes
Success-
The user successfully completed the PingOne Verify evaluation.
Failure-
The user did not successfully complete the PingOne Verify evaluation, or an error occurred.
Time Out-
The node did not receive a response from the user performing the verification before the timeout specified in the Verify Transaction Timeout property.
Example
The following example journey leverages PingOne Verify to perform user identity verification.
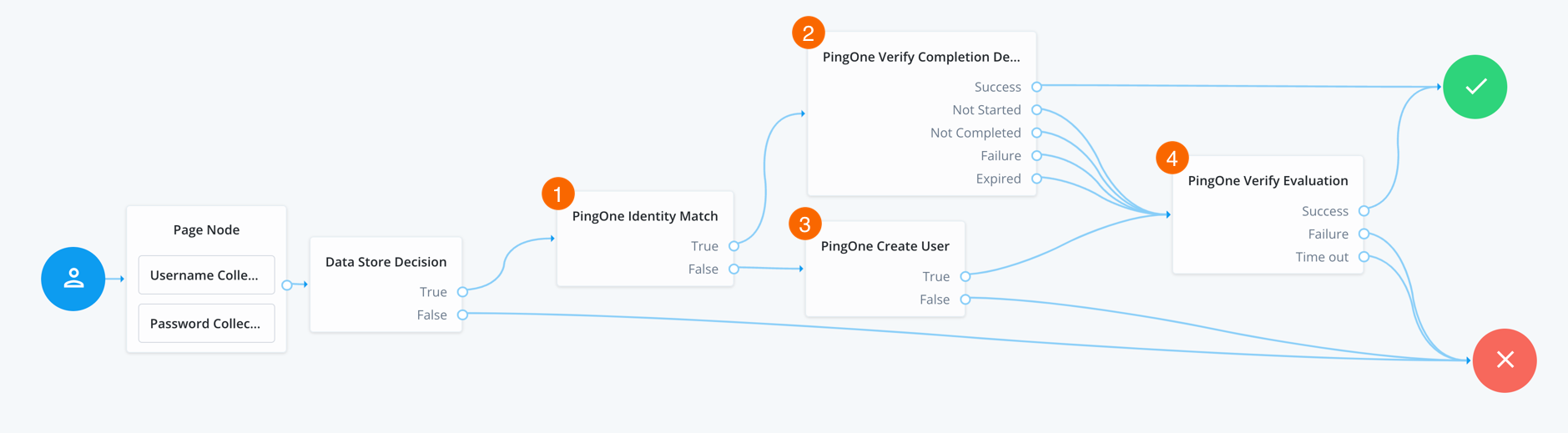
-
The user enters their credentials, which the Data Store Decision node then verifies against the identity store.
-
1 The PingOne Identity Match node checks PingOne for a matching user.
-
2 If a user is found, the PingOne Verify Completion Decision node checks the user’s most recent verification transaction to determine the status:
- Success
-
The user successfully completed the most recent PingOne Verify transaction, so continue directly to the Success node, completing the authentication journey.
- Not Completed
-
The user has an existing PingOne Verify transaction in progress, so continue the journey to resume the existing verification transaction.
The node adds the user’s existing transaction ID to the shared node state in a variable named
pingOneVerifyTransactionId. - Not Started / Failure / Expired
-
The user either does not have an existing transaction (
Not Started), or did not successfully complete the most recent PingOne Verify transaction, or it expired, so continue the journey to start a new verification transaction.
-
3 If a user is not found, the PingOne Create User node creates a new user in PingOne.
-
4 The PingOne Verify Evaluation node starts a new PingOne Verify evaluation, or continues an existing one if
pingOneVerifyTransactionIdis present in the shared node state, and either completes or fails the journey based on the result.
Platform Password node
The Platform Password node prompts the user to enter their password and stores it in a configurable property of the shared node state.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node uses the _id of the object for policy evaluation.
For existing users, the user’s _id must be in the shared state to evaluate user-specific policies,
such as password history, cannot-contain-others, and so on.
No _id is available for new users.
Dependencies
If this node’s Validate Password setting is enabled, the node relies on the underlying identity service for password policies.
Configuration
| Property | Usage | ||
|---|---|---|---|
Validate Password |
When enabled, this node uses the password policies in the underlying identity service to validate the user’s input. It returns any policy failures as errors. For example, if you submitted an invalid password on registration, the response from this node would include a list of failed policies: json Default: disabled |
||
Password Attribute |
The attribute used to store a password in the managed identity object. Default: |
||
Confirm Password |
Enable this option to require the user to enter the password identically in a second field.
Default: disabled |
||
Checkmark Policy Display |
Enable this option to show a checkmark instead of faded bullet points on successful password validation.
Default: disabled |
Outputs
On success, this node updates the Password Attribute property in the shared node state with the password.
The captured password is transient, persisting only until the authentication flow reaches the next node requiring user interaction. It may be persisted to the secure state if required later in the journey.
Errors
This node does not log error or warning messages of its own.
If it fails to get the result from
the underlying identity service
for a validation request,
this node throws an exception with a Communication failure message.
Example
The following journey uses a Page node containing the Platform Username node and Platform Password node to collect the username and password and set their values in the shared node state:
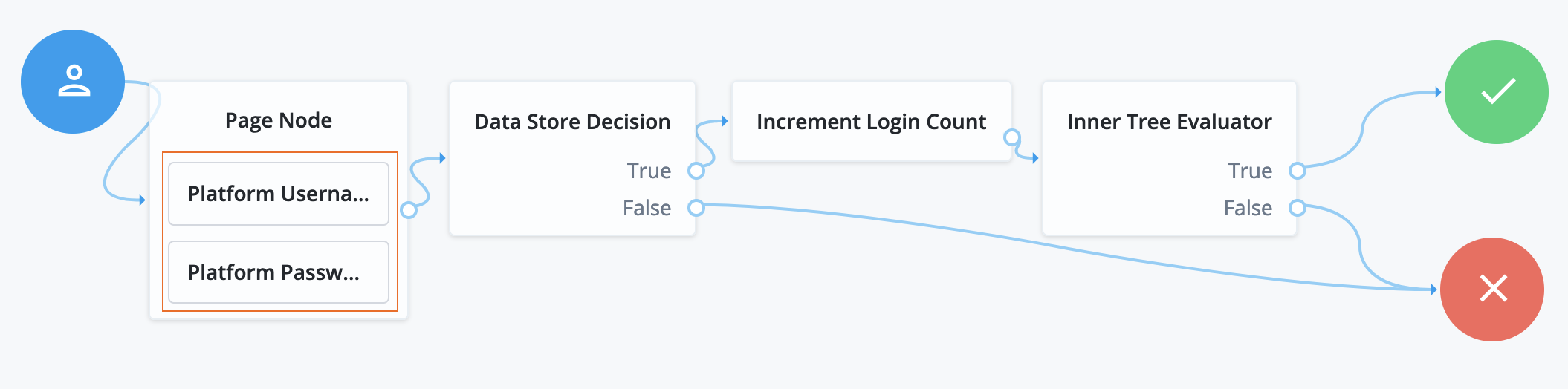
-
The Page node presents a page with input fields to prompt for the username and password.
-
The Platform Username node collects and injects the
userNameinto the shared node state. -
The Platform Password node collects and injects the
passwordinto the shared node state.
-
-
The Data Store Decision node uses the username and password to determine whether authentication is successful.
-
The Increment Login Count node updates the login count on successful authentication.
-
The Inner Tree Evaluator node invokes a nested journey for progressive profiling.
Platform Username node
The Platform Username node prompts the user to enter their username and stores it in a configurable property of the shared node state.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Dependencies
If this node’s Validate Username setting is enabled, the node relies on the underlying identity service for username policies.
Configuration
| Property | Usage | ||
|---|---|---|---|
Validate Username |
When enabled, this node uses the username policies in the underlying identity service to validate the user’s input. It returns any policy failures as errors.
Default: disabled |
||
Username Attribute |
The attribute used to store a username in the managed identity object. Default: |
Outputs
On success, this node updates the Username Attribute property in the shared node state with the username.
Errors
This node does not log error or warning messages of its own.
If it fails to get the result from
the underlying identity service
for a validation request,
this node throws an exception with a Communication failure message.
Example
The following journey uses a Page node containing the Platform Username node and Platform Password node to collect the username and password and set their values in the shared node state:
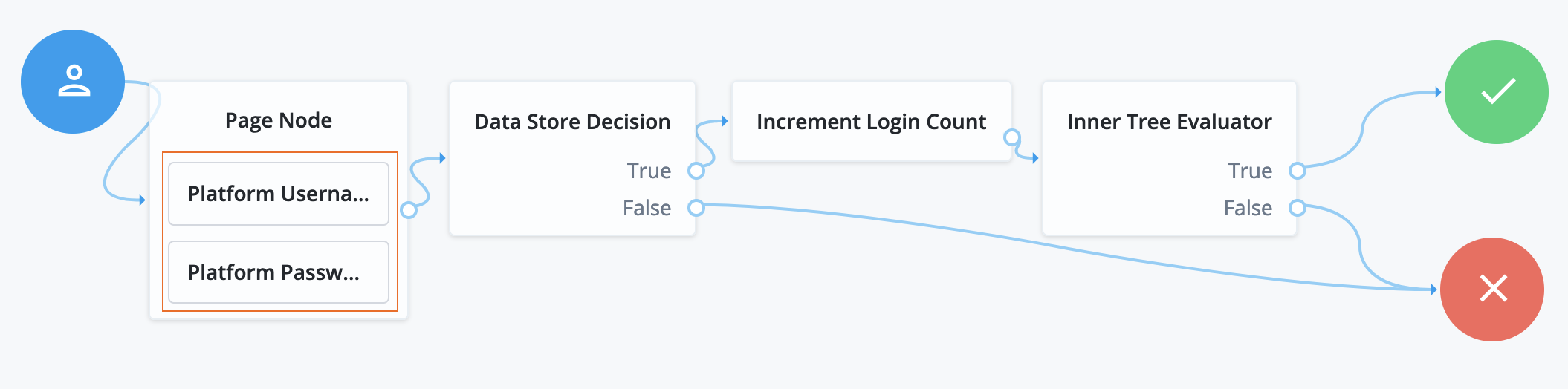
-
The Page node presents a page with input fields to prompt for the username and password.
-
The Platform Username node collects and injects the
userNameinto the shared node state. -
The Platform Password node collects and injects the
passwordinto the shared node state.
-
-
The Data Store Decision node uses the username and password to determine whether authentication is successful.
-
The Increment Login Count node updates the login count on successful authentication.
-
The Inner Tree Evaluator node invokes a nested journey for progressive profiling.
Profile Completeness Decision node
Use progressive profile flows to check how much of a user’s profile has been completed,
where the completeness of a profile is expressed as a percentage of user-viewable,
and user-editable fields that are not null.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Profile Completeness Threshold |
Percentage of user-viewable and user-editable fields in a profile that must be filled for the node to pass. Express this as a number between 0 and 100. |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. |
Query Filter Decision node
The Query Filter Decision node checks if the contents of a user’s profile match the specified query filter.
Use this node to check whether an attribute of the user profile matches a specific pattern. For instance, use this in progressive profile flows to check if marketing preferences are set on a user’s profile.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads the Identity Attribute from the shared node state.
If it can’t read the Identity Attribute, it reads the userName.
It uses the value to look up the identity object.
Configuration
| Property | Usage |
|---|---|
Query Filter |
A query filter used to check the contents of an object. For details on constructing effective query filters, refer to Construct queries. Default: none |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Example
Other journeys invoke the following progressive profile journey to capture missing profile attributes:
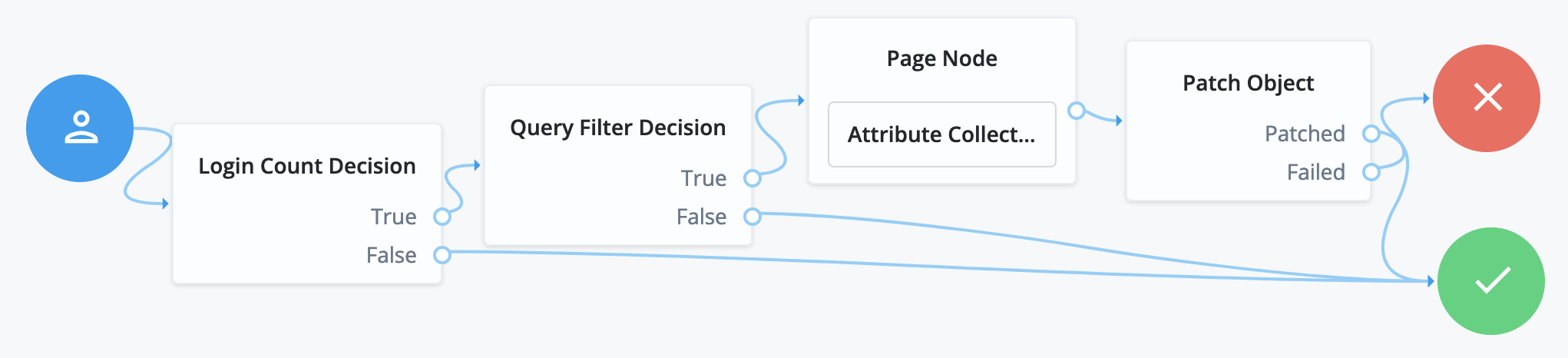
-
The Login Count Decision node triggers the rest of the journey depending on the login count and its settings.
-
The Query Filter Decision node determines whether managed object profile fields are missing.
-
The Attribute Collector node in the Page node requests additional input for the profile.
-
The Patch Object node stores the additional input in the managed object profile.
Required Attributes Present node
Checks the specified identity resource in the underlying identity service, and determines if all attributes required to create the specified object exist within the shared node state.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage | ||
|---|---|---|---|
Identity Resource |
The type of managed identity resource object this node creates. It must match the identity resource type for the current flow.
|
Select Identity Provider node
Presents the user with a list of configured, enabled, social identity providers to use for authentication.
Use this node with the Social Provider Handler node to use the Social Identity Provider Service.
The node has two possible outputs: social authentication and local authentication. Local authentication can be turned off by disabling Include local authentication.
This node returns the SelectIdPCallback when more than one social identity provider is enabled, or a single provider is enabled as well as the Local Authentication option, It then requires a choice from the user. If no choice from the user is required, authentication proceeds to the next node in the flow.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
Social Authentication -
Local Authentication
To turn off local authentication, disable Include local authentication.
Properties
| Property | Usage | ||
|---|---|---|---|
Include local authentication |
Whether local authentication is included as a method for authenticating. |
||
Offer only existing providers |
|||
Password attribute |
|||
Identity Attribute |
|||
Filter Enabled Providers |
By default, the node displays all identity providers marked as Enabled in the Social Identity Provider Service as a selectable option. Specify the name of one of more providers to filter the list.
If this field is not empty, providers must be in the list and must be enabled in the Social Identity Provider service to appear. If left blank, the node displays all enabled providers. |
Terms and Conditions Decision node
Verifies the user has accepted the active set of terms and conditions.
You set up terms and conditions in the Ping Identity Platform admin UI. Learn more in Terms and conditions.
Use this node to verify the user has accepted terms and conditions before proceeding, for example, during login or progressive profile data collection.
You can use this node with the Accept Terms and Conditions node.
Time Since Decision node
Checks if a specified amount of time has passed since the user was registered.
For example, to prompt users to review your terms and conditions after the account is a week old,
set the Elapsed Time property to 1 week.
After that time has elapsed, the next time the user logs in, they are prompted to review your terms and conditions.
Use this node for progressive profile completion.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Elapsed Time |
The amount of time since the user was created, in minutes, that needs to elapse before this node is triggered. This property also supports specifying basic time units.
For example, when setting the property to |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. |
Utility nodes
Agent Data Store Decision node
The Agent Data Store Decision node authenticates the agent using the data store for agent profiles and sets its authentication identifier if successful.
|
This node only authenticates agents, such as PingGateway and PingOne Advanced Identity Cloud Java and web agents. Use the Data Store Decision node for other identities. |
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the username and password properties in the incoming node state.
Obtain the agent credentials from the user or with a Zero Page Login Collector node.
Outcomes
True-
The credentials match those found in the data store for agent profiles.
False-
The credentials do not match those found in the data store for agent profiles.
Errors
This node can log the following warnings:
Exception in data store decision node-
The node couldn’t connect to the data store, or another error occurred.
invalid password error-
The password doesn’t match.
invalid username error-
The username doesn’t match any profiles found in the data store.
Example
The following example uses this node to authenticate an agent with the credentials provided:
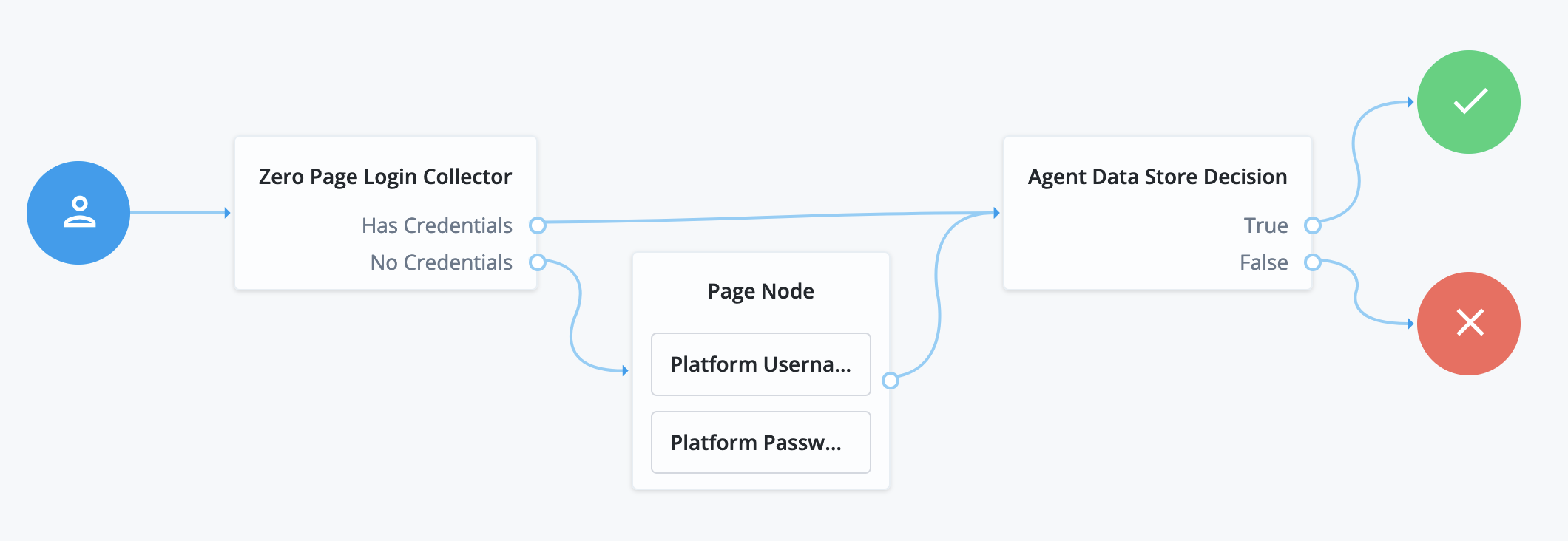
-
The Zero Page Login Collector node collects the username and password from HTTP headers if provided.
-
The Page node collects the username and password interactively from the user.
-
The Agent Data Store Decision node verifies the agent credentials match those in the data store.
Anonymous Session Upgrade node
Upgrades an anonymous session to a non-anonymous session.
Use this as the first node in the flow.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Example
After using the Anonymous User Mapping node to access AM as an anonymous user, this node lets users upgrade their session to a non-anonymous one:
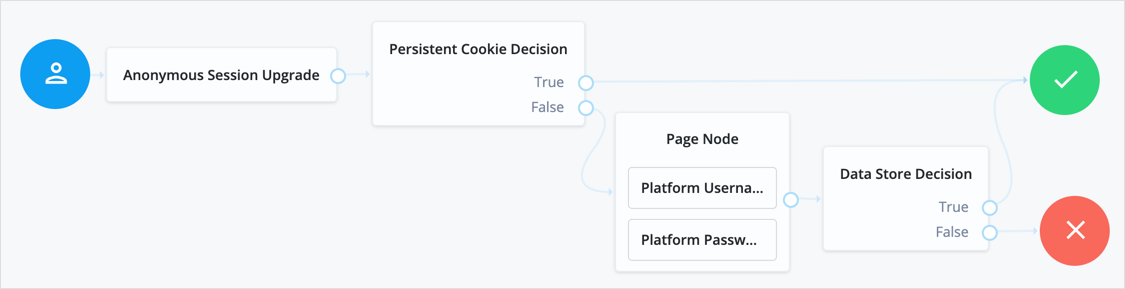
Anonymous User Mapping node
Lets users log in to an application or website without providing credentials,
by assuming the identity of a specified existing user account.
The default user for this purpose is named anonymous.
Take care to limit access for such users. For example, grant anonymous users access to public downloads on your site.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Choice Collector node
Define two or more options to present to the user when authenticating.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage | ||
|---|---|---|---|
Choices |
Enter two or more choice strings to display to the user. To remove a choice, select its Delete icon . To delete all choices, select the Clear all button in the Choices field. |
||
Default Choice (required) |
Enter the value of the choice to be selected by default.
|
||
Prompt (required) |
Enter the prompt string to display to the user when presenting the choices. |
||
Field Display Type |
Specifies the format of the options presented to the user.
Possible values are:
|
Configuration Provider node
The Configuration Provider node is a scripted node that dynamically imitates another node and replaces it in the journey.
The script builds a map of configuration properties matching settings for the imitated node. The Configuration Provider node uses the settings to imitate the other node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
The specific shared state inputs depend on your script and the configuration it builds. The shared state data must include all required Script Inputs properties.
In other words, shared state data must include whatever the Script requires to prepare configuration data for the imitated node.
Dependencies
To use this node, you need to prepare a script that provides values for the settings of the imitated node.
Choose the type of node to imitate
The imitated node must have a defined set of outcomes.
This can be a variable set of outcomes from a predefined list, such as the Polling Wait node, or a fixed set of outcomes, such as the Message node.
You can’t use a node type whose outcomes are defined entirely by configuration, such as the Scripted Decision node.
Get a template script
Use the REST API to get the required configuration properties for the imitated node.
-
Call the following API endpoint with the
configProviderScriptaction to get a template script for the type of node you want to imitate:/realm-config/authentication/authenticationtrees/nodes/node-type?_action=configProviderScriptbashFor example, the following request returns a base64-encoded template script for a Polling Wait node:
$ curl \ --request POST \ --header "Authorization: Bearer access-token"\ --header "Content-Type: application/json" \ "https://tenant-env-fqdn/am/json/realms/root/realms/alpha/realm-config/authentication/authenticationtrees/nodes/PollingWaitNode?_action=configProviderScript" { "script":"LyoqCiAqIFRoZSBmb2xsb3dpbmcgc2.." }bash -
Decode the
scriptvalue, for example, by using an online base64 decoder.The decoded output shows the required properties. For example, a request for the Polling Wait node generates the following template script:
config = { "secondsToWait" : 8, "spamDetectionEnabled" : false, "spamDetectionTolerance" : 3, "waitingMessage" : { }, "exitable" : false, "exitMessage" : { } };json
Configure the script
Use the imitated node’s properties to create a Configuration Provider Node or Configuration Provider Node (Next-Gen) type script.
Learn more in Auth scripting.
-
Base your script on the
config-provider-node.jssample.Your script must have a
configobject. This object must define the configuration properties that match the settings of the imitated node.For example, a script for the Email Suspend node has the following structure:
config = { "emailTemplateName" : "registration", "emailAttribute" : "mail", "emailSuspendMessage" : { "en" : "An email has been sent to the address you entered. Click the link in that email to proceed." }, "objectLookup" : false, "identityAttribute" : "userName" };jsonA Configuration Provider node script can use either the next-generation or legacy script engine. It has access to all the common bindings available for its script type. You can use these to help you set the values of the configuration properties.
Refer to the example for a script that uses shared state data to set the node configuration.
-
Save your script, and select it from the list when you configure the node’s Script property.
Configuration
| Property | Usage |
|---|---|
Script |
Select the script you created for this node. The list displays legacy and next-generation Configuration Provider scripts. Click to open a script editor and create a new script. |
Node Type |
Select the type of node to imitate. The list is restricted to node types with outcomes that are fixed or variable based on predefined values. |
Script Inputs |
Optionally, limit the shared state data properties in the shared state input to the selected Script. Default: |
Outcomes
The Configuration Provider node inherits the outcomes of its configured Node Type. Connect these as you would the outcomes of the imitated node.
Nodes with a variable set of outcomes inherit all the possible outcomes even if runtime configuration makes them unreachable. Connect these outcomes to the Failure node.
This node also has a Configuration failure outcome. The Configuration failure outcome arises when:
-
The Configuration Provider node failed to build the configuration map.
-
The configuration map is missing required values.
-
The configuration map is invalid.
Errors
In addition to the messages from the imitated node, this node can log the following:
- Warnings
-
-
Failed to collect inputs of contained node: node-typeA required input property was missing.
-
Failed to get outcome provider for node type.The Node Type outcomes were missing.
-
- Errors
-
-
Failed to configure node: node-typeThis corresponds to the Configuration failure outcome.
-
To troubleshoot HTTP errors this node causes, refer to the Errors section of the imitated node.
Examples
Example 1: Imitate the Message node
In the following example, the Configuration Provider node imitates a Message node.
The Configuration Provider settings are the following:
- Script
-
A script to configure a Message node dynamically.
The script assigns values to the required properties, accessing the
usernamefrom shared state data to set the message:config = { "message": {"en-GB": `Hi ${nodeState.get("username")}. Please confirm you are over 18.`}, "messageYes": {"en-GB": "Confirm"}, "messageNo": {"en-GB": "Deny"}, "stateField" : null }json - Node Type
-
Message Node - Script Inputs
-
usernameThe default,
*, also works becauseusernameis one of the available shared state properties.
The Configuration Provider node is part of a journey where the user enters their username and password before getting the message screen, so their username is in the shared state data. Notice the outcomes of the node include those of the Message node (True, False):
![Journey with a [.label]#Configuration Provider# node](_images/config-provider-journey.png)
When the journey reaches the Configuration Provider node,
the script for the node retrieves the username and dynamically configures the node.
The Configuration Provider node, imitating a Message node, prompts the user with the message:
![A [.label]#Configuration Provider# node imitating a [.label]#Message# node](_images/config-provider-example.png)
-
When the user clicks Confirm, the journey continues to the Increment Login Count node.
-
When the user clicks Deny, the journey continues to the Failure node.
-
If the configuration process fails, the node triggers the Configuration failure outcome and the journey continues to the Failure node. In this case, you can find the reason for the failure in the logs.
Example 2: Imitate the Set Success Details node
This example uses the Configuration Provider node to imitate a Set Success Details node and add the following additional details to the JSON response:
-
A dynamic
apiResponsefield, which returns the response from themonitoring/healthendpoint. -
A static
authMethod:passwordfield. -
A
universalIdsession property, which returns the corresponding value from the session when the user authenticates.
![Journey with a [.label]#Configuration Provider# node imitating the [.label]#Set Success Details# node](_images/set-success-details-journey-dynamic.png)
-
The Page node containing the Platform Username node and Platform Password node prompts for credentials.
-
The Data Store Decision node validates the username-password credentials.
-
The Increment Login Count node updates the number of successful authentications in the user profile.
-
The Configuration Provider node, imitating a Set Success Details node, adds the additional configured details to the JSON response upon successful authentication. This example uses the following configuration:
- Script
-
The following next-generation script calls the
monitoring/healthendpoint and dynamically configures the node by setting the required properties. It includes the API response in the JSON response if authentication is successful along with the static field and session property:var requestAPI = "https://example.com/monitoring/health"; var response = httpClient.send(requestAPI).get(); var apiResponse = response.json(); config = { "successDetails": { "authMethod": "password", "apiResponse": apiResponse }, "sessionProperties": { "universalId": "sun.am.UniversalIdentifier" } };javascript - Node Type
-
Set Success Details - Script Inputs
-
*
When the user authenticates successfully using this journey, the JSON response includes the additional details you configured. For example:
{
"tokenId": "AQIC5wM…TU3OQ*",
"successUrl": "/enduser/?realm=/alpha",
"realm": "/alpha",
"universalId": "id=bjensen,ou=user,o=alpha,ou=services,ou=am-config",
"apiResponse": {
"status": "OK"
},
"authMethod": "password"
}Example 3: Imitate the Email Suspend node
This example extends the default resetPassword journey to include the user’s email address in the email
suspend message. This is achieved by using the Configuration Provider node to imitate the
Email Suspend node.
![Journey with a [.label]#Configuration Provider# node imitating the [.label]#Email Suspend# node](_images/email-suspend-journey-dynamic.png)
The Configuration Provider node in this example uses the following configuration:
- Script
-
The following next-generation script dynamically configures the node by setting the required properties. It retrieves the user’s email address from the shared state and includes it in the email suspend message:
var attributes = nodeState.getObject("objectAttributes"); config = { "emailTemplateName" : "resetPassword", "emailAttribute" : "mail", "emailSuspendMessage" : { "en" : `An email has been sent to ${attributes.get("mail")}. Click the link in that email to reset your password.` }, "objectLookup" : true, "identityAttribute" : "mail" };javascript - Node Type
-
Email Suspend Node - Script Inputs
-
*
When the journey is suspended, the updated suspend message is shown. For example:
Email Suspend node
The Email Suspend node generates and sends an email, such as an address verification email based on an email template. This node relies on an email provider to send the email.
This node generates a unique link and passes it as the resumeURI property for the template.
How is resumeURI derived?
The External Login Page URL is used as the base of the resumeURI if it’s been configured.
Otherwise, the Base URL Source service is used to construct the base of the resumeURI.
Learn more in Core authentication attributes > General and Base URL Source.
The journey is suspended until the end user clicks the link in the email to resume it. Make sure the journey session is long enough for the end user to complete the journey so that it doesn’t time out. Learn more in Configure suspended journeys.
If you don’t need to suspend a journey and wait for a reply, use the Email Template node instead.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
The Email Suspend node either uses the identity profile in the shared state data or looks up the user profile. In either case, the node uses any applicable profile properties to populate the email template, omitting missing values from the populated template.
If Object Lookup is not enabled for the node (default), the shared state data must hold the Email Attribute with the recipient’s email address and any properties the email template uses.
If Object Lookup is enabled for the node, the shared state data must hold the profile value to match the configured Identity Attribute. The Email Suspend node uses the Identity Attribute to look up the profile, and its Email Attribute to get the recipient’s email address from the profile.
Dependencies
Before you use the Email Suspend node:
-
(Optional) Configure an email provider.
By default, tenants use the built-in SMTP server.
-
The template expressions refer to user profile properties.
Record the email template name for use when configuring the Email Suspend node.
You can find the email template name in the required format in the URL when you’re configuring the template.
For example, the Forgotten Username email template’s name is
forgottenUsername:https://<tenant-env-fqdn>/?realm=alpha#/email/templates/edit/forgottenUsername
Configuration
| Property | Usage |
|---|---|
Email Template Name |
The name of the email template prepared as a dependency. Default: |
Email Attribute |
The shared state data property or profile attribute for the recipient’s email address. Default: |
Email Suspend Message |
The localized message to display when the node suspends the journey. According to OWASP authentication recommendations, the message should be the same regardless of the validity of the recipient’s email address. You can use plain text or HTML code in this message. Default: |
Object Lookup |
Whether to look up the managed identity profile. Default: disabled |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. The node uses this when Object Lookup is enabled. Default: |
PingAM Suspend Duration |
(Optional) The length of time a journey session can be suspended in minutes. The time allowed for suspending the journey must be the same as or less than the maximum duration of the journey session. If set, this overrides the suspend duration set in the core authentication settings. Learn more in Suspend duration. Values from |
Outcomes
The Email Suspend node has a single outcome path.
Evaluation continues when the end user clicks the link in the email to resume the flow.
Examples
The following default journeys use the Email Suspend node:
-
ForgottenUsername -
ResetPassword -
UpdatePassword
Example 1: Forgotten username
In the default journey for recovering a forgotten username, the end user enters their email address to recover their username.
Before you start
-
Configure the email service.
Use the built-in SMTP server.
-
Optionally use the email template editor to modify the
forgottenUsernametemplate.
The journey
![Forgotten username journey with an [.label]#Email Suspend# node](_images/forgotten-username-journey.png)
-
The Page node with an Attribute Collector node prompts for the end user’s email address.
-
The Identify Existing User node attempts to look up the username by matching the email address to the email address in an identity profile.
The lookup fails if more than one user profile uses the same email address.
-
The Email Suspend node reads the user profile, generates a unique
resumeURIlink to resume the journey, and populates theforgottenUsernameemail template. On success, the node makes a request to the email service to send the email. In any case, it displays the suspend message:![Message from an [.label]#Email Suspend# node](_images/email-suspend-message.png)
The node’s settings are:
Email Template Name
forgottenUsernameEmail Attribute
mail(default)Email Suspend Message
An email has been sent to the address you entered. Click the link in that email to proceed.(default)Object Lookup
Enabled
Identity Attribute
mail -
When the end user clicks the link to resume the journey, the Inner Tree Evaluator node starts the
Loginjourney.
Example 2: Registration
For an example registration journey showing how to use the Email Suspend node and the Email Template node, read the Email Template node examples.
Example 3: Add dynamic user data to the email suspend message
This example uses the Configuration Provider node to imitate the Email Suspend node. Using the Configuration Provider node lets you include dynamic user data, such as their email address, in the email suspend message.
![Journey with a [.label]#Configuration Provider# node imitating the [.label]#Email Suspend# node](_images/email-suspend-journey-dynamic.png)
Find more information in Example 3: Imitate the Email Suspend node.
Email Template node
The Email Template node generates and sends an email, such as a welcome email based on an email template. This node relies on an email provider to send the email.
This node doesn’t wait for a reply. If authentication should pause and wait for a reply to the email, use the Email Suspend node instead.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
The Email Template node uses the identity in the shared state data to get the profile,
meaning the journey must have successfully authenticated or at least identified the recipient.
When the journey reaches this node, the shared state must hold the profile value to match
the configured Identity Attribute.
The value can be in the username property or in a property having the same name as the Identity Attribute.
The Email Template node uses its Identity Attribute to look up the profile, and its Email Attribute to get the recipient’s email address from the profile. In other words, the node finds the recipient’s address and other properties in the profile, not the shared state data.
For example, if the node uses default configuration settings and Babs Jensen authenticated to the journey,
the shared state includes "username": "bjensen".
The node looks for a profile with "userName": "bjensen".
It gets the recipient address from the profile’s mail attribute, such as "mail": "bjensen@example.com".
The node uses any applicable profile attributes to populate the email template,
omitting missing values from the populated template.
Dependencies
Before you use the Email Template node:
-
(Optional) Configure an email provider.
By default, tenants use the built-in SMTP server.
-
The template expressions refer to user profile properties.
Record the email template name for use when configuring the Email Template node.
You can find the email template name in the required format in the URL when you’re configuring the template.
For example, the Forgotten Username email template’s name is
forgottenUsername:https://<tenant-env-fqdn>/?realm=alpha#/email/templates/edit/forgottenUsername
Configuration
| Property | Usage |
|---|---|
Email Template Name |
The name of the email template prepared as a dependency. Default: |
Email Attribute |
The profile attribute for the recipient’s email address. Default: |
Identity Attribute |
The attribute used to identify the managed object in the underlying identity service. Default: |
Outputs
This node doesn’t add to the shared state data.
If the outcome is Email Sent, this node has sent the templated message to the recipient through the email service.
Outcomes
Email Sent-
The node completed a request to send the message to the recipient.
If the message doesn’t reach its destination, the problem is with the delivery, not with the node.
Email Not Sent-
The node failed to complete a request to send the message.
This outcome arises, for example, when one of the following happens:
-
The node can’t get the user profile.
-
The template doesn’t match the user profile.
-
The specified Email Attribute doesn’t contain an address.
-
According to OWASP authentication recommendations, any messages displayed in the journey should be the same in both cases.
Examples
Use the Email Template node to send an email message when the journey doesn’t depend on a reply. For example, send a welcome message when a user completes registration.
This example augments the default Registration journey and sends a welcome email.
Before setting up the journey:
-
Configure the email service.
Use the built-in SMTP server.
-
Create an email template for the Email Template node.
Use the platform email template editor to duplicate the
Welcometemplate and customize your copy: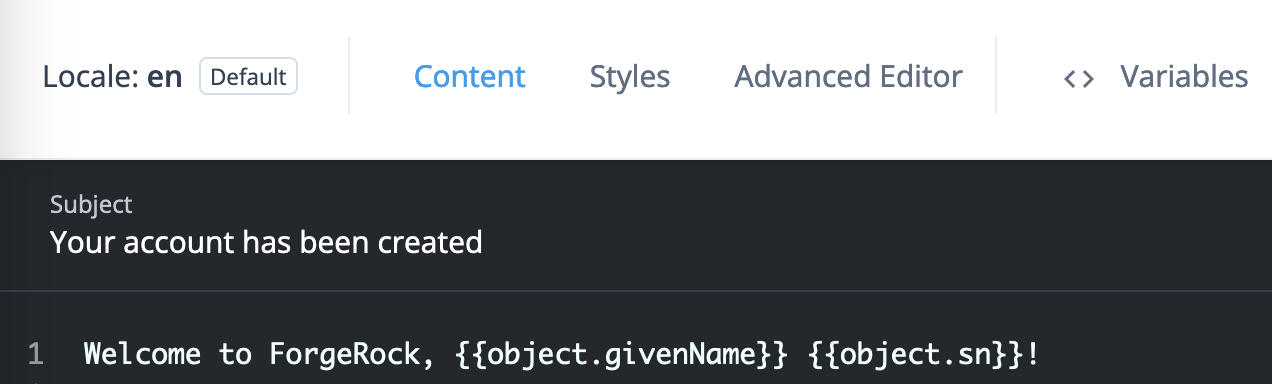
The journey is as follows:
![Registration journey with an [.label]#Email Template# node](_images/email-registration-journey.png)
-
The Page node prompts for the same information as the default Registration journey.
-
The Email Suspend node sends a message to the registered email address with a link for the user to click.
The journey proceeds when the user clicks the link, confirming their email address.
It has default settings and uses the default
Registrationemail template: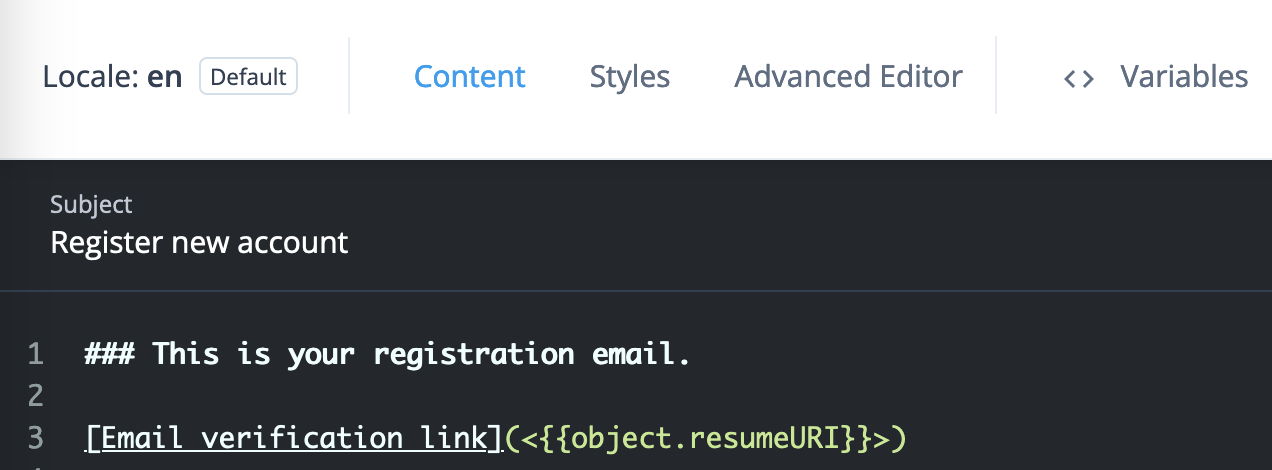
-
The Create Object node stores the newly registered user’s profile.
-
The Email Template node reads the user profile and populates the template from profile attribute values. It makes a request to the email service to send the message.
Its settings are:
Email Template Name
The name of your welcome email template
Email Attribute
mail(default)Identity Attribute
userName(default) -
The Increment Login Count node updates the count on successful authentication.
Use the journey to register an account for Babs Jensen with your email as the address. You receive two messages:
-
The
Register new accountmessage has a link to click to continue the journey, confirming you can access the registered email account. -
The
Your account has been createdwelcomes you on successful registration.
This demonstrates you have successfully used the Email Template node in a journey.
Failure URL node
Sets the redirect URL when authentication fails.
|
Specifying a failure URL overrides any |
For more information on how AM determines the redirection URL, and to configure the Validation Service to trust redirection URLs, refer to Success and failure redirection URLs.
|
The URL is also saved in the shared |
Get Session Data node
The Get Session Data node retrieves the value of a specified key from a user’s session data,
and stores it in the specified key of the shared state (in scripts, the nodeState object).
Use this node only during session upgrade—when the user has already successfully authenticated previously and is now upgrading their session for additional access. For more information on upgrading a session, refer to Session upgrade with MFA.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Dependencies
This node can complete its function only when the user has an existing session. Precede this node in the flow with a Scripted Decision node using a script to determine whether an existing session is present:
if (typeof existingSession !== 'undefined') {
outcome = "hasSession";
} else {
outcome = "noSession";
}Configuration
All the configuration properties are required:
| Property | Usage |
|---|---|
Session Data Key |
Specify the session data key whose value the node reads. Default: none |
Shared State Key |
Specify the name of the shared node state field to hold the session data. Default: none |
Outputs
This node writes the Session Data Key value in the Shared State Key field of the shared node state.
It also writes the field and its value to the objectAttributes object in the shared node state.
Outcomes
Single outcome path; on success, the Shared State Key in the shared node state holds the session data.
Errors
If it cannot read the Session Data Key value, this node logs
an Exception occurred trying to get data (<session-data-key>) from existing session error message.
Example
When the user has an active session, the following example gets the username from the session, collects the password, and confirms the username-password credentials:
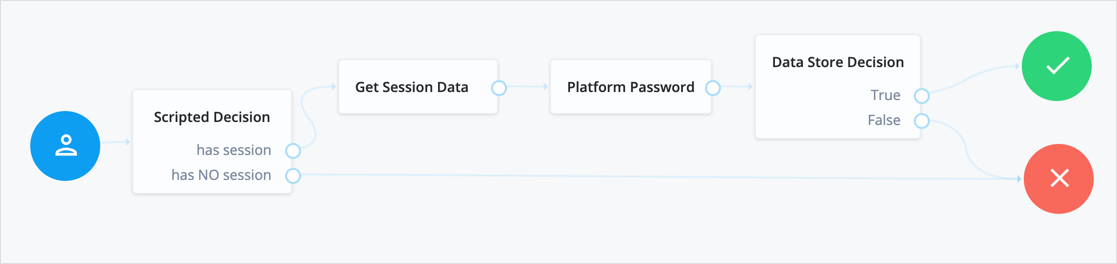
The following table includes example keys from an existing session with their corresponding sample values:
| Key | Sample value |
|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Inner Tree Evaluator node
The Inner Tree Evaluator node lets you nest authentication journeys as children within a parent. There is no limit to the depth of nesting.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
Any information collected or set by the parent journey, such as a username or the authentication level, is available in the child journeys.
For information about shared state data, refer to Access shared state data.
Configuration
| Property | Usage |
|---|---|
Tree Name |
Select or enter the name of the authentication journey to evaluate. You must set this value; there’s no default. |
Outputs
Shared node state data collected by child journeys is available to the parent when evaluation of the child is complete, but data stored in transient and secure state is not. For instance, if a child journey collects and stores the user’s password in transient state, it cannot be retrieved by a node in the parent journey when evaluation continues.
For information about shared state data, refer to Access shared state data.
Errors
If it cannot get the shared node state from the child,
this node logs an Exception when gathering inner tree inputs message.
If the Tree Name doesn’t match an existing journey,
this node throws an exception with a Configured tree does not exist: <tree-name> message.
Example
The following journey uses an Inner Tree Evaluator node for progressive profiling:
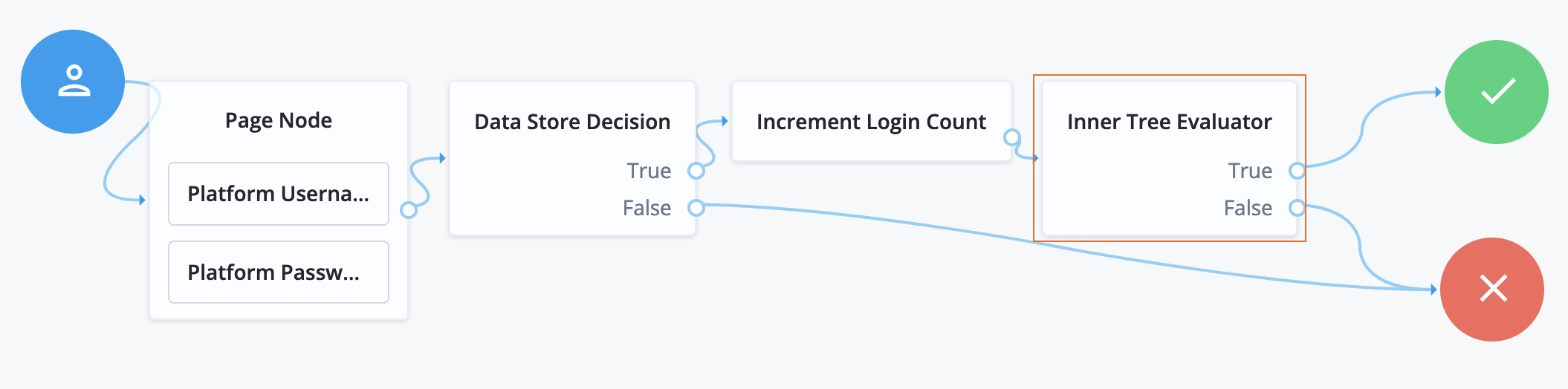
-
The Page node presents a page with input fields to prompt for the username and password.
-
The Platform Username node collects and injects the
userNameinto the shared node state. -
The Platform Password node collects and injects the
passwordinto the shared node state.
-
-
The Data Store Decision node uses the username and password to determine whether authentication is successful.
-
The Increment Login Count node updates the login count on successful authentication.
-
The Inner Tree Evaluator node (outlined) invokes a nested journey:
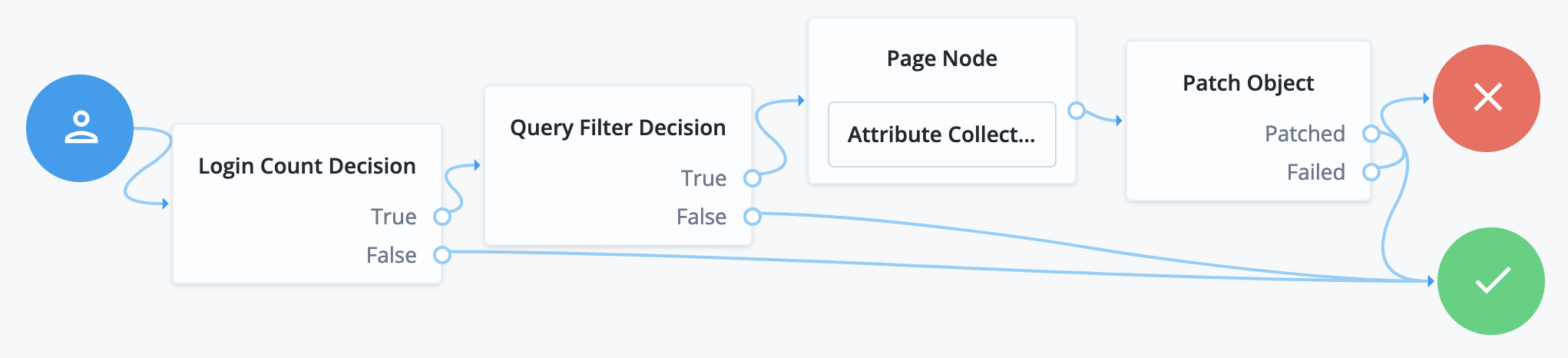
-
The Login Count Decision node triggers the rest of the journey depending on the login count and its settings.
-
The Query Filter Decision node determines whether managed object profile fields are still missing.
-
The Attribute Collector node in the Page node requests additional input for the profile.
-
The Patch Object node stores the additional input in the managed object profile.
Message node
The Message node presents a custom, localized message to the user with customizable, localized positive and negative answer buttons the user must click to proceed.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node reads preferred locales from the incoming request context.
It doesn’t read from the shared node state.
This node has no required predecessor nodes.
Configuration
| Property | Usage | ||
|---|---|---|---|
Message |
Add a custom, localized message per locale:
To edit an entry, click the Pencil icon (). To remove an entry, click the Delete icon (). |
||
Positive answer |
Add the text per locale for the positive answer button that triggers a True outcome:
To edit an entry, click the Pencil icon (). To remove an entry, click the Delete icon (). |
||
Negative answer |
Add the text per locale for the negative answer button that triggers a False outcome:
To edit an entry, click the Pencil icon (). To remove an entry, click the Delete icon (). |
||
Shared State Property Name |
The name of the node state property. If set, the node adds the property to shared node state, setting its value to the numeric value of the outcome:
For example, if you set this to |
||
Only Positive Answer |
When enabled, the node displays only the positive answer button.
|
||
Show buttons as links |
When enabled, the node shows the buttons as links instead.
|
1 Specify a
locale that Java supports, such as en-gb;
otherwise, the node throws a configuration exception with an Invalid locale provided message.
Outputs
When the Shared State Property Name setting has a value, the node adds the property to the shared node state. The property’s value is the numeric value of the outcome:
0-
The user clicked the positive answer button.
1-
The user clicked the negative answer button.
Outcomes
Returns a boolean outcome:
- True
-
The user clicked the positive answer button.
- False
-
The user clicked the negative answer button.
Errors
This node doesn’t cause authentication to fail unless you connect one of the outcomes to a Failure node.
If the message or answer button settings specify a locale Java doesn’t support,
the node throws a configuration exception with an Invalid locale provided message.
If this happens, fix the locale setting.
If this node encounters an internal configuration issue, it logs a warning message
Error attempting to retrieve the realm/global default locale.
If the warning persists, contact ${forgerock.name} Support.
Examples
Use a Message node to:
-
Communicate an important message for the user to acknowledge.
-
Ask a question with a yes/no answer.
The following journey uses the Join VIPs Message Node to prompt the user to join the VIP program:
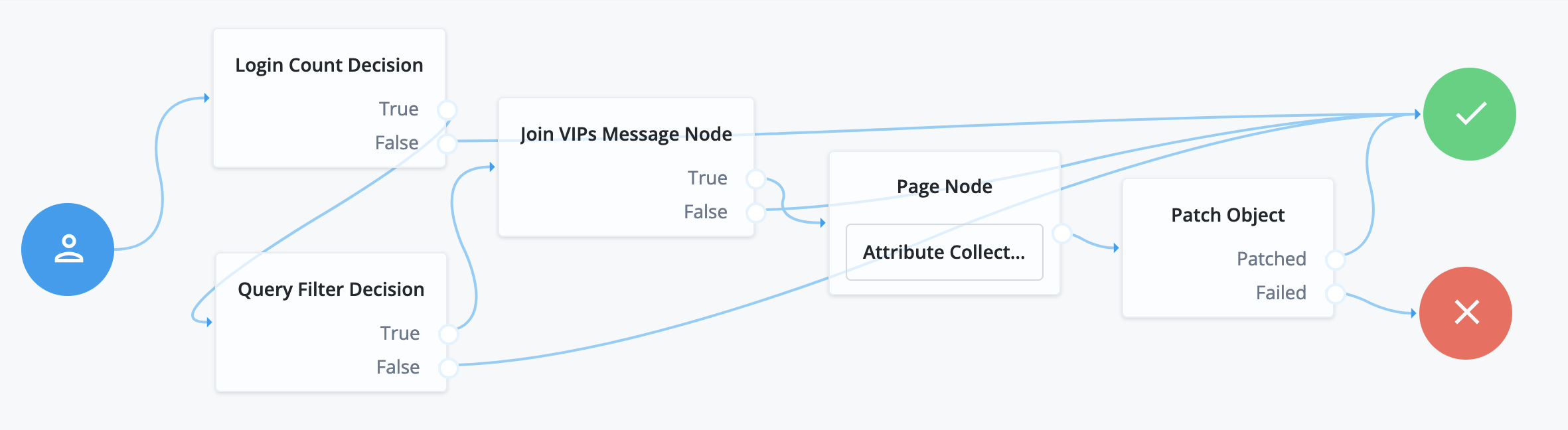
-
The Login Count Decision node triggers the Query Filter Decision node after every tenth authentication.
-
The Query Filter Decision node queries the user profile to determine whether they have signed up for the VIP program.
If the user hasn’t signed up yet, the True outcome triggers the
Join VIPs Message Node, which prompts the user to join the program: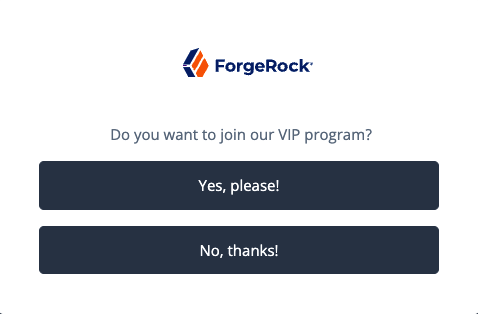
Node property settings:
- Message
-
en-gb;Do you want to join our VIP program? - Positive answer
-
en-gb;Yes, please! - Negative answer
-
en-gb;No, thanks!
-
If the user clicks Yes, please! the Page node with an embedded Attribute Collector node collects opt-in choices to store in user profile attributes.
-
The Patch Object node updates the user profile with the attributes collected.
Call the journey using an Inner Tree Evaluator node from another authentication journey directly after an Increment Login Count node note:
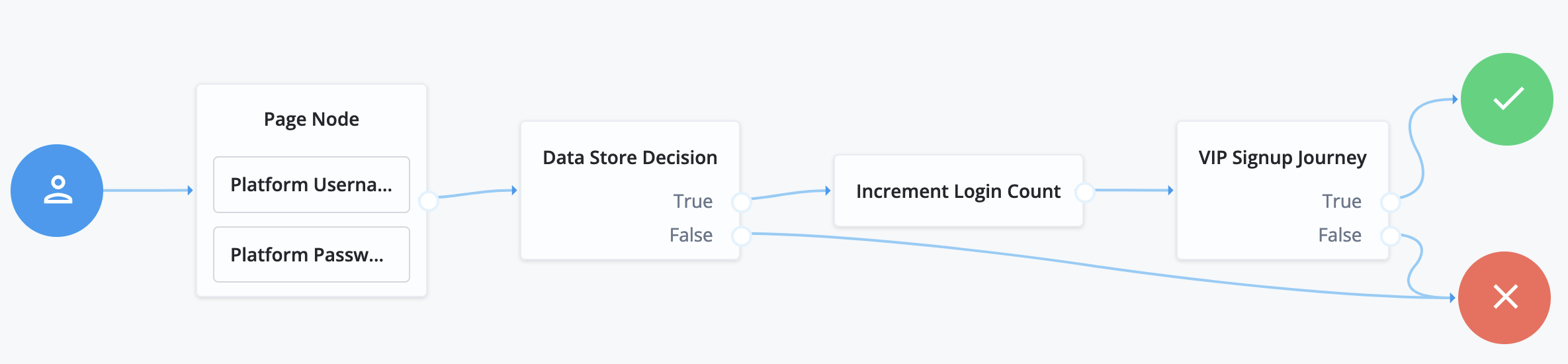
The VIP Signup Journey uses the login count from the Increment Login Count node
in the Login Count Decision node to decide whether to prompt the user to join the VIP program.
Meter node
Increments a specified metric key each time evaluation passes through the node.
Page node
The Page node lets you combine multiple nodes that request input onto a single page for display to the user.
Drag and drop nodes onto the Page node to combine them. Only add nodes that use callbacks to request input. Don’t add other nodes, such as the Data Store Decision node and the Push Sender node to this node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Configuration
| Property | Usage |
|---|---|
Page Header |
Optional. A localized title for the Page node and the nodes contained within it. Use this when components of an authentication journey need a title. For example, dividing a registration flow into labeled sections. |
Page Description |
Optional. A localized description for the Page node and the nodes contained within it. Use this when you need additional descriptive text in an authentication journey. You can use HTML code to format the description. |
Stage |
Optional. A stage name to pass to the client to aid in rendering. NOTE: You can’t configure a Stage for this node if you configure a Page Footer, Theme or Submit Button Text. These properties overwrite the value of the Stage property. |
Submit Button Text |
Optional. Use the Key and Value fields to set the text of the Submit button. |
Page Footer |
Optional. A localized footer for the page node and the nodes contained within it. Use this when you need additional descriptive text in an authentication journey. You can use HTML code to format the footer. |
Theme |
Optional. If using hosted pages, specify a theme to override this journey’s UI theme. |
|
This node’s optional properties are passed in the response, but a self-hosted or custom UI must support these properties to make them visible to the end user. |
Outcomes
The outcomes are determined by the last node in the Page node. Only the last node in the page can have more than one outcome path.
Errors
This node can log the following error messages:
| Message | Notes |
|---|---|
|
The <node-name> could not retrieve required properties from the shared node state |
|
The <node-name> could not retrieve required properties to include in the shared node state |
|
Failed to find the account profile with this |
|
Failed to update the account status; applies when locking and unlocking the account |
This node can throw exceptions with the following messages during operation:
| Message | Notes |
|---|---|
|
A Page node must contain at least one other node |
|
Failed to get to an outcome while processing the contained nodes |
|
Failed to access the properties of a contained node |
This node can throw exceptions with the following messages when saving the journey:
| Message | Notes |
|---|---|
|
A Page node can’t contain a <node-type> |
|
The contained nodes must have at least a single outcome path |
|
Consider rearranging the contained nodes |
|
Use the journey editor to fix the problem |
|
Use the journey editor to fix the problem |
|
Use the journey editor to fix the problem |
Example
The following example uses a Page node containing a Platform Username node, Platform Password node, and Choice Collector node:
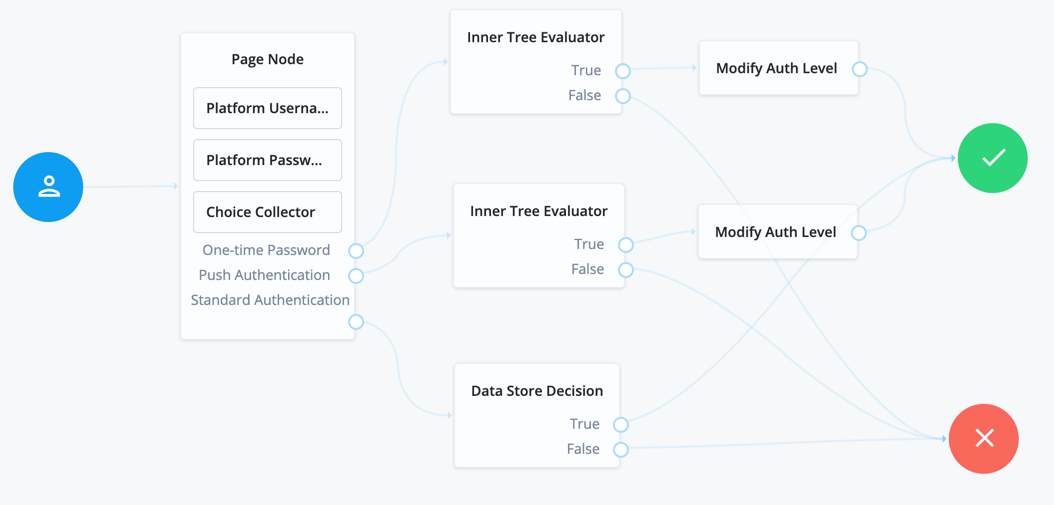
The flow prompts the user for all input on a single page:
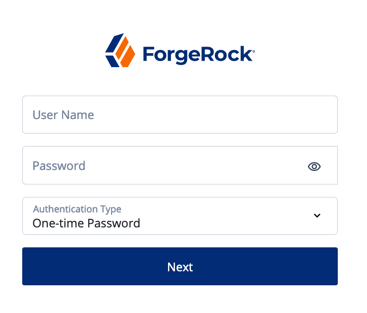
Polling Wait node
Pauses authentication progress for a specified number of seconds, for example, to wait for a response to a one-time passcode email or push notification.
Requests made during the wait period are sent a PollingWaitCallback callback and an authentication ID.
For example, the following callback indicates a wait time of 10 seconds:
{
"authId": "eyJ0eXAiOiJK...u4WvZmiI",
"callbacks": [
{
"type": "PollingWaitCallback",
"output": [
{
"name": "waitTime",
"value": "10000"
},
{
"name": "message",
"value": "Waiting for response..."
}
]
}
]
}The client must wait 10 seconds before returning the callback data, including the authId:
$ curl \
--request POST \
--header "Accept-API-Version: resource=2.0, protocol=1.0" \
--header "Content-Type: application/json" \
--data '{
"authId": "eyJ0eXAiOiJK…u4WvZmiI",
"callbacks": [
{
"type": "PollingWaitCallback",
"output": [
{
"name": "waitTime",
"value": "10000"
},
{
"name": "message",
"value": "Waiting for response…"
}
]
}
]
}' \
'https://am.example.com:8443/am/json/realms/root/realms/alpha/authenticate?authIndexType=service&authIndexValue=Example'The end user UI automatically waits for the required amount of time and resubmits the page to continue evaluation. The message displayed during the wait is configurable with the Waiting Message property.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Outcomes
-
Done -
Exited(configurable) -
Spam(configurable)
Evaluation continues along the Done outcome path when the next request is received after the wait time has passed.
Enabling Spam detection adds a Spam outcome path to the node.
Evaluation continues along the Spam outcome path
if more than the specified number of requests are received during the wait time.
Enabling the user to exit without waiting adds an Exited outcome path to the node.
Evaluation continues along the Exited outcome path
if the user clicks the button that appears when the option is enabled.
The message displayed on the exit button is configurable by using the Exit Message property.
Properties
| Property | Usage |
|---|---|
Seconds To Wait |
Specify the number of seconds to pause authentication. Default: |
Enable Spam Detection |
Specify whether to track the number of responses received during the wait time,
and continue evaluation along the Default: Disabled |
Spam Tolerance |
Specify the number of responses to allow during the wait time
before continuing evaluation along the Default: |
Waiting Message |
Specifies the optional message to display to the user. Provide the message in multiple languages by specifying the locale in the KEY field, for example, Messages provided in the node override the defaults provided by AM. |
Exitable |
Whether the user can exit the node during the wait period. Enabling this option adds a button with a configurable message to the page.
Clicking the button causes evaluation to continue along the Default: Disabled |
Exit Message |
Specifies the optional message to display to the user on the button used to exit the node
before the wait period has elapsed.
For example, Provide the message in multiple languages by specifying the locale in the KEY field, for example, Messages provided in the node override the defaults provided by AM. |
Register Logout Webhook node
Registers the specified webhook to trigger when a user’s session ends. The webhook triggers when a user explicitly logs out or the maximum idle time or expiry time of the session is reached.
The webhook is only registered if evaluation passes through this node. You can register multiple webhooks during the authentication process, but they must be unique.
For more information on webhooks, refer to Configure authentication webhooks.
Remove Session Properties node
Removes properties from the session. The session properties may have been set by a Set Session Properties node elsewhere in the flow.
If a specified key is not found in the list of session properties it is added to the session upon successful authentication, no error is thrown, and evaluation continues along the single outcome path.
If a specified key is found,
the evaluation continues along the single outcome path after setting the value of the property to null.
Retry Limit Decision node
The Retry Limit Decision node tracks failed authentications. If the number of failed authentications is
below a specified Retry Limit, the user can attempt authentication again.
Otherwise, the node continues evaluation along the Reject outcome path.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
This node requires the realm and username properties in the incoming node state.
Implement a Platform Username node before this node in the journey.
Configuration
| Property | Usage |
|---|---|
Retry limit |
Specify the number of retries to allow. Default: |
Save Retry Limit to User |
Specify whether the number of failed login attempts persists across multiple journeys until authentication is successful. Possible values are:
For security reasons, you should enable this setting. Default: Enabled. |
Outputs
If Save Retry Limit to User is enabled, the node increments the retry count and saves the number of failed
attempts to the retryLimitNodeCount attribute in the user’s profile.
If the user can’t be identified during the journey, the journey ends with an error.
If Save Retry Limit to User is disabled, the node increments the retry count and saves the number of failed
attempts to a shared state property named nodeId.retryCount. The count is lost if the journey is restarted.
Outcomes
Retry-
The user hasn’t exceeded the number of allowed retries and can attempt authentication again.
Reject-
The user has exceeded the number of allowed retries.
Errors
This node can log the following:
- Warnings
-
-
Error clearing attributeThe node can’t reset the
retryLimitNodeCountuser attribute after the user has successfully authenticated.
-
- Errors
-
-
Error getting current retry countThe node can’t retrieve the current retry count.
-
Failed to save retryLimitNodeCount to user: Identity Repo has not been upgraded.The node can’t save retry count details to the
retryLimitNodeCountuser attribute during the authentication flow. -
Error setting retry count on user attributeThe node can’t increment the retry count on the
retryLimitNodeCountuser attribute during the authentication flow.
-
These warnings and errors typically occur if the identity store is unreachable or the user no longer exists.
Examples
This example uses the Retry Limit Decision node to allow a user three attempts to authenticate. Otherwise, their account is locked.
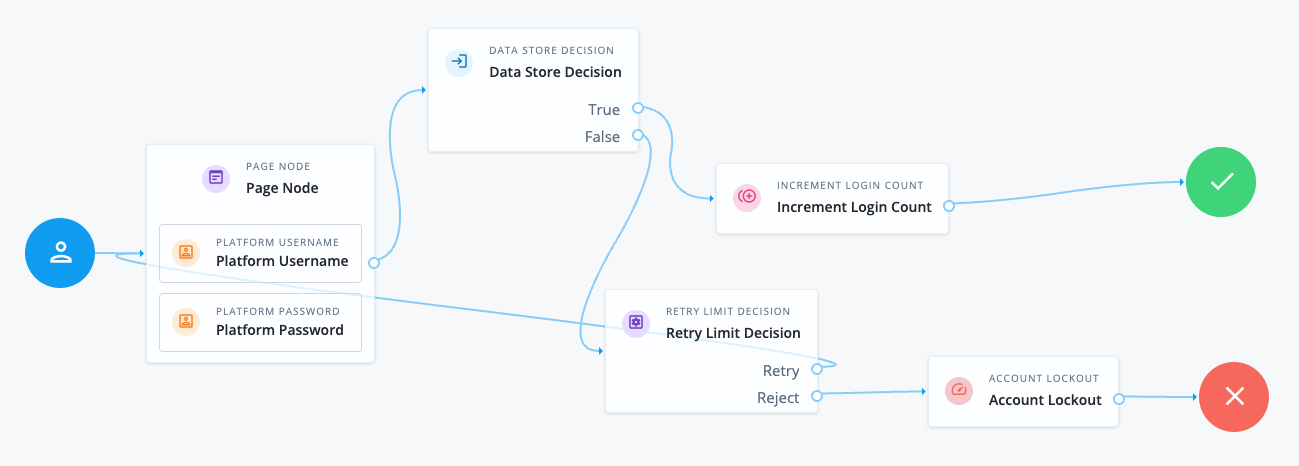
-
The Page node containing the Platform Username node and Platform Password node prompts for credentials.
-
The Data Store Decision node validates the username-password credentials.
-
The Increment Login Count node updates the number of successful authentications in the user profile.
-
The Retry Limit Decision node is configured to allow three login attempts and either retries the login attempt or rejects it depending on the number of failed attempts.
-
The Account Lockout node locks the user’s account on their fourth failed attempt.
Scripted Decision node
The Scripted Decision node lets you run a server-side script in an authentication journey. It exists to let you connect the script to other nodes with the journey editor.
The script makes a decision to set the outcome for the node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
Scripted Decision node inputs depend entirely on the node’s server-side script.
The script has access to the authentication context including:
-
Headers from the request
-
Query string parameters from the request
-
Secrets configured for the realm
-
Shared state data
-
User profile data
The script can use callbacks to prompt the user for information.
For details about the inputs available to the script, refer to Scripted decision node API.
You can restrict available inputs using the Script Inputs field when configuring the node.
Dependencies
A Scripted Decision node depends on a Journey Decision Node script you create before you configure the node.
Configuration
| Property | Usage | ||
|---|---|---|---|
Script |
Select the script to run from the drop-down list. |
||
Outcomes |
Enter one string for each The node shows only the outcomes you configure.
If you omit an When the script sets an |
||
Script Inputs |
Optionally, list the shared state data properties required by the script. If you change the setting, you must declare each property or Default:
|
||
Script Outputs |
Optionally, list the shared state data properties the node expects the script to set. If you change the setting, you must declare each property or Default: |
Outputs
Scripted Decision node outputs, such as updates to shared state data, depend entirely on the node’s server-side script.
You can restrict available outputs using the Script Outputs field when configuring the node.
Outcomes
The script defines the outcomes by setting its outcome variable to an outcome string before returning.
You include all possible outcome strings from the script in the Outcome field when configuring the node.
The authentication journey continues along the outcome path from the script.
Errors
The server-side script can log messages.
The node logs the following warning messages:
Warnings:
-
Found an action result from scripted node, but it was not an Action object: An action in a legacy script didn’t return an object with typeAction. -
Found an action result from scripted node, but it was not an ActionWrapper object: An action in a next generation script didn’t return an object with typeActionWrapper. -
invalid script outcome <outcome>: The <outcome> is missing in the Outcome field of the node configuration. -
invalid script outcome <action-outcome> in action: The <action-outcome> is missing in the Outcome field of the node configuration. -
script outcome error: The script set an outcome not found in the Outcome field of the node configuration.
Examples
You use a Scripted Decision node when no other available node does what you need.
In this example, the node depends on the following JavaScript Journey Decision Node script. The script gets the user’s names from their profile and stores a message in a shared state property:
-
Next-generation
-
Legacy
// Get the username from shared state data:
var username = nodeState.get('username')
// Get the given name(s) and surname(s) from the user profile:
var profile = idRepository.getIdentity(username)
var givenname = profile.getAttributeValues('givenName')
var surname = profile.getAttributeValues('sn')
if (!(givenname && surname)) {
var error = `Failed to get names for ${username}: ${givenname} ${surname}`
action.goTo('Failure').withErrorMessage(error);
} else {
// Record who authenticated in the shared state data:
var firstGivenName = givenname[0]
var firstSurname = surname[0]
var now = new Date().toLocaleString()
var message = `${firstGivenName} ${firstSurname} logged in at ${now}.`
nodeState.putShared('message', message)
action.goTo('Success');
}var goTo = org.forgerock.openam.auth.node.api.Action.goTo
// Get the username from shared state data:
var username = nodeState.get('username').asString()
// Get the given name(s) and surname(s) from the user profile:
var profile = idRepository.getIdentity(username)
var givenname = profile.getAttributeValues('givenName')
var surname = profile.getAttributeValues('sn')
if (!(givenname && surname)) {
var error = `Failed to get names for ${username}: ${givenname} ${surname}`
action = goTo('Failure').withErrorMessage(error).build()
} else {
// Record who authenticated in the shared state data:
var firstGivenName = givenname[0]
var firstSurname = surname[0]
var now = new Date().toLocaleString()
var message = `${firstGivenName} ${firstSurname} logged in at ${now}.`
nodeState.putShared('message', message)
action = goTo('Success').build()
}Notice the script sets the outcomes using the Action.goTo(outcome) function.
The journey is as follows:
![Journey with a [.label]#Scripted Decision# node](_images/scripted-decision-example.png)
-
The Page node prompts the user for their username and password.
-
The Identity Store Decision node checks the username and password with those in the identity store.
The node configuration enables the optional Username as Universal Identifier setting. As a result, the
nodeState.get('username').asString()function in the script returns the user’s_id. TheusernameinidRepository.getIdentity(username)must be the_id, not theuserName, to get the attribute from the user’s profile. -
The Scripted Decision node runs the script and has the following settings:
Script
The name of the script
Outcomes
Success,FailureScript Inputs
usernameScript Outputs
*Notice the Outcomes setting lists all outcome strings from the script.
-
The Increment Login Count node updates the count on successful authentication.
-
The Inner Tree Evaluator node refers to another journey to perform more steps.
This node is optional.
If you activate debug mode for the journey and select Enable Debug Popup, you find the message in the debug popup window when authenticating:
{
"universalId": "id=<_id>,ou=user,o=alpha,ou=services,ou=am-config",
"transactionId": "<transaction-id>",
"password": "<password>",
"pageNodeCallbacks": {
"0": 0,
"1": 1
},
"realm": "/alpha",
"message": "Babs Jensen logged in at August 16, 2023 9:55:33 AM UTC.",
"authLevel": 0,
"objectAttributes": {
"password": "<password>"
},
"username": "id=<_id>"
}Set Session Properties node
The Set Session Properties node lets you change details in the resulting authenticated session. You can do one or both of the following:
- Set session properties
-
Use this node to add
key:valueproperties to the user’s authenticated session on successful authentication.You can access session properties using a variable in a webhook. Learn more in Configure authentication webhooks.
- Update the authenticated session timeouts
-
PingAM Use this node to update the authenticated session timeout settings. For example, you could have different session settings for different branches within the journey based on factors such as which region the user was authenticating from or the authentication methods being used.
Consider the following when updating authenticated session timeout settings:
-
If a journey has multiple nodes that set session timeouts, PingOne Advanced Identity Cloud uses the settings associated with the last executed node to determine the timeouts for the resulting authenticated session.
-
If an inner journey includes nodes that set session timeouts, PingOne Advanced Identity Cloud uses the updated timeouts in the parent journey.
-
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
PingAM This node reads the authenticated session timeout settings from the user, journey or the Session service. Learn more in Configure authenticated session timeout settings.
Dependencies
Make sure the user can successfully authenticate and get a session.
This node is ignored unless the user gets an authenticated session.
Configuration
| Property | Usage | ||
|---|---|---|---|
Properties |
The session properties to set.
When finished, click Save to keep your settings. |
||
PingAM Maximum Session Time |
The maximum authenticated session time in minutes. If set, this overrides the maximum authenticated session time set in the journey or the Session service. Learn more in Configure authenticated session timeout settings.
|
||
PingAM Maximum Idle Time |
The maximum idle time for the authenticated session in minutes. If set, this overrides the maximum idle time set in the journey or the Session service. Learn more in Configure authenticated session timeout settings.
|
Outputs
This node sets session properties. It doesn’t change the shared state data.
This node can’t override system session properties, such as the principal or the authentication level. Use a different journey to re-authenticate the user rather than trying to change such properties with this node.
Additionally, this node updates the authenticated session timeouts if new values are provided.
Examples
Example 1: Update the successURL session property
This example uses the Set Session Properties node to update the successURL session property.
-
A first platform journey updates the session property on successful authentication:
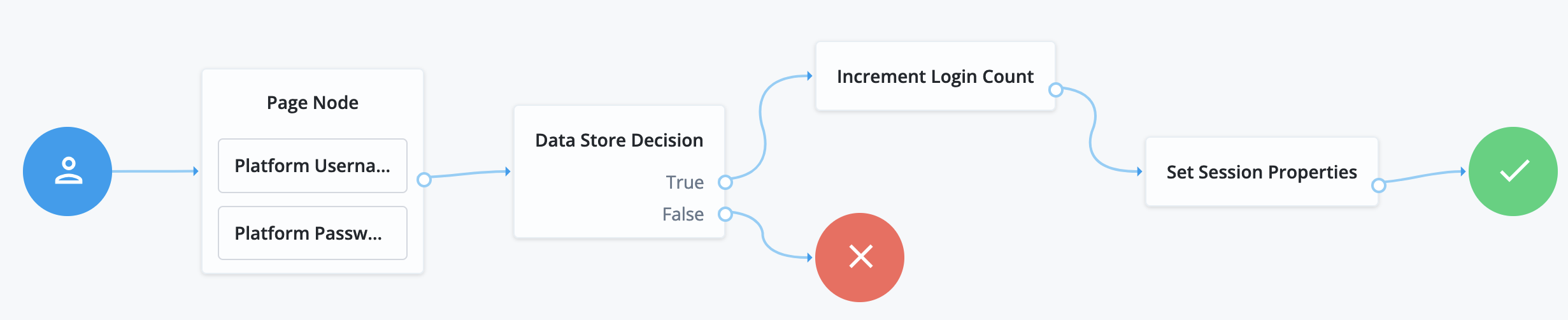
-
The Page node containing the Platform Username node and Platform Password node prompts for credentials.
-
The Data Store Decision node validates the username-password credentials.
-
The Increment Login Count node updates the number of successful authentications in the user profile.
-
The Set Session Properties node, sets the
successURLsession property.Configure the Properties to add a
successURLproperty with the URL of your choice.
When the journey completes successfully, PingOne Advanced Identity Cloud updates the
successURLin the user’s session data. -
-
A second journey uses a script to display the session properties after the user authenticates:
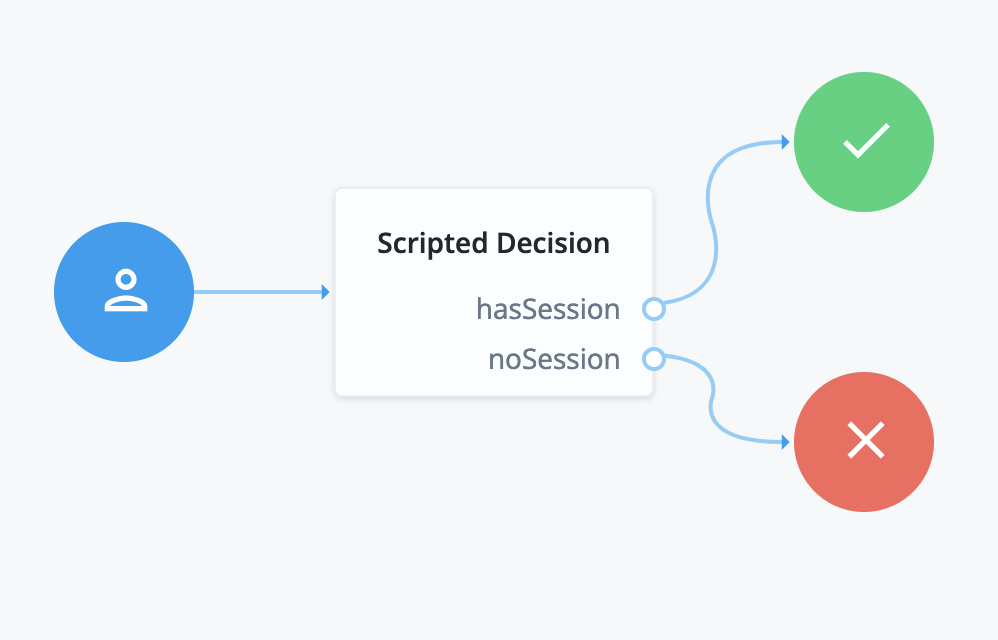
The Scripted Decision node calls the following script to inject the session properties into the shared state data so the journey can display them though a debug popup:
if (typeof existingSession !== 'undefined') { nodeState.putShared('session', existingSession) action.goTo('hasSession') } else { nodeState.putShared('session', null) action.goTo('noSession') }javascriptThe second journey has Debug mode and Enable Debug Popup selected.
Follow these steps to try the example:
-
Create both journeys using the journey editor.
-
Sign in through the first journey with a test user account.
The browser shows the user profile page.
-
In the same browser window, browse to the URL for the second journey.
The debug popup window displays the shared state data including session properties:
{ "transactionId": "...", "session": { "successURL": "<your-success-url>", "...": "..." }, "realm": "/alpha", "authLevel": 0, "username": "test" }jsonThe
successURLproperty is set to <your-success-url>, the one you configured as the value in Properties of the Set Session Properties node. -
Sign out as the test user.
-
Sign in through the default journey as the test user.
The default journey doesn’t use the Set Session Properties node with your configuration, so it uses the default value for the
successURLsession property. -
In the same browser window, browse to the URL for the second journey again.
The debug popup window displays the shared state data, including session properties with the default
successURLvalue.
Example 2: Update the authenticated session timeouts
PingAM This example uses the Set Session Properties node to set different session timeouts depending on the authentication method used. If the user chooses to authenticate with a username and password, the resulting authenticated session will have a shorter lifetime than if they use a social provider to authenticate. For both authentication methods, the idle timeout will be lower than the default.
| Instead of setting the same maximum session idle timeout in each node, you could set it at the journey level and leave the node setting blank. They have been set in the nodes in this example for demonstration purposes. |

a The Page node containing the Select Identity Provider node prompts the user to select a social identity provider or to authenticate with a username and password.
b If the user selects local authentication, the Data Store Decision node takes care of the authentication.
c The Set Session Properties node for local authentication updates the session timeout values with the following settings:
-
Maximum Session Time: 60
-
Maximum Idle Time: 20
d If the user selects social authentication, the Social Provider Handler node does the following:
-
Routes the user to the selected social provider to authenticate there
-
Retrieves the user’s profile information and transforms it into a format that PingOne Advanced Identity Cloud can use
-
Assesses whether the user has an existing identity in PingOne Advanced Identity Cloud
-
If the user has an existing identity, authenticates that identity
-
If the user doesn’t have an identity, routes the user to another page node
-
If the user interrupts the social authentication, routes the user back to the Select Identity Provider node
-
e The Set Session Properties node for social authentication updates the session timeout values with the following settings:
-
Maximum Session Time: 180
-
Maximum Idle Time: 20
f The nodes on the page node request the information required to register a new identity.
g The Create Object node creates the new identity in PingOne Advanced Identity Cloud.
h The Set Session Properties node for social authentication updates the session timeout values with the following settings:
-
Maximum Session Time: 180
-
Maximum Idle Time: 20
State Metadata node
The State Metadata node returns selected attributes from the shared node state as metadata.
This node sends a MetadataCallback to retrieve shared state values,
which it adds to the JSON response from the /authenticate endpoint.
This example shows how a shared state attribute, mail, is returned:
{
"callbacks": [
{
"type": "MetadataCallback",
"output": [
{
"name": "data",
"value": {
"mail": "bjensen@example.com"
}
}
]
}
]
}Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Configuration
| Property | Usage |
|---|---|
Attributes |
Specify one or more shared state attribute names for return. Default: none |
Example
Use this node to display custom information that includes user attributes without having to alter the existing flow.
For example, for OTP authentication with a choice of email or SMS, use this node to return the user’s email address or phone number. You can use the attributes with an OTP Collector Decision node, and optionally, a Scripted Decision node, to customize the data for display later.
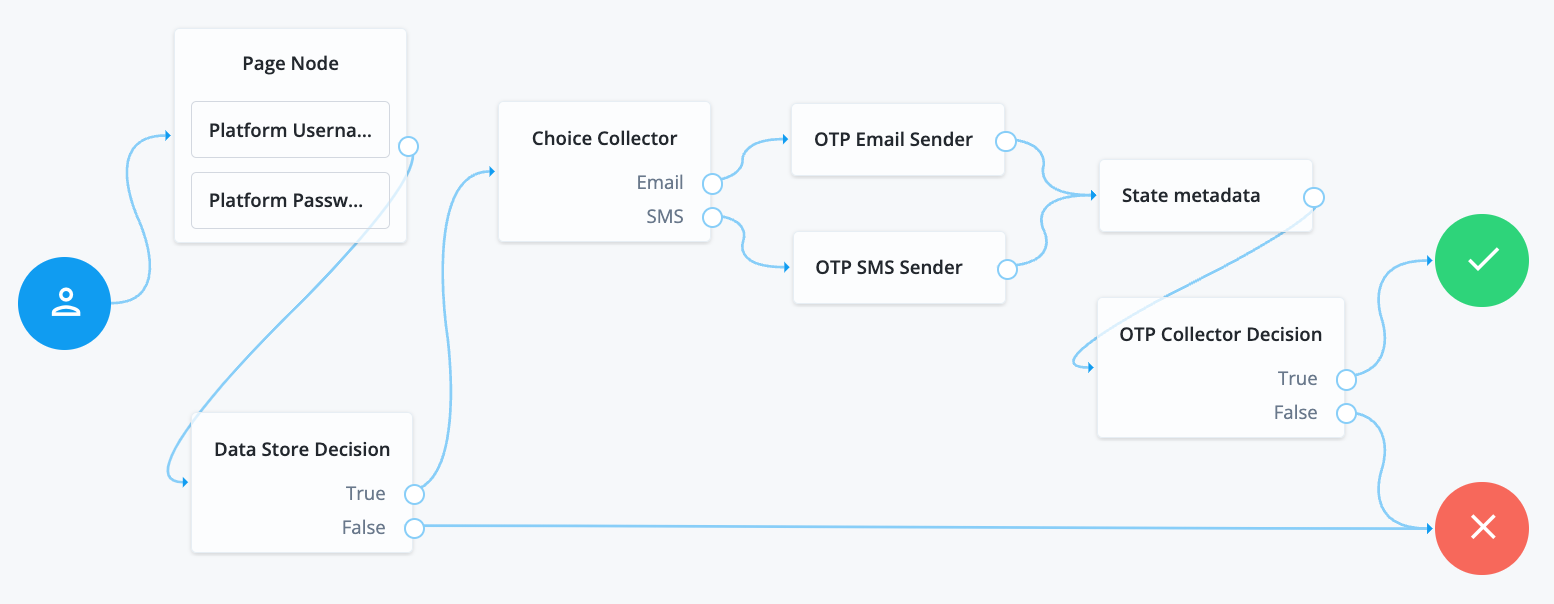
-
The Page node with a Platform Username node and Attribute Collector node prompts for the credentials.
-
The Data Store Decision node confirms the user’s credentials.
-
The Choice Collector node lets the user opt for notification through email or a text message.
-
The OTP Email Sender node sends the one-time passcode (OTP) as email.
-
The OTP SMS Sender node sends the OTP as a text message.
-
The State Metadata node injects attributes for additional information.
-
The OTP Collector Decision node displays the additional information when collecting the OTP to verify.
Success URL node
Sets the redirect URL when authentication succeeds.
|
Specifying a success URL overrides any |
For more information on how AM determines the redirection URL, and to configure the Validation Service to trust redirection URLs, refer to Success and failure redirection URLs.
|
The URL is also saved in the |
Timer Start node
Starts a named timer metric, which you can stop with a Timer Stop node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage |
|---|---|
Start Time Property |
Specify a property name into which to store the current time. Specify the same value in any instances of the Timer Stop node that measure the time elapsed since evaluation passed through this node. |
Timer Stop node
Records the time elapsed since evaluation passed through the Timer Start node in the specified metric name.
Note that this node does not reset the time stored in the specified Start Time Property property. Other Timer Stop nodes can also calculate the time elapsed since evaluation passed through the same Timer Start node.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Properties
| Property | Usage | ||
|---|---|---|---|
Start Time Property |
Specify the property name containing the time from which to calculate the elapsed time. |
||
Metric Key (required) |
Enter the name for a new metric that stores the calculated elapsed time.
|
Uncategorized nodes
Identity Assertion node
The Identity Assertion node provides a secure communication channel for authentication journeys to communicate directly with PingGateway.
The node extends PingOne Advanced Identity Cloud by adding PingGateway’s routing capabilities and supporting identity assertion with third-party authentication services. Authentication services include Windows Desktop SSO and Kerberos.
The following image shows the flow of an authentication request:
PingOne Advanced Identity Cloud and PingGateway share a symmetric key for encryption and decryption at both ends of the flow.
Compatibility
| Product | Compatible? |
|---|---|
Advanced Identity Cloud |
Yes |
PingAM (self-managed) |
Yes |
Ping Identity Platform (self-managed) |
Yes |
Inputs
All shared node state properties listed in Mapping to server claims
are valid optional inputs to this node.
To allow the node to validate that an Identity Assertion JWT is the result of an
identity request, the nonce must be present in the shared node state as
identityAssertionNonce. This isn’t required for the initiating authentication request.
Dependencies
The Identity Assertion node relies on the following prerequisites:
-
An Identity Assertion service must be configured in the same realm, with at least one server configuration that can be selected for use with the Identity Assertion node.
-
The Identity Assertion service server must have a valid shared secret encryption key configured as an ESV in the secret store.
-
The Identity Assertion server must be deployed, running, and accessible to the Identity Assertion node.
It must also be configured with the shared secret encryption key.
PingGateway can fulfil the role of the Identity Assertion server.
To use the Identity Assertion node in your PingOne Advanced Identity Cloud environment, you must complete the following steps, as described in detail in the worked Example :
Configuration
The configurable properties for this node are:
| Property | Usage |
|---|---|
Node name |
The name given to this node in the Journey. Default: |
Identity Assertion server ID |
The ID of the Identity Assertion server that handles assertion requests. The ID is composed of the server’s ID and realm (if realm-scoped). |
Mapping to server claims (optional) |
Mapping of:
Required only if the server requires additional data. When a shared node state attribute has a value for a mapped key, the value is added to the identity request JWT claims according to the corresponding claim. |
Mapping from server result (optional) |
Mapping of:
Required only if the server requires additional data. Default: the JWT When an Identity Assertion JWT claim has a value for a mapped claim, the value is added to the shared node state according to the corresponding shared node state key. |
Outputs
Any data mapped from the claims returned by the Identity Assertion server stored in the shared node state of the journey.
- Successful Identity Assertion
-
The configuration
Mapping from server result (optional)determines the shared node state property to set for the mandatory claimprincipal. The value of the shared node state property is set with the value of theprincipalclaim.For example, if
principalis mapped tousernameReceived, the attributeusernameReceivedis set in the shared node state. By default,principalis mapped tousername.Other values mapped in
Mapping from server result (optional)are set in the shared node state only if the claim exists in the resulting Identity Assertion JWT. - Failed Identity Assertion
-
The shared node state property
erroris set with the value of theerrorclaim in the resulting Identity Assertion JWT.
Outcomes
Success-
The Identity Assertion server indicates that authentication was successful. It provides the authenticated
principal. Error-
The Identity Assertion server indicates that authentication failed. It provides information about the error.
Example
The following worked example describes how to use the Identity Assertion node to authenticate internal access.
Create and import a secret encryption key
Identity Assertion in PingOne Advanced Identity Cloud and PingGateway uses a single secret for all encryption and decryption:
-
PingOne Advanced Identity Cloud uses the key to encrypt the identity request JWT; PingGateway uses it to decrypt the identity request JWT.
-
PingGateway uses the key to encrypt the resulting Identity Assertion JWT; PingOne Advanced Identity Cloud uses it to decrypt the Identity Assertion JWT.
Provide the encryption key as a PEM-encoded AES secret key or base64aes-encoded secret key ESV.
The example route in Configure PingGateway as an Identity Assertion Server uses PEM for PingGateway and imports the secret key value as an ESV into PingOne Advanced Identity Cloud.
Configure a key for that route as described in this section, and learn more from Map ESV secrets to secret labels
-
Generate a random 32-byte AES secret-key:
$ head -c32 /dev/urandom | base64 Rf8...Ig=bash -
Put the key string into a .pem file called
idassert.pem, for use on the PingGateway side.-----BEGIN AES SECRET KEY----- Rf8...Ig= -----END AES SECRET KEY-----bashIn the following steps, you import the raw key as an ESV and configure it in an ESV secret store.
-
Using information in Authenticate to Identity Cloud REST API with access token, get an access token for your tenant.
-
Using the access token, import the new ESV into your tenant. The following example imports an ESV named
esv-idassert:$ export VALUE=$(echo -n Rf8…Ig= | base64) $ curl -X PUT "<tenant-env-fqdn>/environment/secrets/esv-idassert" \ -H "Authorization: Bearer <TOKEN>" \ -H "Content-Type: application/json" \ -H "Accept-API-Version: protocol=1.0;resource=1.0" \ --data-raw "{\"encoding\":\"base64aes\",\"useInPlaceholders\":false,\"valueBase64\":\"$VALUE\"}"bashConsider the following points for ESVs:
-
Prefix the name with
esv-. -
Don’t suffix the name with a number.
-
Use
base64aesencoding. PEM encoding is also available.
-
-
Using information in Tenant settings, check that the ESV is displayed in the Environment Secrets and Variables panel.
Configure the Identity Assertion service
Enable the service
-
In the Advanced Identity Cloud admin console, go to Native Consoles > Access Management > Realms > Realm name > Services, click +Add a Service and select Identity Assertion Service to create.
-
In the Identity Assertion Service page, ensure Enable is selected.
Configure a server
-
In the
Secondary Configurationstab, click +Add a Secondary Configuration and enter the following information:-
Name: A unique name for the Identity Assertion server. For example, use
IG01. -
Identity Assertion server URL: The Identity Assertion server URL. For example, enter
https://ig.ext.com:8443. -
Shared Encryption Secret: PingOne Advanced Identity Cloud uses this identifier to create a secret label for encrypting the identity request JWT and resulting Identity Assertion JWT.
The secret label takes the form
am.services.identityassertion.service.identifier.shared.secretwhere identifier is the value of Shared Encryption Secret. For example, use identifieridassertto create a label calledam.services.identityassertion.service.idassert.shared.secret.
-
-
Click Create.
-
Keep the default values for JWT TTL (seconds) and Skew Allowance (seconds) and save your changes.
Learn more about the service configuration in Identity Assertion service .
Map the secret label to the encryption key
The example route in Configure PingGateway as an Identity Assertion Server uses PEM for PingGateway and imports the secret key value as an ESV into PingOne Advanced Identity Cloud.
-
Log in to your Advanced Identity Cloud admin console, and go to Native Consoles > Access Management.
-
In the Realm Overview page, click Secret Stores.
-
Map the secret label used by the Identity Assertion service to the ESV secret store.
In the
Mappingstab, enter the following information:-
Secret Label: Enter the value for the Shared Encryption Secret you created in the Identity Assertion Service. For example, enter
idassert.You can configure the secret only after you have named it in the Identity Assertion service secondary configuration.
The full-length secret label is automatically constructed from the value. In this example, the full-length secret label is
am.services.identityassertion.service.idassert.shared.secret. -
Aliases: Enter the alias to the secret you created earlier. For example, enter
esv-idassert.
-
Configure PingGateway as an Identity Assertion Server
Configure PingGateway to:
-
Validate the identity request JWT.
-
Create an encrypted Identity Assertion JWT to send back to PingOne Advanced Identity Cloud.
The PingGateway configuration includes two routes:
- Authentication filter route
-
Directs unauthenticated requests to an authentication journey in PingOne Advanced Identity Cloud.
For testing purposes, configure PingOne Advanced Identity Cloud and PingGateway as described in Cross-domain single sign-on. The setup configures a demo user and validation service that are required for the example.
In
cdsso-idc.json, the CrossDomainSingleSignOnFilter uses PingOne Advanced Identity Cloud’s default authentication service. Add the propertyauthenticationServiceto the CrossDomainSingleSignOnFilter to direct requests to the journey.The following example redirects unauthenticated requests to a journey called
IgCallout.{ "name": "CrossDomainSingleSignOnFilter-1", "type": "CrossDomainSingleSignOnFilter", "config": { ... "authenticationService" : "IgCallout", ... }json - Identity Assertion service route
-
Directs unauthenticated requests to a local authentication service such as Kerberos or Windows Desktop SSO.
Consider the example in PingGateway’s Example Identity Assertion service route for Identity Assertion node. The route contains an
IdentityAssertionHandlerthat calls aScriptableIdentityAssertionPluginto manage local authentication.The route requires the following:
-
The key and PingOne Advanced Identity Cloud setup described in this worked example.
-
That the
IdentityAssertionHandler'speerIdentifierproperty refers to the host part of the tenant URL. -
That the
IdentityAssertionHandler'sconditionrefers to the same path as theRouteconfigured in the node. In this example, it refers to/idassert.
-
Configure the example authentication journey
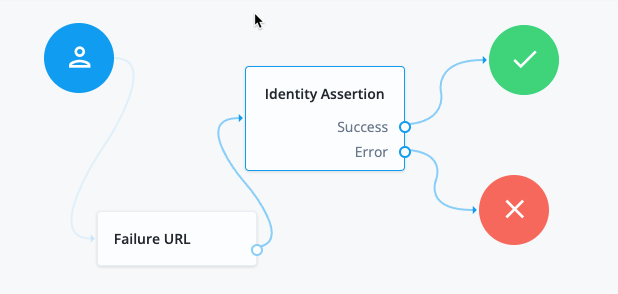
|
Add a Failure URL node to manage the journey flow if assertion fails. Configure the node with a URL to use for failed requests. For example, the following URL returns PingGateway to the CDSSO redirect endpoint: https://ig.ext.com:8443/home/cdsso/callback?error=Login%20failed&error_description=Identity%20Assertion%20Failure |
Configure the Identity Assertion node as follows:
-
Identity Assertion server ID: Select the ID and realm configured for the PingGateway server that supports Identity Assertion. For example, enter
IG01 [/alpha], whereIG01is the name of the server created in the Configure the Identity Assertion service. -
Route: Enter the value of the
conditionproperty in the PingGateway route that will handle Identity Assertion requests. For example, enter/idassert, as used for the example route in Configure PingGateway as an Identity Assertion Server.When a request matches the path
/idassert, the journey accesses the PingGateway route in PingGateway’s Example Identity Assertion service route for IdentityAssertionNode.